
.webp)
Cyber Security News
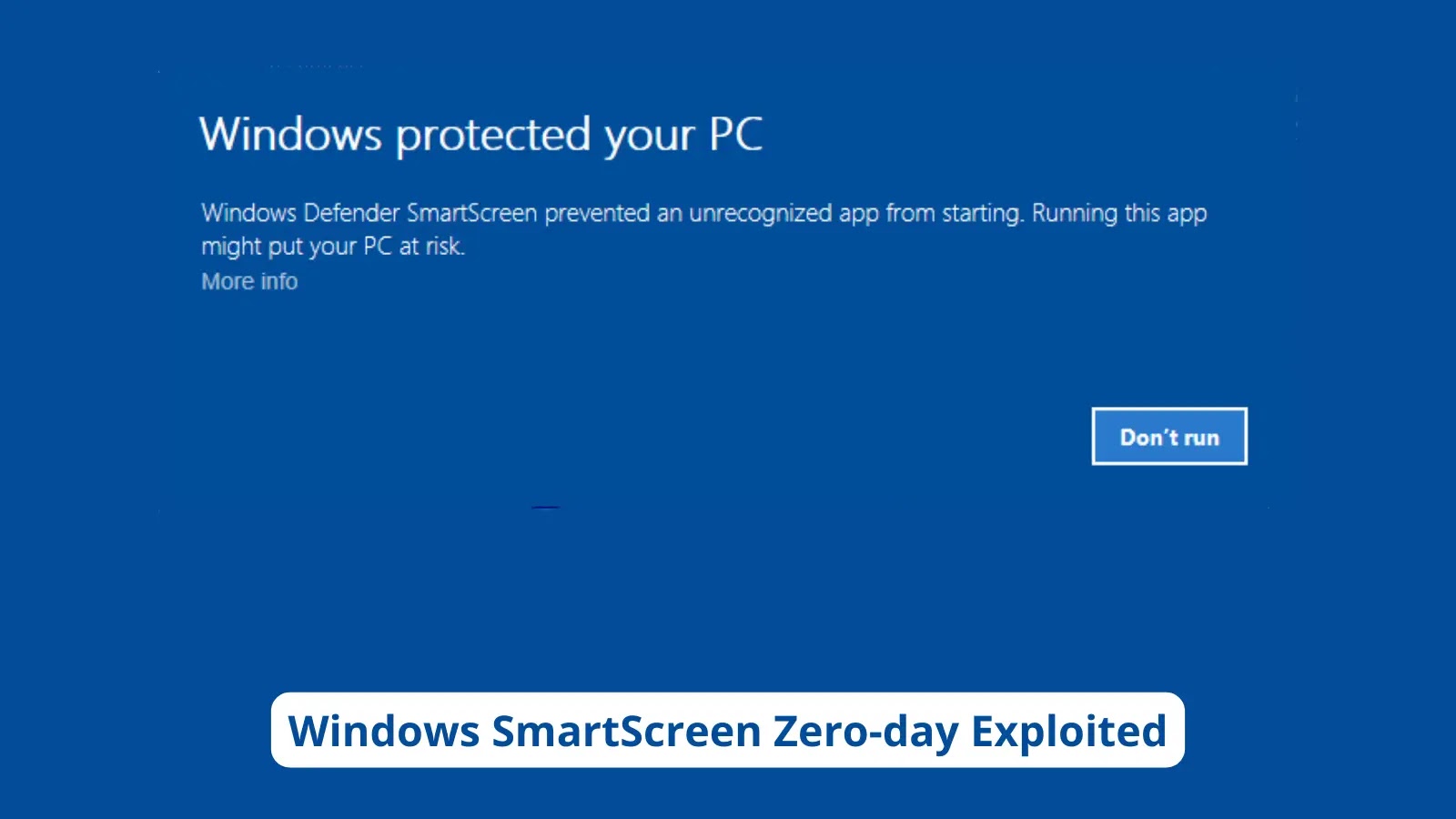
Remcos Everywhere! Attacking From a Weaponized Zip File
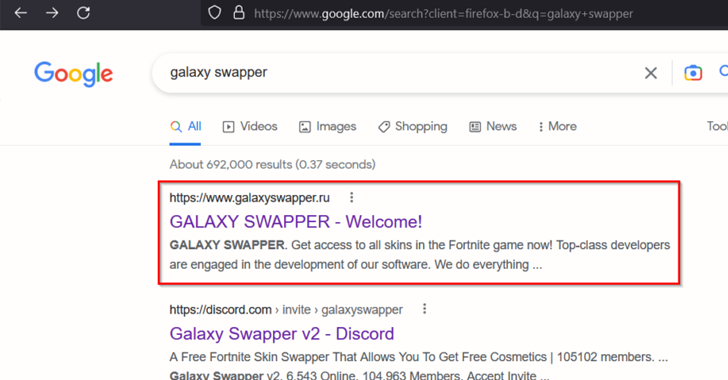
Cybersecurity circles are abuzz with the latest campaign involving the notorious Remote Control System (RAT), Remcos.

.webp)
Cyber Security News
Cybersecurity circles are abuzz with the latest campaign involving the notorious Remote Control System (RAT), Remcos.


Security Affairs
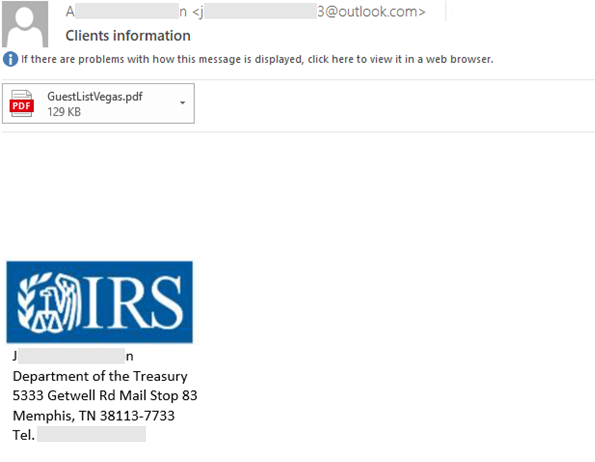
Microsoft warns of a new Remcos RAT campaign targeting US accounting and tax return preparation firms ahead of Tax Day. Ahead of the U.S. Tax Day, Microsoft has observed a new Remcos RAT campaign targeting US accounting and tax return preparation firms. The phishing attacks began in February 2023, the IT giant reported. Remcos is […]


The Hacker News
Ukrainian entities in Finland targeted in a malicious campaign distributing Remcos RAT using IDAT Loader.

.webp)
Cyber Security News
Researchers have confirmed the accuracy of the Remcos RAT malware being distributed through UUE (UUEncoding) files compressed with Power Archiver.


The Hacker News
reaking News: Remcos RAT, a stealthy remote access trojan, is now spreading in South Korea disguised as adult-themed games via webhards

.webp)
Cyber Security News
Hackers have been found leveraging weaponized virtual hard disk (VHD) files to deploy the notorious Remote Control Software (RAT), Remcos.


Cyber Security News
Threat actors adopting the use of two software GuLoader (also known as CloudEyE Protector) and Remcos (Remote administration tool) for malicious purposes


Security Affairs
The Computer Emergency Response Team of Ukraine (CERT-UA) warns of a new wave of attacks against state authorities to deploy the Remcos software. The Computer Emergency Response Team of Ukraine (CERT-UA) is warning of a phishing campaign aimed at state authorities that involves the use of the legitimate remote access software Remcos. The phishing emails, […]

The Hacker News
New phishing campaign targets European entities using Remcos RAT & Formbook via DBatLoader malware!


The Record
Hacking group UAC-0050 tried to deploy the remote management software Remcos in an effort to spy on government agencies, Ukraine said.


The Hacker News
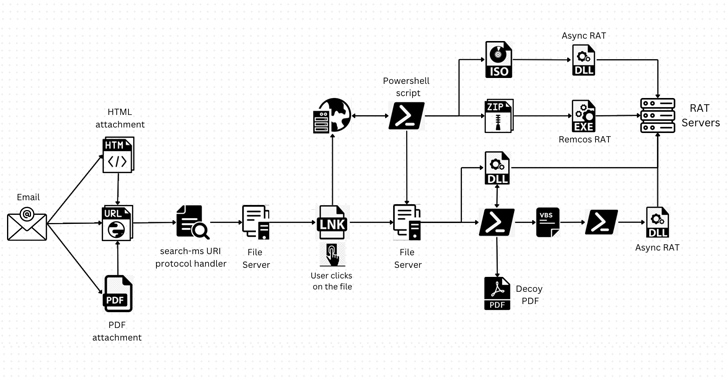
The threat actor UAC-0050 is using phishing attacks to distribute the Remcos RAT while employing new strategies to avoid detection.


The Record
In a recent campaign, the hacking group tracked as UAC-0050 attempted to spread the Remcos remote access tool, according to research by Ukraine's computer emergencies response team (CERT-UA).

Security Affairs
A new malware campaign is targeting a Ukraine entity in Finland with Remcos RAT distributed via a loader called IDAT Loader.


Bleeping Computer
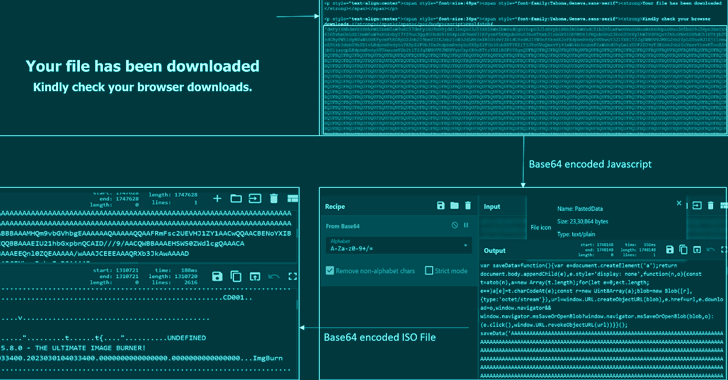
A hacking group tracked as 'UAC-0184' was observed utilizing steganographic image files to deliver the Remcos remote access trojan (RAT) onto the systems of a Ukrainian entity operating in Finland.


DarkReading
Attackers use phishing emails that appear to come from reputable organizations, dropping the payload using public cloud servers and an old Windows UAC bypass technique.

.webp)
Cyber Security News
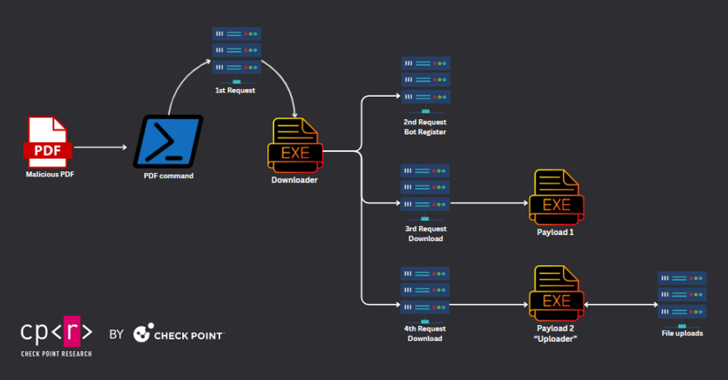
Cybercriminals have launched a sophisticated campaign targeting individuals and utilizing weaponized PDF files to deploy dangerous RATs.


DarkReading
The IDAT Loader malware was used to deliver the cyber espionage tool, employing steganography, a seldom-seen technique in real-world attacks.

The Hacker News
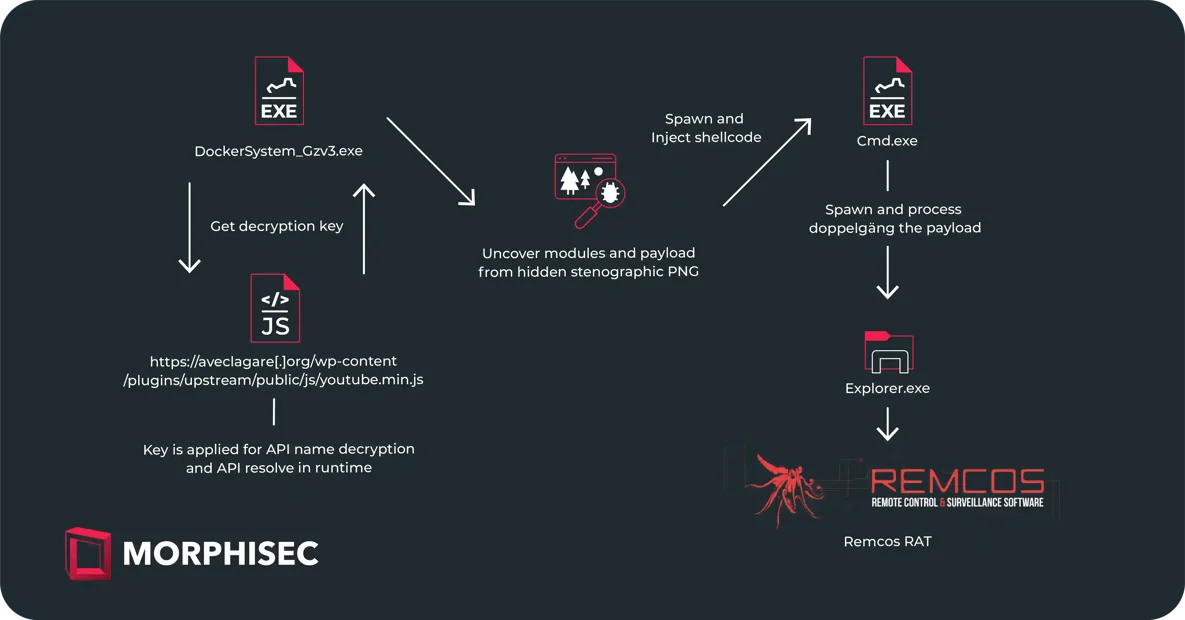
Threat actors are deploying fake websites with trojanized software to infect unsuspecting users with Fruity downloader malware.


Infosecurity News
Weekly attacks targeting Ukraine decreased by 44% between October 2022 and February 2023


The Hacker News
CERT-UA has issued a warning of cyber attacks targeting state authorities using a legitimate remote access software.


DarkReading
Disguised as harmless PDF documents, LNK files trigger a PowerShell script, initiating a Rust-based injector called Freeze[.]rs and a host of malware infections.


The Record
Cybersecurity researchers have discovered that a hacking group targeting Ukraine is using a new method to efficiently and secretly transfer malicious data.


The Cyber Express
As the New Year festivities unfold, cyber threats take on a deceptive facade, with malicious actors exploiting the celebratory spirit


The Hacker News
🕵️♂️ Despite infrastructure disruption, QakBot malware operators are still active in an ongoing phishing campaign, delivering Ransom Knight ransomwa


Cyber Security News
Remcos is categorized as a Remote Access Trojan (RAT), granting attackers complete control over compromised computers.

Cyber Security News
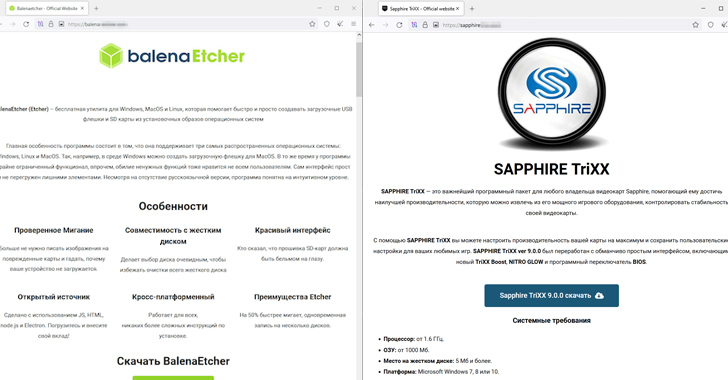
Microsoft released multiple security patches as part of their Patch Tuesday in which three zero-day vulnerabilities were also patched.


Infosecurity News
Group-IB said cyber-criminals used the flaw to create archives packaged with DarkMe, GuLoader and Remcos RAT


The Hacker News
TA558 hackers are using steganography to hide and distribute malware like Agent Tesla, FormBook, Remcos RAT, LokiBot.


The Hacker News
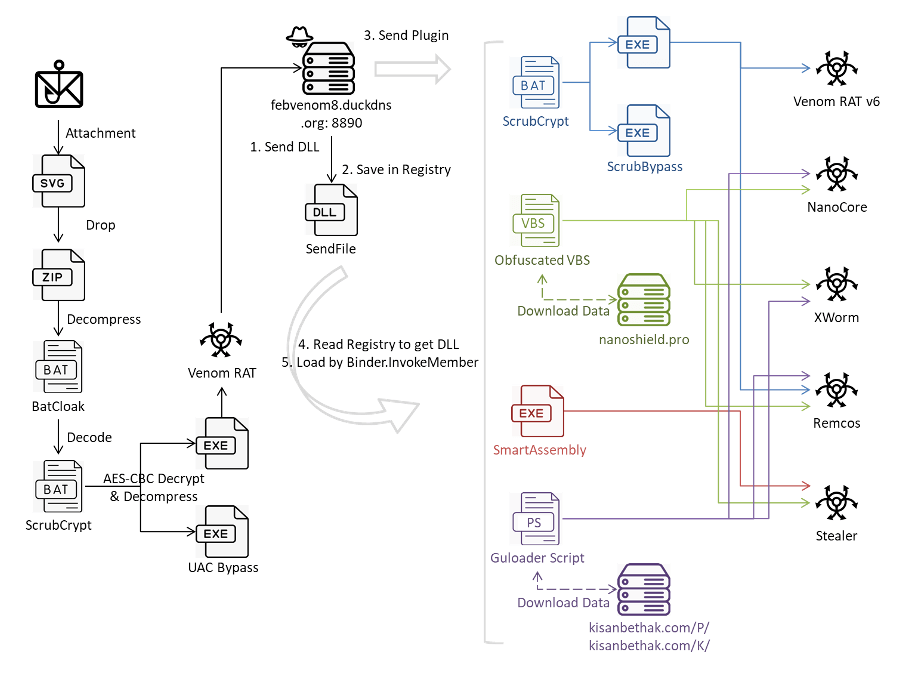
Cybersecurity experts uncover a sophisticated multi-stage attack! 🛡️ Malware including Venom RAT, Remcos RAT, and more deployed via invoice-themed ph


Bleeping Computer
A new phishing campaign targets organizations in Eastern European countries with the Remcos RAT malware with aid from an old Windows User Account Control bypass discovered over two years ago.

Cyber Security News
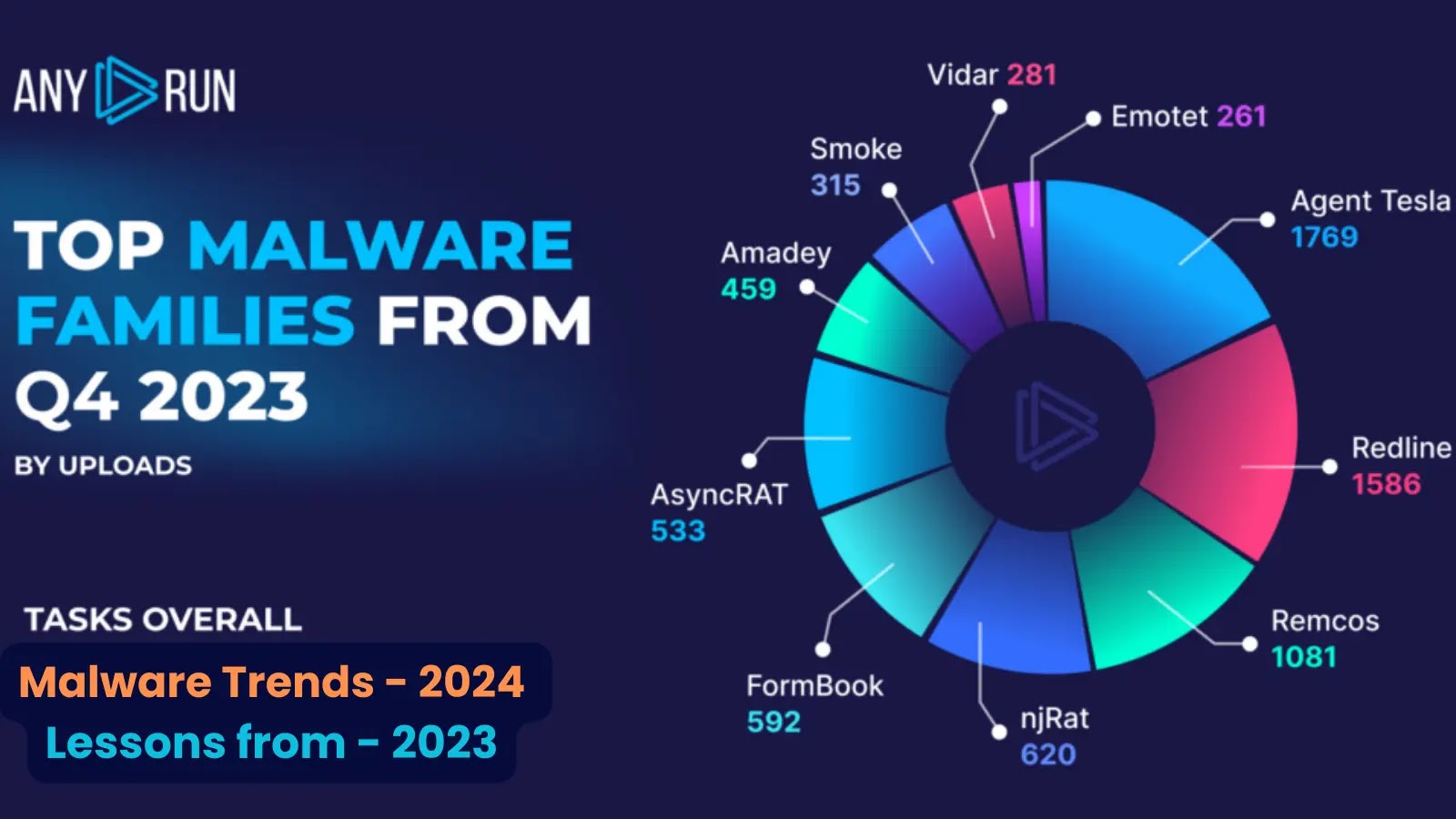
Remcos (1,385 detections in Q1) and AgentTesla (1,769 in Q4) were the two most prevalent examples, closely followed by NjRAT and AsyncRAT.


Cyber Security News
Threat actors have used phishing emails to distribute fileless malware. The attachment consists of a .hta (HTML Application) file, which can be used for deploying other malware like AgentTesla, Remcos, and LimeRAT.


Bleeping Computer
Threat actors are distributing malware using phishing themes related to the invasion of Ukraine, aiming to infect their targets with remote access trojans (RATs) such as Agent Tesla and Remcos.


Trend Micro
In this entry, we detail our analysis of how the TargetCompany ransomware abused an iteration of fully undetectable (FUD) obfuscator engine BatCloak to infect vulnerable systems.

.jpg)
The Hacker News
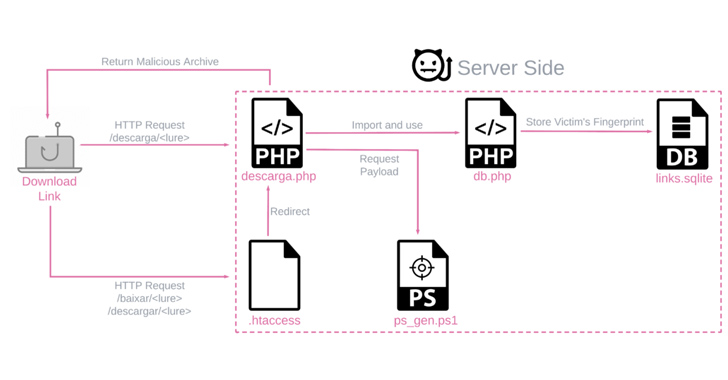
Blind Eagle expands its cyber attack realm! Now targeting North America's manufacturing sector with phishing emails.

Cyber Security News
phishing campaigns have been identified by the security analysts at SentinelOne using the DBatLoader malware loader.


Cyber Security News
Steganography is employed by threat actors to hide malicious payloads in benign files such as pictures or documents.


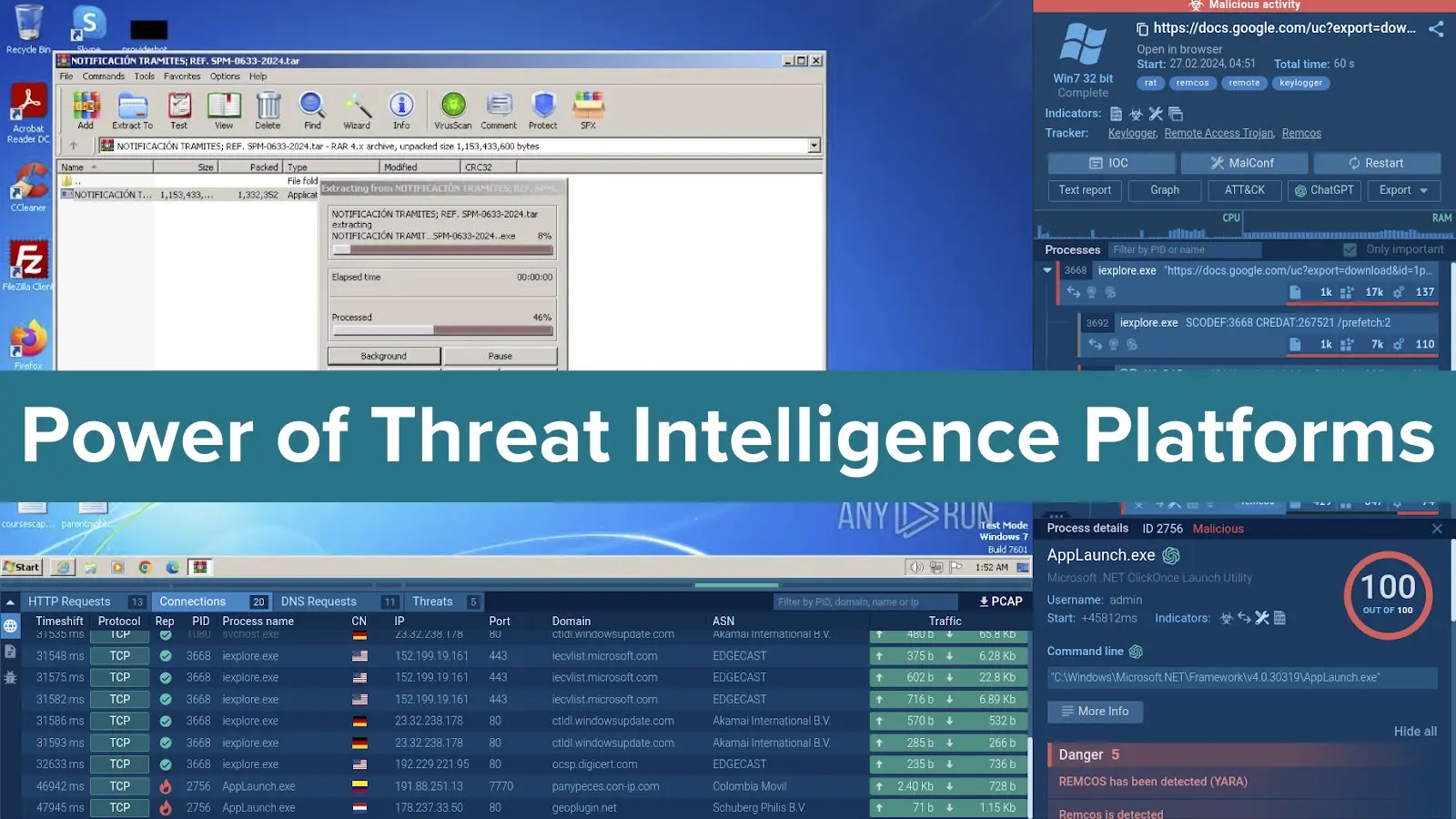
Cyber Security News
ANY.RUN, an interactive online sandbox for fast malware analysis, has published the results of its research into the top cyber threat trends in Q2 2023.


The Record
Researchers at ESET say they spotted thousands of new infections with AceCryptor, which allows malware to slip into systems without being detected by anti-virus software.

SecurityWeek
A new joint cybersecurity advisory from CISA and the Australian Cyber Security Centre details 2021’s top malware strains.


Infosecurity News
Rise in malspam campaigns exploiting attack on Ukraine by Russia


Bleeping Computer
Microsoft is warning of a phishing campaign targeting accounting firms and tax preparers with remote access malware allowing initial access to corporate networks.

The Hacker News
Malicious actors are leveraging the legitimate Rust-based injector Freeze[.]rs to deploy the XWorm malware in targeted environments.


The Record
The most commonly seen malware strains in 2021 include Agent Tesla, Qakbot, TrickBot, GootLoader and several others, according to a new list released by CISA and the Australian Cyber Security Centre.


Bleeping Computer
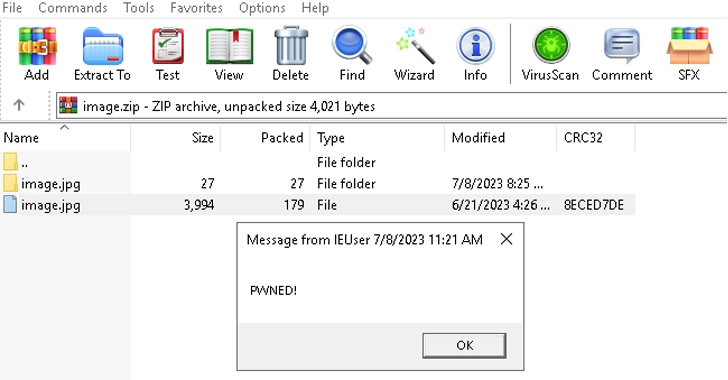
A WinRar zero-day vulnerability tracked as CVE-2023-38831 was actively exploited to install malware when clicking on harmless files in an archive, allowing the hackers to breach online cryptocurrency trading accounts.

The Hacker News
Beware Latin America! BBTok banking trojan strikes Brazil & Mexico. Crafty phishing emails, unique payloads, and a sneaky approach.


SecurityWeek
Qakbot cybercriminals continue to push malware, which shows they are still operational after the recent takedown attempt.


Infosecurity News
The malware discovered by Kaspersky employs a multistage attack method

The Hacker News
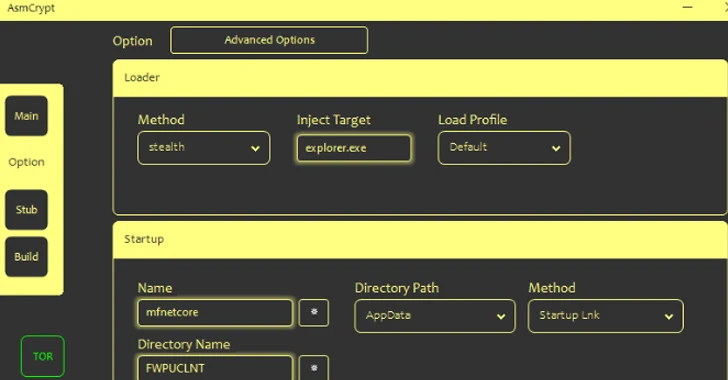
Cybercriminals are currently employing ASMCrypt, an advanced iteration of DoubleFinger, to evade detection by security tools.

The Hacker News
The recent WinRAR vulnerability was exploited as a zero-day since April to compromise traders' devices and withdraw money.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released today a list of the most detected malware strains during last year in a joint advisory with the Australian Cyber Security Centre (ACSC).

The Hacker News
Multiple threat actors are exploiting a design flaw inFoxit PDF software to deliver various malware.

The Hacker News
Malicious actors are exploiting a legitimate Windows search feature to download arbitrary payloads and compromise systems with RATs like AsyncRAT.

Cyber Security News
Malware authors persistently seek novel approaches to exploit unsuspecting users in the active cyber threat landscape.


Bleeping Computer
Threat actors are abusing the Microsoft Build Engine (MSBuild) to deploy remote access tools and information-stealing malware filelessly as part of an ongoing campaign.

The Hacker News
🚨 Yashma ransomware is on the rampage, hitting English-speaking nations, Bulgaria, China, and Vietnam! Leaked builders are fueling these attacks.


The Hacker News
Russian cyber espionage group linked to the FSB are using a USB worm called LitterDrifter to target Ukrainian organizations.


Cyber Security News
HijackLoader, a modular malware loader observed in 2023, is evolving with new evasion techniques, as it is a variant using a PNG image to


The Hacker News
An information-stealing malware called Amadey is being distributed by means of another backdoor called SmokeLoader.

DarkReading
Vulnerable MS-SQL database servers have external connections and weak account credentials, researchers warn.


The Hacker News
Researchers have observed a surge in email phishing campaigns delivering Latrodectus, a new malware loader believed to be the successor to IcedID.


DarkReading
A literal seven-nation (cyber) army wasn't enough to hold back the famous initial access broker (IAB) for long — it's been chugging along, spreading ransomware, despite a massive takedown in August.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Cyber Security News
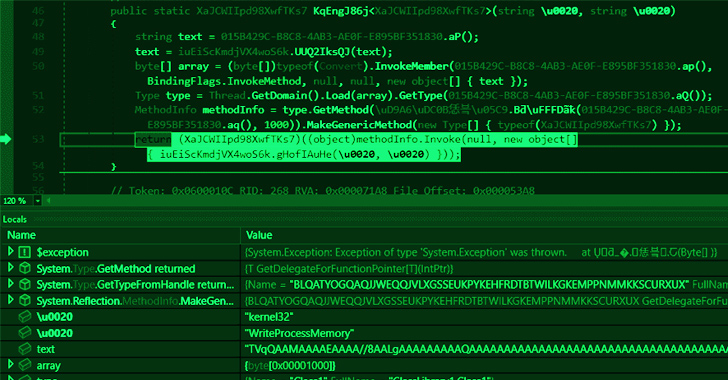
An unrecorded .NET Loader was identified during routine threat hunting that downloads, decrypts, and executes a malicious payloads.


CyberSecurity Dive
Cybercriminals remain the most prolific users of malware, wielding these top strains to deliver ransomware and steal data.

The Hacker News
oubleFinger loader is a multi-stage, highly sophisticated crimeware that targets your Bitcoin wallets.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. Clop ransomware claims the hack of 130 orgs using GoAnywhere MFT flaw CISA adds Fortra […]

The Hacker News
dotRunpeX is a new malware injector that's distributing various known malware families via phishing emails & malicious Google Ads.


The Hacker News
Malware families are making use of PrivateLoader's pay-per-install service in order to expand their victim list.


The Record
Just weeks after an international effort took down the Qakbot botnet's infrastructure, researchers from Cisco Talos say the hackers behind the group have pivoted to spreading ransomware.

Infosecurity News
A new Fortinet analysis revealed a plethora of final-stage payloads delivered by a series of malware droppers


The Hacker News
Researchers have uncovered a shellcode-based packer service that has been helping hackers hide their malware for the past 6 years.

Security Affairs
Experts warn of a new phishing campaign distributing the QakBot malware, months after law enforcement dismantled its infrastructure.


Latest Hacking News
SpyAgent exploits RATs like Teamviewer to deploy other malware and RATs to steal data and gain control on target device.


CyberNews
An increase in cyber incidents compared to 2022 underscores the growing challenges in protecting digital realms.

The Hacker News
🚨 TrueBot, the notorious downloader trojan botnet, is back! Cybersecurity researchers reveal its latest activity surge.

Latest Hacking News
Days after fixing the vulnerability, details have surfaced online about a WinRAR zero-day vulnerability that went under attack. The researchers noticed active exploitation of the vulnerability to target traders. While the patch has already arrived,


Infosecurity News
The report shows an 11% rise in archive files containing malware, including LNK files


The Hacker News
A new malware loader called JinxLoader is being used by threat actors to deliver payloads such as Formbook and XLoader.

The Hacker News
New malware alert! The Zaraza bot steals credentials and is sold on Telegram. It targets 38 web browsers and captures sensitive data.


HACKRead
Russian hackers are escalating cyberattacks, leveraging readily available malware and broadening their targets beyond governments.


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


The Record
CERT-UA is attributing the surge to a group tracked as UAC-0184, which was also recently spotted targeting an unnamed Ukrainian entity in Finland.


HACKRead
Beware! Agent Tesla & Taskun Malware are targeting US Education & Gov. This cyberattack steals data & exploits vulnerabilities.


CSO
The bad actors behind a dangerous malware campaign may not have been put completely out of action by law enforcement, the Talos research group at Cisco warned today.

The Hacker News
Iranian hackers deploying SideTwist backdoor in fresh phishing attack. Separate campaign features new variant of Agent Tesla


The Hacker News
Threat actor UAC-0099 continues to target Ukraine with cyberattacks. They exploit a critical WinRAR flaw to deliver the dangerous LONEPAGE malware.

Cyber Security News
In cybersecurity, information is what ultimately makes it possible to respond to threats effectively and proactively.


The Hacker News
APT28, the Russian nation-state threat actor, is using lures related to the Israel-Hamas war to distribute the HeadLace backdoor.


The Hacker News
A newer version of the Hijack Loader malware has been observed with updated anti-analysis techniques to evade detection.


Security Affairs
Researchers detailed a fully undetectable (FUD) malware obfuscation engine named BatCloak that is used by threat actors. Researchers from Trend Micro have analyzed the BatCloak, a fully undetectable (FUD) malware obfuscation engine used by threat actors to stealthily deliver their malware since September 2022. The samples analyzed by the experts demonstrated a remarkable ability to persistently evade […]

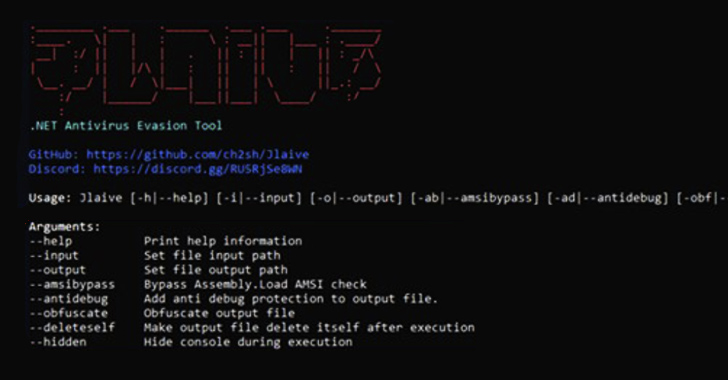
The Hacker News
BatCloak, the undetectable malware obfuscation engine deployed since Sep '22, allowing threat actors to easily load multiple malware families.


Cyber Security News
Stealing cryptocurrencies is a joint event, and a recent addition to this trend is the DoubleFinger loader malware.


The Cyber Express
The City of Defiance has fallen victim to a cyberattack orchestrated by the notorious Knight ransomware group. The City of

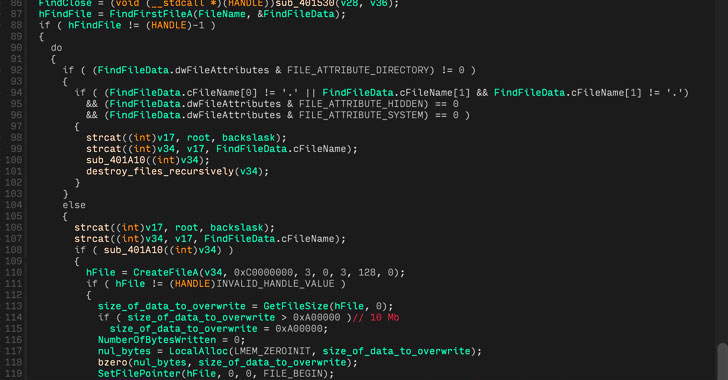
The Hacker News
Researchers have discovered a new data wiper malware, dubbed CaddyWiper, delivered in cyberattacks against Ukraine.

Security Affairs
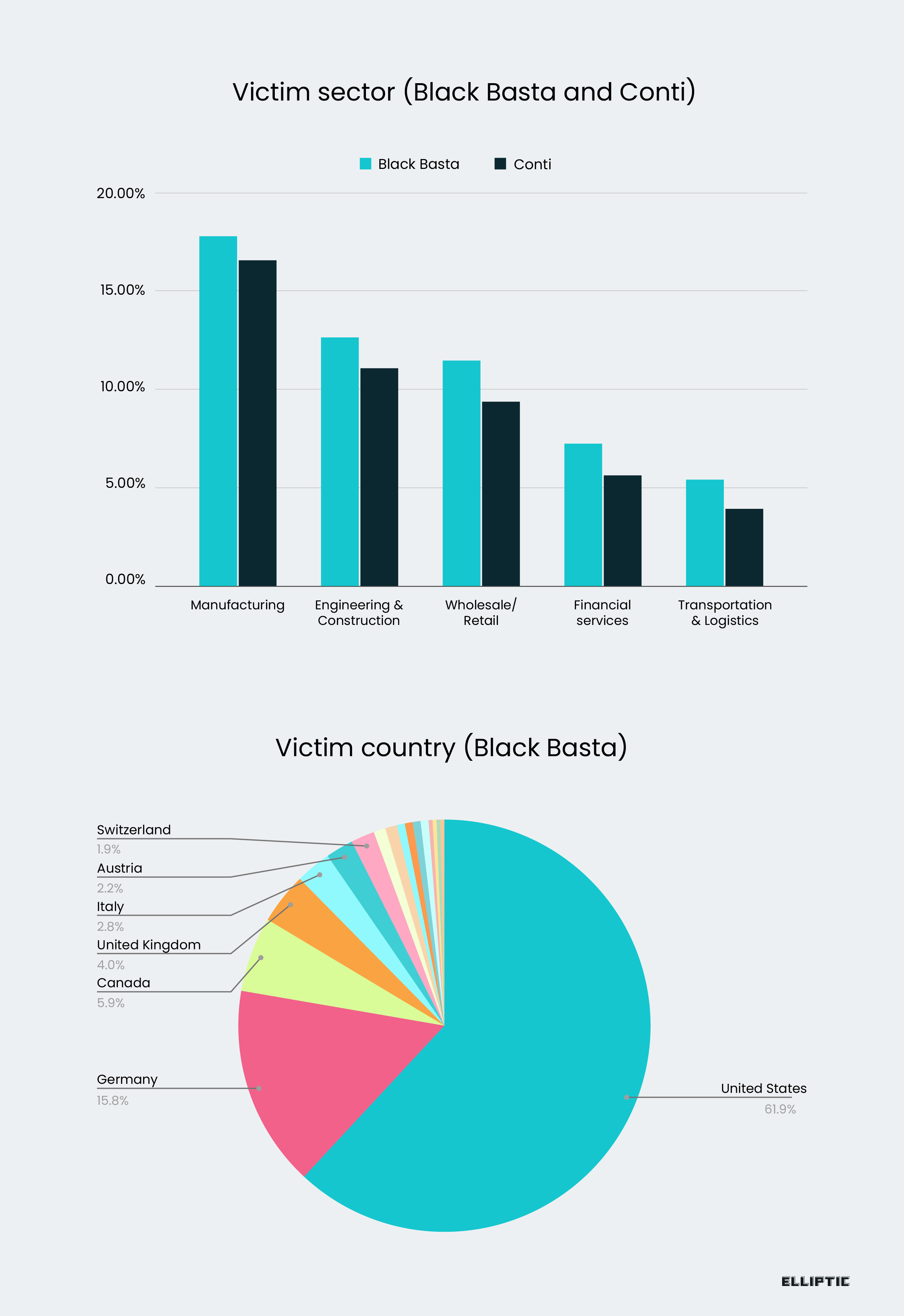
The Black Basta ransomware gang infected over 300 victims accumulating ransom payments exceeding $100 million.


Security Affairs
The CERT of Ukraine (CERT-UA) revealed that Russia-linked threat actors have compromised multiple government websites this week. The Computer Emergency Response Team of Ukraine (CERT-UA) said that Russia-linked threat actors have breached multiple government websites this week. The government experts attribute the attack to UAC-0056 group (DEV-0586, unc2589, Nodaria, or Lorec53). “the Government Computer Emergency […]


Infosecurity News
Cisco Talos found new evidence that Qakbot-affiliated actors were still distributing ransomware despite the August FBI takedown of the threat group

Security Affairs
Researchers discovered a sophisticated multi-stage attack that leverages ScrubCrypt to drop VenomRAT along with many malicious plugins.


Bleeping Computer
A new malware framework known as NetDooka has been discovered being distributed through the PrivateLoader pay-per-install (PPI) malware distribution service, allowing threat actors full access to an infected device.
Loading more articles....