
.webp)
Cyber Security News
PlugX USB worm Infected Over 2.5M Devices
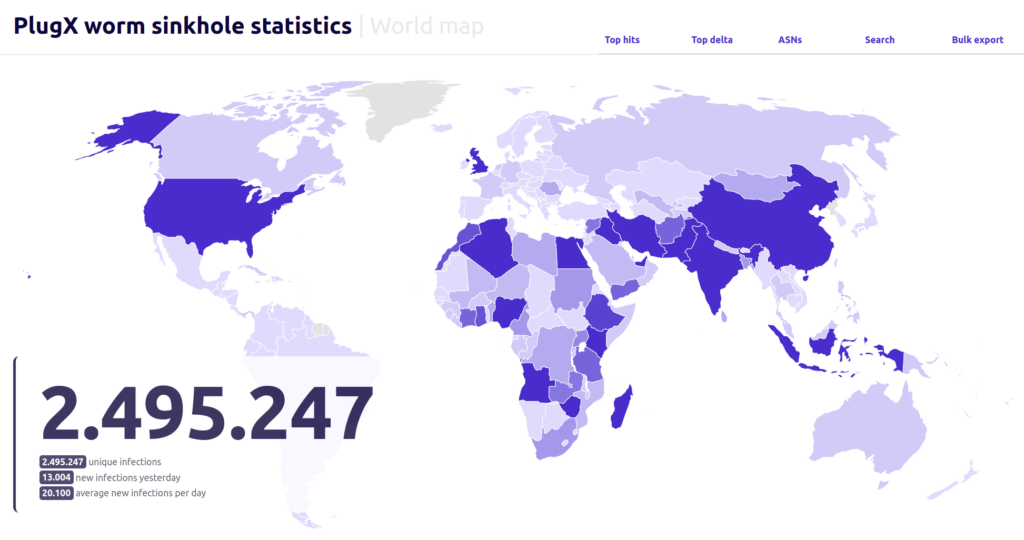
The PlugX USB worm, a piece of malware, has been reported to have infected over 2.5 million devices, posing a threat to global cybersecurity.

.webp)
Cyber Security News
The PlugX USB worm, a piece of malware, has been reported to have infected over 2.5 million devices, posing a threat to global cybersecurity.


The Hacker News
Threat actors are exploiting security vulnerabilities in remote desktop programs to deploy PlugX malware.


Cyber Security News
ASEC (AhnLab Security Emergency response Center) has recently reported that in order to deploy PlugX malware, threat actors are exploiting vulnerabilities


Security Affairs
Researchers observed threat actors deploying PlugX malware by exploiting flaws in Chinese remote control programs Sunlogin and Awesun. Researchers at ASEC (AhnLab Security Emergency response Center) observed threat actors deploying the PlugX malware by exploiting vulnerabilities in the Chinese remote control software Sunlogin and Awesun. Sunlogin RCE vulnerability (CNVD-2022-10270 / CNVD-2022-03672) is known to be […]

The Hacker News
Chinese cyber group targets European ministries with sophisticated HTML smuggling techniques to deploy the PlugX trojan.

The Hacker News
A Chinese government-linked hacker group has been observed targeting Russian officials and military personnel with an updated version of the PlugX.

The Hacker News
Cybersecurity researchers uncover a new variant of PlugX that infects attached USB media devices to spread the malware to other systems.

Bleeping Computer
Researchers have sinkholed a command and control server for a variant of the PlugX malware and observed in six months more than 2.5 million connections from unique IP addresses.

SecurityWeek
More than 90,000 unique IPs are still infected with a PlugX worm variant that spreads via infected flash drives.

The Hacker News
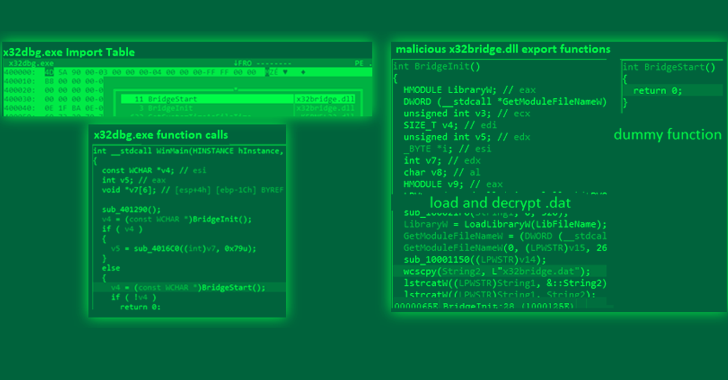
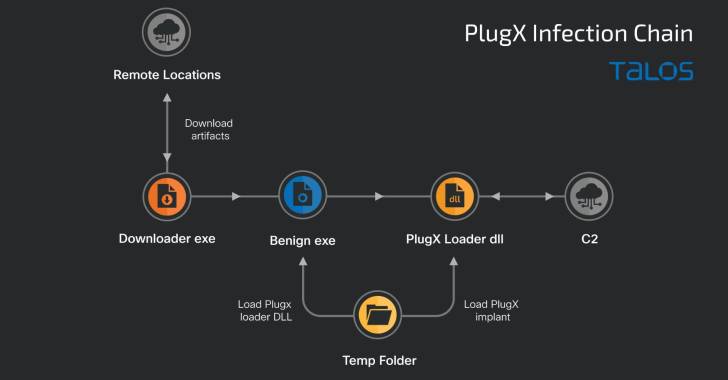
PlugX remote access trojan has been caught disguising itself as a legitimate open source Windows debugger tool called x64dbg to gain control of target

Bleeping Computer
Security researchers have analyzed a variant of the PlugX malware that can hide malicious files on removable USB devices and then infect the Windows hosts they connect to.


Cyber Security News
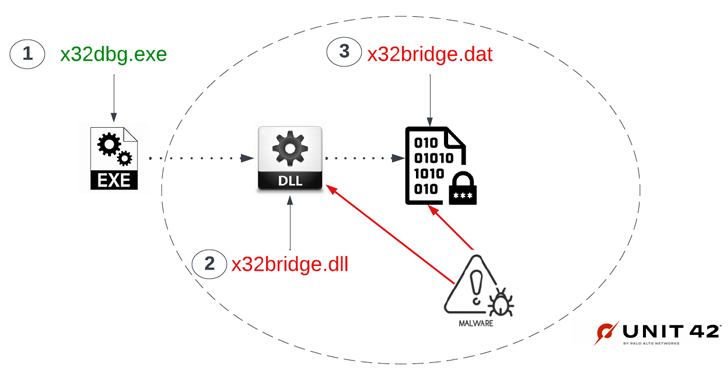
An investigation by cyber security experts at Palo Alto Network’s Unit 42 team recently revealed that a variation of PlugX malware has the ability to conceal harmful files on USB drives and subsequently infect Windows systems upon connection.


Security Affairs
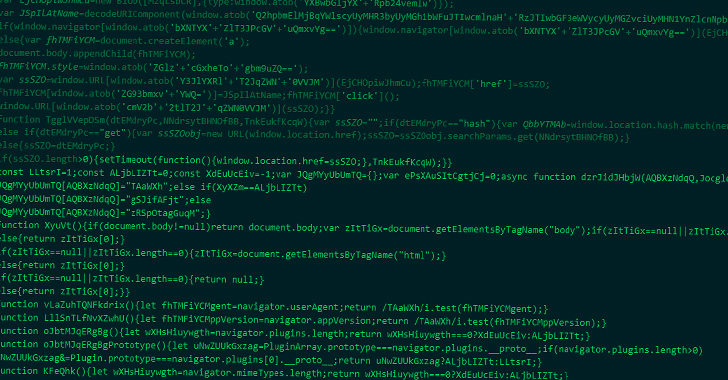
Researchers detailed a new wave of attacks distributing the PlugX RAT disguised as a legitimate Windows debugger tool. Trend Micro uncovered a new wave of attacks aimed at distributing the PlugX remote access trojan masqueraded as an open-source Windows debugger tool called x32dbg. The legitimate tool allows to examine kernel-mode and user-mode code, crash dumps, or CPU […]


Trend Micro
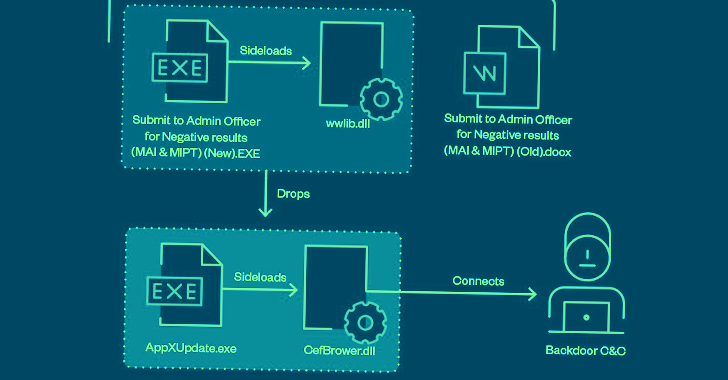
Trend Micro’s Managed Extended Detection and Response (MxDR) team discovered that a file called x32dbg.exe was used to sideload a malicious DLL we identified as a variant of PlugX.

The Hacker News
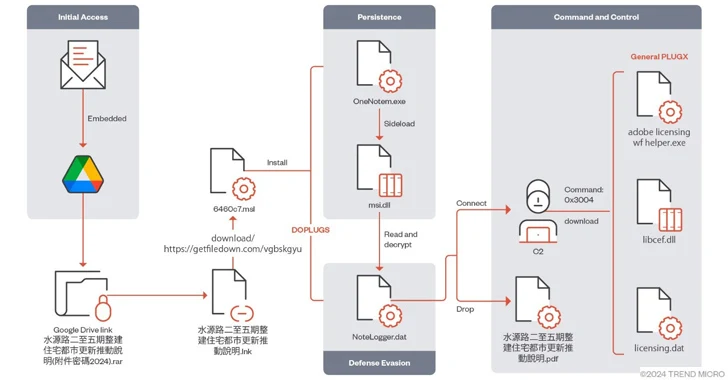
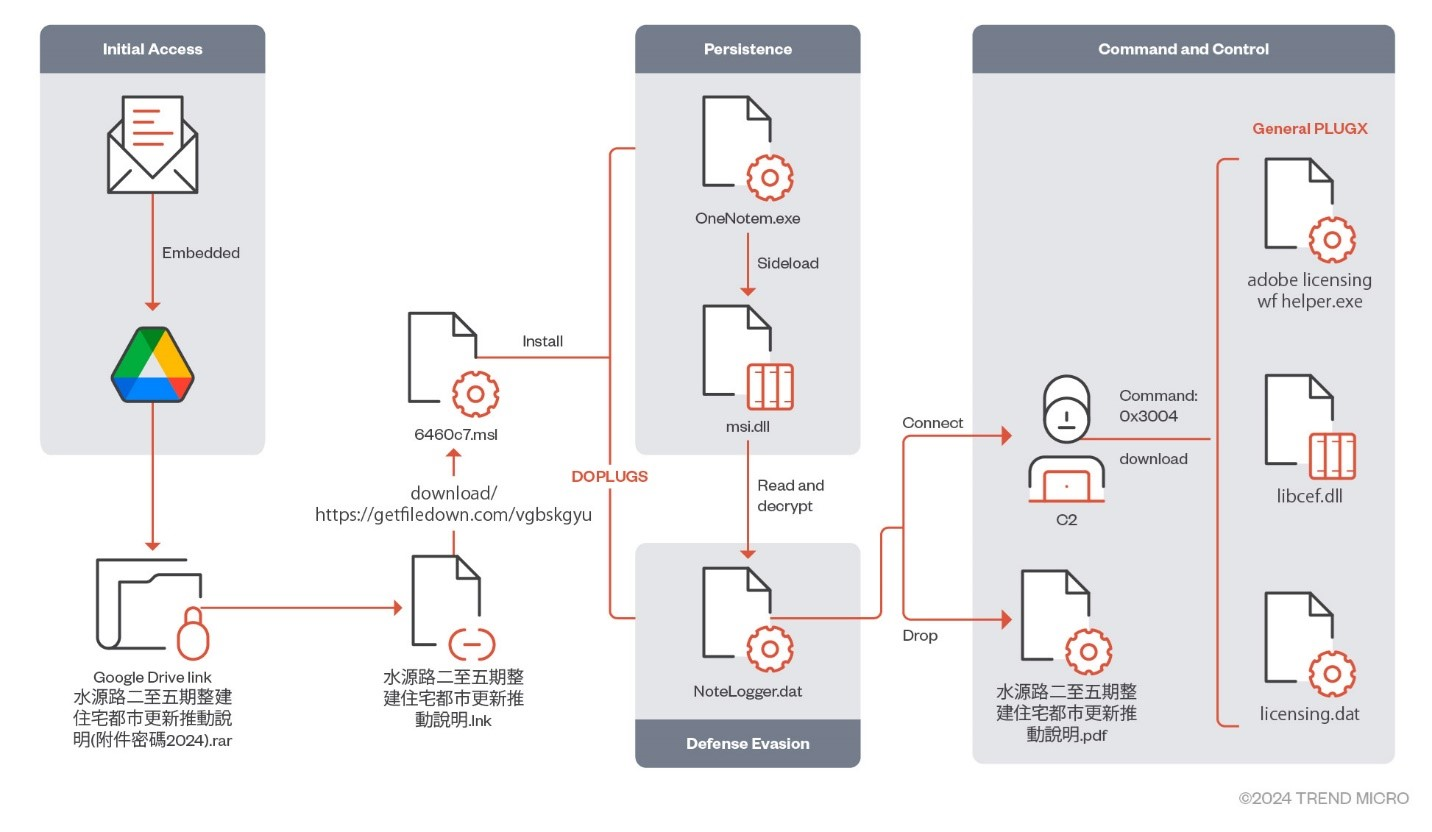
Mustang Panda escalates cyber espionage in Asia with advanced DOPLUGS malware. Discover how this China-linked group targets nations with sophisticated


Infosecurity News
The variant is “wormable” and can infect USB devices to hide itself from the Windows OS


The Record
One of the malware's capabilities — spreading through infected USB flash drives — appears to be giving it multiple lives, according to researchers at Sekoia.


Infosecurity News
The attacks rely on novel delivery methods to deploy a variant of PlugX


The Hacker News
Hackers from China used the PlugX malware to attack government officials in Europe, the Middle East, and South America.


Ars Technica
Ability of PlugX worm to live on presents a vexing dilemma: Delete it or leave it be.

Security Affairs
China-linked APT group Mustang Panda targeted various Asian countries with a variant of the PlugX (aka Korplug) backdoor dubbed DOPLUGS.

DarkReading
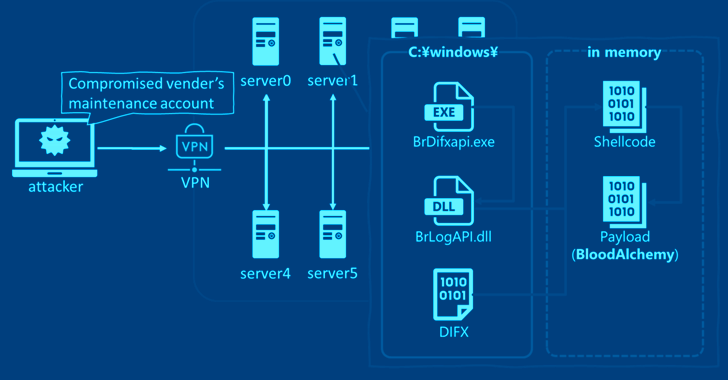
Dubbed Carderbee, the group used legitimate software and Microsoft-signed malware to spread the Korplug/PlugX backdoor to various Asian targets.

DarkReading
Attackers use HTML smuggling to spread the PlugX RAT in the campaign, which has been ongoing since at least December.


SecurityWeek
A new APT called Carderbee has been observed deploying the PlugX backdoor via a supply chain attack targeting organizations in Hong Kong.


Security Affairs
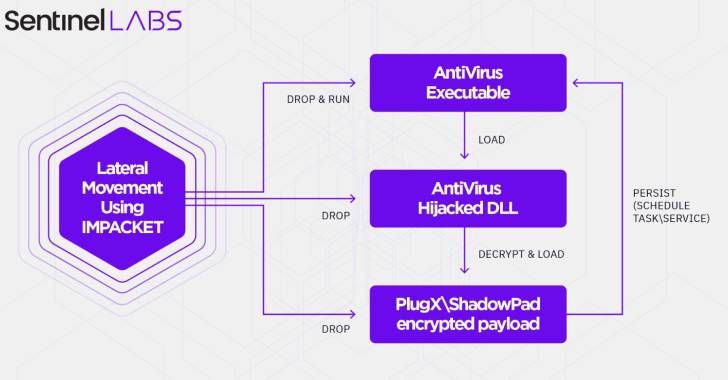
A China-linked APT group, tracked as Moshen Dragon, is exploiting antivirus products to target the telecom sector in Asia. A China-linked APT group, tracked as Moshen Dragon, has been observed targeting the telecommunication sector in Central Asia with ShadowPad and PlugX malware, SentinelOne warns. Both PlugX and ShadowPad malware are very common among China-linked cyberespionage […]


ThreatPost
Mustang Panda’s already sophisticated cyberespionage campaign has matured even further with the introduction of a brand-new PlugX RAT variant.


Security Affairs
China-linked BRONZE PRESIDENT group is targeting government officials in Europe, the Middle East, and South America with PlugX malware. Secureworks researchers reported that China-linked APT group BRONZE PRESIDENT conducted a new campaign aimed at government officials in Europe, the Middle East, and South America with the PlugX malware. Attacks part of this campaign were spotted […]

SecurityWeek
In an ongoing campaign aligned with the current war in Ukraine, Chinese cyberespionage group Mustang Panda has been targeting European diplomats with an updated variant of the PlugX backdoor


Bleeping Computer
A previously unidentified APT hacking group named 'Carderbee' was observed attacking organizations in Hong Kong and other regions in Asia, using legitimate software to infect targets' computers with the PlugX malware.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. PlugX malware delivered by exploiting flaws in Chinese programs Prometei botnet evolves and infected +10,000 […]


Trend Micro
In this blog entry, we focus on Earth Preta's campaign that employed a variant of the DOPLUGS malware to target Asian countries.


Infosecurity News
Symantec described the findings today, saying the ongoing campaign likely started in November 2022


Bleeping Computer
A phishing campaign that security researchers named SmugX and attributed to a Chinese threat actor has been targeting embassies and foreign affairs ministries in the UK, France, Sweden, Ukraine, Czech, Hungary, and Slovakia, since December 2022.


Bleeping Computer
Security researchers analyzing a phishing campaign targeting Russian officials found evidence that points to the China-based threat actor tracked as Mustang Panda (also known as HoneyMyte and Bronze President).

The Hacker News
China-aligned "Moshen Dragon" cyberespionage group has been caught using abusing popular antivirus products to sideload malware.


Security Affairs
China-linked Mustang Panda APT group targets entities in Asia, the European Union, Russia, and the US in a new wave of attacks. In February 2022, Cisco Talos researchers started observing China-linked cyberespionage group Mustang Panda conducting phishing attacks against European entities, including Russian organizations. The attacks were also reported by Google’s TAG team, which confirmed they were for […]


CSO
The China-based APT actor has been found using HTML smuggling to avoid detection.

SecurityWeek
State-sponsored cyberespionage group Mustang Panda starts targeting Russian military as Chinese interests shift towards the Russian-Ukraine war.

SecurityWeek
Researchers at cybersecurity firm SentinelOne have observed a Chinese hacking group taking a trial-and-error approach to abusing antivirus applications for the sideloading of malicious DLLs.


The Record
The number of unique command-and-control servers increased 30% in 2022, an indication that cybercriminals are increasingly using them in attacks


Infosecurity News
Trellix report observed a surge in malicious emails targeting Taiwanese industries and government officials


Bleeping Computer
The China-aligned group tracked as TA416 (aka Mustang Panda) has been consistently targeting European diplomats since August 2020, with the most recent activity involving refreshed lures to coincide with the Russian invasion of Ukraine.

The Hacker News
Research uncovered a new cyber espionage campaign by Chinese 'Mustang Panda' hackers.

The Hacker News
A China-linked nation-state hacking group is using decoys related to the ongoing Russian-Ukrainian war to attack facilities in Europe and the Asia-Pac


The Hacker News
A new threat cluster, dubbed Carderbee, is targeting organizations in Hong Kong & parts of Asia, using software supply chain attacks.


The Hacker News
Cyber warfare escalates amidst rising tensions between China and Taiwan. Find out how malicious actors are using phishing lures and trojans.


The Record
The espionage effort, labeled SmugX by cybersecurity researchers at Check Point, has similarities to previous campaigns linked to China. HTML smuggling helped the malware avoid detection.


ZDNet
It's not necessarily because Russia is considered hostile, however.


The Hacker News
Hackers from China's Mustang Panda hacker group spotted deploying a new variant of Korplug malware, dubbed Hodur.


Security Affairs
Trend Micro addressed a DLL hijacking issue in Trend Micro Security actively exploited by a China-linked threat group to deploy malware. Trend Micro addressed a DLL hijacking flaw in Trend Micro Security that a China-linked threat actor actively exploited to deploy malware. In early May, SentinelOne researchers observed a China-linked APT group, tracked as Moshen […]


Security Affairs
China-linked APT group was spotted using HTML smuggling in attacks aimed at Foreign Affairs ministries and embassies in Europe. A China-linked APT group was observed using HTML smuggling in attacks against Foreign Affairs ministries and embassies in Europe, reports the cybersecurity firm Check Point. The researchers tracked the campaign as SmugX and reported that it […]


CyberScoop
The findings add detail to other suspected Chinese hacking campaigns in Europe related to the Russian invasion of Ukraine.


The Hacker News
Budworm APT group of hackers has resurfaced after 6 years with new cyber espionage attacks targeted at U.S. organizations.


CSO
Latest campaigns by Mustang Panda highlight the threat actor's versatility in terms of the tools and techniques it is able to use.

DarkReading
The war in Ukraine appears to have triggered a change in mission for the APT known as Bronze President (aka Mustang Panda).


The Hacker News
APT Hackers Use ShadowPad Backdoor and MS Exchange Bug to Target Building Automation Systems

The Hacker News
BLOODALCHEMY malware, an updated version of Deed RAT and successor to ShadowPad, targets government organizations in Southern and Southeastern Asia.


The Hacker News
Chinese hackers Mustang Panda caught red-handed targeting Myanmar's Ministry of Defence and Foreign Affairs

The Hacker News
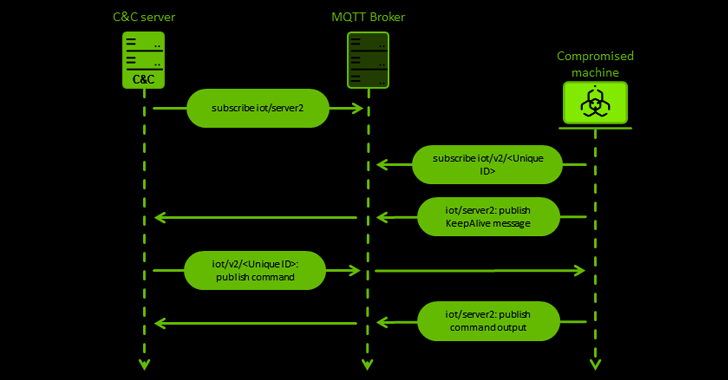
China-based hackers Mustang Panda are using a new custom backdoor called MQsTTang in their latest social engineering campaign against European entitie


CSO
New research links the ShadowPad remote-access Trojan to China's Ministry of State Security and the People's Liberation Army.

DarkReading
Plug X and other information-stealing remote-access Trojans are among the malware targeting networking, manufacturing, and logistics companies in Taiwan.


The Hacker News
Researchers have uncovered a new malware campaign in which Chinese "Lucky Mouse" hackers backdoor chat app MiMi to compromise Microsoft Windows, Linux


Bleeping Computer
Researchers have identified a new cluster of malicious cyber activity tracked as Moshen Dragon, targeting telecommunication service providers in Central Asia.


The Hacker News
RedGolf, a highly-likely Chinese state-sponsored threat group, is using a new custom backdoor called KEYPLUG to target multiple sectors.

CyberScoop
The unknown and unattributed hackers compromised legitimate software in apparent focused attack, researchers said.


The Record
Cybersecurity researchers have uncovered a new campaign by advanced persistent threat (APT) group Mustang Panda to spread a variant of the Korplug malware by exploiting the invasion of Ukraine, COVID-19 and other timely topics.

The Hacker News
Government and state organizations in several Asian countries were targeted by a distinct group of cyberespionage hackers as part of an intelligence.


The Hacker News
Latest Cybersecurity reports unveil two China-linked APT groups targeting ASEAN nations in cyberespionage campaign over the past 3 months.


Bleeping Computer
Security researchers have identified new cyber-espionage activity focusing on government entities in Asia, as well as state-owned aerospace and defense firms, telecom companies, and IT organizations.


Cyber Security News
A new sophisticated cyber espionage group named Earth Estries which overlaps notorious threat group FamousSparrow was unveiled.

The Hacker News
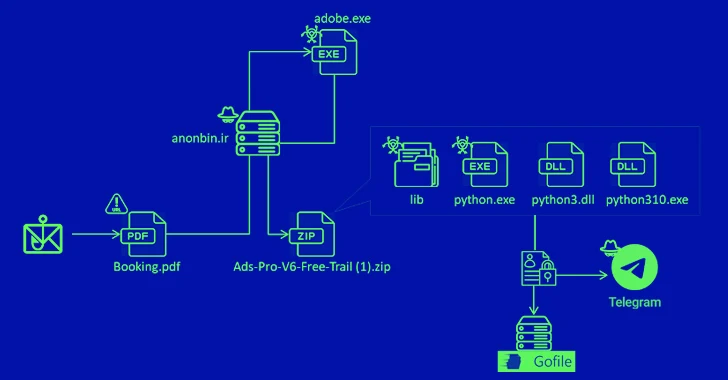
A new campaign is spreading the MrAnon Stealer, a Python-based malware, via fake hotel booking PDFs. It can steal your credentials, browser data, and


Infosecurity News
Researchers at SRLabs have revealed a new suite of decryption tools for Black Basta ransomware


Infosecurity News
Unlike the group’s usual tactics, MQsTTang only has a single stage and does not use obfuscation


CyberNews
Hackers imitated official EU and Ukrainian reports on Russia's war.


DarkReading
The previously undocumented data exfiltration malware was part of a successful cyber-espionage campaign against the Guyanese government, likely by the Chinese.


Infosecurity News
The group previously targeted government agencies and think tanks in Asia and Europe

SecurityWeek
Trend Micro has patched a DLL hijacking vulnerability exploited in attacks by a China-linked cyberespionage group tracked as Moshen Dragon.

The Hacker News
ESET discovers a targeted cyber-espionage campaign in Guyana.


Infosecurity News
Telecommunications companies in Pakistan and Afghanistan and a port in Malaysia targeted


Trend Micro
We recently found a new advanced persistent threat (APT) group that we have dubbed Earth Berberoka (aka GamblingPuppet). This APT group targets gambling websites on Windows, macOS, and Linux platforms using old and new malware families.

The Hacker News
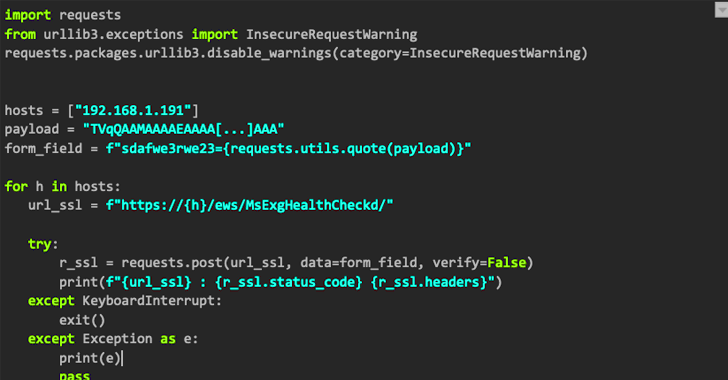
REF2924, a threat group targeting entities in South and Southeast Asia, has been spotted deploying NAPLISTENER.


Infosecurity News
According to SentinelOne, these novel variants emerged between 2022 and 2023

SecurityWeek
China-linked cyberespionage group APT27 was recently observed targeting a US state legislature.


Bleeping Computer
Trend Micro says it patched a DLL hijacking flaw in Trend Micro Security used by a Chinese threat group to side-load malicious DLLs and deploy malware.


Infosecurity News
The attackers established a channel for data exfiltration, including from air-gapped systems


The Hacker News
Chinese Hackers Targeting South American Diplomatic Entities with ShadowPad and QuasarLoader


Infosecurity News
The unauthorized third party stole employee and business customers' data


The Hacker News
Webworm hackers have used customized versions of three older remote access trojans (RATs), including Trochilus, Gh0st, and 9002.


Bleeping Computer
A Chinese-speaking hacking group exploited a zero-day vulnerability in the Windows Win32k kernel driver to deploy a previously unknown remote access trojan (RAT).


CSO
Cyberthreat group DEV-0147 is deploying the ShadowPad RAT to hit diplomatic targets in South America, expanding from its traditional attack turf in Asia and Europe, Microsoft says.


The Hacker News
Space Pirates, a notorious cyber threat actor, has been ramping up attacks in Russia and Serbia over the past year.

The Hacker News
Earth Preta's evolving tactics: Threat actors now using TONEINS, TONESHELL, and PUBLOAD malware for more effective infiltration.


The Hacker News
Budworm, a China-linked group, strikes again with updated malware tools, targeting government and telecom entities.


ZDNet
Just as criminals seized on the pandemic, this group is trying to capitalize on Russia's invasion of Ukraine.

The Hacker News
Lucky Mouse has developed SysUpdate, a malware toolkit with a Linux version, and updated the artifact since July 2022.


The Hacker News
Learn more about the SOGU and SNOWYDRIVE campaigns targeting public and private sector entities worldwide.

The Hacker News
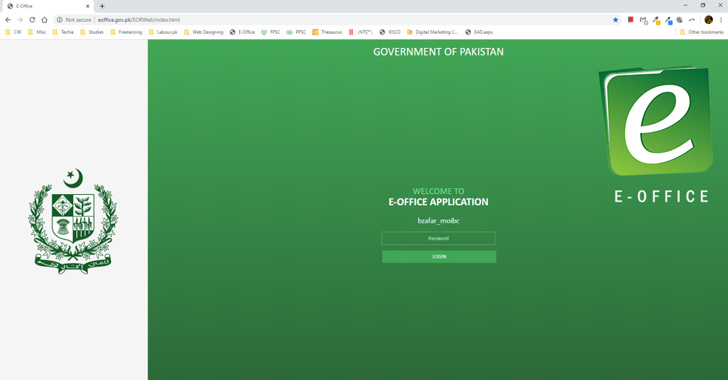
A sophisticated threat actor is targeting Pakistan government entities through a trojanized version of the E-Office application.


The Hacker News
China-linked Bronze Highland hackers aka Daggerfly group is targeting telecom services providers in Africa using spear-phishing and MgBot malware.


The Hacker News
Government, aviation, education, and telecom sectors in South and Southeast Asia are under attack!


SecurityWeek
Symantec warns that the Redfly APT appears to be focusing exclusively on targeting critical national infrastructure organizations.
Loading more articles....