

DataBreaches
US Government Disrupts Botnet Controlled by Russian Government Hackers
Lorenzo Franceschi-Bicchierai reports: The U.S. government announced on Wednesday that it had disrupted a botnet controlled by Russian government hackers...


DataBreaches
Lorenzo Franceschi-Bicchierai reports: The U.S. government announced on Wednesday that it had disrupted a botnet controlled by Russian government hackers...


Security Affairs
The US authorities dismantled the Moobot botnet, which was controlled by the Russia-linked cyberespionage group APT28


The Record
US Attorney General Merrick Garland announced Wednesday that US officials have disrupted a global botnet of thousands of infected devices allegedly controlled by the Russian military.

SecurityWeek
The U.S. government says it has disabled the "Cyclops Blink" botnet of hardware devices controlled by Russia’s main intelligence agency (GRU).


Cyber Security News
A security flaw has been identified in the Cisco DNA Center, which has the potential to enable unauthorized access by a remote attacker.


Infosecurity News
Social media giant restricts access to state media and disrupts disinfo networks


Computerworld
The ransomware defense baked into Windows 10 and 11 lets users and admins protect certain folders from “untrusted” apps. But it may block apps you trust, causing frustration and wasted time. Caution is advised.


DataBreaches
Sergiu Gatlan reports: GitHub revealed today that an attacker is using stolen OAuth user tokens (issued to Heroku and Travis-CI) to download data from private...


Cyber Security News
An unauthenticated remote attacker could exploit multiple high-severity vulnerabilities detected in Passwordstate, an online password management solution, to obtain plaintext passwords for users of the service.


Security Affairs
The Conti ransomware group takes over TrickBot malware operation and plans to replace it with BazarBackdoor malware. TrickBot operation has arrived at the end of the journey, according to AdvIntel some of its top members move under the Conti ransomware gang, which is planning to replace the popular banking Trojan with the stealthier BazarBackdoor. TrickBot is […]

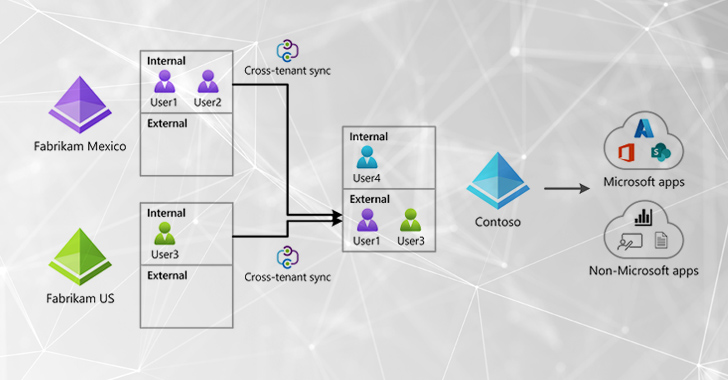
The Hacker News
Attackers are misusing Microsoft's native features to achieve their goals. Dive into the details of the Cross-Tenant Synchronization attack.


SecurityWeek
The US government says it has neutralized a network of hundreds of Ubiquiti Edge OS routers under the control of the notorious APT28 group.


DataBreaches
Phil Muncaster reports: Ukrainian law enforcers have arrested a suspected botnet herder responsible for controlling an automated network of around 100,000...


DataBreaches
Simon Sharwood reports: An Indian flight booking website majority-owned by US retail colossus Walmart has experienced a data breach, but is saying very little...


CyberSecurity Dive
Russia’s GRU-backed group exploited hundreds of vulnerable routers to conduct spear phishing and credential harvesting attacks against U.S. targets.


Bleeping Computer
The Federal Bureau of Investigation (FBI) has issued an alert about hackers targeting healthcare payment processors to route payments to bank accounts controlled by the attacker.


The Record
The British government has been accused of dropping the ball by allowing a company with alleged ties to the Chinese government to acquire a semiconductor start-up.


Bleeping Computer
A devious new phishing technique allows attackers to bypass MFA by secretly having victims log in to their accounts directly on attacker-controlled servers using VNC.


PCMag
Cloudflare says the hacker infiltrated some systems by exploiting credentials that were stolen during the Okta breach last October. However, no Cloudflare customer data was affected.


SecurityWeek
A recently patched Aiohttp vulnerability tracked as CVE-2024-23334 is being targeted by threat actors, including by a ransomware group.


Cyber Security News
HPE OneView is an integrated IT infrastructure management software that automates IT operations and streamlines infrastructure lifecycle management that includes computing, storage, and networking.


SecurityWeek
Attackers are exploiting two path traversal vulnerabilities in the Stagil navigation for Jira – Menus & Themes plugin.


SecurityWeek
Shadowserver sees possible in-the-wild exploitation of a critical Apache OFBiz vulnerability tracked as CVE-2023-49070.


Infosecurity News
Defendant indicted over deployment of REvil ransomware arrives in America


Cyber Security News
Two flaws in Samsung's official app store, the Galaxy App Store, might let attackers install any app without the user's knowledge or lead users to a malicious website.


SecurityWeek
Attackers are attempting to exploit a critical RCE flaw in Apache Struts 2 after researchers publish PoC code.


CyberNews
Hackers target victims via fake game developer companies.


DarkReading
Unlike the SolarWinds and CodeCov incidents, all that it took for an adversary to nearly pull off a massive supply chain attack was some slick social engineering and a string of pressure emails.

Security Affairs
A critical flaw, named ‘BatBadBut’, impacts multiple programming languages, its exploitation can lead to command injection in Windows apps.


Cyber Security News
An authentication bypass vulnerability exists in VMware SD-WAN (Edge). Upon successful exploitation, unauthorized attackers gain access.


Infosecurity News
It now takes threat actors on average just 62 minutes to move laterally from initial access, Crowdstrike claims


DarkReading
The adversary is exploiting two known misconfigurations in the big data technologies to drop a Monero cryptominer.

Cyber Security News
Atlassian released critical and high vulnerabilities which were detected through bug bounty, third-party library scans as well as pentest.


Cyber Security News
A high-severity cross-site scripting (XSS) vulnerability tracked as (CVE-2023-29183) affecting several FortiOS and FortiProxy versions has been patched by Fortinet.


Cyber Security News
SAP has released their updates for patch day of this month in which several vulnerabilities have been fixed and CVEs have been updated. The severity of the patched bugs varies from 4.5 (medium) to 10.0 (critical).


Infosecurity News
GitHub says npm is among the organizations affected

CSO
Thanks to the availability of malware such as Emotet, deploying backdoors on victims' networks is becoming easier and more lucrative for cybercriminals.

Cyber Security News
VMware has been discovered CVE-2023-34048 and CVE-2023-34056, associated with Out-of-Bounds Write and Partial Information Disclosure.


DarkReading
Just 79 minutes — that's how long it takes attackers to move from an initial compromise to extending their infiltration of a firm's network.

Cyber Security News
The cloud cybersecurity firm, Wiz discovered a chain of critical vulnerabilities in the widely used Azure Database for PostgreSQL Flexible Server. This could result in unauthorized cross-account database access in a region.


Cyber Security News
Cybersecurity researchers at OneKey recently discovered that the TP-Link Archer C5400X router flaw enables attackers to hack devices remotely.

-1.webp)
Cyber Security News
A Denial-of-Service (DoS) vulnerability has been discovered in the Cisco Firepower 4100 Series, Firepower 9300 Security Appliances, and UCS 6300 Series Fabric Interconnects.


Cyber Security News
An open redirect vulnerability in the VMware Workspace ONE UEM console has been identified as CVE-2023-20886.


Cyber Security News
HP Enterprise LaserJet and HP LaserJet Managed printers may be susceptible to information exposure when IPsec is enabled.


Cyber Security News
A 'critical' severity flaw has been detected inFortiOS and FortiProxy, Fortinet, identified as CVE-2023-33308 (CVSS rating 9.8).


ThreatPost
GitHub shared the timeline of breaches in April 2022, this timeline encompasses the information related to when a threat actor gained access and stole private repositories belonging to dozens of organizations.


Cyber Security News
Google has updated the Stable channels to 121.0.6167.85 for Mac and Linux and 121.0.6167.85/.86 for Windows as part of a security update for Chrome.


Cyber Security News
An Open-redirect vulnerability was discovered by IBM which could allow threat actors to spoof the original URL of IBM Security Verify Access.


Infosecurity News
Mandiant’s latest M-Trends report found that vulnerability exploitation was the most common initial infection vector in 2023, making up 38% of intrusions


Infosecurity News
Every second counts as threat actors accelerate lateral movement


SecurityWeek
Malicious hackers are targeting SAP applications at an alarming pace, according to warnings from Onapsis and Flashpoint.

Cyber Security News
Two vulnerabilities have been identified on three Atos Unify OpenScape products, SBC, Branch, and BCF, which are associated with Missing authentication.


Naked Security
The US Independence Day weekend of 2021 wasn’t much of a holiday for cybersecurity staff. That was when the Kaseya attack unfolded…


Cyber Security News
Multiple Information Disclosure vulnerabilities were discovered in the IBM Security Verify Information Queue, which can reveal several internal product details.

Cyber Security News
IBM Security Guardium is a data protection platform that can be used by security teams to automatically analyze data environments sensitive.


Cyber Security News
A security researcher declared the discovery of an unpatched flaw in PayPal that could allow attackers to steal money from users with one click.


The Record
Password management service LastPass now says a well-publicized 2022 incident stemmed from an intrusion on one engineer's home computer.


SecurityWeek
Akamai details more vulnerabilities and patch bypasses leading to zero-click remote code execution in Microsoft Outlook.


Cyber Security News
When Atlassian Companion is installed on macOS, a vulnerability has been detected that enables remote code execution on users' computers.


Cyber Security News
An intrusion detection system called Snort has been found to have a security vulnerability, reported by the cyber security analysts at Team82. And this could trigger the occurrence of a denial of service (DoS) condition, making the system ineffective.


DarkReading
Event organizers should be exercising various cyberattack scenarios to ensure they have the proper checks and balances in place to respond accordingly and maintain resilience.

SecurityWeek
Critical vulnerability in F5 BIG-IP (CVE-2022-1388) is being targeted in attacks as hackers develop exploits.


Infosecurity News
IT security professionals are concerned about the increasing use of AI in cyber-attacks, particularly deepfakes

.webp)
Cyber Security News
Multiple vulnerabilities have been found in IBM QRadar Wincollect which were associated with Denial of service that could allow a threat.


Cyber Security News
Cacti is a web-based open-source network monitoring, fault, and configuration management tool that acts as an RRDtool (round-robin database tool).

Cyber Security News
Recent reports indicate that the Remote Desktop Manager and Devolutions Server have been affected by improper access control and Remote code execution vulnerabilities.


Cyber Security News
Updates for QNAP's network-attached storage (NAS) systems have been released to address a critical security flaw that might allow arbitrary code injection.


Infosecurity News
Cybersecurity experts believe senior leadership teams underestimate cyber-threats


Cyber Security News
Microsoft releases a few patches in December normally, and this year is no exception. Microsoft Patch for December 2022, a total of 52 vulnerabilities in Microsoft Windows and Windows Components, Azure, Office and Office Components, SysInternals, Microsoft Edge (Chromium-based), SharePoint Server, and the.NET framework was fixed by security patches released on Tuesday.


Cyber Security News
Evil QR is a spin-off of a QR Jacking Attack, the latest phishing attempt by threat actors to gain access to the victim's machine.


Cyber Security News
Adobe addressed critical security issues in ColdFusion and InDesign. Users should install security updates immediately to ensure system safety.

Cyber Security News
Junos OS and Junos OS Evolved have been found to be vulnerable to a DoS (Denial of Service) condition which can be exploited.


DarkReading
Alleged teen hacker claims he found an admin password in a network share inside Uber that allowed complete access to ride-sharing giant's AWS, Windows, Google Cloud, VMware, and other environments.


DataBreaches
Through Operation MEDUSA, the FBI, and the U.S. Attorney’s Office for the Eastern District of New York Neutralized the FSB’s Premier Cyberespionage Malware...


Cyber Security News
Cybersecurity analysts at Akamai reported that threat actors exploiting the Microsoft Windows Server 2022 vulnerability to launch DoS attacks.


Infosecurity News
Carrier says attack began in November 2022


DataBreaches
James Hopkin reports: The Huron-Superior Catholic District School Board has confirmed that board officials received a note this morning — delivered through...


Cyber Security News
Microsoft Azure Service Fabric has been exposed to a spoofing vulnerability that has been unveiled recently in a proof-of-concept exploit.


Cyber Security News
Using SPNEGO, a client and a remote server are able to reach a consensus over the protocol to be used to authenticate the connection by agreeing on the protocol to be used.


Cyber Security News
Cisco addressed high-impact vulnerability CVE-2023-20243 in the Cisco Identity Services Engine (ISE) that allows attackers to stop processing Radius packets.


Cyber Security News
Cisco has warned about a serious security issue in the Web Bridge feature of the Cisco Meeting Server. The flaw (CVE-2023-20255) could let someone who is not authorized attack the system and cause a DoS condition.


The Hacker News
Join us for an exclusive webinar on social engineering in cyberattacks. Gain tactical awareness and strategic defense insights. Don't miss it!


Infosecurity News
The malware can cloak a malicious payload that could be remotely controlled by an adversary

SecurityWeek
The median dwell time figure may have less to do with improving defensive postures than with increasing and successful criminal ransomware attacks.


Cyber Security News
The Chinese-based Video surveillance equipment manufacturer has disclosed a critical flaw in their storage products, allowing threat actors to obtain admin permissions.


CyberSecurity Dive
The threat actor ramped up pressure by leaking data on the Australian company’s customers, then quickly backed down for unknown reasons.

Cyber Security News
Cisco was reported with a critical vulnerability that could allow threat actors to log in to the affected devices as a root account.

-1.webp)
Cyber Security News
A self-signed China-originated Rootkit acts as a universal downloader targeting gaming sectors to exfiltrate sensitive information.


The Hacker News
In the digital age, businesses must manage their external attack surface to effectively assess and mitigate cybersecurity risk.


DataBreaches
Jamie Redman reports: On February 10, the well-known developer of Cydia and iOS Jailbreak, Jay Freeman, otherwise known as Saurik, published a Twitter thread...


SecurityWeek
H.R. 7520 prohibits data brokers from selling Americans’ data to foreign adversary countries or entities controlled by them.


DarkReading
Weaponizing Microsoft's own services for command-and-control is simple and costless, and helps attackers better avoid detection.


CSO
Intune Suite will streamline endpoint management with added features for controlled and secure access.


The Record
Bank accounts controlled by Olugbenga Lawal received over $3.6 million in deposits generated by conning people in online scams.


Cyber Security News
Splunk has been reported with a Unauthenticated Log injection vulnerability in the Splunk IT Service Intelligence (ITSI) product.


The Hacker News
More than 200,000 MicroTik routers worldwide are controlled by botnet malware.


ZDNet
Reserves were drained after the attacker awarded themselves voting rights.

Bleeping Computer
Ukrainian police have arrested a hacker who controlled a 100,000 device botnet used to perform DDoS attacks on behalf of paid customers.

The Hacker News
FBI has dismantled a Russia-linked botnet called Cyclops Blink that controlled thousands of infected devices around the world.


CyberNews
The US Justice Department disrupted a global botnet of thousands of infected network hardware devices controlled by infamous threat actor Sandworm.
Loading more articles....