

The Hacker News
MDR: Empowering Organizations with Enhanced Security
Worried about your organization's security? Managed Detection and Response (MDR) is the key!


The Hacker News
Worried about your organization's security? Managed Detection and Response (MDR) is the key!

The Hacker News
Here are just seven reasons why you (yes, you – the CISO or Security Lead of an SME) should consider searching for an MDR provider.


The Hacker News
Overcoming the talent gap in #cybersecurity is crucial for defending against new threats. Discover how Managed Detection and Response (#MDR) services

SecurityWeek
HelpSystems has agreed to acquire Alert Logic, a provider of managed detection and response (MDR) services for an undisclosed sum


CSO
Expel MDR for Kubernetes addresses three core layers of Kubernetes applications: configuration, control panel, and run-time security.


Trend Micro
This blog entry will examine Trend Micro MDR team's investigation that successfully uncovered the intrusion sets employed by Earth Kapre in a recent incident, as well as how the team leveraged threat intelligence to attribute the extracted evidence to the cyberespionage threat group.

SecurityWeek
Warburg Pincus-backed eSentire is the latest entrant to the cybersecurity "unicorn" list.


CyberSecurity Dive
It's not just the front door businesses need to protect. Organizations also have to recognize the damage threat actors can do once they’re inside.


CSO
Ontinue ION promises faster detection and response, deeper understanding of customer’s environments, and the ability to maximize Microsoft security investments.

Cyber Security News
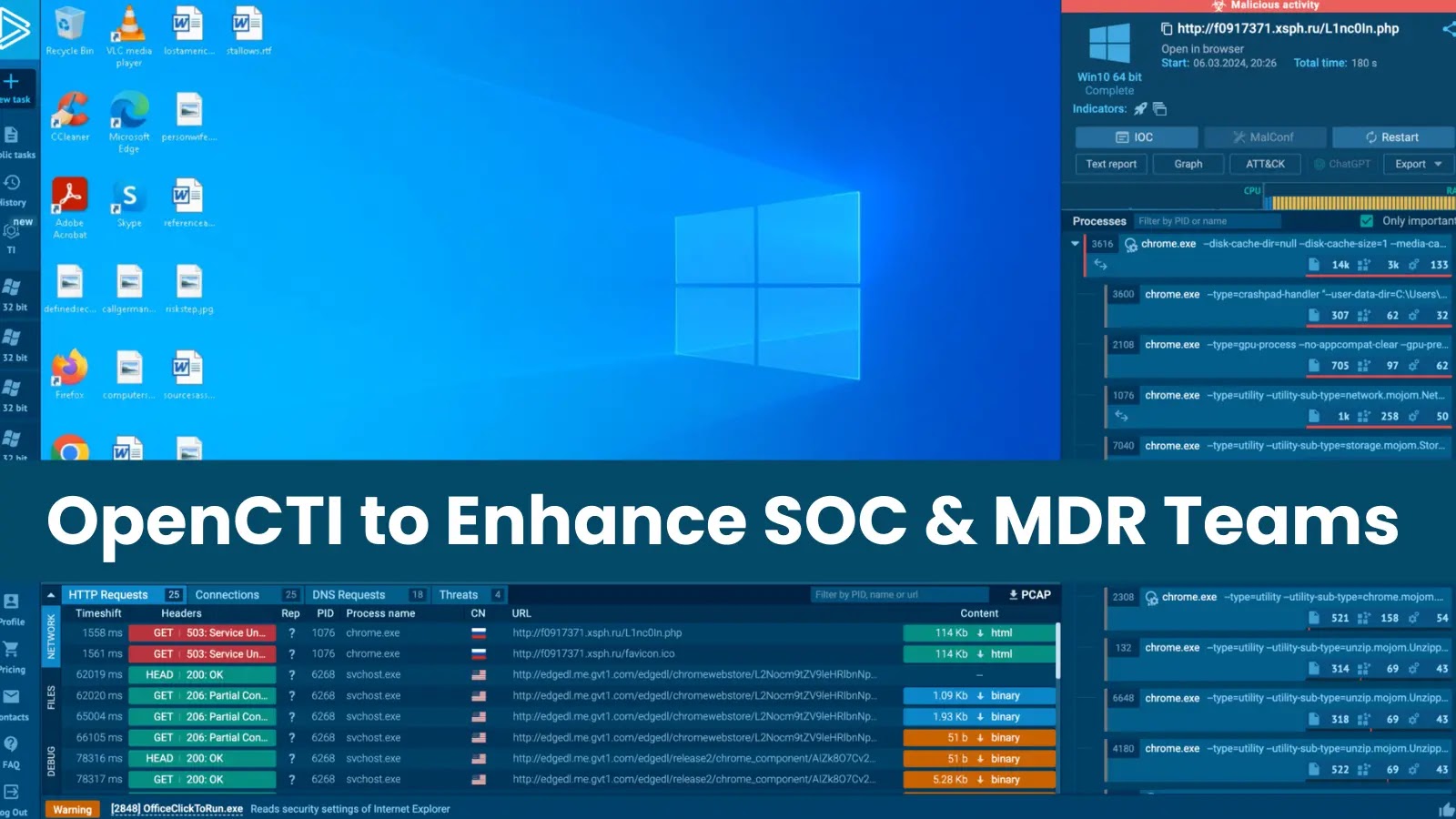
ANY.RUN integrates with OpenCTI to streamline threat analysis, which allows enriching OpenCTI observations with data.


CSO
Kyndryl’s new managed security services include managed detection and response (MDR) and security information and event management (SIEM).


CSO
Dell Technologies has added improved MDR capabilities, cloud-based component verification, and a new cyber recovery solution along with a partnered threat management offering.


Security Affairs
VMware’s Carbon Black Managed Detection and Response (MDR) team observed a surge of TrueBot activity in May 2023. Researchers at VMware’s Carbon Black Managed Detection and Response (MDR) team warn of a surge of TrueBot activity in May 2023. Truebot has been active since 2017 and some researchers linked it to the Silence Group, while a […]

CSO
MDR firm claims solution is the industry’s only vendor-agnostic open XDR solution that supports identity threat detection and response.

SecurityWeek
Managed detection and response (MDR) start-up Huntress has secured a $40 million debt financing round to speed up global expansion plans.


DarkReading
Red Canary, a leader in Managed Detection and Response (MDR), is one of 15 providers that participated in the first-ever MITRE Engenuity™ ATT&CK® Evaluations for Managed Services.


The Cyber Express
By Andrew Hural, VP of Managed Detection and Response, UnderDefense Do you know how firefighters famously run to their stations


CSO
Critical Start’s new offering is designed to handle security teams with specialized detection and response tooling for operational technology systems.


The Hacker News
In the age of DevOps, CISOs must ensure security is integrated from the start. Discover strategies for effective collaboration with DevOps teams to pr

HACKRead
Microsoft Teams targeted for phishing and malware attacks. Learn how to protect your organization against these evolving cyber threats.


CSO
Cybersecurity companies Trustwave and Trellix say they want to help end users simplify their systems in the face of a complicated threat environment.

The Hacker News
Guide: Alert Overload and Handling for Lean IT Security Teams


Bleeping Computer
US cybersecurity firm Rapid7 has disclosed that some source code repositories were accessed in a security incident linked to the supply-chain attack that recently impacted customers of the popular Codecov code coverage tool.

Trend Micro
Running real-world attack simulations can help improve organizations' cybersecurity resilience


Trend Micro
The Trend Micro™ Managed XDR team addressed a stealthy multilayered attack that progressed from an exploited endpoint vulnerability to the use of legitimate remote access tools including Remote Desktop Protocol (RDP) as its final means of intrusion.


DarkReading
The deal will allow Trustwave to expand its global reach.


DarkReading
The new company will focus on cybersecurity services as a top-10 managed security service provider, but must expand outside the low-margin managing of security into detection and response.


SecurityWeek
Adlumin, a startup working on technology to boost security for mid-market firms, has banked $70 million in new funding led by SYN Ventures.


Infosecurity News
The firm said the tools used to attack Cisco were also deployed to compromise one of its clients

Cyber Security News
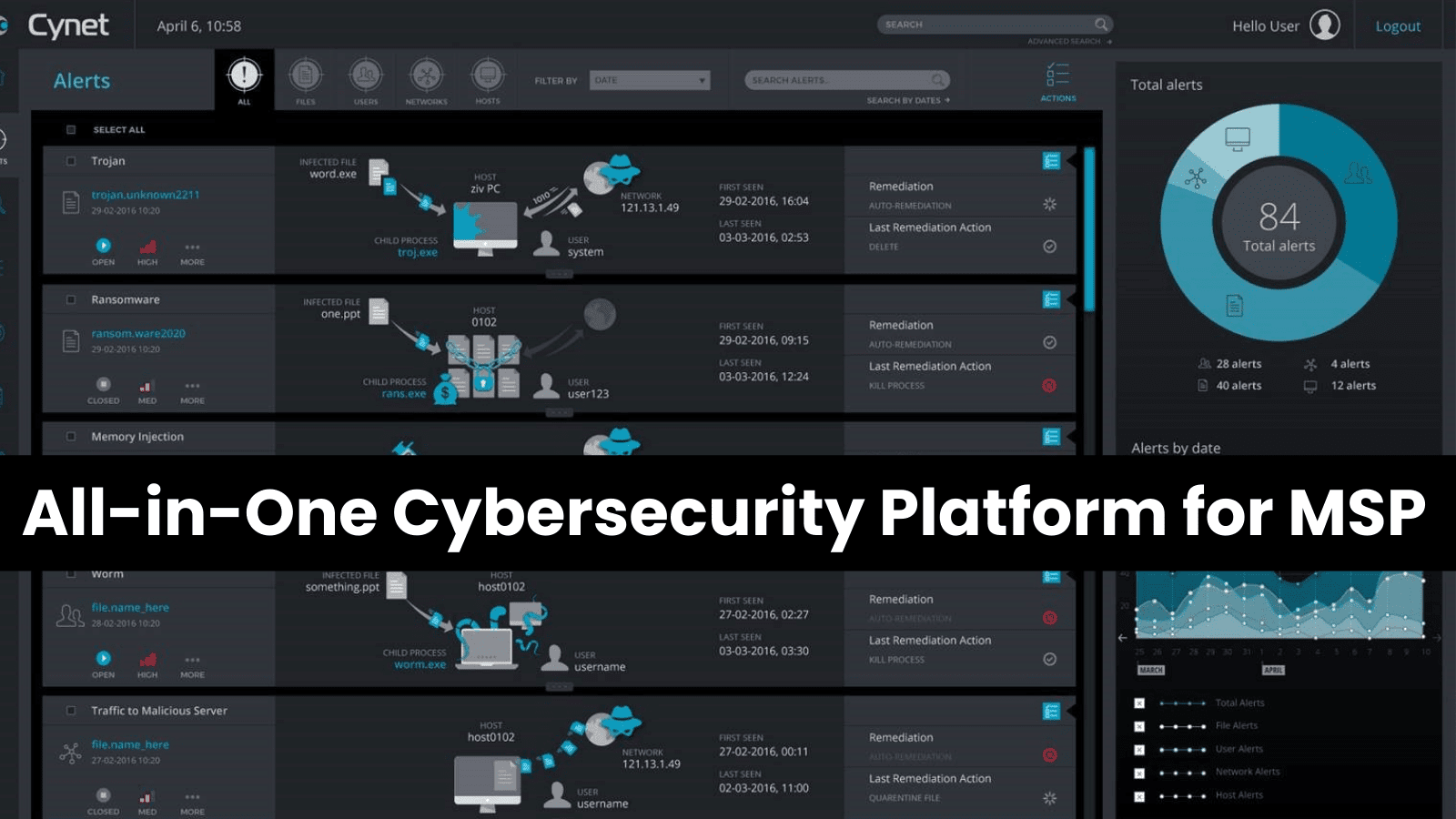
Managed service providers (MSPs) are on the front lines of soaring demand for cybersecurity services as cyberattacks increase in volume and sophistication.


Infosecurity News
Malware and botnet detections also soar

Infosecurity News
Attempts can lead to unauthorized access to important company resources


ZDNet
This acquisition augments Google Project Zero with an infusion of sophisticated practitioners in forensics, malware analysis, threat intelligence, and security research.


DarkReading
The results are labor-intensive to parse, so knowing how to interpret them is key, security experts say.


SecurityWeek
Noteworthy stories that might have slipped under the radar: Volkswagen hacked by Chinese threat group, DDoS service shut down, Rubrik IPO.


SecurityWeek
Hundreds of companies and organizations showcased their products and services this week at the 2023 edition of Black Hat in Las Vegas.

.webp)
Cyber Security News
Rhysida, a new ransomware group, hit its first victim in May 2023. They use their ransomware, offered as RaaS (Ransomware-as-a-Service), with at least 50 global victims listed on their website.

.webp)
Cyber Security News
Hacking group known as Earth Kapre, referred to as RedCurl & Red Wolf, targeting across the globe with weaponized ISO and IMG files.


SecurityWeek
More than a dozen cybersecurity-related M&A deals were announced in the first half of October 2023.

SecurityWeek
Motorola Solutions announces the Public Safety Threat Alliance, a cyber threat intelligence sharing hub for the public safety community.


DarkReading
The false advertisement has been left up for days, flying under the radar by managing to adhere to Google Ads' policies.


CSO
Here are the top cybersecurity tools, platforms, capabilities, services, and technologies launched at Black Hat USA 2023 that you need to know about.


SecurityWeek
Zero trust endpoint security company ThreatLocker has announced a $115 million Series D funding round that brings the total to $240 million.


CSO
AI can improve threat-hunting efficiencies with improved automation and accuracy, according to a study.


SecurityWeek
Mainsail Partners leads a $15 million financing round for end-to-end cybersecurity compliance platform company Apptega.


SecurityWeek
Healthcare cybersecurity company Blackwell Security has raised $13 million and appointed Geyer Jones as its first CEO.


The Hacker News
Don't wait for cybersecurity alerts to address threats. Discover the benefits of proactive threat hunting in our latest article.


SecurityWeek
Twenty-five cybersecurity-related merger and acquisition M&A deals were announced in the first half of August 2023.


DarkReading
BatLoader has spread rapidly to roost in systems globally, tailoring payloads to its victims.

SecurityWeek
Red Canary's 2022 Threat Detection Report sheds light on the scale of ransomware in the cybercriminal ecosystem.

Infosecurity News
VMware explained that 8Base employs a combination of encryption and “name-and-shame” tactics

Infosecurity News
Alert fatigue is a major issue, says Expel

Infosecurity News
The figures from the latest Critical Start report also suggest 30% come from phishing campaigns


ZDNet
According to IDC, most organizations will seek security service providers amid skills shortages to boost in-house teams.


Infosecurity News
Figure is more than 10% higher than cross-sector average


SecurityWeek
The recently disclosed Check Point VPN attacks involve the zero-day vulnerability CVE-2024-24919, which allows hackers to obtain passwords.


Infosecurity News
Rapid7 has observed that some vulnerabilities in Adobe ColdFusion were still being exploited several days after the patches were published

The Hacker News
Companies need to consolidate cybersecurity technology to improve their overall security posture and reduce the risk of cyber attacks.

The Hacker News
Ransomware readiness starts with a recovery plan, immutable cloud backups, and an incident communication plan.


The Hacker News
More zero knowledge attacks, more leaked credentials, more Gen-Z cyber crimes - 2022 trends and 2023 predictions.

SecurityWeek
CISA has added 95 security holes to its Known Exploited Vulnerabilities Catalog, including more than 60 flaws affecting Cisco and Microsoft products.


Security Affairs
CISA and the FBI warned today of a new Truebot variant employed in attacks against organizations in the United States and Canada. A new variant of the Truebot malware was used in attacks against organizations in the United States and Canada. Threat actors compromised target networks by exploiting a critical remote code execution (RCE) vulnerability in […]


CyberSecurity Dive
A variety of hackers are working to exploit a critical vulnerability in the remote desktop application.

The Hacker News
[Webinar] When More Is Not Better: Solving Alert Overload


Naked Security
Latest episode – listen now! (Or read the transcript if you prefer the text version.)


Trend Micro
Explore why Trend Micro is recognized—for the 18th time—as a Leader in the Gartner Magic Quadrant for Endpoint Protection Platforms.


Trend Micro
We analyzed a fileless QAKBOT stager possibly connected to the recently reported Squirrelwaffle campaign.

SecurityWeek
CISOs struggling to fill their cybersecurity vacancies should take a closer look at the opportunities afforded by military veterans

Cyber Security News
CrushFTP disclosed a zero-day vulnerability (CVE-2024-4040) affecting versions below 10.7.1 and 11.1.0, allowing remote attackers with low


Infosecurity News
Threat actors put the pressure on with references to family members


SecurityWeek
Rapid7 says attackers are targeting a critical pre-authentication flaw in Progress Software’s WS_FTP server just days after disclosure.

Cyber Security News
This Russia-linked criminal group has adopted an increasingly sophisticated modus operandi, deploying Remote Monitoring and Management (RMM) tools to infiltrate target networks and discreetly execute ransomware attacks.


Trend Micro
We discovered the use of two Python penetration-testing tools, Impacket and Responder, that malicious actors used to compromise systems and exfiltrate data. We share our key findings in this report.


CSO
Cybersecurity vendor says enhancement allows for increased human-led threat hunting to uncover more behavior-based findings associated with specific threat actors.


Cyber Security News
Cisco ASA SSL VPN Appliances is a type of network security device that allows remote users to access a private network over the internet securely.


SecurityWeek
At least two new Adobe ColdFusion vulnerabilities have been exploited in the wild, including one that has not been completely patched


Security Affairs
As technology evolves and our dependence on digital systems increases, the cybersecurity threat landscape also rapidly changes.


DarkReading
Analysts seem bullish about funding and M&A activity for the second half of the year, though transaction volumes and values dipped again in Q2.


SecurityWeek
Forty cybersecurity-related merger and acquisition (M&A) deals were announced in August 2023.


The Cyber Express
The ever-evolving digital landscape presents a constant challenge for businesses and individuals alike: staying secure in the face of increasingly


ZDNet
The company reported a loss per share of $0.09 for the quarter.


Bleeping Computer
The DarkSide ransomware gang has collected at least $90 million in ransoms paid by its victims over the past nine months to multiple Bitcoin wallets.


Security Affairs
Industrial cybersecurity firm Dragos revealed that a ransomware group attempted to breach its infrastructure and extort it. Industrial cybersecurity firm Dragos revealed that on May 8, 2023, a known ransomware group attempted and failed to breach the company systems. The cybercriminals compromised the personal email address of a new sales employee prior to his/her start […]


CSO
The virtual machine allows cyber professionals to access the dark web and conduct investigations anonymously, reducing risks like accidental malware installation.


The Hacker News
Building your organization's security framework.


CSO
Cato XDR will use Cato Networks’ native SASE capabilities to improve incident detection and response.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. WordPress sites using the Ultimate Member plugin are under attack LockBit gang demands a $70 million […]


Bleeping Computer
Attackers are exploiting a recently patched and critical severity Atlassian Confluence authentication bypass flaw to encrypt victims' files using Cerber ransomware.


Naked Security
Uber is all over the news for a widely-publicised data breach. We help you answer the question, “How do I stop this happening to me?”


The Cyber Express
According to the findings from a recent Kaspersky study revealed at Cybersecurity Weekend, 41% of companies worldwide are facing a

Cyber Security News
Bridewell's Cyber Threat Intelligence (CTI) team has discovered previously undetected Ursnif infrastructure used in 2023 campaigns, suggesting that the malware operators have not yet utilized this highly elusive infrastructure.


Cyber Security News
Hackers leverage the LockBit 3.0 ransomware due to its sophisticated encryption functionalities which enables them to successfully encrypt

SecurityWeek
The U.S. government has reissued an alert warning organizations about Conti ransomware attacks as the cybercrime group deals with the recent leaks.


ZDNet
Federal agencies have until the end of fiscal year 2024 to "achieve specific zero trust security goals."


Infosecurity News
The proximity of organizations’ headquarters, like Asda’s and NHS England’s, prompted BlueVoyant to choose Leeds as the location for its first UK SOC

Cyber Security News
Researchers at eSentire have identified a shady piece of malware downloader, BatLoader, that has been engaged in a wicked campaign of exploiting Google Ads to distribute malicious secondary payloads


Trend Micro
How Trend Micro’s unified cybersecurity platform is transforming cloud security


The Hacker News
CISOs globally are turning to Cato SSE 360 for seamless SASE and SSE transitions, achieving top results in visibility, threat prevention, and data sov


Bleeping Computer
Over the weekend, security researchers released a proof-of-concept (PoC) exploit for a maximum severity remote code execution vulnerability in Progress Software's WS_FTP Server file sharing platform.


CSO
XDR platform uses native and third-party attack signals across hybrid cloud domains including AWS, Microsoft Azure, and Google Cloud as well as networks and endpoints.
Loading more articles....