
The Hacker News
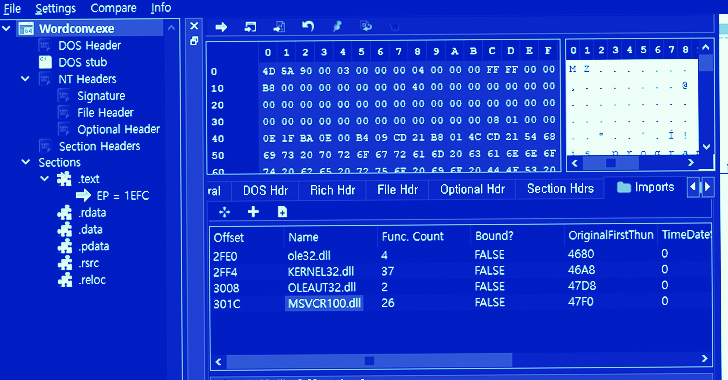
New Malicious PyPI Packages Caught Using Covert Side-Loading Tactics
Malicious packages lurking in open-source repositories. Discover how DLL side-loading is the latest technique used to evade security software.

The Hacker News
Malicious packages lurking in open-source repositories. Discover how DLL side-loading is the latest technique used to evade security software.


The Hacker News
DLL side-loading, a tactic used by malicious actors, helps Quasar RAT and other malware evade detection, steal data.

Infosecurity News
Uptycs researchers said the technique exploits Microsoft files to execute malicious commands


The Cyber Express
Researchers have discovered a sophisticated phishing campaign meticulously crafted to target cryptocurrency users. This elaborate scheme, equipped with the notorious


Security Affairs
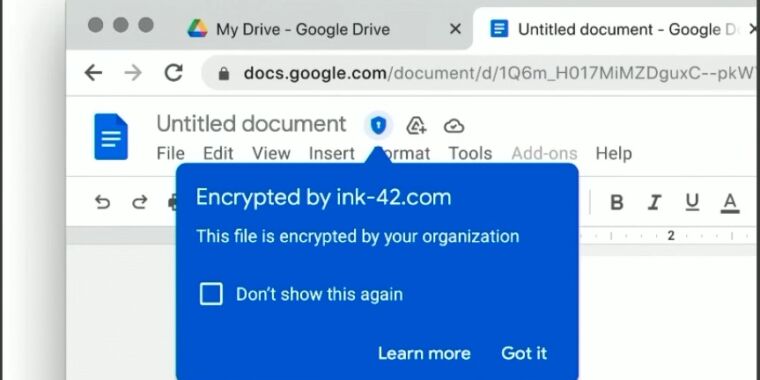
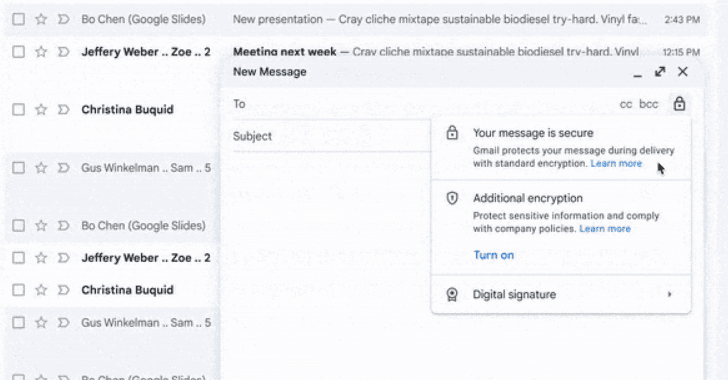
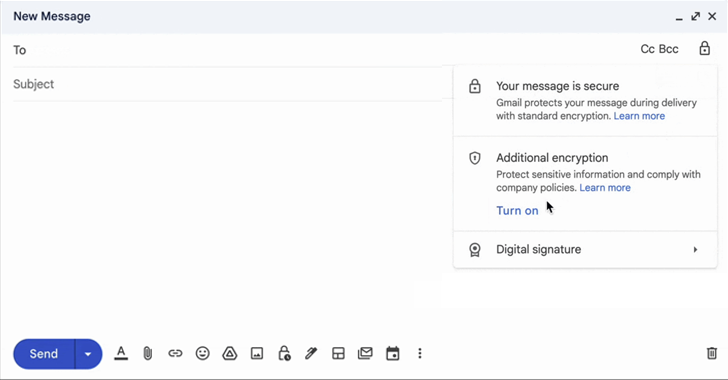
Gmail client-side encryption (CSE) is now available for Workspace Enterprise Plus, Education Plus, and Education Standard customers. Google announced that Gmail client-side encryption (CSE) is now available for all Google Workspace Enterprise Plus, Education Plus, and Education Standard customers. In December, Google announced end-to-end encryption for Gmail (E2EE), with Gmail client-side encryption beta users can […]

SecurityWeek
Google has announced the beta availability of client-side encryption in Gmail for Google Workspace customers.


Bleeping Computer
Gmail client-side encryption (CSE) is now generally available for Google Workspace Enterprise Plus, Education Plus, and Education Standard customers.


ZDNet
Some Workspace customers can apply for the client-side encryption for Gmail beta until January 20.

SecurityWeek
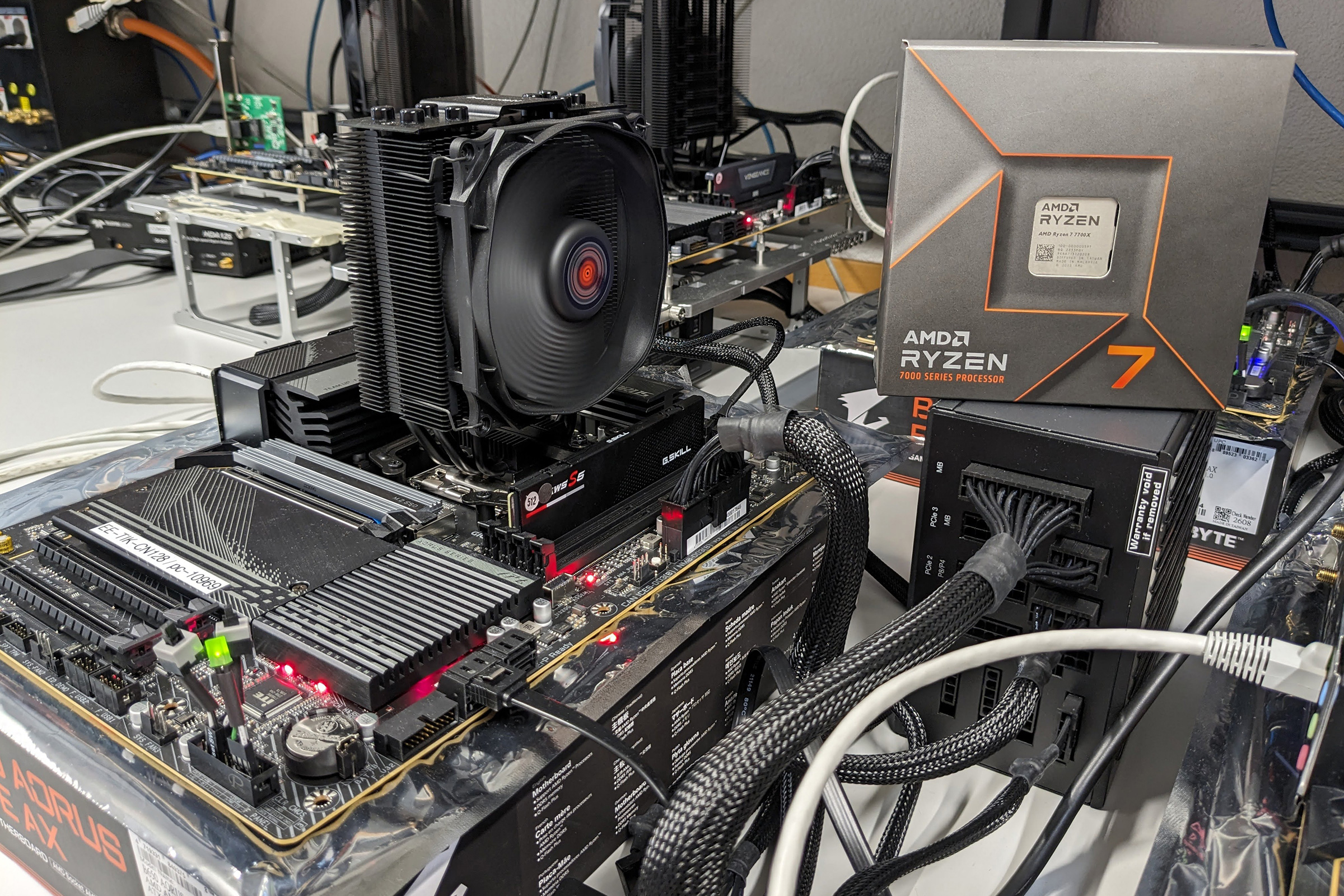
Researchers have disclosed the details of a new locally exploitable side-channel attack targeting AMD CPUs named Inception


Latest Hacking News
With the recent Google Meet update, Google has strengthened call security for its users. Google Meet users can now use the client-side encryption to secure their calls even with non-Google users. Google Meet Launches Client-Side Encryption According

Latest Hacking News
Researchers have identified a new side-channel attack impacting all existing processors. Named “Collide+Power”, this side-channel attack exploits target CPU’s measured power consumption following a collision between the attackers’ and the other apps’ datasets in cache


Bleeping Computer
Google Workspace (formerly G Suite) has been updated with client-side encryption and new Google Drive phishing and malware content protection.

SecurityWeek
AWS has announced that server-side encryption is now automatically enabled for all Amazon S3 buckets.

CSO
The method, developed by MIT, improves on performance of alternative schemes to mitigate side-channel memory attack risks.

Ars Technica
New service occupies a middle ground between E2EE and mere server-side encryption


SecurityWeek
C/side has emerged from stealth mode with $1.7 million in pre-seed funding from Scribble Ventures and angel investors


Infosecurity News
Researchers detail the DLL side-loading technique used to deploy malware that facilitates credential theft and lateral movement


The Hacker News
Researchers Demonstrate New Side-Channel Attack on Homomorphic Encryption | Read latest news headlines on latest news and technical coverage on cybersecurity, infosec and hacking.

Bleeping Computer
A new side-channel attack impacting multiple generations of Intel CPUs has been discovered, allowing data to be leaked through the EFLAGS register.


Security Affairs
Google researcher Daniel Moghimi devised a new side-channel attack technique, named Downfall, against Intel CPU. Google researcher Daniel Moghimi devised a new side-channel attack technique Intel CPU, named Downfall, that relies on a flaw tracked as CVE-2022-40982. An attacker can exploit this vulnerability to access and steal data from other users who share the same […]

SecurityWeek
LockBit ransomware operators or affiliates are leveraging Windows Defender to decrypt and load Cobalt Strike payloads.

SecurityWeek
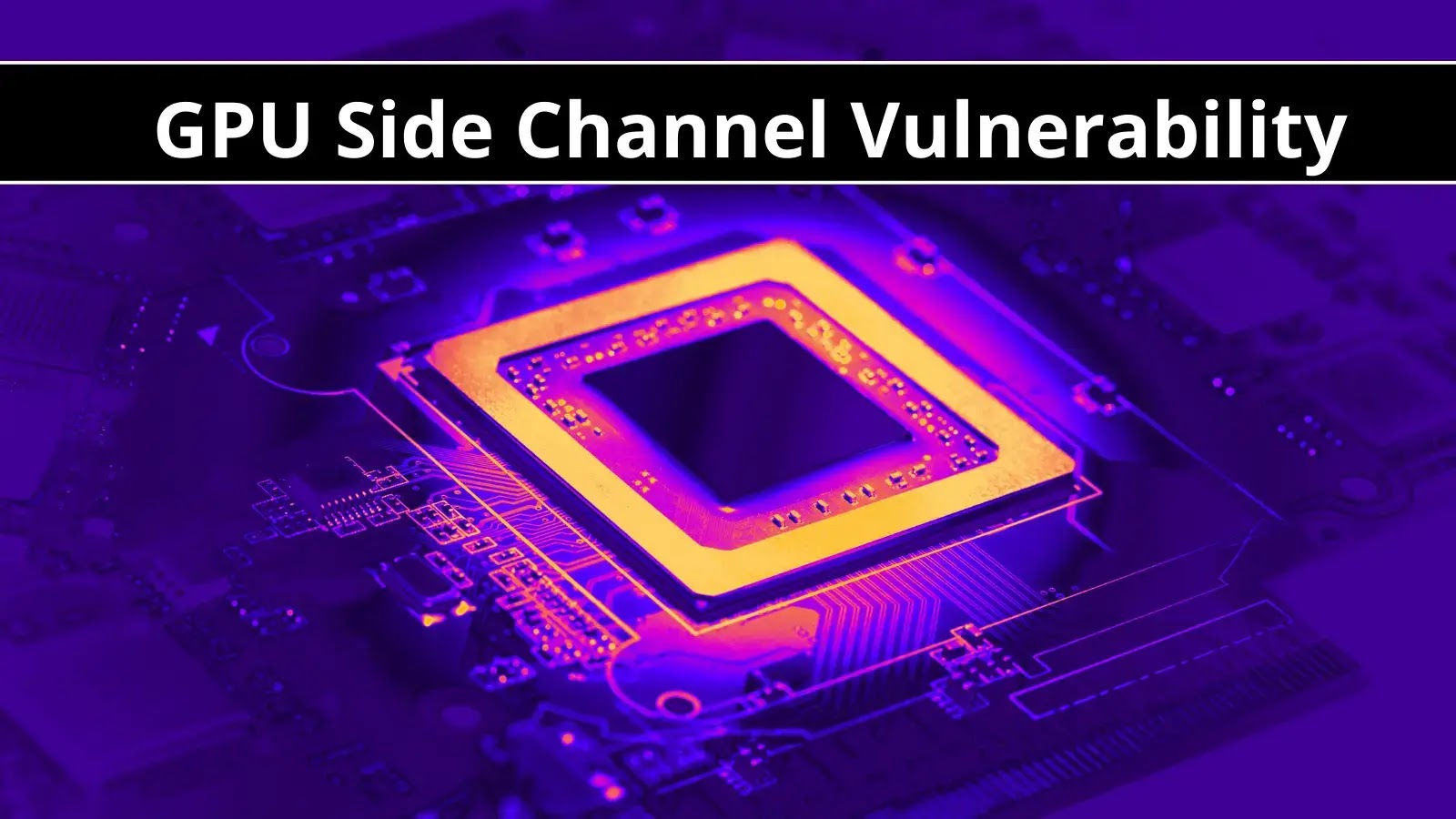
A group of academic researchers has devised a side-channel attack targeting architectures that rely on multiple graphics processing units (GPUs) for resource-intensive computational operations.

Bleeping Computer
A new side-channel attack known as Hertzbleed allows remote attackers to steal full cryptographic keys by observing variations in CPU frequency enabled by dynamic voltage and frequency scaling (DVFS).

SecurityWeek
GPUs from AMD, Apple, Arm, Intel, Nvidia and Qualcomm are vulnerable to a new type of side-channel attack named GPU.zip.

Cyber Security News
Google announced that CSE (client-side encryption) is now generally available for Gmail and Calendar users. This will let more companies become the sole arbiters.

The Hacker News
Your GPU might be leaking data. GPU Side-Channel Vulnerability Exposes Modern GPUs to Data Leakage. Learn how this could impact your online privacy.


Bleeping Computer
Google is updating the client-side encryption mechanism for Google Meet to allow external participants, including those without Google accounts, to join encrypted calls.


The Hacker News
Researchers unveil a new class of side-channel attacks dubbed 'Hertzbleed" that affect all modern AMD and Intel processors.

The Hacker News
Collide+Power, Downfall, and Inception! New side-channel attacks exploit vulnerabilities in modern CPUs.

The Hacker News
North Korean Lazarus Group remains relentless in targeting vulnerable Microsoft IIS servers, utilizing DLL side-loading techniques to deploy malware.

SecurityWeek
Academic researchers describe Hertzbleed, a new Intel and AMD CPU side-channel attack that leverages remote timing to extract secrets from the targeted system.


Security Affairs
Researchers demonstrated a new side-channel attack, named GoFetch, against Apple CPUs that could allow an attacker to obtain secret keys.


The Hacker News
Google has announced the general availability of client-side encryption (CSE) for Gmail and Calendar.


Bleeping Computer
Researchers from four American universities have developed a new GPU side-channel attack that leverages data compression to leak sensitive visual data from modern graphics cards when visiting web pages.


Security Affairs
Qakbot malware operators are using the Windows Calculator to side-load the malicious payload on target systems. Security expert ProxyLife and Cyble researchers recently uncovered a Qakbot campaign that was leveraging the Windows 7 Calculator app for DLL side-loading attacks. Dynamic-link library (DLL) side-loading is an attack method that takes advantage of how Microsoft Windows applications handle DLL […]

The Hacker News
Gmail just got a whole lot more secure with Google's new client-side encryption! With the new feature, emails are encrypted on your end.


Security Affairs
Chinese LuoYu Hackers Using Man-on-the-Side Attacks to Deploy WinDealer Backdoor An “extremely sophisticated” China-linked APT tracked as LuoYu was delivering malware called WinDealer via man-on-the-side attacks. Researchers from Kaspersky have uncovered an “extremely sophisticated” China-linked APT group, tracked as LuoYu, that has been observed using a malicious Windows tool called WinDealer. LuoYu has been active since at […]

Cyber Security News
A new research paper has been published that mentions a side-channel attack to leak sensitive visual data from modern GPU cards when visiting a malicious website.


The Hacker News
LuoYu, an "extremely sophisticated" Chinese-speaking APT hacker group, has been observed using man-on-the-side attacks to deploy a Windows backdoor.


SecurityWeek
A new power side-channel attack named Collide+Power can allow an attacker to obtain sensitive information and it works against any modern CPU.

Krebs on Security
A new data leak that appears to have come from one of China's top private cybersecurity firms provides a rare glimpse into the commercial side of China's many state-sponsored hacking groups. Experts say the leak illustrates how Chinese government agencies…


The Record
Client-side scanning technology, which involves checking the content of a message before it's encrypted, can't guarantee a user's confidentiality, experts say.


Bleeping Computer
Reddit is investigating a major outage that prevents users worldwide from accessing the social network's website on native mobile apps.

Bleeping Computer
A new software-based power side-channel attack called 'Collide+Power' was discovered, impacting almost all CPUs and potentially allowing data to leak. However, the researchers warn that the flaw is low-risk and will likely not be used in attacks on end users.


DarkReading
Although the unauthenticated Java deserialization flaw has been known since 2015, GWT apps remain vulnerable to malicious server-side code execution, new research says.


Security Affairs
Threat actors rely on the ‘versioning’ technique to evade malware detections of malicious code uploaded to the Google Play Store. Google Cybersecurity Action Team (GCAT) revealed that threat actors are using a technique called versioning to evade malware detection implemented to detect malicious code uploaded to the Google Play Store. The technique is not new […]


Security Affairs
Hertzbleed attack: Researchers discovered a new vulnerability in modern Intel and AMD chips that could allow attackers to steal encryption keys. Researchers from University of Texas, University of Illinois Urbana-Champaign, and the University of Washington, devised a new side-channel attack technique dubbed Hertzbleed that could allow remote attackers to steal encryption keys from modern Intel […]


Infosecurity News
Lawyers for the bloc issue warning


The Hacker News
Deep session inspection offers unparalleled protection against phishing attacks. Learn how it works.


DarkReading
Burned-out cybersecurity professionals dealing with layoffs and stressful working conditions are increasingly finding a better way to earn a buck: cybercrime.

DarkReading
A novel timing attack allows remote attackers with low privileges to infer sensitive information by observing power-throttling changes in the CPU.


Infosecurity News
The move will facilitate compliance procedures for private and public sector organizations


CSO
The iLeakage proof of concept targets Apple silicon devices running Safari, demonstrating techniques that improve on Sceptre and MeltDown exploits and demonstrate continuing vulnerabilities in modern CPUs.


CyberSecurity Dive
CrowdStrike researchers discovered a new attack method by the Play ransomware actors that uses Outlook Web Access and leverages additional tools to maintain access.


Latest Hacking News
A team of researchers has developed a new attack strategy that analyzes users’ typing patterns to determine keystrokes. This acoustic attack can deduce keystrokes with better accuracy by specifically deciphering the typing patterns while ignoring


Latest Hacking News
SMS delivery reports not only let the sender know about the message receipt, but can also leak the recipient’s location. This is what researchers have demonstrated in their recent study, showing how receiving a silent


Security Affairs
North Korea-linked APT group Lazarus actor has been targeting vulnerable Microsoft IIS servers to deploy malware. AhnLab Security Emergency response Center (ASEC) researchers reported that the Lazarus APT Group is targeting vulnerable versions of Microsoft IIS servers in a recent wave of malware-based attacks. Once discovered a vulnerable ISS server, the attackers leverage the DLL side-loading […]


Cyber Security News
Banking malware is a malicious program that is mainly designed and used by threat actors to steal the following sensitive financial information from victims' computers or mobile devices.


The Record
Researchers in Sweden say they found a vulnerability in a “quantum safe” algorithm deemed the gold standard for future cryptographic systems.


CyberSecurity Dive
Researchers from Orca Security said no authentication was required in two of the four instances.


The Hacker News
LCNC apps and RPA can leave your business exposed to security risks similar to traditional development.


Bleeping Computer
If you've been experiencing Tor network connectivity and performance issues lately, you're not the only one since many others have had issues with onion sites loading slower or not loading at all.


ThreatPost
Scammers are bypassing Apple's App Store security, stealing thousands of dollars’ worth of cryptocurrency from the unwitting, using the TestFlight and WebClips programs.

Bleeping Computer
The Complete 2021 Superstar Backend Developer helps you master this field, with 13 courses covering key languages and frameworks. For a limited time, you can pick up the training for just $23.99 with code VIP40.


Naked Security
The security error was in the error handling system that was supposed to catch potential security errors…


SecurityWeek
Japan’s Port of Nagoya this week suspended cargo loading and unloading operations following a ransomware attack.

Cyber Security News
The rapid surge in LLMs across several industries and sectors has raised critical concerns about their safety, security, and potential for misuse.


ThreatPost
The year wasn't ALL bad news. These sometimes cringe-worthy/sometimes laughable cybersecurity and other technology stories offer schadenfreude and WTF opportunities, and some giggles.


Bleeping Computer
Google has launched a new pilot program to fight financial fraud by blocking the sideloading of Android APK files that request access to risky permissions.

Infosecurity News
New side-channel attacks reportedly use frequency side channels to extract cryptographic keys


Bleeping Computer
Major websites around the world are either completely down or not loading properly in a global outage.

The Hacker News
Browser security has evolved! Say goodbye to Browser Isolation's limitations and hello to the future of web security.


CyberScoop
Links in tooling, crypto wallets and even attacking victims simultaneously strongly suggest a link, researchers say.


Cyber Security News
Japan’s largest port NAGOYA was attacked by pro-Russian hackers, disrupting the loading of Toyota parts by ransomware attack.


SC Magazine
Malware first identified in 2014 re-emerges and gets delivered by the criminal proxy service Faceless, now growing at 7,000 users per week.


DataBreaches
Brandon Vigliarolo reports: If you can’t join them, then you may as well try to beat them – at least if you’re a talented security engineer...


The Hacker News
The Dark Web's anonymity attracts a variety of users. Explore the various techniques used to identify the individuals behind these sites and personas.


Cyber Security News
Watch out for harmful Finnish SMS which tricks Android device users into loading banking malware by dialing a spoofed service number.

Bleeping Computer
The operators of the QBot malware have been using the Windows Calculator to side-load the malicious payload on infected computers.


ThreatPost
Two powerful trojans with spyware and RAT capabilities are being delivered in side-by-side campaigns using a common infrastructure.

Ars Technica
Fixing newly discovered side channel will likely take a major toll on performance.


Bleeping Computer
Microsoft has addressed a new known issue causing DNS stub zones loading failures that could lead to DNS resolution issues on Windows Server 2019 systems.


Bleeping Computer
Google is rolling out a server-side fix for a known issue affecting the Chrome browser that causes webpage content to temporarily disappear when users change between open tabs.


SC Magazine
Data memory-dependent prefetching can enable side-channel extraction of cryptographic secrets.

Cyber Security News
By using Windows Calculator, the QBot malware operators are able to side-load their malicious payload onto the computers that are compromised. In short, Windows Calculator is being used to distribute dangerous code.


Bleeping Computer
The team behind the Matrix open standard and real-time communication protocol has announced the release of its second major version, bringing end-to-end encryption to group VoIP, faster loading times, and more.


Bleeping Computer
A new variant of the BlackGuard stealer has been spotted in the wild, featuring new capabilities like USB propagation, persistence mechanisms, loading additional payloads in memory, and targeting additional crypto wallets.


Ars Technica
All non-Google chat GPTs affected by side channel that leaks responses sent to users.


SecurityWeek
New iLeakage side-channel speculative execution attack exploits Safari to steal sensitive information from Macs and iPhones.

Cyber Security News
Microarchitectural side-channel attacks misuse shared processor state to transmit information between security domains.


ZDNet
Optimize Mac Storage is dangerous. Turns out that in concert with iCloud and Time Machine, it can make your files go poof. Ask me how I know.


ZDNet
Google's client-side encryption for Gmail and Calendar reaches general availability, but not for all Gmail users.


Bleeping Computer
OpenAI's ChatGPT is down for many people worldwide, with users facing multiple problems, including being unable to access their accounts, having their chat history come up empty, and the chat screens not loading properly.


The Hacker News
Academics have developed a powerful "deep learning-based acoustic side-channel attack" that can classify laptop keystrokes.

Ars Technica
A previously unknown compression side channel in GPUs can expose images thought to be private.

.webp)
Cyber Security News
Google has announced that external participants without Google accounts can now join client-side encrypted Google Meet calls.

Ars Technica
Key-leaking side channels are a fact of life. Now they can be done by video-recording power LEDs.


DarkReading
A team has found that the Crystals-Kyber encryption algorithm is open to side-channel attacks, under certain implementations.


The Hacker News
Researchers have discovered new side-channel attacks on the CRYSTALS-Kyber encryption algorithm, which the U.S. government selected last year.


CyberNews
A feature that makes Apple M-series processors faster also leaves them vulnerable to a new side-channel attack that cannot be patched, according to research.
Loading more articles....