

CSO
North Korean threat actor APT43 pivots back to strategic cyberespionage
The APT43 group is highly adept at using social engineering to target individuals and extract sensitive information.


CSO
The APT43 group is highly adept at using social engineering to target individuals and extract sensitive information.


The Hacker News
APT43, a moderately-sophisticated cyber operator that supports North Korea's regime, engages in financially-motivated cybercrime to fund its operation


Bleeping Computer
A new North Korean hacking group has been revealed to be targeting government organizations, academics, and think tanks in the United States, Europe, Japan, and South Korea for the past five years.


Infosecurity News
Mandiant says unit is focused on espionage and crypto theft


Infosecurity News
The advisory identifies several actors: Kimsuky, Thallium, APT43, Velvet Chollima and Black Banshee


Bleeping Computer
The NSA and FBI warned that the APT43 North Korea-linked hacking group exploits weak email Domain-based Message Authentication Reporting and Conformance (DMARC) policies to mask spearphishing attacks.


DarkReading
In cyberattacks against the US, South Korea, and Japan, the group (aka APT43 or Thallium) is using advanced social engineering and cryptomining tactics that set it apart from other threat actors.


The Hacker News
North Korea's Kimsuky group, a.k.a APT43, wields spear-phishing campaigns and is leveraging social engineering to compromise high-value targets.


Bleeping Computer
State-sponsored North Korean hacker group Kimsuky (a.ka. APT43) has been impersonating journalists and academics for spear-phishing campaigns to collect intelligence from think tanks, research centers, academic institutions, and various media organizations.


SecurityWeek
The US has announced sanctions against North Korean cyberespionage group Kimsuky over its intelligence gathering activities.


The Record
The U.S. partnered with several nations in the Pacific to hand down sanctions on North Korea — particularly the country’s Kimsuky cyber espionage group — after the country launched a surveillance satellite last week.


The Hacker News
North Korean-backed threat actor ARCHIPELAGO targets South Korean & US government, military, and policy experts.


The Hacker News
Korean hacking group Lazarus Group targets defense industry and nuclear engineers with fake job interviews, using trojanized VNC apps to steal data an


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.

Cyber Security News
Google's TAG released defensive measures that followed to protect users from the infamous Noth Korean government-backed APT hackers attacks.

The Hacker News
Did you know about SuperBear? A recent phishing attack in South Korea exposed this dangerous remote access trojan. Read how this remote access trojan


Security Affairs
The US Department of the Treasury’s Office of Foreign Assets Control (OFAC) announced sanctions against North Korea-linked APT group Kimsuky.


Infosecurity News
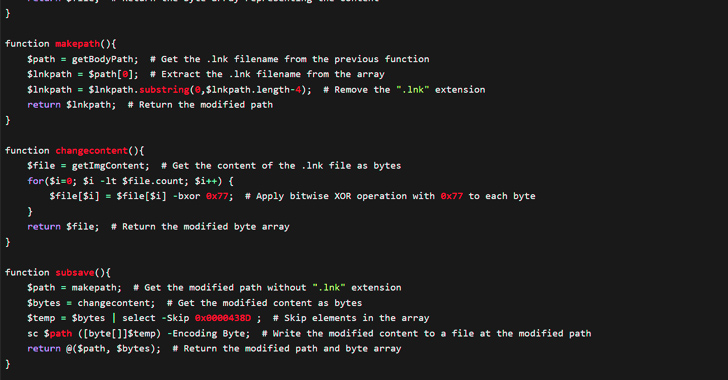
This shift is not exclusive to ROKRAT but represents a larger trend that became popular in 2022


Infosecurity News
Proofpoint confirmed Kimsuky has directly contacted foreign policy experts since 2023 through seemingly benign email conversations


Infosecurity News
SentinelOne said the campaign specifically targets experts in North Korean affairs


Security Affairs
North Korea-linked APT Kimsuky launched a spear-phishing campaign targeting US contractors working at the war simulation centre. North Korea-linked APT group Kimsuky carried out a spear-phishing campaign against US contractors involved in a joint U.S.-South Korea military exercise. The news was reported by the South Korean police on Sunday, the law enforcement also added that […]


The Hacker News
North Korean hackers Kimsuky using new ReconShark reconnaissance tool to target individuals via spear-phishing.

The Hacker News
Threat actor Konni, potentially tied to North Korea, deploys RAT in cyber espionage using Russian Word doc, exploiting WinRAR flaw.


Bleeping Computer
The Treasury Department's Office of Foreign Assets Control (OFAC) has sanctioned the North Korean-backed Kimsuky hacking group for stealing intelligence in support of the country's strategic goals.

The Hacker News
North Korean APT Kimsuky caught using new Golang-based info stealer "Troll Stealer" and malware "GoBear," both signed with stolen certificates.


Bleeping Computer
The X_Trader software supply chain attack that led to last month's 3CX breach has also impacted at least several critical infrastructure organizations in the United States and Europe, according to Symantec's Threat Hunter Team.

Bleeping Computer
A hacking unit of North Korea's Reconnaissance General Bureau (RGB) was linked to the JumpCloud breach after the attackers made an operational security (OPSEC) mistake, inadvertently exposing their real-world IP addresses.


The Hacker News
OFAC sanctions North Korea-linked group Kimsuky and 8 agents for supporting WMD programs.


SC Magazine
The attacks are deploying ToddlerShark, a new variant of a malware strain linked to the threat group.


The Hacker News
New findings reveal that ransomware actors, cryptocurrency scammers, and nation-state hackers are exploiting cloud mining services to launder.


SecurityWeek
The US government warns of a North Korean threat actor abusing weak email DMARC settings to hide spear-phishing attacks.

The Hacker News
U.S. government warns of North Korean hackers sending spoofed emails to gather intelligence.


CSO
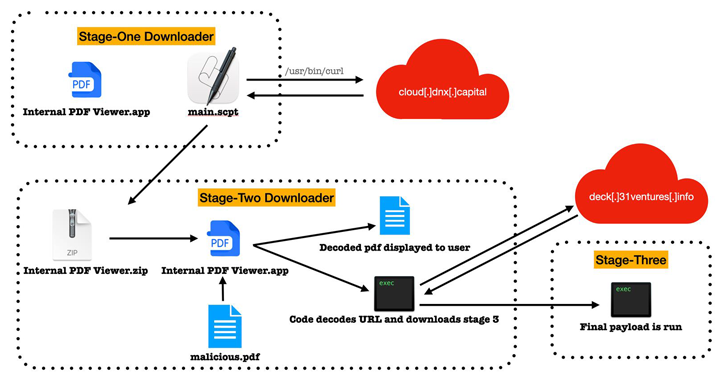
Mandiant research has attributed the hack to UNC4899, a Democratic People’s Republic of Korea (DPRK) threat actor, with a history of targeting companies within the cryptocurrency vertical.


SC Magazine
The state-sponsored group is exploiting weak DMARC policies to impersonate legitimate domains.


Security Affairs
North Korea-linked APT group Kimsuky has been observed using a new reconnaissance tool dubbed ReconShark in a recent campaign. SentinelOne researchers observed an ongoing campaign from North Korea-linked Kimsuky Group that is using a new malware called ReconShark. The reconnaissance tool is delivered through spear-phishing emails, OneDrive links leading to document weaponized downloads, and the execution of malicious […]


DarkReading
Kim Jong Un's Swiss Army knife APT continues to spread its tendrils around the world, showing it's not intimidated by the researchers closing in.


Security Affairs
The Korean National Police Agency (KNPA) warns that a North Korea-linked APT group had breached the Seoul National University Hospital (SNUH). The Korean National Police Agency (KNPA) revealed that a North Korea-linked APT group has breached one of the largest hospitals in the country, the Seoul National University Hospital (SNUH). The security breach took place […]


The Hacker News
State-sponsored North Korean hackers are using a sneaky macOS malware called KANDYKORN to target crypto engineers via Discord.


Bleeping Computer
An investigation into last month's 3CX supply chain attack discovered that it was caused by another supply chain compromise where suspected North Korean attackers breached the site of stock trading automation company Trading Technologies to push trojanized software builds.


Security Affairs
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google’s Threat Analysis Group (TAG) is warning of the North Korea-linked ARCHIPELAGO group that is targeting government and military personnel, think tanks, policy makers, academics, and researchers in South Korea, the US and elsewhere. Google experts are tracking ARCHIPELAGO since […]


Security Affairs
North Korea-linked APT group Kimsuky is posing as journalists to gather intelligence, a joint advisory from NSA and FBI warns. A joint advisory from the FBI, the U.S. Department of State, the National Security Agency (NSA), South Korea’s National Intelligence Service (NIS), National Police Agency (NPA), and the Ministry of Foreign Affairs (MOFA), warns that North-Korea-linked Kimsuky APT […]


The Hacker News
North Korean threat actors known as Diamond Sleet and Onyx Sleet are exploiting a critical security flaw in JetBrains TeamCity to breach servers.


Bleeping Computer
The North Korean Kimsuky hacking group has been observed employing a new version of its reconnaissance malware, now called 'ReconShark,' in a cyberespionage campaign with a global reach.


DarkReading
Kimsuky-attributed campaign uses eight steps to compromise systems — from initial execution to downloading additional code from Dropbox, and executing code to establish stealth and persistence.


The Hacker News
Lazarus Group launched a new global campaign involves exploiting security flaws in Log4j to deploy previously undocumented RAT on compromised hosts.


Security Affairs
North Korea-linked APT Kimsuky has been linked to a social engineering campaign aimed at experts in North Korean affairs. SentinelLabs researchers uncovered a social engineering campaign by the North Korea-linked APT group Kimsuky that is targeting experts in North Korean affairs. The attacks are part of a broader campaign recently detailed in a joint advisory published by […]


DarkReading
An unprecedented collaboration by various APTs within the DPKR makes them harder to track, setting the stage for aggressive, complex cyberattacks that demand strategic response efforts, Mandiant warns.


Security Affairs
Symantec warns of a new Linux backdoor used by the North Korea-linked Kimsuky APT in a recent campaign against organizations in South Korea.

The Hacker News
BlueNoroff, a suspected subgroup of Lazarus Group, is now targeting Apple's macOS with new malware RustBucket, highlighting hackers' expanding toolset


The Hacker News
North Korean state actors linked to the RGB have been identified in the JumpCloud hack! An OPSEC mistake exposed their IP address.