

Infosecurity News
Windows Quick Assist Exploited in Ransomware Attacks
Microsoft warned Storm-1811 started vishing attacks in April to gain access to target devices


Infosecurity News
Microsoft warned Storm-1811 started vishing attacks in April to gain access to target devices


Cyber Security News
Three vulnerabilities have been discovered in SAP Customer Experience (CX) commerce cloud and SAP Netweaver Application which were


The Hacker News
Beware of Storm-1811! This financially motivated group is abusing Microsoft's Quick Assist tool in social engineering attacks.


SC Magazine
Threat actors use the remote management tool and social engineering to access victims’ systems and install malware.


Bleeping Computer
Nissan North America (Nissan) suffered a data breach last year when a threat actor targeted the company's external VPN and shut down systems to receive a ransom.

The Hacker News
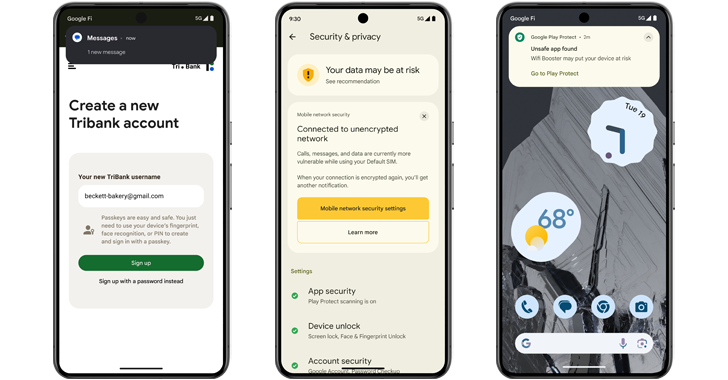
Android 15 introduces new features to prevent malicious apps from capturing your sensitive data. Find out more about these crucial updates:

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


HACKRead
Researchers warn that hackers can bypass FIDO2 phishing-resistant protections under certain conditions using a sophisticated MITM technique.


DarkReading
While the protocol has made passwordless authentication a reality, token-binding is key to prevent against token theft and reuse, security vendor says.


Krebs on Security
Microsoft today released updates to fix more than 60 security holes in Windows computers and supported software, including two "zero-day" vulnerabilities in Windows that are already being exploited in active attacks. There are also important security patches available for macOS…

The Hacker News
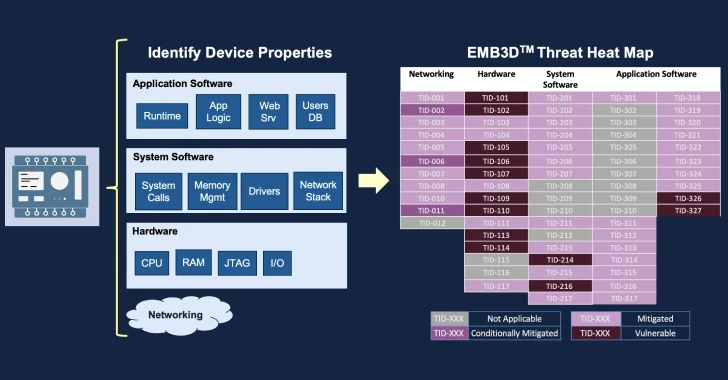
MITREcorp has launched EMB3D, a new threat-modeling framework for embedded devices used in critical infrastructure.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.

The Hacker News
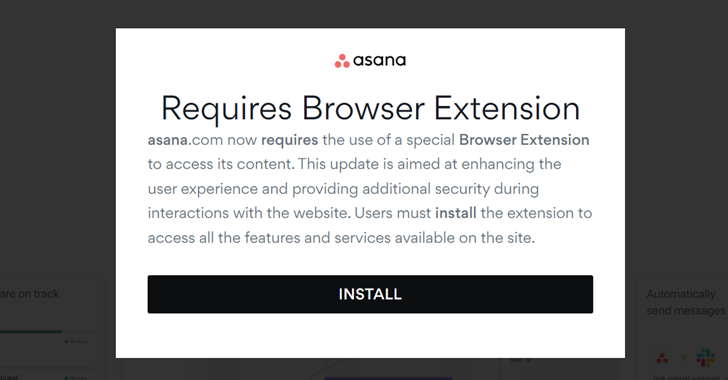
The notorious FIN7 hacking group is at it again! This time, they're using malicious Google ads to trick users into downloading malware disguised as le

Cyber Security News
Two new vulnerabilities have been discovered in Next.js which were related to response queue poisoning and SSRF on certain Next.js versions.


CSO
CISA’s pledge drew some big names, but the impact on software security could be limited. Meanwhile the org has extended its comment period on the CIRCIA cyberattack reporting law.


DarkReading
CISA's agreement is voluntary and, frankly, basic. Signatories say that's a good thing.


CyberSecurity Dive
Federal officials are taking steps toward a long-stated goal of shifting the security burden from technology users to the companies that build it.


The Cyber Express
Lenovo takes a bold step towards fortifying cybersecurity by joining the Secure by Design pledge, initiated by the US Cybersecurity


The Hacker News
Researchers have uncovered a vulnerability (CVE-2024-3661) that allows threat actors to snoop on your VPN traffic.

%20(1).png)
Cyber Security News
Microsoft announced a major shift in its operational priorities, placing security at the forefront of its agenda, above other considerations.


SecurityWeek
BetterHelp customers have started receiving refund notices from a $7.8 million data privacy settlement, the FTC says.


CyberSecurity Dive
CISA said companies ranging from Microsoft to Palo Alto Networks signed the voluntary pledge in an effort to boost resiliency and increase transparency around CVEs and cyberattacks.


The Record
CISA Director Jen Easterly said the voluntary pledge by software companies is important because of widespread nation-state hacking campaigns, including the Volt Typhoon operation attributed to China.


HACKRead
The norotious IntelBroker hackers claims to have breached a leading cybersecurity company selling its access for $20,000 in XMR cryptocurrency.


DarkReading
At least a portion of executive compensation going forward will be tied to meeting security goals and metrics.


Security Affairs
MITRE published more details on the recent security breach, including a timeline of the attack and attribution evidence.


Ars Technica
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


The Hacker News
Czechia and Germany reveal they were targets of a massive cyber espionage campaign by Russia-linked APT28 hacker group.


Ars Technica
ZTDNS brings the best of both worlds to DNS: encryption and fine-grained control.


CyberNews
Google and the US Justice Department wrap up closing arguments over claims that parent company Alphabet unlawfully dominated web search and related advertising.


HACKRead
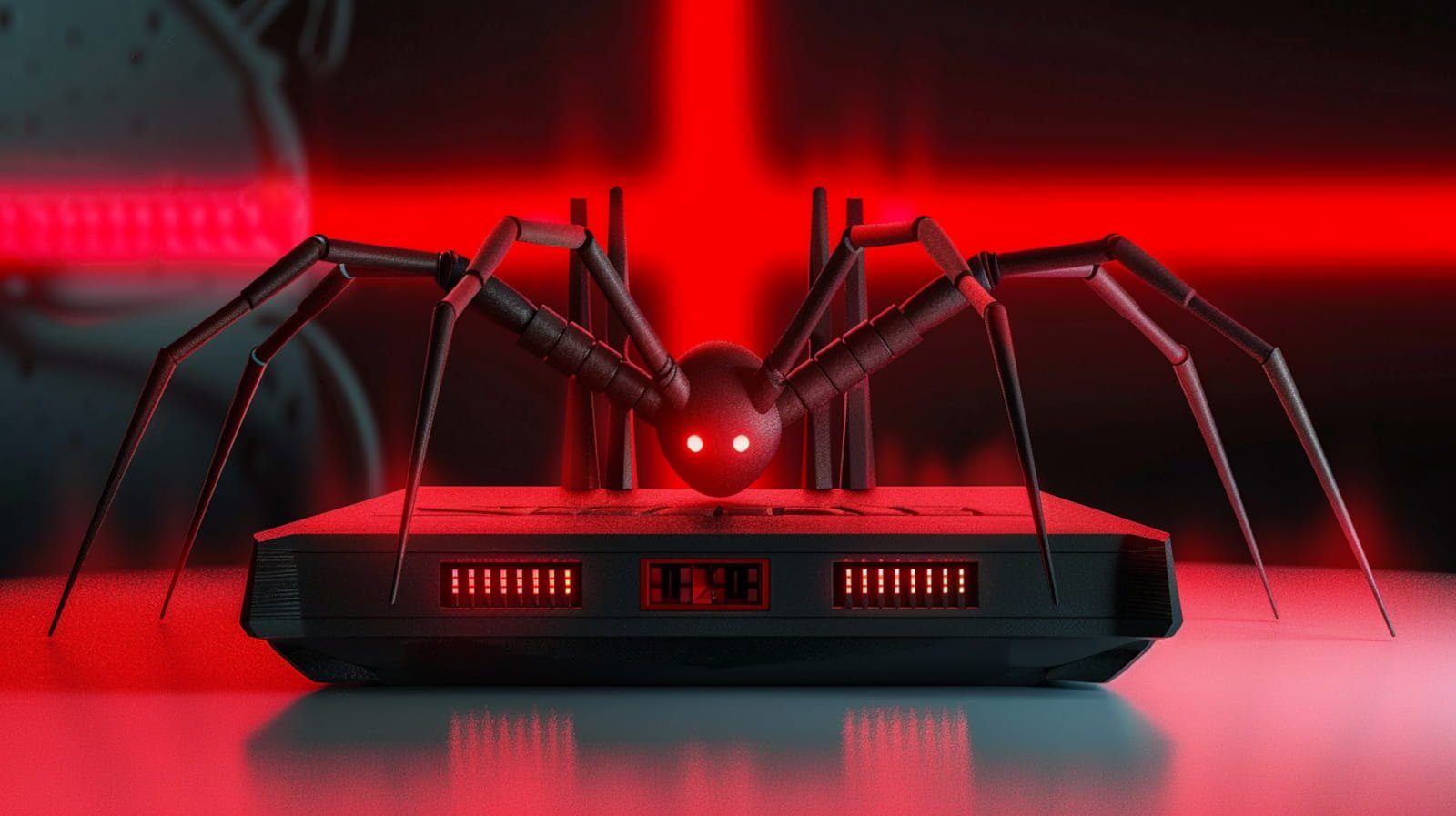
A new botnet called Goldoon targets D-Link routers and NAS devices putting them at risk of DDoS attacks and more. Learn how weak credentials leave you vulnerable and how to secure your network. pen_spark


Ars Technica
Microsoft has been criticized for "preventable" failures and poor communication.


SecurityWeek
Microsoft security chief Charlie Bell pledges significant reforms and a strategic shift to put security above all other product features.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


SecurityWeek
CISA and the FBI warn of threat actors abusing path traversal software vulnerabilities in attacks targeting critical infrastructure.


The Hacker News
Google announces over 400 million accounts now use passkeys - the passwordless authentication solution.


The Hacker News
Aruba Networking has released critical security patches for ArubaOS. Four flaws could allow remote code execution, giving attackers full control.


Security Affairs
Government agencies from the US, Canada and the UK warn of Russian threat actors targeting critical infrastructure in North America and Europe


Security Affairs
HPE Aruba Networking addressed four critical remote code execution vulnerabilities impacting its ArubaOS network operating system.


CyberNews
Independent and ideologically motivated pro-Russian hacktivists can physically threaten insecure and misconfigured operational technology devices.


DarkReading
DMARC adoption is more important than ever following Google's and Yahoo's latest mandates for large email senders. This Tech Tip outlines what needs to be done to enable DMARC on your domain.


SecurityWeek
Government agencies are sharing recommendations following attacks claimed by pro-Russian hacktivists on ICS/OT systems.


Infosecurity News
The US and its allies claim Russian hacktivists are disruptive operations in water, energy, food and agriculture sectors

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


SC Magazine
Government agencies warn industry to improve their operational technology security following breaches of North American and European systems.


Bleeping Computer
The US government is warning that pro-Russian hacktivists are seeking out and hacking into unsecured operational technology (OT) systems used to disrupt critical infrastructure operations.


CyberSecurity Dive
CISA, the FBI and international partner agencies want water, energy, agriculture and other sectors to immediately reset passwords and apply multifactor authentication.


DarkReading
The newly discovered malware, which has so far mainly targeted Turkish telcos and has links to HiatusRat, infects routers and performs DNS and HTTP hijacking attacks on connections to private IP addresses

CyberScoop
Other sectors that the hacktivists — who sometimes pose physical threats — are targeting in North America and Europe include energy and agriculture, according to a Wednesday advisory.

Bleeping Computer
A new malware named 'Cuttlefish' has been spotted infecting enterprise-grade and small office/home office (SOHO) routers to monitor data that passes through them and steal authentication information.


The Cyber Express
National Supply Chain Day, which was recently observed on April 29, serves as a dedicated day to recognize the critical


Latest Hacking News
A security researcher discovered a security vulnerability in the Judge0 system, which received a patch that could further be bypassed, leading to further vulnerabilities. While the developer eventually patched the issue after repeated exploits, the


The Record
The Cybersecurity and Infrastructure Security Agency (CISA) and international partners are warning about weak security practices in operational technology (OT) that could be targeted by pro-Russia hackers.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


Ars Technica
Amazon says it's working on stopping others from "making your AWS bill explode."


Bleeping Computer
Google has increased rewards for reporting remote code execution vulnerabilities within select Android apps by ten times, from $30,000 to $300,000, with the maximum reward reaching $450,000 for exceptional quality reports.


Cyber Security News
In a significant move to bolster cybersecurity, the United Kingdom has introduced a groundbreaking law aimed at enhancing the security of


Security Affairs
The UK National Cyber Security Centre (NCSC) orders smart device manufacturers to ban default passwords starting from April 29, 2024.


Cyber Security News
an AWS customer faced a staggering $1,300 bill for S3 usage, despite creating a single, empty bucket for testing purposes.


The Hacker News
The U.K. is the first country to ban default passwords on smart devices starting April 29, 2024. Manufacturers must provide unique passwords and secur


The Cyber Express
The UK government has taken steps to safeguard consumers from cyberattacks by prohibiting common and easily-guessable passwords such as "admin"


Ars Technica
The law aims to prevent global-scale botnet attacks.


CyberNews
Internet-connected smart devices will soon be required to meet minimum security standards by law in the UK.


Cyber Security News
Tanto Security has disclosed critical vulnerabilities in the widely-used open-source service Judge0, which could allow attackers to perform a sandbox escape and gain root access to the host machine.


Infosecurity News
IoT manufacturers, retailers and importers must comply with new security legislation, the PSTI act, from today


The Hacker News
Multiple vulnerabilities have been discovered in the popular Judge0 online code execution system, putting users at risk of complete system compromise.

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

The Record
Britain now has IoT hardware standards that ban weak or easily guessable default passwords such as “admin” or “12345." Manufacturers are also required to publish contact details so users can report bugs.


The Record
Ukraine’s government uses the bots to collect and share real-time information about Russian military activity.


SC Magazine
A look back at the Heartbleed bug and measuring its’ legacy, impact and how some view one of cybersecurity’s biggest headaches as an important learning moment.


Bleeping Computer
Some Google Chrome users report having issues connecting to websites, servers, and firewalls after Chrome 124 was released last week with the new quantum-resistant X25519Kyber768 encapsulation mechanism enabled by default.


The Hacker News
A new Android malware called Brokewell is disguising itself as updates for popular apps like Google Chrome and Klarna


SecurityWeek
The Brocade SANnav management application is affected by multiple vulnerabilities, including a publicly available root password.


SC Magazine
Security pros say given the complexity of SAN management tools, it’s understandable the patches took so long.

Ars Technica
Perimeter devices ought to prevent network hacks. Why are so many devices allowing attacks?


DarkReading
The city is stymied in efforts to pinpoint the issue since its IT systems were shut down in the wake of the cyberattack.


CyberSecurity Dive
State-linked actors are using a custom tool for post exploitation activity of a vulnerability in Windows Print Spooler, which could result in credential theft and backdoor installs.

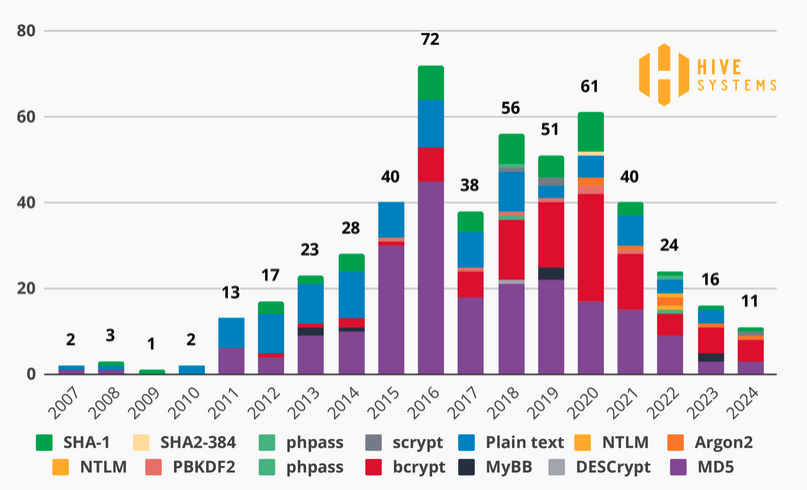
SecurityWeek
Hive Systems conducts another study on cracking passwords via brute-force attacks, but it’s no longer targeting MD5.


Security Affairs
An attack on Leicester City Council resulted in certain street lights remaining illuminated all day and severely impacted its operations


SC Magazine
A new CryptBot variant targets password managers and authentication apps in the new campaign.


DarkReading
Growing attacks targeting the flaw prompted CISA to include it in the known exploited vulnerabilities catalog earlier this month.

.webp)
Cyber Security News
This issue stems from a severe cyber attack that targeted Leicester City Council's IT systems, leading to a disruptions in city services


The Hacker News
European police warn that default E2EE could severely hamper efforts to tackle online crimes like child abuse and terrorism.


DarkReading
Malaysia, Singapore, and Ghana are among first countries to mandate licenses for cybersecurity firms to do business, but concerns remain.


SC Magazine
Arbitrary code in Lambda Layers may be unsafely executed in older versions of Keras.

.webp)
Cyber Security News
A new supply-chain vulnerability has been identified in the Lambda Layers of third-party TensorFlow-based Keras models that could allow

Cyber Security News
A new backdoor named "Kapeka" has been identified to be attacking victims in Eastern Europe since mid-2022.


CyberNews
Europol urges politicians and industry leaders “to take urgent action to ensure public safety across social media platforms.”


The Hacker News
Major cybercrime groups are under attack by police. But are these takedowns effective? Some groups vanish, others bounce back in DAYS.


Latest Hacking News
Apple users in China may no longer find various popular apps, such as WhatsApp and Telegram, on the App Store. Apple seemingly removed these apps from the App Store following the Chinese government orders that


The Record
A joint declaration from European police chiefs does not mention Meta by name, but just a few months ago the company began rolling out the technology as default across “all personal chats and calls on Messenger and Facebook.”


The Cyber Express
by Neelesh Kripalani, Chief Technology Officer, Clover Infotech As businesses grapple with an ever-changing and increasingly hostile threat environment, the


DarkReading
Attackers are indiscriminately targeting VPNs from Cisco and several other vendors in what may be a reconnaissance effort, company says.


The Hacker News
Ukrainian government networks have been compromised by the OfflRouter malware since 2015. This malware is causing sensitive documents to be exposed.

Cyber Security News
Hackers often use Linux ransomware due to its prevalence in server environments, offering higher potential payouts from organizations with


Cyber Security News
Microsoft said the attack begins by identifying Kubernetes workloads running OpenMetadata that are exposed to the Internet.


Security Affairs
Cisco addressed a high-severity vulnerability in its Integrated Management Controller (IMC) for which publicly available exploit code exists


The Hacker News
Vulnerabilities in OpenMetadata are being exploited. These critical security flaws enable hackers to get into Kubernetes environments.
Loading more articles....