

The Hacker News
Popular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
Malicious "test files" linked to the XZ Utils backdoor found in popular Rust crate liblzma-sys, downloaded over 21,000 times.


The Hacker News
Malicious "test files" linked to the XZ Utils backdoor found in popular Rust crate liblzma-sys, downloaded over 21,000 times.

-1.webp)
Cyber Security News
Three new zero-days have been reported to Qualcomm which were CVE-2023-33106, CVE-2023-33107, and CVE-2023-33063.

SecurityWeek
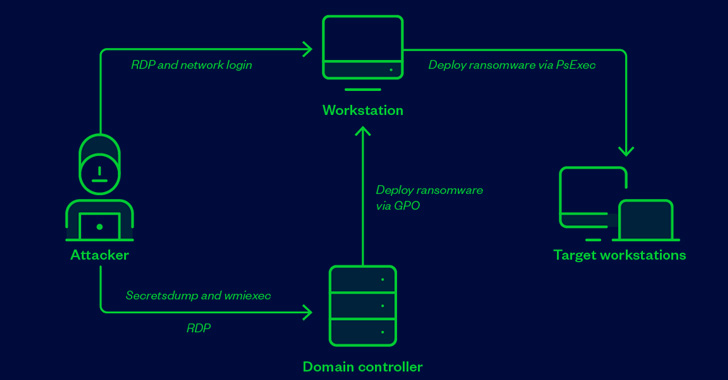
BlackByte ransomware is seen targeting a vulnerability in the legitimate RTCore64.sys driver to disable EDR solutions.


Trend Micro
We investigate mhyprot2.sys, a vulnerable anti-cheat driver for the popular role-playing game Genshin Impact. The driver is currently being abused by a ransomware actor to kill antivirus processes and services for mass-deploying ransomware.


Bleeping Computer
Microsoft has released Sysmon 14 with a new 'FileBlockExecutable' option that lets you block the creation of malicious executables, such as EXE, DLL, and SYS files, for better protection against malware.


Security Affairs
Threat actors abused a vulnerable anti-cheat driver for the Genshin Impact video game to disable antivirus software. Threat actors abused a vulnerable anti-cheat driver, named mhyprot2.sys, for the Genshin Impact video game to disable antivirus software. According to Trend Micro, a cybercrime gang abused the driver to deploy ransomware. The driver provides anti-cheat functions, but […]


Security Affairs
North Korea-linked Lazarus APT has been spotted deploying a Windows rootkit by taking advantage of an exploit in a Dell firmware driver. The North Korea-backed Lazarus Group has been observed deploying a Windows rootkit by relying on exploit in a Dell firmware driver dbutil_2_3.sys, ESET researchers warn. The discovery was made by ESET researchers while […]

%20--%20Supply%20Chain%20Backdoor%20(1).webp)
Cyber Security News
Fedora Linux 40 beta users have been urged to take immediate action after an Upstream supply chain attack that has compromised SSH protocol.

SecurityWeek
Major Linux distributions have been impacted by a supply chain attack involving backdoored versions of the XZ Utils data compression library.


The Hacker News
Secret backdoor found in XZ Utils compression library used by major Linux distros, like Fedora, Kali Linux, and openSUSE.


SC Magazine
The critical supply chain threat affects beta releases of Red Hat Fedora, Debian and more.


Infosecurity News
A backdoor in XZ Utils, a widely used file-compressing software in Linux systems, could have led to a critical supply chain attack had a Microsoft researcher not spotted it in time

HACKRead
A vulnerability, CVE-2024-3094, was discovered in XZ Utils package. This vulnerability threatens Linux systems with backdoor attacks.


The Hacker News
Researchers uncover vulnerabilities in 34 Windows drivers that non-privileged hackers can exploit to take control of your device and execute code.


Bleeping Computer
Hackers are abusing an anti-cheat system driver for the immensely popular Genshin Impact game to disable antivirus software while conducting ransomware attacks.


DarkReading
Had a researcher not spotted the malware when he did, the outcome could have been much worse.


Security Affairs
The BlackByte ransomware operators are leveraging a flaw in a legitimate Windows driver to bypass security solutions. Researchers from Sophos warn that BlackByte ransomware operators are using a bring your own vulnerable driver (BYOVD) attack to bypass security products. In BYOVD attacks, threat actors abuse vulnerabilities in legitimate, signed drivers, on which security products rely, […]

SecurityWeek
A vulnerable anti-cheat driver for the Genshin Impact video game has been abused in ransomware attacks to disable antivirus programs.


Bleeping Computer
A new hacking campaign exploits Sunlogin flaws to deploy the Sliver post-exploitation toolkit and launch Windows Bring Your Own Vulnerable Driver (BYOVD) attacks to disable security software.


Security Affairs
US CISA added actively exploited flaws in Fortra MFT, Intel driver, and TerraMaster NAS to its Known Exploited Vulnerabilities Catalog. US CISA added actively exploited flaws in Fortra MFT, Intel driver, and TerraMaster NAS, respectively tracked as CVE-2023-0669, CVE-2015-2291, and CVE-2022-24990, to its Known Exploited Vulnerabilities Catalog. The CVE-2015-2291 flaw (CVSS v3 score 7.8) is a […]


Latest Hacking News
Researchers have warned users about the new BlackByte ransomware campaign that exploits a legit but vulnerable Windows driver. The ransomware employs this strategy to evade detection, making it difficult to prevent the attack. BlackByte Ransomware Abuses


SecurityWeek
Two memory safety vulnerabilities in WatchGuard and Panda Security products could lead to code execution with System privileges.


DarkReading
In this Tech Tip, we outline how to check if a system is impacted by the newly discovered backdoor in the open source xz compression utility.

Cyber Security News
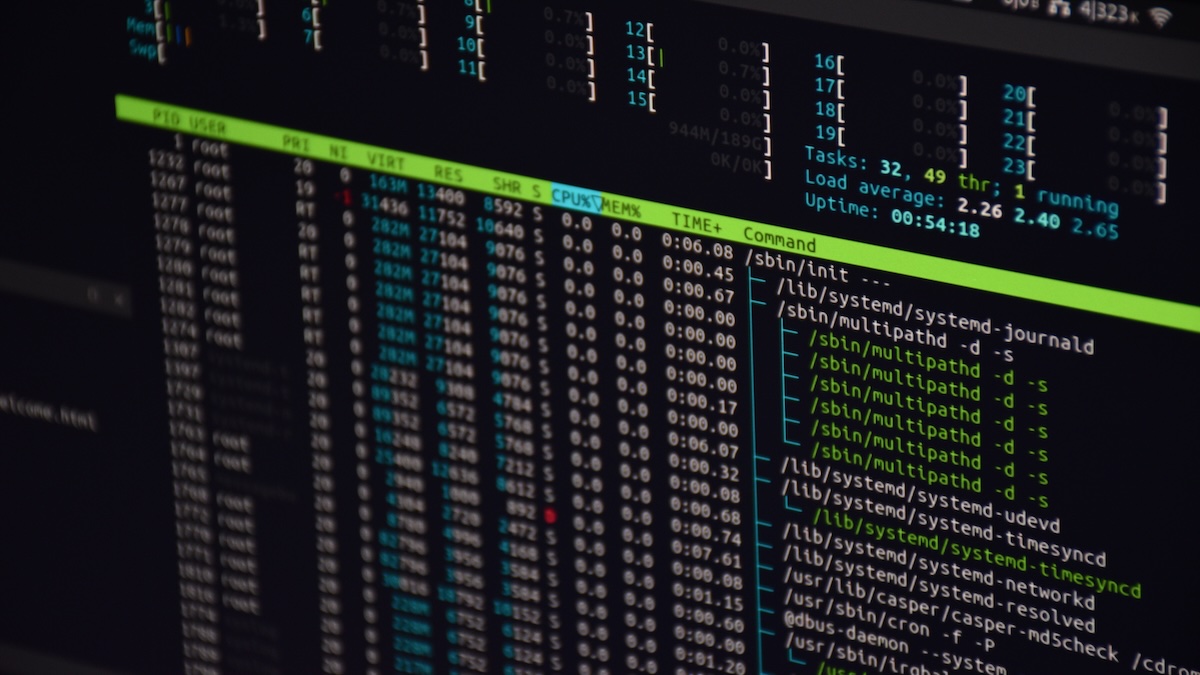
With a CVSS score of 7.5, a high-severity IPv6 implementation issue in the Linux kernel identified as CVE-2023-6200.

The Hacker News
CISA has added three more actively exploited vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog.

The Hacker News
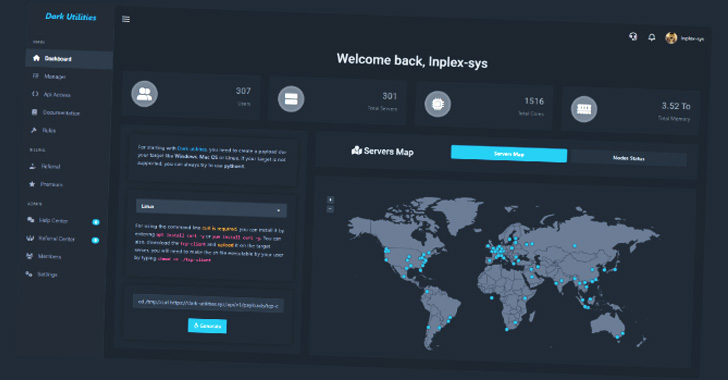
An increasing number of malware attacks are leveraging a nascent command-and-control service called Dark Utilities.


Bleeping Computer
The BlackByte ransomware gang is using a new technique that researchers are calling "Bring Your Own Driver," which enables bypassing protections by disabling more than 1,000 drivers used by various security solutions.


The Cyber Express
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ

.webp)
Cyber Security News
Agenda ransomware group, also known by its aliases Qilin and Water Galura, has been ramping up its attacks on a global scale.

The Hacker News
Ransomware hackers are abusing an anti-cheat system driver for the extremely popular game Genshin Impact to disable antivirus software.


Security Affairs
Dark Utilities “C2-as-a-Service” is attracting a growing number of customers searching for a command-and-control for their campaigns. The popularity of the Dark Utilities “C2-as-a-Service” is rapidly increasing, over 3,000 users are already using it as command-and-control for their campaigns. Dark Utilities was launched in early 2022, the platform that provides full-featured C2 capabilities to its users. Dark […]


Bleeping Computer
A threat actor known as Spyboy is promoting a Windows defense evasion tool called "Terminator" on the Russian-speaking forum RAMP (short for Russian Anonymous Marketplace).


Bleeping Computer
Millions of HP OMEN laptop and desktop gaming computers are exposed to attacks by a high severity vulnerability that can let threat actors trigger denial of service states or escalate privileges and disable security solutions.


Infosecurity News
Two open source organizations have revealed attempts to socially engineer project takeovers

.webp)
Cyber Security News
Attackers tried to take over the JavaScript project from OpenJS Foundation, which is home to JavaScript projects utilized by billions of


The Hacker News
A cryptojacking campaign called Commando Cat is exploiting exposed APIs


HACKRead
The OpenSSF issued alerts for social engineering takeovers of open-source projects after hackers tried to gain control of an OpenJS-hosted project.

The Hacker News
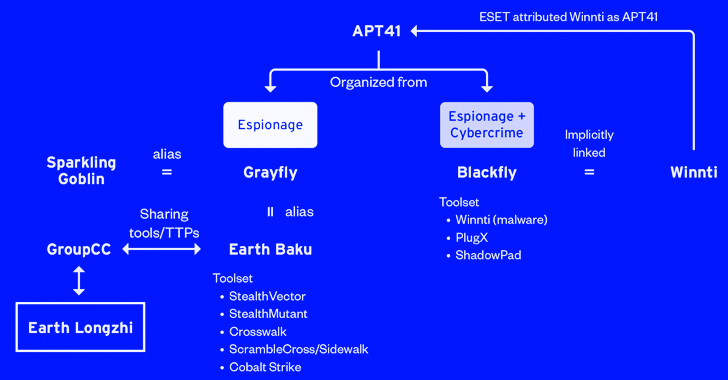
Researchers have identified a previously undocumented subgroup of APT41 that has been targeting entities located in East and Southeast Asia and Ukrain

Bleeping Computer
The notorious North Korean hacking group 'Lazarus' was seen installing a Windows rootkit that abuses a Dell hardware driver in a Bring Your Own Vulnerable Driver attack.


Trend Micro
We looked into the campaigns deployed by a new subgroup of advanced persistent threat (APT) group APT41, Earth Longzhi. This entry breaks down the technical details of the campaigns in full as presented at HITCON PEACE 2022 in August.


Bleeping Computer
In DDoS Protection, Gcore uses the bundle of XDP and regular expressions (regex). This article will explain why Gcore started using this solution (regex in XDP) and how they bound them via a third-party engine and API development.


Bleeping Computer
A previously unknown Chinese APT (advanced persistent threat) hacking group dubbed 'Earth Longzhi' targets organizations in East Asia, Southeast Asia, and Ukraine.


Security Affairs
Ransomware operators use the AuKill tool to disable EDR software through Bring Your Own Vulnerable Driver (BYOVD) attack. Sophos researchers reported that threat actors are using a previously undocumented defense evasion tool, dubbed AuKill, to disable endpoint detection and response (EDR) software. The tool relies on the Bring Your Own Vulnerable Driver (BYOVD) technique to disable the […]

Bleeping Computer
Kali Linux 2021.4 was released today by Offensive Security and includes further Apple M1 support, increased Samba compatibility, nine new tools, and an update for all three main desktop.


The Hacker News
As part of another BYOVD attack, BlackByte ransomware exploits a flaw in a legitimate Windows driver to bypass security software.


Cyber Security News
Users can keep their internet traffic private and anonymous with these ubiquitous utilities while avoiding restrictions or censorship on their usage of the internet.

Infosecurity News
BlackByte delivers new way to circumvent endpoint detection


Infosecurity News
Kaspersky experts developed the tool after analyzing Shutdown.log, a file retaining reboot information


The Hacker News
Cyber criminals are taking advantage of Sunlogin software vulnerabilities to carry out post-exploitation activities with the Sliver C2 framework.

SecurityWeek
The discovery of the XZ Utils backdoor reminds an F-Droid developer of a similar incident that occurred a few years ago.

Latest Hacking News
US cybersecurity officials have issued a detailed advisory alerting cyberattacks on critical ICS infrastructure via tools. US warns companies to be aware of such APT attacks. Industrial Control System (ICS) Cyberattacks Via Custom APT Tools Through a

SecurityWeek
North Korea’s Lazarus hackers were seen exploiting a Dell DBUtil driver vulnerability to disable security mechanisms on target Windows machines.


DarkReading
Unlike the SolarWinds and CodeCov incidents, all that it took for an adversary to nearly pull off a massive supply chain attack was some slick social engineering and a string of pressure emails.


Bleeping Computer
Microsoft has released the optional KB5011563 cumulative update preview for Windows 11, with fixes for stop errors triggering blue screens of death (BSOD) and other issues.


The Hacker News
Researchers warn of BiBi-Windows Wiper, a dangerous Windows version of a wiper malware used in cyber attacks on Israel.

Cyber Security News
the North Korean hacking group, Lazarus installed a Windows rootkit that exploited a Dell hardware driver. read more here.


Ars Technica
An unknown threat actor is exploiting the vulnerability to create admin accounts.


DataBreaches
Quinn Emanuel Urquhart & Sullivan, LLP write, in part: Companies face yet another major risk after a data breach—one which is increasing...


Bleeping Computer
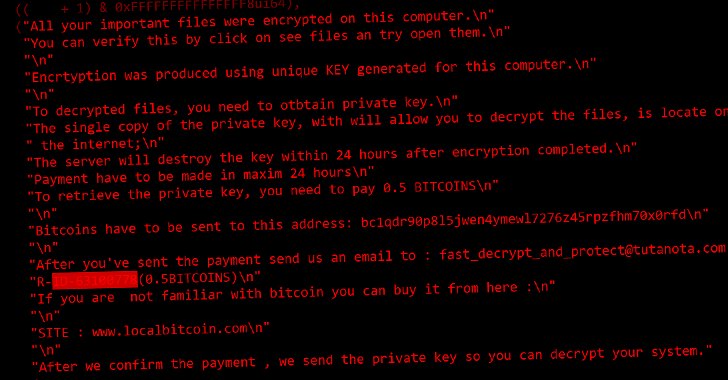
A previously undocumented data wiper named CryWiper is masquerading as ransomware, extorting victims to pay for a decrypter, but in reality, it just destroys data beyond recovery.


Bleeping Computer
The Russian 'Sandworm' hacking group has been linked to an attack on Ukrainian state networks where WinRar was used to destroy data on government devices.

The Hacker News
New CryWiper malware disguised as ransomware targeting Russian government agencies, including mayor's offices and courts.


ZDNet
FBI raises an alarm about RagnarLocker, a ransomware gang that hides its malware inside a Windows XP virtual machine.


Bleeping Computer
Hackers are compromising websites to inject scripts that display fake Google Chrome automatic update errors that distribute malware to unaware visitors.


ZDNet
How embarrassing! It turns out there was a security hole lurking in Linux's netfilter firewall program.


Cyber Security News
The top-level executives at more than 100 global organizations have been shaken by cloud account takeover incidents.


Bleeping Computer
A previously undocumented data wiper named CryWiper is masquerading as ransomware, extorting victims to pay for a decrypter, but in reality, it just destroys data beyond recovery.


Ars Technica
Thousands of hack attempts made in the days following discovery of the vulnerability.

The Hacker News
North Korean Lazarus hackers have been observed deploying a Windows rootkit on targeted computers by exploiting a vulnerability in a Dell drivers.


Security Affairs
CERT-UA is warning of destructive cyberattacks conducted by the Russia-linked Sandworm APT group against the Ukraine public sector. Russia-linked APT group Sandworm is behind destructive cyberattacks against Ukrainian state networks, the Ukrainian Government Computer Emergency Response Team (CERT-UA) warns. The Sandworm group (aka BlackEnergy, UAC-0082, Iron Viking, Voodoo Bear, and TeleBots) has been active since 2000, it operates under the control […]


Bleeping Computer
A recently uncovered ransomware operation named 'Kasseika' has joined the club of threat actors that employs Bring Your Own Vulnerable Driver (BYOVD) tactics to disable antivirus software before encrypting files.


Trend Micro
CVE-2024-27198 and CVE-2024-27199 are vulnerabilities within the TeamCity On-Premises platform that can allow attackers to gain administrative control over affected systems.

Cyber Security News
First identified in 2020, Sysrv is a botnet that uses a Golang worm to infect devices and deploy cryptominers, propagates by exploiting


Cyber Security News
Using Sunlogin flaws, a new hacking campaign has been detected by security analysts at AhnLab Security Emergency Response Center (ASEC) that takes advantage of Windows BYOVD attacks to disable security software and deploy the post-exploitation toolkit Sliver.

The Hacker News
Cybercriminals are distributing info-stealing malware to developers through Python Package Index (PyPI).


Bleeping Computer
A new malware campaign disguised as Google Translate or MP3 downloader programs was found distributing cryptocurrency mining malware across 11 countries.

Cyber Security News
Ransomware attacks have been increasing rapidly. The Two countries Ukraine and Russia have been facing severe ransomware attacks in the past few weeks. Many were state-sponsored but some were personal.


CSO
Traditionally known to target only Windows systems, the new Linux version of the IceFire ransomware exploits an IBM Aspera Faspex file-sharing vulnerability, according to SentinelLabs.


Bleeping Computer
A new Sugar Ransomware operation actively targets individual computers, rather than corporate networks, with low ransom demands.

_Igor_Golovnov_Alamy.jpg?disable=upscale&width=1200&height=630&fit=crop)
DarkReading
A new and improved variant of the group's malware combines fileless infection, BYOVD, and more to cause havoc in virtual environments.

The Hacker News
Chinese state-sponsored hacking group Earth Longzhi resurfaces after six months of inactivity, targeting government, healthcare, tech.


Bleeping Computer
The PyPi python package repository is being bombarded by a wave of information-stealing malware hiding inside malicious packages uploaded to the platform to steal software developers' data.


ZDNet
US government puts energy sector on high alert over specialized malware for disrupting industrial control systems.


Bleeping Computer
A new version of the BiBi Wiper malware is now deleting the disk partition table to make data restoration harder, extending the downtime for targeted victims.


Bleeping Computer
Data-wiping attacks are becoming more frequent on Israeli computers as researchers discovered variants of the BiBi malware family that destroys data on both Linux and Windows systems.


The Hacker News
Kasseika, the latest ransomware kid on the block, is using a sneaky trick called BYOVD to disarm your defenses before encrypting your files! It even


DarkReading
Attackers are using custom malware to exploit drivers and terminate security processes so they can deploy ransomware.

SecurityWeek
A SafeBreach security researcher discovered several vulnerabilities that allowed him to turn endpoint detection and response (EDR) and antivirus (AV) tools into wipers.


Ars Technica
Malicious submissions have been a fact of life for code repositories. AI is no different.


Trend Micro
This blog entry discusses the Agenda ransomware group's use of its latest Rust variant to propagate to VMWare vCenter and ESXi servers.

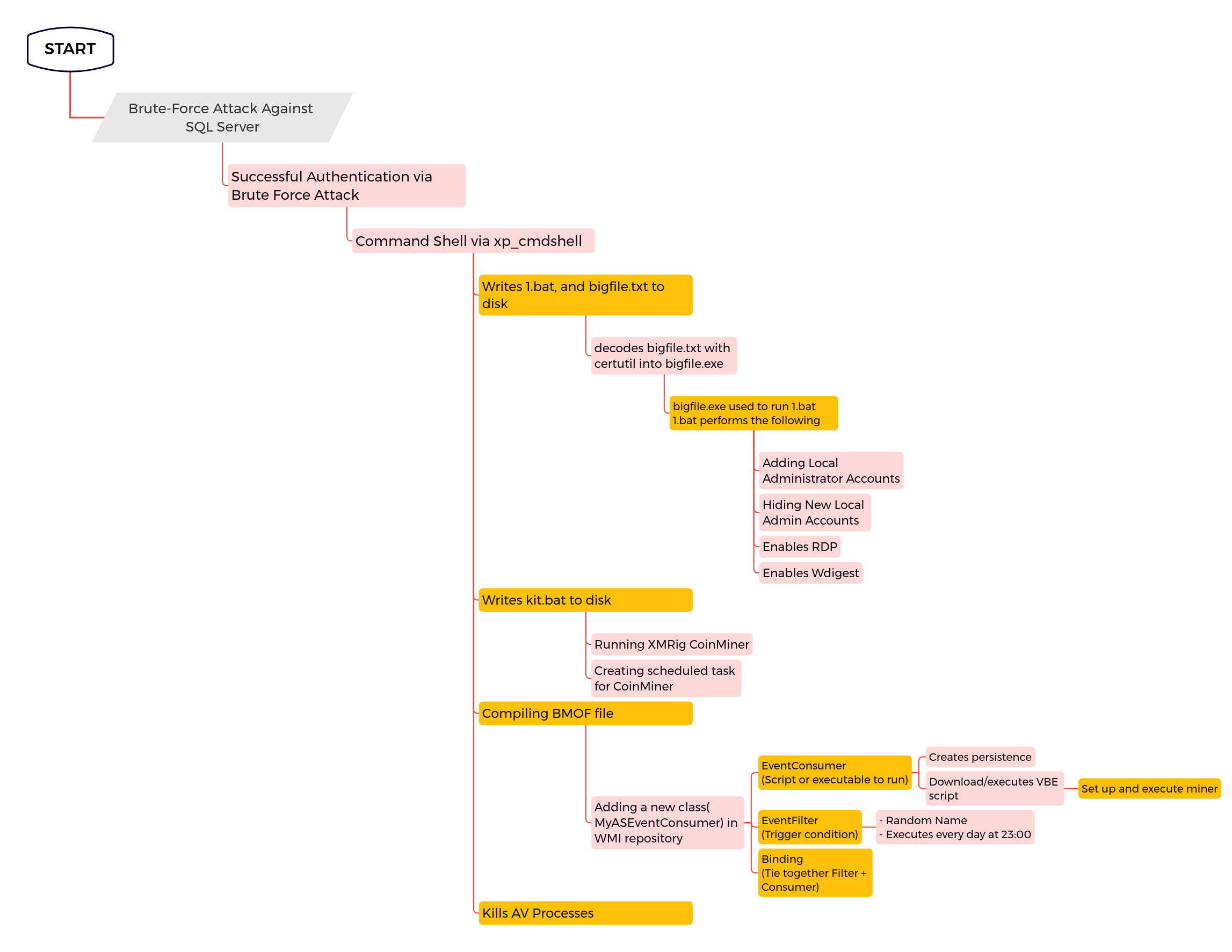
The DFIR Report
In March 2022, we observed an intrusion on a public-facing Microsoft SQL Server. The end goal of this intrusion was to deploy a coin miner.


Trend Micro
After months of dormancy, Earth Longzhi, a subgroup of advanced persistent threat (APT) group APT41, has reemerged using new techniques in its infection routine. This blog entry forewarns readers of Earth Longzhi’s resilience as a noteworthy threat.


Bleeping Computer
The Rhysida ransomware as a service (RaaS) operation that emerged in May 2023 is gradually leaving the period of obscurity behind, as a recent wave of attacks on healthcare organizations has forced government agencies and cybersecurity companies to pay closer attention to its operations.


Ars Technica
Authorities who took down the ransomware group brag about their epic hack.


ThreatPost
CaddyWiper is one in a barrage of data-wiping cyber-attacks to hit the country since January as the war on the ground with Russia marches on.


Bleeping Computer
The new Akira ransomware operation has slowly been building a list of victims as they breach corporate networks worldwide, encrypt files, and then demand million-dollar ransoms.


Bleeping Computer
A suspected North Korean hacking group is targeting security researchers and media organizations in the U.S. and Europe with fake job offers that lead to the deployment of three new, custom malware families.

Trend Micro
We analyze the ransomware White Rabbit and bring into focus the familiar evasion tactics employed by this newcomer.


Trend Micro
Trend Micro Research observed the resurgence of the Cuba ransomware group that launched a new malware variant using different infection techniques compared to past iterations. We discuss our initial findings in this report.


Bleeping Computer
The Akira ransomware operation uses a Linux encryptor to encrypt VMware ESXi virtual machines in double-extortion attacks against companies worldwide.


ThreatPost
The ever-shifting, ever-more-powerful malware is now hijacking email threads to download malicious DLLs that inject password-stealing code into webpages, among other foul things.
Loading more articles....