

Infosecurity News
#BHUSA: What has Changed in the Post-Stuxnet Era?
Investigative journalist Kim Zetter explains that Stuxnet continues to serves as a precedent for attacks happening now


Infosecurity News
Investigative journalist Kim Zetter explains that Stuxnet continues to serves as a precedent for attacks happening now

SecurityWeek
Researchers have discovered two serious vulnerabilities that can be exploited to launch Stuxnet-style attacks against PLCs from Rockwell Automation.


SecurityWeek
Researchers demonstrate that remote Stuxnet-style attacks are possible against many modern PLCs using web-based malware.


DarkReading
Report says US and Israel spent $1 billion to develop the infamous Stuxnet virus, using a Dutch spy to deploy it and sabotage Iran's nuclear program in 2008.

SecurityWeek
An engineer recruited by intelligence services used a water pump to deliver Stuxnet, which reportedly cost $1-2 billion to develop.

HACKRead
Investigative journalist Huib Modderkolk from Dutch national newspaper De Volkskrant uncovered that 36-year-old Dutch civil engineer Erik van Sabben played a ‘crucial role’ in a 2007 mission supported by the US and Israel. He was instrumental in deploying the advanced Stuxnet virus to sabotage an Iranian nuclear complex.


Security Affairs
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds new vulnerabilities to its Known Exploited Vulnerabilities Catalog, including the bug used in the Stuxnet attacks. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added six new vulnerabilities to its Known Exploited Vulnerabilities Catalog. Below is the list of vulnerabilities added to the catalog: CVE-2022-40139: Trend […]


DarkReading
CISA urges organizations using affected technologies to implement recommended mitigation measures.


Ars Technica
Over 120 PLC models contain a serious vulnerability—and no fix is on the way.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added half a dozen vulnerabilities to its catalog of Known Exploited Vulnerabilities and is ordering federal agencies to follow vendor's instructions to fix them.


ZDNet
The flaws can be exploited to execute code on vulnerable controllers and workstations.


CyberNews
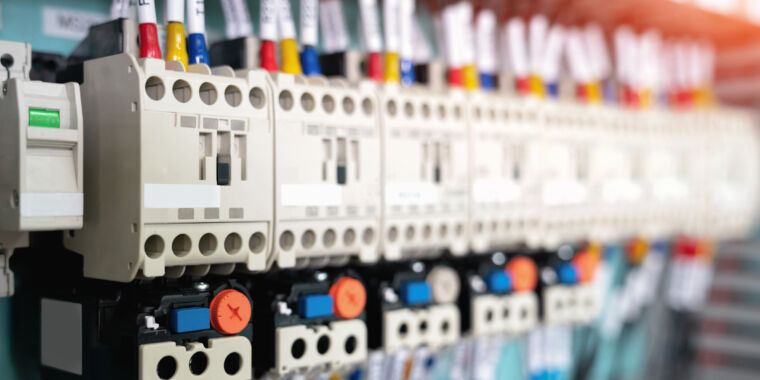
Hackers claim to have permanently damaged some physical devices with the malware Fuxnet, which they describe as “Stuxnet on steroids.”


Security Affairs
State television announced that Iran has foiled massive cyberattacks that targeted public services operated by both government and private organizations. According to the Iran state television, the attack attempts took place in recent days and aimed at the infrastructure of more than 100 public sector agencies. The report did not name entities that were targeted […]


Ars Technica
LitterDrifter's means of self-propagation are simple. So why is it spreading so widely?


DarkReading
The recent discovery of highly customized malware targeting programmable logic controllers has renewed concerns about the vulnerability of critical infrastructure.

SecurityWeek
Iran on April 24th said it thwarted cyberattacks that planned to target the infrastructure of more than 100 public sector agencies.


ThreatPost
DDoS attacks against Israel telecom companies took down government sites, sparking a temporary state of emergency.


The Record
CISA on Thursday released two Industrial Controls Systems Advisories detailing vulnerabilities in Rockwell Automation products that could allow a threat actor to inject malicious code on an affected system.

SecurityWeek
The big difference between the Russia of the USSR and the Russia of today has been the emergence of cyber as an accepted theater of war. It is this role of cyber that SecurityWeek discussed with Marcus Willett.


The Record
As the Cold War drew to a close a surprising contender emerged as the third largest nuclear power on earth: Ukraine. The country was home to some 5,000 nuclear weapons, placed there by Moscow when Ukraine was still part of the Soviet Union. Kyiv sent the weapons back to Russia in exchange for security guarantees […]


Trend Micro
In part two of our oil and gas series, we look at more threats that can expose the industry to cyberattacks.


SecurityWeek
Nearly 70% of Iran’s nearly 33,000 gas stations went out of service in what is a suspected cyberattack


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. LastPass revealed that intruders had internal access for four days during the August hack CISA adds […]


SecurityWeek
Rockwell Automation is concerned about internet-exposed ICS due to heightened geopolitical tensions and adversarial cyber activity globally.

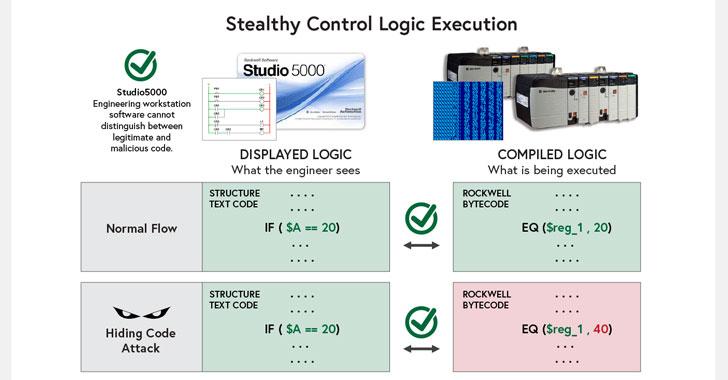
The Hacker News
Critical Bugs in Rockwell Automation PLC Could Allow Hackers to Implant Malicious Code on Affected Systems.


Infosecurity News
Unnamed intelligence officials say President Biden is considering unprecedented action


ThreatPost
Cisco Talos discovered eight vulnerabilities in the Open Automation Software, two of them critical, that pose risk for critical infrastructure networks.


ZDNet
The new tool aims to protect developers against API and token exposure.


SecurityWeek
Critical vulnerabilities in a Delta OT monitoring product can allow hackers to hide their destructive activities from the victim.


Infosecurity News
The research resulted in proof-of-concept exploits against seven market-leading automation firms

CSO
A coalition of U.S. government agencies, security researchers, and companies warn about this new malware that can gain complete access to ICS and SCADA systems.

SecurityWeek
Quantum resiliency firm Qrypt has released a product designed to take asymmetric encryption out of the equation by eliminating the need for traditional key distribution


Ars Technica
Code-signing is supposed to make people safer. In this case, it made them less so.


SecurityWeek
Rockwell Automation ThinManager ThinServer vulnerabilities could allow remote attackers to take control of servers and hack HMIs.


The Cyber Express
A hacktivist collective known as "Predatory Sparrow" (or "Gonjeshke Darande" in Persian) declared on Monday that it had perhaps subverted

SecurityWeek
ICS Patch Tuesday: Siemens and Schneider Electric address dozens of vulnerabilities affecting their industrial products.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


CyberSecurity Dive
The malware initially targeted Schneider Electric and Omron controllers.

SecurityWeek
An exiled Iranian opposition group claimed a hacking attack which it said temporarily took control of dozens of websites run by Tehran's municipality and thousands of the capital's surveillance cameras.


CSO
The OT:ICEFALL report shows that makers of operational technology manufacturers have to improve the security of their devices.


The Hacker News
New industrial malware COSMICENERGY unearthed – targeting electric transmission operations in Europe, Middle East, and Asia.

The Hacker News
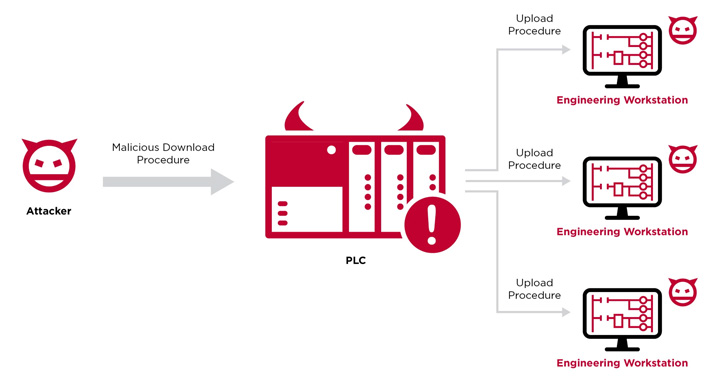
Researchers have developed a novel attack technique that weaponizes PLCs to gain an initial foothold in technical workplaces and penetrate operational

SecurityWeek
Albania has suffered a new cyberattack, the country's interior ministry said on September 10, blaming Iran which Tirana also accused of an earlier assault on its digital systems.


The Record
The number of cybersecurity patent applications has skyrocketed over the past decade, with U.S. companies leading the way.

.webp)
Cyber Security News
Ukrainian hackers have successfully infiltrated and disabled a vast network of industrial sensors and monitoring infrastructure in Russia.


SecurityWeek
Two Rockwell Automation product vulnerabilities have been used for a new exploit by an APT group that could target critical infrastructure.


ZDNet
US government puts energy sector on high alert over specialized malware for disrupting industrial control systems.


SecurityWeek
An analysis conducted by Honeywell shows that much of the USB-borne malware targeting industrial organizations can still cause OT disruption.


DarkReading
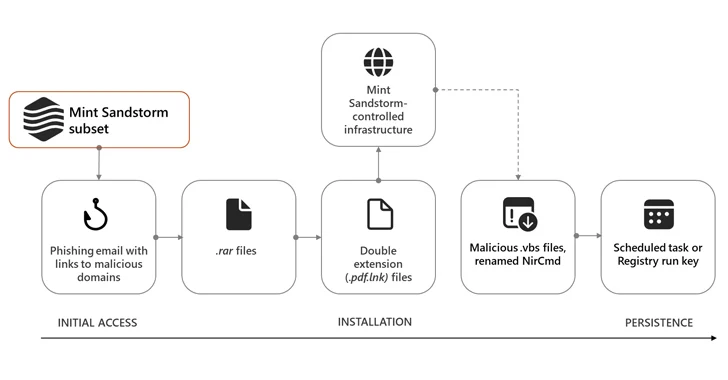
Seedworm, aka MuddyWater, drops PowerShell-based malware on victims using living-off-the-land techniques.


The Hacker News
Rockwell Automation urges customers to disconnect industrial control systems from the public internet due to heightened cyber threats

The Hacker News
"Mind Sandstorm," an Iranian cyber espionage group, has targeted experts in Middle Eastern affairs across several countries.

SecurityWeek
A team of researchers from the Technion research university in Israel is conducting an analysis of Siemens software controllers and they are gradually identifying security issues.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Trend Micro
With geopolitical tensions running high, oil and gas companies may be more susceptible to cyberattacks.

CSO
Researchers demonstrate a proof of concept where hijacked programmable logic controllers can compromise engineering workstations to allow lateral movement.


SecurityWeek
ICS malware Fuxnet allegedly used by Ukrainian hackers to disrupt industrial sensors and other systems belonging to a Russian firm.


ZDNet
Cybersecurity researchers at Ben-Gurion University demonstrate a novel technique that steals data using electromagnetic radiation and a $1 antenna.


Cyber Security News
Researchers discovered four vulnerabilities in CyberPower's PowerPanel Enterprise Data Center Infrastructure Management (DCIM) platform and five vulnerabilities in Dataprobe's iBoot Power Distribution Unit (PDU).


DarkReading
Escalating incursions into military base infrastructure, telecom networks, utilities, and more signal that Beijing is laying the groundwork for mass disruption.


Ars Technica
After decades of watching Kremlin-backed hackers, the FBI ID'd weaknesses and pounced.


Trend Micro
Trend Micro’s Chief Technology Strategy Officer discusses the biggest cybersecurity trends and what to watch for in 2024.


Bleeping Computer
A new attack method named COVID-bit uses electromagnetic waves to transmit data from air-gapped systems isolated from the internet over a distance of at least two meters (6.5 ft), where its captured by a receiver.

DarkReading
Cybercriminals and hacktivists have joined state-backed actors in using sabotage-bent malware in destructive attacks, new report shows.

The Hacker News
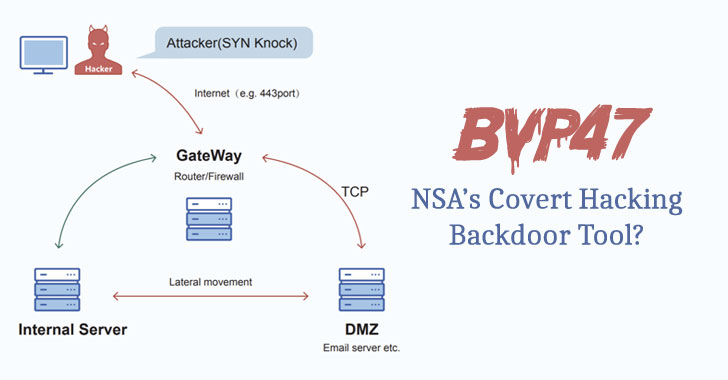
A team of Chinese researchers has revealed details of a "top-tier" backdoor used by the Equation Group, a APT group linked to the NSA.


Bleeping Computer
Microsoft announced a new Windows Protected Print Mode (WPP), introducing significant security enhancements to the Windows print system.


CyberScoop
The code designed to target industrial control systems joins the pantheon of dangerous malware that can cause cyber-physical harm.


The Hacker News
Microsoft highlights the critical need to secure internet-exposed OT devices amidst rising cyber attacks.


Cyber Security News
A malware attack is a cyber-attack using malicious software to gain unauthorized access to a computer system or network.

DarkReading
After the US and its allies formally accused China of irresponsible and malicious behavior in cyberspace back in 2021, the government there has been on a mission to cast the US in the same light.

Bleeping Computer
Researchers at the School of Cyber Security at Korea University, Seoul, have presented a new covert channel attack named CASPER can leak data from air-gapped computers to a nearby smartphone at a rate of 20bits/sec.


Computerworld
State-sponsored attacks similar to NSO Group's Pegasus will begin to leak into the criminal hacker community in 2022, Watchguard warns.

SecurityWeek
Cyber warfare campaigns are being intensely deployed by both sides as Russia's invasion of Ukraine grinds on, though the covert operations have not yet proved decisive on the battlefield.


DarkReading
Initial attacks used damaging wiper malware and targeted infrastructure, but the most enduring impacts will likely be from disinformation, researchers say. At Black Hat USA, SentinelOne's Juan Andres Guerrero-Saade and Tom Hegel will discuss.


The Record
CISA released a warning about several vulnerabilities found in Dataprobe’s iBoot power distribution units allowing for remote exploitation.

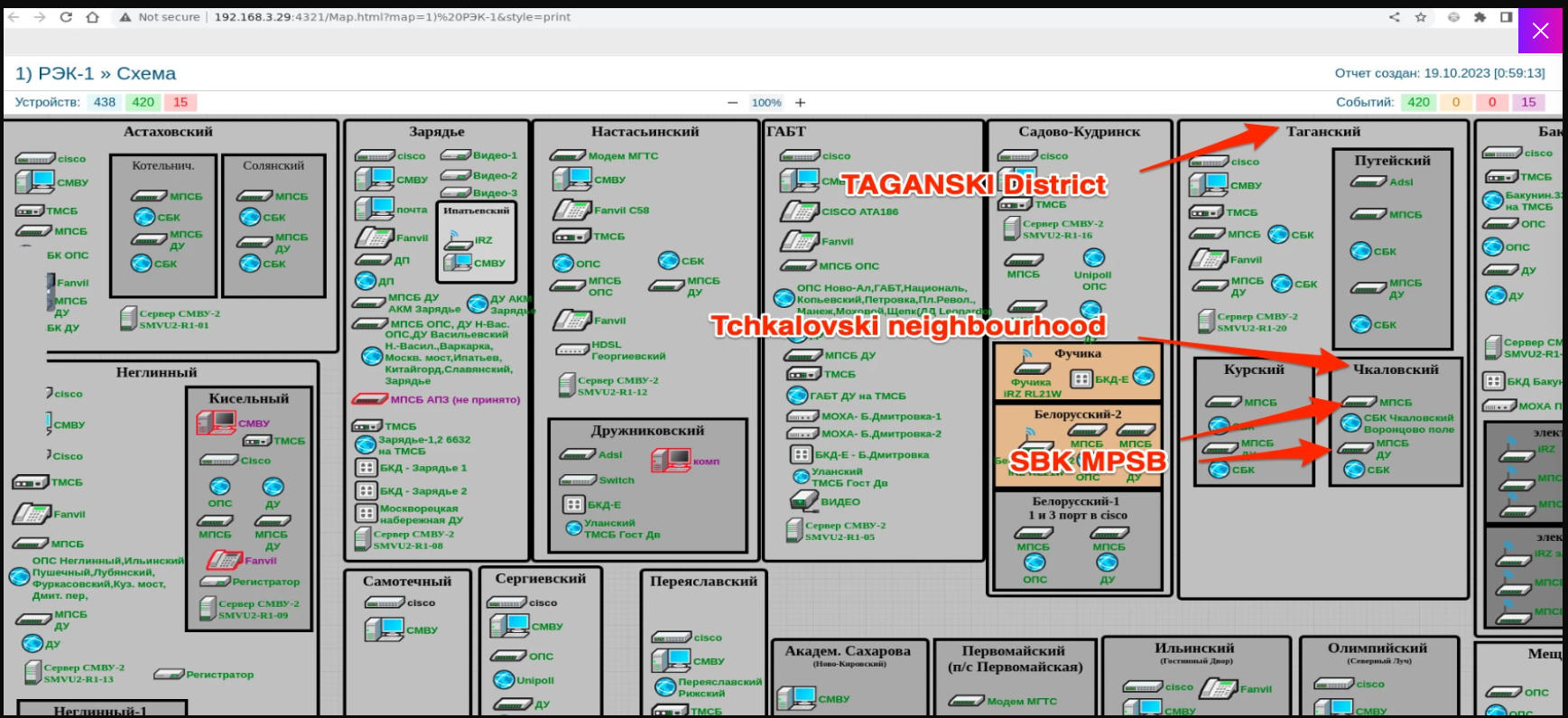
Security Affairs
The Ukrainian hacking group Blackjack used a destructive ICS malware dubbed Fuxnet in attacks against Russian infrastructure.


Bleeping Computer
Microsoft has now confirmed signing a malicious driver being distributed within gaming environments. This driver, called "Netfilter," is in fact a rootkit that was observed communicating with Chinese command-and-control IPs.


Security Affairs
As digital transformation is advancing and automation is becoming an essential component of modern enterprises, collaboration between humans and machines is crucial. With this level of interaction, a new identity problem is emerging as machines operate on behalf of humans. Collaboration between humans and machines is a working reality today. Along with this comes the […]


Bleeping Computer
The Russian state-sponsored hacking group known as Sandworm tried on Friday to take down a large Ukrainian energy provider by disconnecting its electrical substations with a new variant of the Industroyer malware for industrial control systems (ICS) and a new version of the CaddyWiper data destruction malware.


Naked Security
Not just that infamous Twitter hack, but SIM-swapping, stalking and swatting too…


Ars Technica
"Operation Triangulation" stole mic recordings, photos, geolocation, and more.


SecurityWeek
Microsoft PlayReady vulnerabilities that could allow rogue subscribers to illegally download movies from popular streaming services.


The Record
Researchers from Mandiant reported on an October 2022 incident involving Russian nation-state hackers that included multiple rare or previously unseen elements.


ThreatPost
Nate Warfield, CTO at Prevailion, discusses the dangers of focusing on zero-day security vulnerabilities, and how security teams are being distracted from the day-to-day work that prevents most breaches.

Ars Technica
"Pipedream" an extremely versatile malware toolkit for targeting power grids, refineries.


Trend Micro
In this blog series our team examined various ICS vulnerabilities using the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) for ICS.


Trend Micro
Code signing certificates help us assure the file's validity and legitimacy. However, threat actors can use that against us. In this blog, discover how QAKBOT use such tactic and learn ways how to prevent it.

SecurityWeek
If the West were to respond harshly to Russian aggression, Moscow could retaliate against NATO nations in cyberspace with an intensity and on a scale previously unseen


The Hacker News
AI arms race in cybersecurity: From spam filters to spear phishing, AI is both defender and weapon. Learn how Cylance AI is staying ahead of the game,


Bleeping Computer
Recently, FortiGuard Labs released the latest Global Threat Landscape Report for the second half of 2021. There is a ton of data in it and several key takeaways. The main themes that weave through this report are about the increase in cybercriminal sophistication as well as speed.


The Hacker News
Industry under fire: Manufacturing seems to be exceptionally impacted by cyberattacks. Why could that be? Is it the vulnerable machinery?


The Record
The Kremlin-affiliated Sandworm is perhaps Russia's most visible hacker group, with an emphasis on disruptive cyberattacks.

SecurityWeek
Creating a global cyber intelligence organization would likely drive Russia and China closer together – perhaps including Iran and North Korea and Russian and Chinese satellite nations – into their own special relationship.


ThreatPost
The supply-chain attack on the U.S. energy sector targeted thousands of computers at hundreds of organizations, including at least one nuclear power plant.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps.


CSO
Researchers demonstrate how attackers can target PLCs to bypass authentication and perform remote code execution on industrial networks.

The Record
Participants in high-profile wargames "react in very unusual ways to cyber operations," the Hoover Institution's Jacquelyn Schneider tells the Click Here podcast team.


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and