

The Hacker News
Kasseika Ransomware Using BYOVD Trick to Disarms Security Pre-Encryption
Kasseika, the latest ransomware kid on the block, is using a sneaky trick called BYOVD to disarm your defenses before encrypting your files! It even


The Hacker News
Kasseika, the latest ransomware kid on the block, is using a sneaky trick called BYOVD to disarm your defenses before encrypting your files! It even

The Hacker News
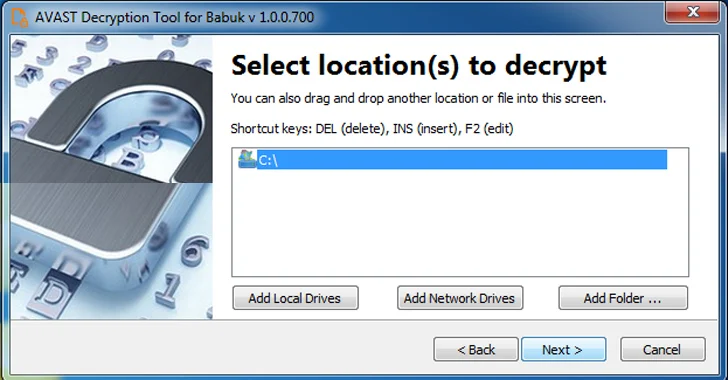
Researchers have released decryptors for both the Tortilla variant of Babuk ransomware and Black Basta ransomware


Bleeping Computer
Researchers from Cisco Talos working with the Dutch police obtained a decryption tool for the Tortilla variant of Babuk ransomware and shared intelligence that led to the arrest of the ransomware's operator.


Infosecurity News
Cisco Talos announced that a decryption key for the Babuk Tortilla ransomware variant is available for victims to download


Bleeping Computer
Tens of thousands of Microsoft Exchange email servers in Europe, the U.S., and Asia exposed on the public internet are vulnerable to remote code execution flaws.


SecurityWeek
New CISA guidance details cyber threats and risks to healthcare and public health organizations and recommends mitigations.

The Hacker News
Earth Lusca, a China-linked group, is using a stealthy Linux backdoor called SprySOCKS to target government entities worldwide.


Trend Micro
While monitoring Earth Lusca, we discovered an intriguing, encrypted file on the threat actor's server — a Linux-based malware, which appears to originate from the open-source Windows backdoor Trochilus, which we've dubbed SprySOCKS due to its swift behavior and SOCKS implementation.

The Hacker News
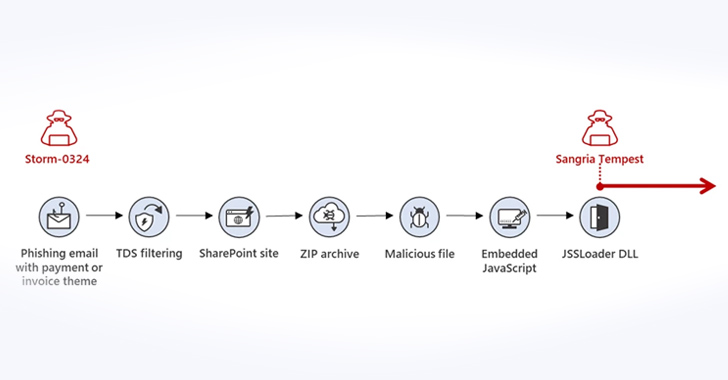
Microsoft sounds the alarm on Storm-0324's tactics, luring its prey through Teams messages to breach corporate networks.


Cyber Security News
Cybersecurity researchers at Qualys recently unveiled the top 20 most exploited vulnerabilities and also affirmed that hackers are particularly drawn to the products of Microsoft.


Cyber Security News
Virtual patching protects an application by examining the web application traffic and blocking the attacks while they're in transit.


SecurityWeek
Five Eyes government agencies publish a list of the software vulnerabilities that were most frequently exploited in malicious attacks in 2022.

The Hacker News
CISA, NSA, FBI, & global partners disclose the top exploited vulnerabilities of 2022.

CyberScoop
The list includes well-known vulnerabilities impacting Fortinet's VPNs and Log4Shell that hackers still routinely exploit.


The Record
A joint advisory from the Five Eyes nations warns that malicious cyber actors are exploiting older software vulnerabilities more frequently than recently disclosed ones.


Security Affairs
Google’s Threat Analysis Group Google states that more than 40% of zero-day flaws discovered in 2022 were variants of previous issues. The popular Threat Analysis Group (TAG) Maddie Stone wrote Google’s fourth annual year-in-review of zero-day flaws exploited in-the-wild [2021, 2020, 2019], it is built off of the mid-year 2022 review. In 2022, the researchers […]


Security Affairs
Iran-linked APT group Charming Kitten employed a new malware dubbed BellaCiao in attacks against victims in the U.S., Europe, the Middle East and India. Iran-linked Charming Kitten group, (aka APT35, Phosphorus, Newscaster, and Ajax Security Team) made the headlines in 2014 when experts at iSight issued a report describing the most elaborate net-based spying campaign organized by Iranian hackers using social media. Microsoft has been tracking the threat actors at […]


CSO
Attacks using the BellaCiao malware dropper seem to be customized for specific targets.


Infosecurity News
Sophos warns against simple interpretation of the data


The Hacker News
Attackers love to hunt down unwatched service accounts for lateral movement and ransomware spread. Don't let your organization be their next victim.


Bleeping Computer
Over 15 million publicly facing services are susceptible to at least one of the 896 vulnerabilities listed in CISA's KEV (known exploitable vulnerabilities) catalog.


Bleeping Computer
Microsoft is introducing a new Exchange Online security feature that will automatically start throttling and eventually block all emails sent from "persistently vulnerable Exchange servers" 90 days after the admins are pinged to secure them.

The Hacker News
Cryptojacking group TeamTNT suspected to be behind new strain of Monero-mining malware discovered by Cado Security

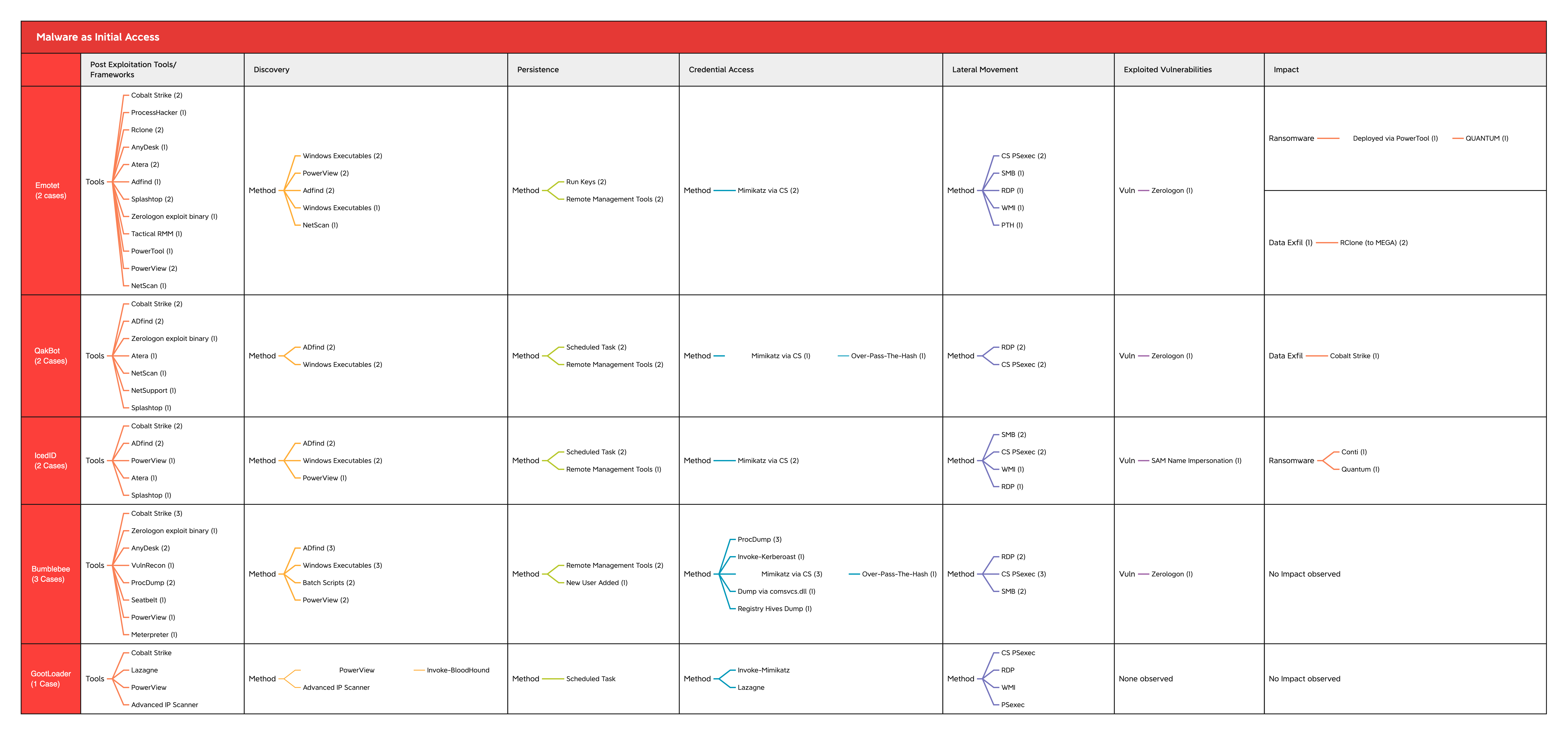
The DFIR Report
As we move into the new year, it’s important to reflect on some of the key changes and developments we observed and reported on in 2022. This year’s year-in-review report … Read More


CSO
The top five exploited vulnerabilities in 2022 include several high-severity flaws in Microsoft Exchange, Zoho ManageEngine products, and virtual private network solutions from Fortinet, Citrix and Pulse Secure.


Bleeping Computer
Microsoft says some antivirus exclusions previously recommended for Exchange servers should be removed to boost their security.


Bleeping Computer
A new malware dubbed 'ProxyShellMiner' exploits the Microsoft Exchange ProxyShell vulnerabilities to deploy cryptocurrency miners throughout a Windows domain to generate profit for the attackers.


Cyber Security News
As part of their second Patch Tuesday for the year, Microsoft recently released patches for 78 vulnerabilities along with the three actively exploited zero-day vulnerabilities overnight, 66 of which were marked important by the company.


DarkReading
78 new CVEs patched in this month's batch — nearly half of which are remotely executable and three of which attackers already are exploiting.


Bleeping Computer
Microsoft revealed today that its security teams are tracking more than 100 threat actors deploying ransomware during attacks.


ZDNet
Microsoft warns admins to keep Exchange Server updated as the platform is constantly being targeted by attackers.


The Hacker News
Microsoft urges customers keep their servers up to date and implement additional security measures, such as enabling Windows Extended Protection.


Bleeping Computer
Microsoft urged customers today to keep their on-premises Exchange servers patched by applying the latest supported Cumulative Update (CU) to have them always ready to deploy an emergency security update.

DarkReading
The growing use of mobile devices for MFA and the proliferation of 5G and VoIP in general could result in more attacks in future, experts say.


ZDNet
Microsoft kicks off 2023 with a bumper January Patch Tuesday.


Bleeping Computer
More than 60,000 Microsoft Exchange servers exposed online are yet to be patched against the CVE-2022-41082 remote code execution (RCE) vulnerability, one of the two security flaws targeted by ProxyNotShell exploits.

CSO
Log4Shell is likely to remain a favored vulnerability to exploit as organizations lack visibility into their software supply chains.


The Record
The Guacamaya leaks in September exposed corruption, militarization and surveillance throughout Latin America.


The Hacker News
An analysis of the FIN7 cybercrime syndicate has revealed its organizational hierarchy and role as a partner in various ransomware attacks.

SecurityWeek
Play ransomware operators seen achieving RCE on Exchange server with requests made through OWA endpoint, bypassing Microsoft’s ProxyNotShell mitigations.


CyberSecurity Dive
Fears of the next SolarWinds or Log4j-style incident hitting over the holidays have some cybersecurity experts on edge.


DarkReading
The custom malware used by the state-backed Iranian threat group Drokbk has so far flown under the radar by using GitHub as a "dead-drop resolver" to more easily evade detection.


The Hacker News
China-linked APT group BackdoorDiplomacy has been spotted launching sophisticated cyber attacks against telecom companies in the Middle East.


DarkReading
Though there have been fewer than expected publicly reported attacks involving the vulnerability, nearly three-quarters of organizations remain exposed to it.


Naked Security
Latest episode – security expert John Shier explains what the real-life cybercrime stories in the Sophos Threat Report can teach us


Naked Security
Review your servers, your patches and your authentication policies – there’s a proof-of-concept out


The Hacker News
More than 1,300 companies around the world were attacked by the Hive ransomware-as-a-service (RaaS) scheme, netting the hackers $100 million in illici


Security Affairs
Cyber espionage group Worok abuses Dropbox API to exfiltrate data via using a backdoor hidden in apparently innocuous image files. Researchers from cybersecurity firm Avast observed the recently discovered espionage group Worok abusing Dropbox API to exfiltrate data via using a backdoor hidden in apparently innocuous image files. The experts started their investigation from the analysis published […]

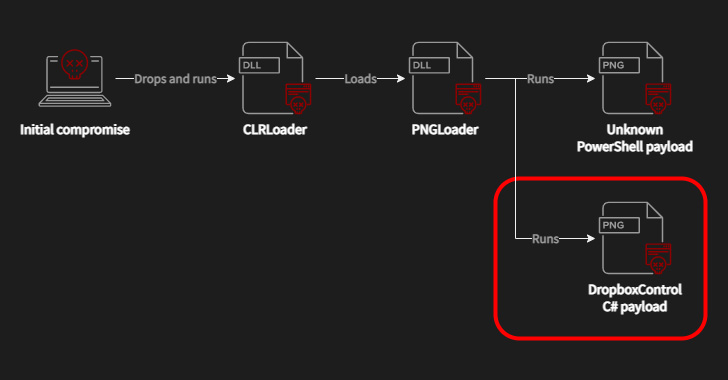
The Hacker News
A recently discovered cyber espionage group dubbed Worok has been abusing Dropbox API to exfiltrate data stolen by malware hiding in image files.


Cyber Security News
Experts at Avast, who built on the discoveries of ESET, the first to notice and report on the threat group known as “Worok”, conceals malware within PNG images to silently infect victims' computers with information-stealing malware.


Naked Security
In all the excitement, we kind of lost track ourselves. Were there six 0-days, or only four?


Trend Micro
Our blog entry provides a look at an attack involving the LV ransomware on a Jordan-based company from an intrusion analysis standpoint


Naked Security
Latest episode – listen and learn now (or read and revise, if the written word is your thing)…


The Record
Microsoft updated the guidance it provided for CVE-2022-41040 and CVE-2022-41082 but researchers are concerned it still not enough.


The Hacker News
Microsoft has revised its mitigation measures for the newly disclosed and actively exploited zero-day vulnerabilities in Exchange Server.


DarkReading
Researchers had discovered that Microsoft's original mitigation steps for the so-called "ProxyNotShell" flaws was easily bypassed.

SecurityWeek
A mitigation proposed by Microsoft and others for the Exchange server vulnerabilities tracked as ProxyNotShell can be easily bypassed.

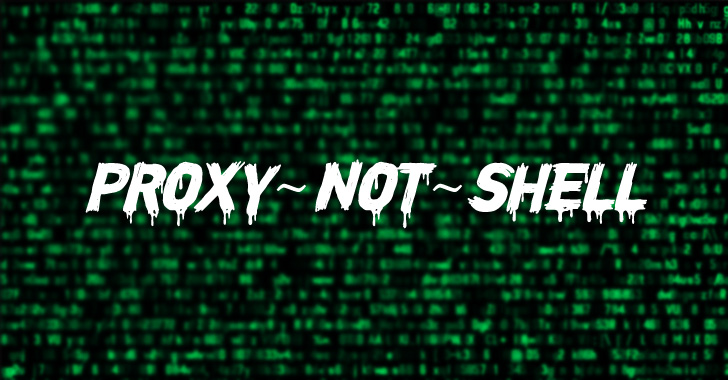
The Hacker News
There is a new exploit, ProxyNotShell, being exploited in the wild to take advantage of the recent Microsoft exchange vulnerabilities.


CSO
No permanent fix for the Exchange Server vulnerabilities is yet available, but other steps can mitigate the risk.

SecurityWeek
Microsoft believes a single state-sponsored threat group — linked by others to China — has exploited the new Exchange zero-days to hack less than 10 organizations.

SecurityWeek
CISA has added to its KEV catalog a recent Atlassian Bitbucket flaw and two Microsoft Exchange zero-days.


CyberSecurity Dive
The actor, which Microsoft says is state sponsored, installed Chopper web shells to gain hands-on-keyboard access, conduct Active Directory reconnaissance and exfiltrate data.


Security Affairs
A hacker group called Guacamaya stole classified government information from multiple military and government agencies across several Latin American countries. Among the data stolen by a group of hackers called Guacamaya (macaw in Spanish) there was a huge trove of emails from Mexico’s Defense Department, which shed the light on the poor resilience of the […]


Naked Security
Who’s affected, what you can do while waiting for Microsoft’s patches, and how to plan your threat hunting…


The Hacker News
Microsoft says state-sponsored hackers likely exploited the recently disclosed zero-day vulnerabilities in Exchange servers.


Security Affairs
A cyberespionage group, tracked as Witchetty, used steganography to hide a previously undocumented backdoor in a Windows logo. Broadcom’s Symantec Threat Hunter Team observed a threat actor, tracked as Witchetty, using steganography to hide a previously undocumented backdoor in a Windows logo. The group used the backdoor in attacks against Middle Eastern governments. The cyber […]


Ars Technica
Microsoft said it's working on an accelerated schedule to roll out a patch.


DarkReading
While ransomware seems stalled, business email compromise (BEC) attacks continue to make profits from the ProxyShell and Log4j vulnerabilities, nearly doubling in the latest quarter.


Infosecurity News
The group continued to use the LookBack backdoor, but also several new types of malware


The Record
Mexico's president confirmed a widely reported cyberattack that leaked sensitive documents from militaries across Central and South America.


The Record
Microsoft confirms it is aware of “limited targeted attacks” using vulnerabilities.


DarkReading
The "ProxyNotShell" security vulnerabilities can be chained for remote code execution and total takeover of corporate email platforms.


Naked Security
Double-play 0-day in Exchange – what you need to know, and what you can do

SecurityWeek
Microsoft has confirmed that it’s aware of two Exchange Server zero-day vulnerabilities being exploited in targeted attacks.

SecurityWeek
Part of the Cicada group, Witchetty has been observed progressively updating its toolset in recent attacks against Middle Eastern and African targets.

The Hacker News
A threat actor targeting Middle Eastern governments has been observed using a steganographic trick to hide an undocumented backdoor in a Windows logo.

SecurityWeek
Researchers report seeing new Microsoft Exchange zero-day being exploited in the wild, but it may just be a variation of the old ProxyShell exploit.


Security Affairs
Security researchers are warning of a new Microsoft Exchange zero-day that are being exploited by malicious actors in the wild. Cybersecurity firm GTSC discovered two Microsoft Exchange zero-day vulnerabilities that are under active exploitation in attacks in the wild. Both flaws were discovered by the researchers as part of an incident response activity in August […]


The Hacker News
Researchers warn of a new unpatched zero-day vulnerability in Microsoft Exchange servers that is being exploited by attackers to achieve RCE.


CyberSecurity Dive
One vulnerability is a server-side request forgery, while the second allows remote-code execution when an attacker has access to PowerShell.


Bleeping Computer
Threat actors are exploiting yet-to-be-disclosed Microsoft Exchange zero-day bugs allowing for remote code execution, according to claims made by security researchers at Vietnamese cybersecurity outfit GTSC, who first spotted and reported the attacks.


Bleeping Computer
Threat actors are exploiting yet-to-be-disclosed Microsoft Exchange zero-day bugs allowing for remote code execution, according to claims made by security researchers at Vietnamese cybersecurity outfit GTSC, who first spotted and reported the attacks.


Bleeping Computer
Threat actors are exploiting yet-to-be-disclosed Microsoft Exchange zero-day bugs allowing for remote code execution, according to claims made by security researchers at Vietnamese cybersecurity outfit GTSC, who first spotted and reported the attacks.


Bleeping Computer
Security researchers have discovered a malicious campaign by the 'Witchetty' hacking group, which uses steganography to hide a backdoor malware in a Windows logo.


DarkReading
APT group Witchetty (aka LookingFrog) has exploited the ProxyShell and ProxyLogon vulnerabilities to gain initial access and deploy new custom cyber tools against government agencies and a stock exchange.


Infosecurity News
US authorities indict and sanction in fresh crackdown

SecurityWeek
Government agencies in the US, UK, Canada, and Australia say APTs associated with Iran’s IRGC have been engaging in data encryption and extortion operations.


DarkReading
Authorities are cracking down on persistent cybercriminal attacks from APTs associated with Iran's Islamic Revolutionary Guard Corps.


The Hacker News
United States charges 3 Iranian hackers who carried out ransomware attacks on hundreds of organizations around the world and imposes sanctions on

SecurityWeek
ESET has identified a new cyberespionage group that has been targeting private and public entities in Asia, the Middle East, and Africa since 2020.


DarkReading
The threat actor — whose techniques and procedures do not match known groups — has created custom attack tools, including a program that hides scripts in .PNG images.


Bleeping Computer
A newly discovered cyber-espionage group has been hacking governments and high-profile companies in Asia since at least 2020 using a combination of custom and existing malicious tools.


The Hacker News
Researchers uncover targeted attacks by cyber espionage hacking group Worok against high-profile Asian companies and governments.


DarkReading
The operators of the emerging cross-platform ransomware BianLian increased their command and control infrastructure this month, indicating an acceleration in their operational pace.


Infosecurity News
The threat actor using the common Go programming language and a custom toolkit claims twenty victims

.jpg)
The Hacker News
Researchers describe the operations and techniques used by the operators of the emerging cross-platform BianLian ransomware.


Bleeping Computer
The BlackByte ransomware is back with version 2.0 of their operation, including a new data leak site utilizing new extortion techniques borrowed from LockBit.

SecurityWeek
New research shows that cyberattack victims are often attacked by multiple adversaries – usually, in rapid succession but sometimes simultaneously.


The Record
The most commonly seen malware strains in 2021 include Agent Tesla, Qakbot, TrickBot, GootLoader and several others, according to a new list released by CISA and the Australian Cyber Security Centre.


CyberSecurity Dive
Attackers are scanning for vulnerabilities in unpatched systems within 15 minutes, stressing the pace and scale of the threat.
Loading more articles....