

The Hacker News
Detecting Windows-based Malware Through Better Visibility
Traditional defense tactics don't always apply to cyber warfare. With EventSentry, bolster your network's defense with prevention, detection, and ongo


The Hacker News
Traditional defense tactics don't always apply to cyber warfare. With EventSentry, bolster your network's defense with prevention, detection, and ongo


Ars Technica
Toss certbot or acme.sh onto some servers and baby, you got a stew going!


Security Affairs
Crooks stole nearly $10 million from the wallet of one of the co-founders of the video game Axie Infinity and the related Ronin Network.


Infosecurity News
Discovered by the SentinelLabs team, FBot targets web servers, cloud services and SaaS platforms


SecurityWeek
The tool, called FBot, is capable of credential harvesting for spamming attacks, and AWS, PayPal and SaaS account hijacking.


SecurityWeek
Recorded Future calculates that North Korean state-sponsored threat actors are believed to have stolen more than $3 billion in cryptocurrency.


Cyber Security News
TriangleDB", this malware infection chain consists of a malicious iMessage attachment which launches a chain of exploits on affected devices.


SecurityWeek
Kaspersky analyzes the stealth techniques that were used in the ‘Operation Triangulation’ iOS zero-click attacks.


The Hacker News
Sophisticated Apple iOS attack dubbed Operation Triangulation employed clever techniques to targets victims with a backdoor implant called "TriangleDB

The Hacker News
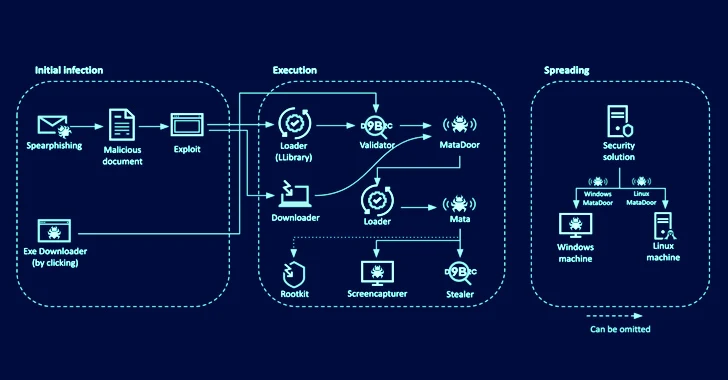
New MATA cyber espionage operation strikes Eastern European companies in oil & gas and defense sectors.


Bleeping Computer
A threat actor known as W3LL developed a phishing kit that can bypass multi-factor authentication along with other tools that compromised more than 8,000 Microsoft 365 corporate accounts.


SecurityWeek
SecurityWeek interviews Field CISOs, Fawaz Rasheed (VMware Carbon Black) and Nabil Hannan (NetSPI), about the emerging cybersecurity role.


The Record
State-controlled media said the alleged intrusion could "illegally control and steal seismic intensity data," calling it "a serious threat to national security."


The Hacker News
Unmasking the E-Crime Mastermind: Vietnamese suspect linked to notorious XE Group unveiled!


The Hacker News
New Analysis Reveals Raspberry Robin Attack Infrastructure Can be Repurposed by Other Threat Actors


DarkReading
Version 2.0 of the Common Security Advisory Framework will enable organizations to automate vulnerability remediation.

SecurityWeek
Hackers have exploited a blockchain bridge to divert 2 million Binance Coins (BNB) – worth more than $560 million – from Binance Bridge.


Security Affairs
US authorities recovered more than $30 million worth of cryptocurrency stolen by the North Korea-linked Lazarus APT from Axie Infinity. A joint operation conducted by enforcement and leading organizations in the cryptocurrency industry allowed to recover more than $30 million worth of cryptocurrency stolen by North Korean-linked APT group Lazarus from online video game Axie […]


Bleeping Computer
The North Korean 'Kimsuky' threat actors are going to great lengths to ensure that their malicious payloads are only downloaded by valid targets and not on the systems of security researchers.

SecurityWeek
Cryptocurrency bridge Nomad has lost roughly $200 million worth of tokens following a hack described as chaotic.

SecurityWeek
The US government has warned that rogue IT workers from North Korea enable DPRK hacking operations and provide logistical support for its threat actors.


ZDNet
Blender.io blocked from transactions involving Americans after laundering crypto for North Korea.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. U.S. Gov believes North Korea-linked Lazarus APT is behind Ronin Validator cyber heist The […]


Security Affairs
The U.S. government blames North Korea-linked APT Lazarus for the recent $600 million Ronin Validator cyber heist. The U.S. government attributes the recent $600 million Ronin Validator cryptocurrencty heist to the North Korea-linked APT Lazarus. The U.S. Treasury announced in a notice the sanctions against the Ethereum address used by the APT to receive the […]


ZDNet
Binance, a16z, and Animoca Brands chip in for funding round while the network has its security upgraded.


Infosecurity News
Cyber-heist could be biggest ever


ZDNet
The attacker took control of validation nodes and then stripped the network in a pair of transactions.


Security Affairs
Threat actors have stolen approximately $625 million worth of Ethereum and USDC tokens from Axie Infinity ‘s Ronin network bridge. Threat actors have stolen almost $625 million in Ethereum and USDC (a U.S. dollar pegged stablecoin) tokens from Axie Infinity’s Ronin network bridge. The attack took place on March 23rd, but the cyber heist was […]


CyberScoop
It's one of the largest crypto heists in history.


The Record
The Ronin Network announced on Tuesday that hackers have stolen more than $600 million worth of Ethereum (173,600 ETH) and $25.5 million of US dollar-pegged stablecoin USDC, making it one of the largest decentralized finance (DeFi) hacks to date.


Bleeping Computer
A hacker has stolen almost $620 million in Ethereum and USDC tokens from Axie Infinity's Ronin network bridge, making it possibly the largest crypto hack in history.


DataBreaches
Shanthi Rexaline reports: Ronin, an Ethereum-linked sidechain made by Sky Mavis specifically for Axie Infinity disclosed Tuesday a major security breach that...