

Cyber Security News
OpenSSH Agent RCE Flaw Let Attackers Execute Arbitrary Commands
The flaw exists in OpenSSH's forward ssh-agent. This flaw allows an attacker to execute arbitrary commands on vulnerable OpenSSH’s forwarded ssh-agent.


Cyber Security News
The flaw exists in OpenSSH's forward ssh-agent. This flaw allows an attacker to execute arbitrary commands on vulnerable OpenSSH’s forwarded ssh-agent.


Security Affairs
A new flaw in OpenSSH could be potentially exploited to run arbitrary commands remotely on compromised hosts under specific conditions. Researchers from the Qualys Threat Research Unit (TRU) have discovered a remote code execution vulnerability in OpenSSH’s forwarded ssh-agent. OpenSSH (Open Secure Shell) is a set of open-source tools and utilities that provide secure encrypted […]


Cyber Security News
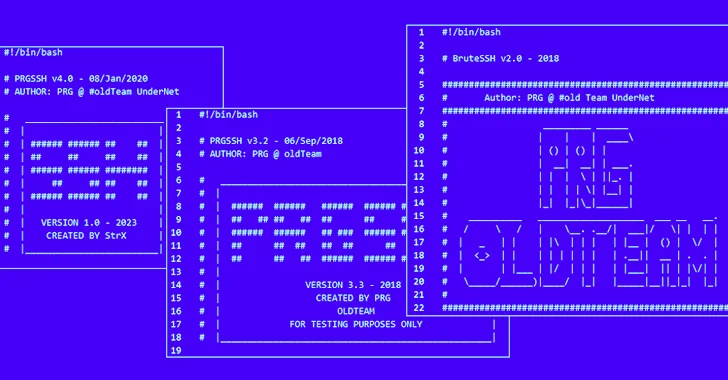
Threat actors abuse SSH credentials to gain unauthorized access to systems and networks. By exploiting weak or compromised credentials, they


Bleeping Computer
A novel malware named 'Agent Raccoon' (or Agent Racoon) is being used in cyberattacks against organizations in the United States, the Middle East, and Africa.


Bleeping Computer
A threat actor is using an open-source network mapping tool named SSH-Snake to look for private keys undetected and move laterally on the victim infrastructure.


Bleeping Computer
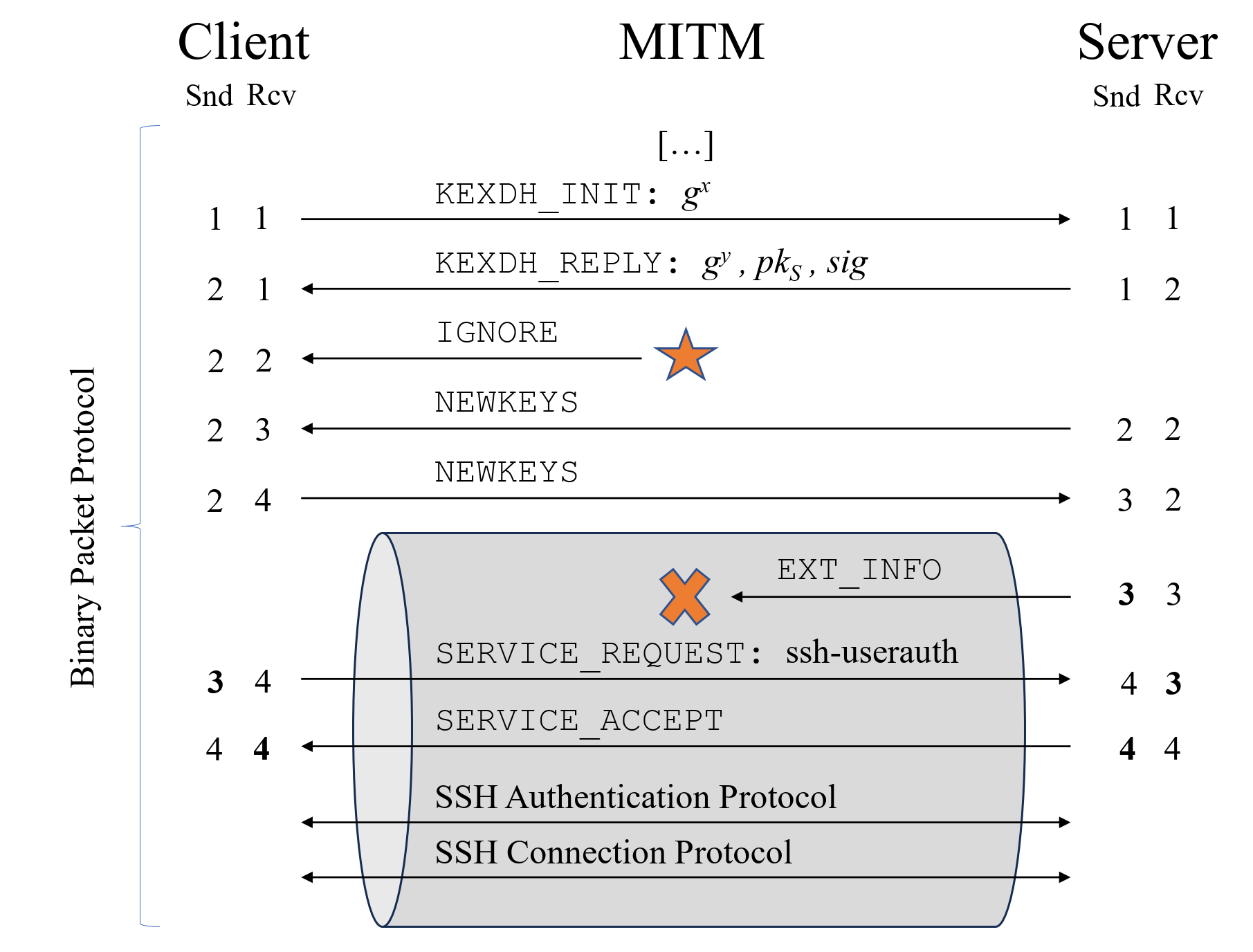
Almost 11 million internet-exposed SSH servers are vulnerable to the Terrapin attack that threatens the integrity of some SSH connections.


Cyber Security News
It was reported that SSH servers were vulnerable to the new Terrapin Attack in which threat actors can downgrade an SSH protocol version.


Bleeping Computer
Citrix notified customers this week to manually mitigate a PuTTY SSH client vulnerability that could allow attackers to steal a XenCenter admin's private SSH key.

SecurityWeek
Interpol has announced the arrest of three Nigerians accused of using the Agent Tesla malware to redirect financial transactions and steal data.


SC Magazine
The fileless, self-modifying, worm-like network traversal tool automatically searches for SSH keys.


Cyber Security News
Check Point Research has exposed a recent wave of cyberattacks utilizing the infamous Agent Tesla malware. This campaign targeted organization

Security Affairs
Researchers discovered an SSH vulnerability, called Terrapin, that could allow an attacker to downgrade the connection's security.


HACKRead
Beware! Agent Tesla & Taskun Malware are targeting US Education & Gov. This cyberattack steals data & exploits vulnerabilities.


Security Affairs
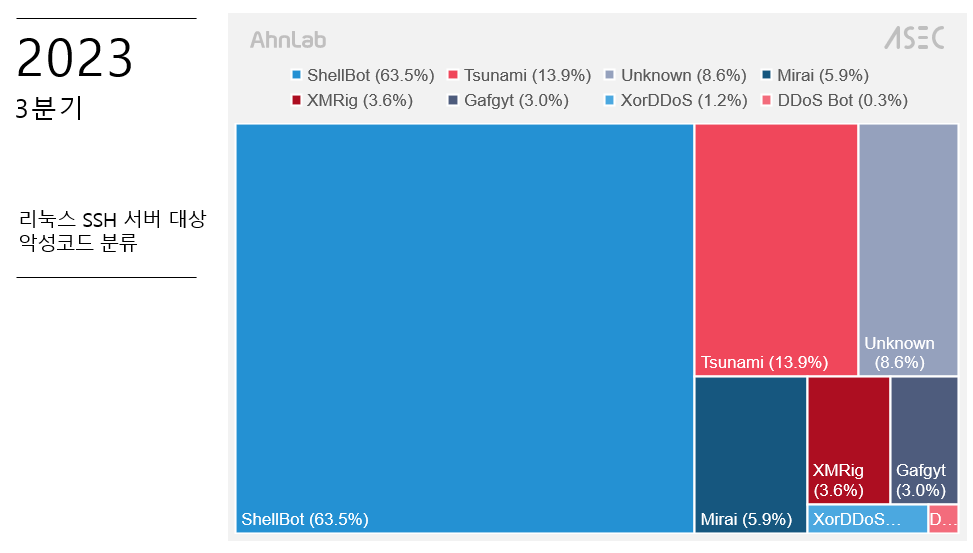
Researchers warn of an ongoing Tsunami DDoS botnet campaign targeting inadequately protected Linux SSH servers. Researchers from AhnLab Security Emergency response Center (ASEC) have uncovered an ongoing hacking campaign, aimed at poorly protected Linux SSH servers, to install the Tsunami DDoS botnet (aka Kaiten). The threat actors behind these attacks were also observed installing other […]

Bleeping Computer
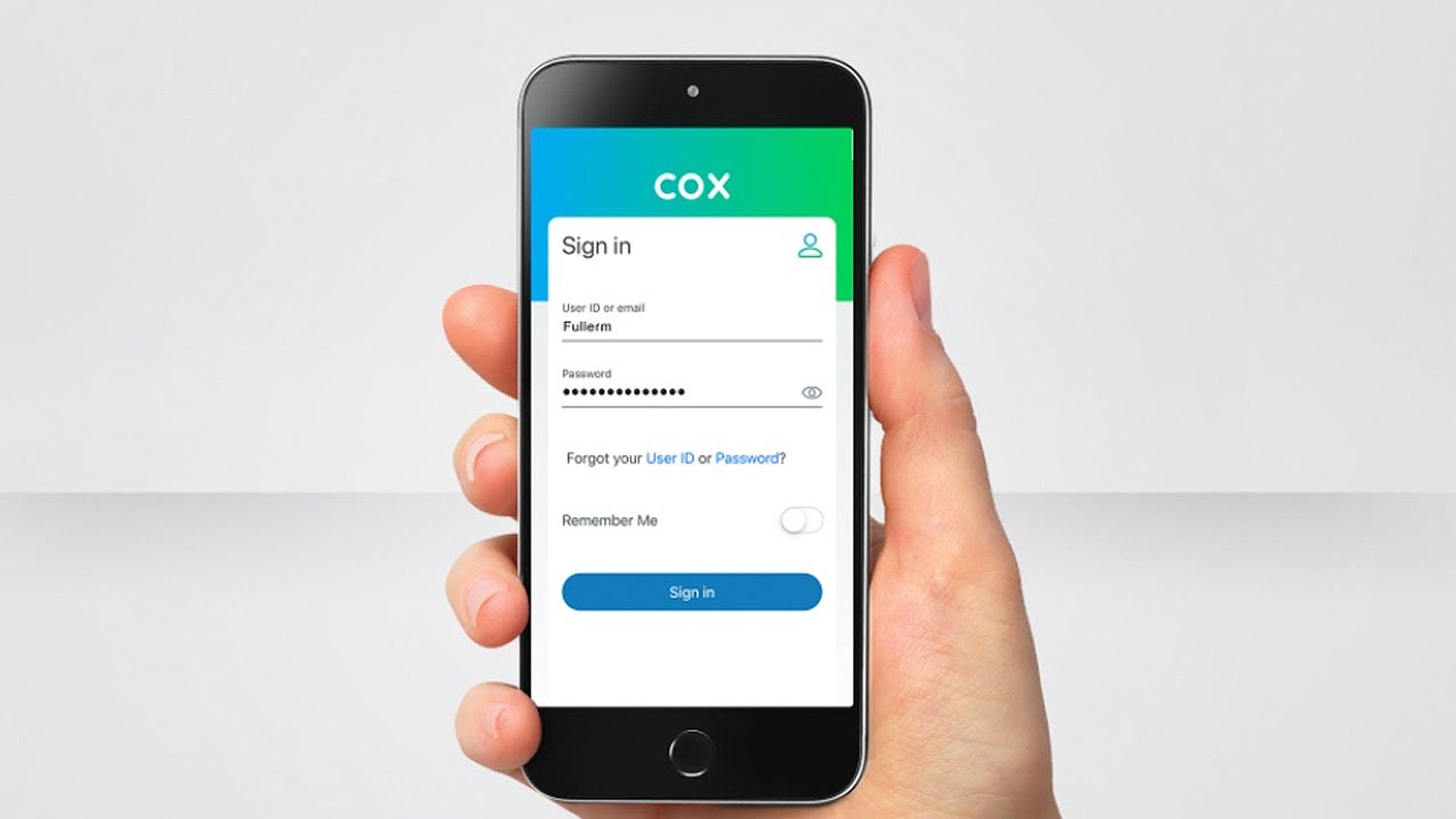
Cox Communications has disclosed a data breach after a hacker impersonated a support agent to gain access to customers' personal information.


Bleeping Computer
Mozilla has launched an experiment where they change the Firefox browser user agent to a three-digit "Firefox/100.0" version to see if it will break websites.


The Hacker News
A mysterious malware called Agent Racoon is infiltrating organizations in the Middle East, Africa, and the U.S.


Latest Hacking News
Researchers have devised a new attack strategy, called “Terrapin,” that exploits vulnerabilities in the SSH protocol. While vendors are moving on with mitigating the flaws, it may take some time for the patches to be


SecurityWeek
Threat actors are actively deploying the recently released self-replicating and self-propagating SSH-Snake worm.


Bleeping Computer
Google is testing whether changing the Chrome user agent to three-digit 'Chrome/100' will cause loss of functionality on websites that are expecting a two digit version number.


The Hacker News
This article will go in-depth on the strengths and weaknesses of each approach, agent-based and network-based vulnerability scanning.

The Hacker News
Iranian hackers deploying SideTwist backdoor in fresh phishing attack. Separate campaign features new variant of Agent Tesla


Security Affairs
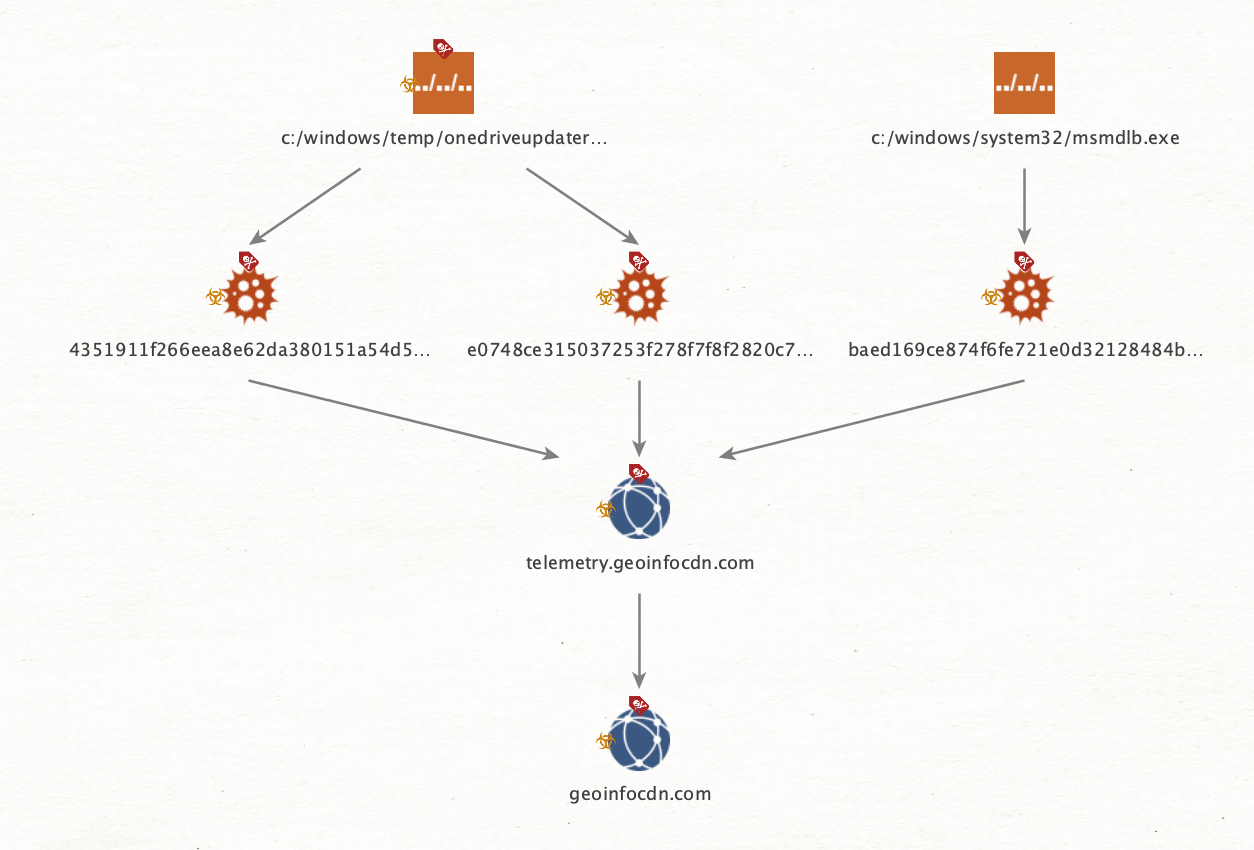
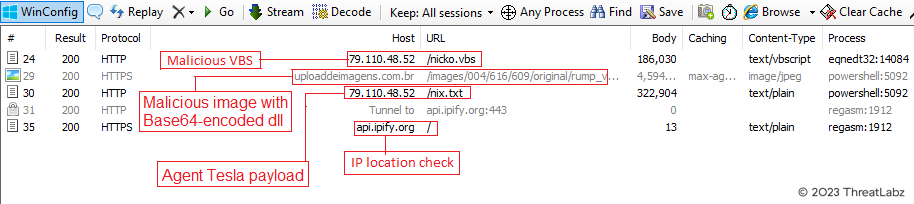
The recently discovered malware builder Quantum Builder is being used by threat actors to deliver the Agent Tesla RAT. A recently discovered malware builder called Quantum Builder is being used to deliver the Agent Tesla remote access trojan (RAT), Zscaler ThreatLabz researchers warn. “Quantum Builder (aka “Quantum Lnk Builder”) is used to create malicious shortcut […]

Security Affairs
Researchers warn of attacks against poorly managed Linux SSH servers that mainly aim at installing DDoS bot and CoinMiner.


Bleeping Computer
Discord is notifying users of a data breach that occurred after the account of a third-party support agent was compromised.


Bleeping Computer
GitHub has revoked weak SSH authentication keys generated using a library that incorrectly created duplicate RSA keypairs.

Cyber Security News
a new malicious campaign in which the Agent Tesla RAT is delivered by a malware builder called Quantum Builder.

The Hacker News
💻🔒 Beware of the latest phishing attack! Attackers are using Microsoft Word docs to spread malware like Agent Tesla, OriginBotnet, and RedLine.


Cyber Security News
Cybersecurity researchers at SOCRadar recently reported about an open-source botnet, Supershell, that obtains SSH shell access.

Security Affairs
Threat actors are using the Agent Raccoon malware in attacks against organizations in the Middle East, Africa and the U.S.


The Hacker News
A high-severity Time-of-Check to Time-of-Use (TOCTOU) (CVE-2023-27470) in N-Able's Take Control Agent could give hackers SYSTEM privileges.


The Hacker News
Researchers uncover a critical SSH protocol vulnerability, "Terrapin" (CVE-2023-48795), allowing attackers to compromise secure connections.


The Hacker News
NoaBot, a Mirai-based botnet, is targeting SSH servers for crypto mining since early 2023


CyberNews
77% of SSH servers on the internet supported at least one mode that can be exploited in practice by the new attack.


Bleeping Computer
GitHub has added support for securing SSH Git operations using FIDO2 security keys for added protection from account takeover attempts.


Cyber Security News
Terrapin attack” has been discovered which will allow threat actors to downgrade the SSH protocol version exploitation of vulnerable servers.


DataBreaches
An enforcement action and prosecution was announced by the U.K. Information Commissioner’s Office this week: A former tracing agent pleaded guilty and...


Security Affairs
New ShellBot DDoS bot malware, aka PerlBot, is targeting poorly managed Linux SSH servers, ASEC researchers warn. AhnLab Security Emergency response Center (ASEC) discovered a new variant of the ShellBot malware that was employed in a campaign that targets poorly managed Linux SSH servers. The ShellBot, also known as PerlBot, is a Perl-based DDoS bot that uses IRC […]

The Hacker News
Beware of proxyjacking! Vulnerable SSH servers are under attack in a financially motivated campaign, covertly ensnaring them into a proxy network.


The Hacker News
Legion malware evolves with expanded capabilities. Latest version exploits SSH servers and gains access to DynamoDB and CloudWatch credentials.


Ars Technica
Novel Terrapin attack uses prefix truncation to downgrade the security of SSH channels.

The Hacker News
Researchers discover new IoT RapperBot malware capable of brute-forcing ssh credentials to compromise Linux servers.


Bleeping Computer
Attackers behind an ongoing series of proxyjacking attacks are hacking into vulnerable SSH servers exposed online to monetize them through services that pay for sharing unused Internet bandwidth.

Security Affairs
The PuTTY Secure Shell (SSH) and Telnet client are impacted by a critical vulnerability that could be exploited to recover private keys.

Security Affairs
Threat actors are exploiting an old Microsoft Office vulnerability, tracked as CVE-2017-11882, to spread the Agent Tesla malware


Bleeping Computer
McAfee has patched a security vulnerability discovered in the company's McAfee Agent software for Windows enabling attackers to escalate privileges and execute arbitrary code with SYSTEM privileges.


Bleeping Computer
Microsoft revoked insecure SSH keys some Azure DevOps have generated using a GitKraken git GUI client version impacted by an underlying issue found in one of its dependencies.

The Hacker News
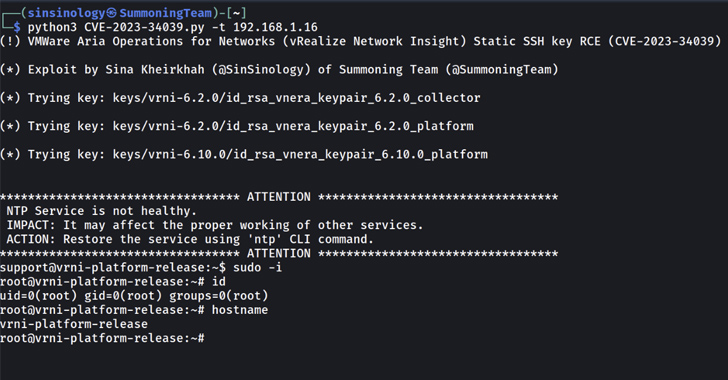
Exploit code now available for critical SSH authentication bypass flaw in VMware Aria Operations for Networks.

The Hacker News
New variant of Agent Tesla malware identified. It's a keylogger and remote access trojan (RAT) offered as part of a malware-as-a-service (MaaS) model.


Bleeping Computer
North Korean hackers are using trojanized versions of the PuTTY SSH client to deploy backdoors on targets' devices as part of a fake Amazon job assessment.


The Hacker News
A tool intended for security, SSH-Snake, now aids attackers in exploiting networks. Discover the depths of its reach and how to safeguard your infrast


Bleeping Computer
A Navy nuclear engineer and his wife were arrested under espionage-related charges alleging violations of the Atomic Energy Act after selling restricted nuclear-powered warship design data to a person they believed was a foreign power agent.


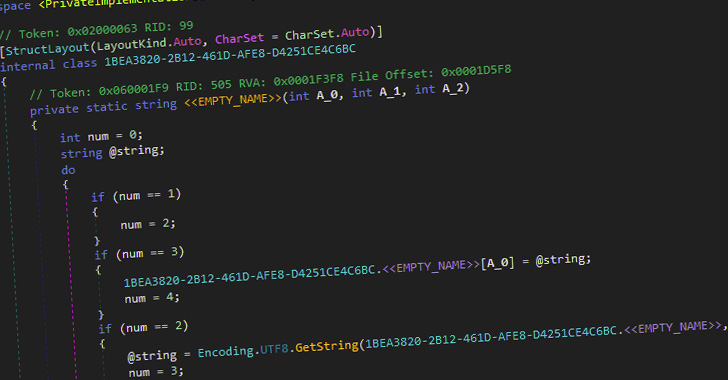
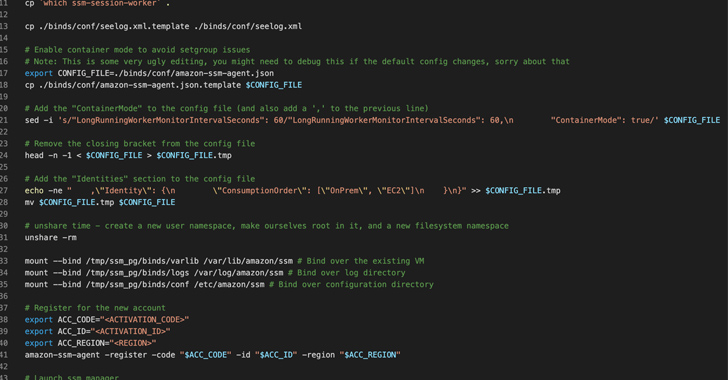
CSO
Mitiga researchers found that the AWS SSM agent could be hijacked and turned into a remote access trojan that is difficult to detect.


The Hacker News
Beware of phishing emails with invoice-themed attachments! Attackers are using an old Office vulnerability (CVE-2017-11882) to spread the Agent Tesla


Bleeping Computer
Proof-of-concept exploit code has been released for a critical SSH authentication bypass vulnerability in VMware's Aria Operations for Networks analysis tool (formerly known as vRealize Network Insight).

The Hacker News
Poorly secured Linux SSH servers are under attack! Threat actors are installing tools to guess credentials, co-opt other servers.

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


Cyber Security News
The adversaries from North Korea are deploying critical backdoors on the devices of targets by using trojanized versions of the PuTTY SSH client. Posing as a fake Amazon job application to put backdoors onto their devices.


The Hacker News
The study highlights a vulnerability in SSH servers that allows passive attackers to obtain private RSA host keys.


Bleeping Computer
GitHub has rotated its private SSH key for GitHub.com after the secret was was accidentally published in a public GitHub repository. The software development and version control service says, the private RSA key was only "briefly" exposed, but that it took action out of "an abundance of caution."


Bleeping Computer
A new botnet called 'RapperBot' has emerged in the wild since mid-June 2022, focusing on brute-forcing its way into Linux SSH servers and then establishing persistence.


The Record
Researchers at AhnLab are urging administrators of Linux SSH servers — which are intended to allow for secure remote access — to maintain strong passwords and take other security measures.


The Hacker News
GitHub replaces RSA SSH host key after brief exposure in public repository to prevent any bad actor from impersonating the service or eavesdropping on


Cyber Security News
It has been observed that a new Proxyjacking campaign attack SSH servers and subsequently builds Docker services that share the victim's bandwidth for money.


SecurityWeek
Cisco has observed an increase in brute-force attacks targeting web application authentication, VPNs, and SSH services.


The Hacker News
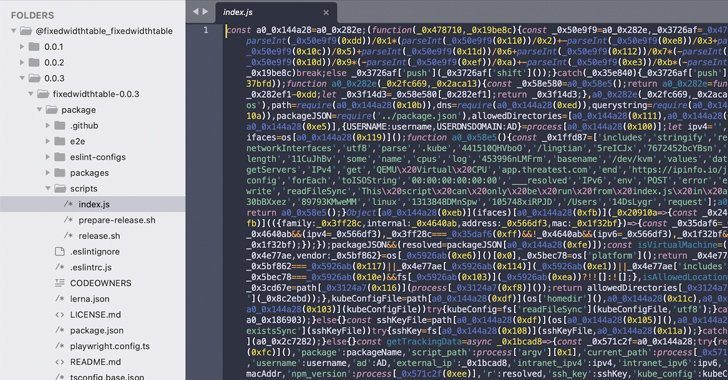
Did you download Warbeast2000 or Kodiak2k from npm? If so, your SSH keys might be compromised! These packages steal keys & upload them to GitHub.


Bleeping Computer
Researchers have discovered a new post-exploitation technique in Amazon Web Services (AWS) that allows hackers to use the platform's System Manager (SSM) agent as an undetectable Remote Access Trojan (RAT).


Bleeping Computer
Cisco has released security updates to address critical security flaws allowing unauthenticated attackers to log in using hard-coded credentials or default SSH keys to take over unpatched devices.


Cyber Security News
In a concerning development for cybersecurity, over 150 SSH accounts with root access are currently being advertised for sale on various


Latest Hacking News
Cisco has recently fixed a trivial but serious issue in its Umbrella Virtual Appliance. The flaw mainly included the existence of a static SSH key in Cisco Umbrella VA that allowed an adversary to steal

%20--%20Supply%20Chain%20Backdoor%20(1).webp)
Cyber Security News
Fedora Linux 40 beta users have been urged to take immediate action after an Upstream supply chain attack that has compromised SSH protocol.


Bleeping Computer
An unknown threat actor is brute-forcing Linux SSH servers to install a wide range of malware, including the Tsunami DDoS (distributed denial of service) bot, ShellBot, log cleaners, privilege escalation tools, and an XMRig (Monero) coin miner.

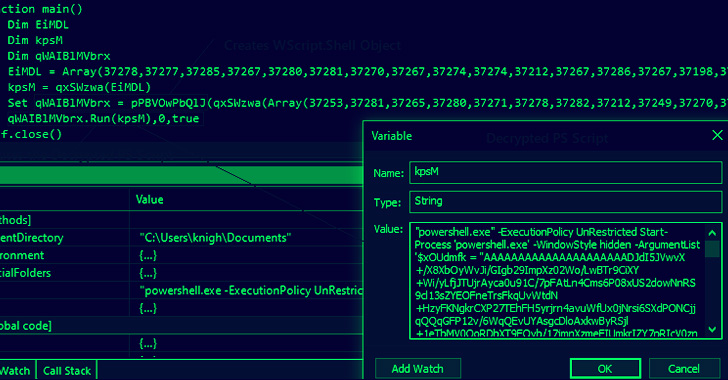
The Hacker News
Cybercriminals are using a tool called "Quantum Builder" sold on the Dark Web to generate malicious LNK, HTA, and PowerShell payloads to deliver Agent


Bleeping Computer
VMware Aria Operations for Networks (formerly vRealize Network Insight) is vulnerable to a critical severity authentication bypass flaw that could allow remote attackers to bypass SSH authentication and access private endpoints.


Bleeping Computer
A team of academic researchers from universities in California and Massachusetts demonstrated that it's possible under certain conditions for passive network attackers to retrieve secret RSA keys from naturally occurring errors leading to failed SSH (secure shell) connection attempts.


Security Affairs
RapperBot is a new botnet employed in attacks since mid-June 2022 that targets Linux SSH servers with brute-force attacks. Researchers from FortiGuard Labs have discovered a new IoT botnet tracked as RapperBot which is active since mid-June 2022. The bot borrows a large portion of its code from the original Mirai botnet, but unlike other […]


Security Affairs
Cisco Talos warns of large-scale brute-force attacks against VPN services, web application authentication interfaces and SSH services.

The Hacker News
Beware of npm imposters! 14 fraudulent packages found in the registry, posing as legit tools. They aim to steal your Kubernetes configs and SSH keys.


Bleeping Computer
Offensive Security has released Kali Linux 2022.1, the first version of 2022, with improved accessibility features, a visual refresh, SSH wide compatibility, and of course, new toys to play with!


The Hacker News
Researchers alert of a global rise in brute-force attacks from TOR nodes targeting VPNs, web interfaces, and SSH services

Cyber Security News
Since mid-June 2022, several cyberattacks have been carried out by a new botnet called RapperBot. The botnet mainly tries to establish a foothold on Linux SSH servers by brute-forcing its way in. This new botnet, RapperBot is completely based on the Mirai trojan, which was discovered by the cybersecurity researchers at Fortinet. However, the behavior […]


DataBreaches
A federal jury yesterday convicted a former Media Partnerships Manager for the Middle East/North Africa (MENA) region at Twitter of acting as a foreign agent...


Infosecurity News
Incident impacts user emails and support messages


DarkReading
Cybercriminals employ obfuscated script to stealthily hijack victim server bandwidth for use in legitimate proxy networks.


Cyber Security News
The persistent search for money and the threat actors becoming more sophisticated are driving the alarming rate of malware change.


Bleeping Computer
A vulnerability tracked as CVE-2024-31497 in PuTTY 0.68 through 0.80 could potentially allow attackers with access to 60 cryptographic signatures to recover the private key used for their generation.

SecurityWeek
Vietnamese hacker Ngo Minh Hieu made a fortune stealing the personal data of hundreds of millions of Americans, but has since turned his back on his criminal past and works on cybersecurity for the government


Infosecurity News
The move reportedly did not stem from a compromise of GitHub systems or customer information

The Hacker News
Researchers have detailed the inner workings of a malware called OriginLogger, which is being traded as a successor to the widespread malware.


Ars Technica
Terrapin isn't likely to be mass-exploited, but there's little reason not to patch.


Infosecurity News
Mitiga’s research demonstrated two potential attack scenarios


CSO
The Axeda platform, used by hundreds of IoT devices, has seven vulnerabilities, three of which allow for remote code execution.

The Hacker News
Researchers have found a sneaky post-exploitation technique in Amazon Web Services (AWS).


Bleeping Computer
Cisco has released security updates to address a high severity vulnerability in the Cisco Umbrella Virtual Appliance (VA), allowing unauthenticated attackers to steal admin credentials remotely.


DarkReading
The botnet — built for DDoS, backdooring, and dropping malware — is evading standard URL signature detections with a novel approach involving Hex IP addresses.


DarkReading
The botnet — built for DDoS, backdooring, and dropping malware — is evading standard URL signature detections with a novel approach.


SC Magazine
Malware distribution on open source package repositories increased 1,300% in the last three years, researchers say.


Infosecurity News
ReversingLabs noted a 1300% surge in harmful open-source packages between 2020 and 2023


SC Magazine
Vulnerability allows remote code execution with System privileges on all Windows endpoints within a Kubernetes cluster.


DarkReading
Over the past few weeks, a Mirai variant appears to have made a pivot from infecting new servers to maintaining remote access.
Loading more articles....