

The Hacker News
4 Cloud Data Security Best Practices All Businesses Should Follow Today
4 Cloud Data Security Best Practices All Businesses Should Follow Today


The Hacker News
4 Cloud Data Security Best Practices All Businesses Should Follow Today


DataBreaches
There was a follow-up last week to a case DataBreaches.net has reported on several times, beginning in December, 2020 when Demetrius Cervantes, 46, of...


ThreatPost
Cyberattackers made off with addresses, insurance information, dates of birth, and most worryingly, clinical information, such as diagnosis, procedures and/or prescription information.


DataBreaches
Bill Toulas of Bleeping Computer reported on a recent Arctic Wolf Labs investigation that caught my eye. Arctic Wolf investigated two cases where victims of...


CyberSecurity Dive
A threat actor that previously intruded Cloudflare’s network through its Okta environment regained access with mistakenly unrotated credentials.


DarkReading
Texas and Maryland this week joined three other states in prohibiting accessing the popular social media app from state-owned devices.


CyberSecurity Dive
Ransomware foists a difficult choice on executives and very few leave business operations in limbo to test a best practice.


DataBreaches
Issued Date: July 20, 2023 Agency/Authority: Homeland Security and Emergency Services, Division of Objective To assess the extent of implementation of the...


CyberNews
After multiple media reports on abusers using smart car services for stalking and harming their victims, the FCC is launching formal proceedings.


ZDNet
Here's a bit of advice that Android users should consider to keep their smartphones and tablets as secure as possible.


DataBreaches
Not all ransomware victims have given up on getting attackers to sign a nondisclosure agreement (NDA), so they can call a ransom payment a “bug...


Ars Technica
Zuckeberg and Altman both tamp down fear and hype with casual statements about AGI.


Cyber Security News
The FBI alerts on rising ransomware trends and urges organizations to follow mitigation recommendations for minimizing ransomware risks and consequences.


CyberNews
Blocking of news links has led to changes in the way Canadian Facebook users engage with info about politics.


DataBreaches
Mint reports: Payments firm One Mobikwik Systems Ltd on Monday, in its draft IPO prospectus, said that a forensic audit conducted by an independent expert...

SecurityWeek
When the Supreme Court last June stripped away constitutional protections for abortion, concerns grew over the use of period tracking apps because they aren’t protected by federal privacy laws.


Infosecurity News
Several suffered follow-on session hijacking attacks


The Record
Several VPN services said they are considering moving operations out of India after ExpressVPN announced this week that it plans to remove servers from the country.


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and


DataBreaches
GVS reports: A hacking group claiming to be Russian-linked cybercriminals has published sensitive data from one of Australia’s largest law firms, HWL...


Bleeping Computer
The National Security Agency (NSA) has shared mitigations and best practices that systems administrators should follow when securing Unified Communications (UC) and Voice and Video over IP (VVoIP) call-processing systems.


Infosecurity News
Victims were targeted by follow-on phishing attacks


Ars Technica
Midnight Blizzard is now using stolen secrets in follow-on attacks against customers.


Ars Technica
Following "lousy first quarter," Upton expects "hundreds of thousands" by Q3.

The Record
A comprehensive data privacy bill that includes the country’s toughest data minimization standards is on the cusp of passing the Maryland state legislature, giving advocates hope that similar bills will follow nationwide.


DataBreaches
EMI Health is committed to protecting the confidentiality and security of our members’ information. Regrettably, we recently identified and addressed a...


The Record
When it comes to privacy and cybersecurity regulations, the EU often sets the standards that other governments follow, and Despina Spanou has played a key role.


Infosecurity News
Tech giants also follow Meta in cracking down on Kremlin propaganda


DataBreaches
Wassayos Ngamkham has some interesting follow-up reporting on the recent attack on Phetchabun Hospital. That hospital and Bhumirajanagarindra Kidney...


The Hacker News
Ransomware attacks on VMware ESXi follow a similar pattern, exploiting misconfigurations and vulnerabilities.


DataBreaches
Anthony Mirenda, Stephen Garvey, and Natalie Panariello of Foley Hoag write: As we anticipated last spring, the Department of Justice (DOJ) has signaled that...


DataBreaches
DataBreaches.net has continued to follow up on the ransomware attack on Missouri Delta Medical Center claimed by Hive threat actors. This site broke the story...

DarkReading
The company hasn't acknowledged responsibility for the incident, although allowing scraping paves the way for dangerous follow-on attacks.


DataBreaches
To follow up on two previously reported breaches involving protected health information, here are two class action settlements that involve business...


DarkReading
Sites spoofing Grammarly and a Cisco webpage are spreading the DarkTortilla threat, which is filled with follow-on malware attacks.


The Record
In the wake of an escalating crisis between Ukraine and Russia, Serhii Demediuk agreed to a follow-up interview in which he discussed issues including the recent defacement of Ukrainian websites, the security of the country’s critical infrastructure, and Russia’s motivations.


DataBreaches
Zhao Yifan reports a follow-up to an incident previously noted on this site. Ecommerce Enablers, which operates the online shopping service platform ShopBack,...

DarkReading
Deployed by the infamous SmokeLoader botnet, the location-tracking malware could be used for a host of follow-on cyberattacks or even physical targeting.


DarkReading
A new threat actor just concluded a month and a half of two major leaks per day. Now comes phase two: follow-on attacks.


DataBreaches
There’s a follow-up to the Tulsa ransomware incident previously reported on this site in May and June. AP is reporting that continued investigation by...


DataBreaches
Lorenzo Franceschi-Bicchierai reports on yet another incident in which responsible disclosure by a researcher and follow-up by media failed to get a company to...


DataBreaches
This is a follow-up to an incident first reported on this site back in May. Jeremy Rogalski reports: HOUSTON — A local health care provider attacked by a...


Infosecurity News
Check Point study urges developers to follow best practices


CyberScoop
The pledges by NATO and G-7 nations follow the Biden administration saying that Russia's calculus on digital assaults had changed.


DataBreaches
Rochelle Alleyne reports a follow up to a breach not previously noted on this site: Hacked. That was the headline back in April when it came to the 20th...


DataBreaches
Brian Krebs reports on a follow-up to the case of Missouri’s Governor Parsons tried to sue a journalist and others who had responsibly disclosed and...


Bleeping Computer
Security researchers are working on compiling an easy to follow list of initial access attack vectors ransomware gangs and their affiliates are using to breach victims' networks.


SecurityWeek
AT&T on March 30 said that data on 73 million customers was exposed on the dark web, including social security numbers.


CSO
The advisory highlights how developers can follow best practices to fix these vulnerabilities during production.


The Hacker News
Experts Shed Light on BlackGuard Infostealer Malware Sold on Russian Hacking Forums


Bleeping Computer
Twitter accounts giving Elon Musk a follow are being targeted in a crypto giveaway scam dubbed 'Freedom Giveaway.'


Bleeping Computer
Twitter accounts giving Elon Musk a follow are being targeted in a crypto giveaway scam dubbed 'Freedom Giveaway.'


ThreatPost
The resurgent trojan has targeted 60 top companies to harvest credentials for a wide range of applications, with an eye to virulent follow-on attacks.


DataBreaches
I am so glad to see a follow-up on this case because I had the same questions about how and why Walgreens did not suffer the same federal penalties as CVS and...


DataBreaches
HC3 has issued an alert about Lorenz ransomware. Lorenz threat actors have been mentioned on DataBreaches’ site several times since 2021. In one case...


Naked Security
20 years to turn it on, then 20 weeks to turn it off, then just 2 weeks to turn it back on again. That’s progress!


DataBreaches
Norton Healthcare has six hospitals in Kentucky and one in Indiana. Since May 9, they have been working on recovering from a cyberattack. They don’t call...

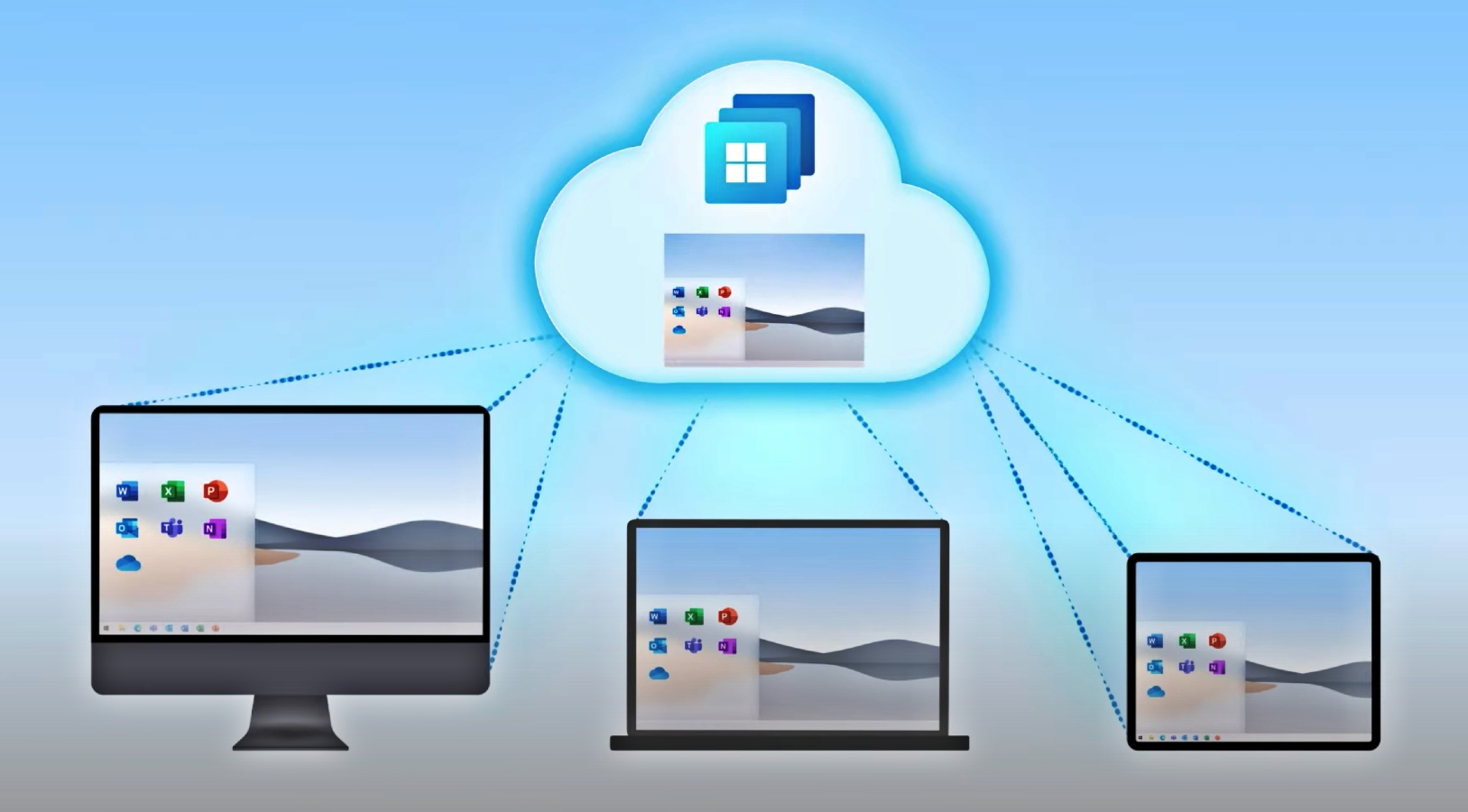
Bleeping Computer
Microsoft has shared guidance on securing Windows 365 Cloud PCs and more info on their built-in security capabilities.

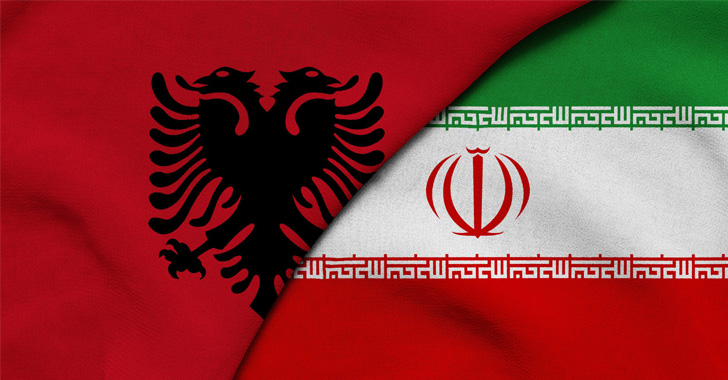
The Hacker News
The U.S. Treasury Department has imposed new sanctions on Iran for engaging in cyberattack activities against the Albanian government.


CyberScoop
The meeting will follow an Aug. 4 briefing with railroad executives to discuss industry responses to critical infrastructure cybersecurity.


The Cyber Express
NoName ransomware group has allegedly targeted multiple Ukrainian government websites. The latest victims of the alleged NoName ransomware attack on


The Cyber Express
The Mogilevich ransomware group has claimed responsibility for a cyberattack on Bazaarvoice, a leading platform connecting brands and retailers with


Ars Technica
Screens said to ship in Apple Watch first, with iPhone and others to follow.


CyberNews
The ransomware group Stormous has claimed responsibility for the cyberattack on Duvel Moortgat brewery on Wednesday.


The Cyber Wire
Solution Spotlight: Simone Petrella sits down with Kristie Grinnell from DXC Technology to discuss their All in on Cyber program.


The Hacker News
Don't let cybercriminals steal your holiday cheer – follow these simple steps to protect yourself and your personal information while shopping online.


DataBreaches
Marco A. De Felice prefaces his reporting on a Ragnar_Locker attack with this message: For ethical reasons we did not want to spread the news of the attack on...


DarkReading
The strategy document does nothing to change things on the ground in the near term; legislation, regulation, and follow-up executive action are all going to be key to moving forward the administration's agenda.


ZDNet
Setting up a VPN on your router can protect the computers and devices on your network. Here's how to pull this off.


CSO
The platform analyzes XIoT firmware using large language model capabilities to follow compromised or vulnerable assets back to their source.

Bleeping Computer
Join over nine million people on Brilliant, and discover a better way to learn. One subscription will unlock the benefits on all your devices. Be one of the first 200 students to get started today and enjoy 20% off a year of Brilliant Premium.


DataBreaches
The City of Grass Valley has a notice on YubaNet that begins: On June 29, 2021 the City of Grass Valley discovered an unknown source had made unauthorized...


DataBreaches
On July 9, the Royatonic spa in France suffered a ransomware attack. A notice on their web site informs people that as of July 12, the spa had to close...


DataBreaches
Kathleen Magramo reports: Hong Kong’s electoral office has apologised after an employee failed to follow guidelines and sent the personal details of about...


Bleeping Computer
IT service desks have become a popular target over the past year in social engineering attacks. Learn more from Specops Software on the best practices orgs should follow to secure their help desks.


ZDNet
EFF urges Apple to follow Google and give smartphone users the option to dodge 2G.


The Cyber Express
Anonymous Arabia, a notorious group of hacktivists, has allegedly launched a cyberattack on Columbia University in response to the recent


DataBreaches
Jessica Davis has the somewhat predictable follow-up to a recently reported breach involving Insight Global, a contact tracing vendor for the Pennsylvania...

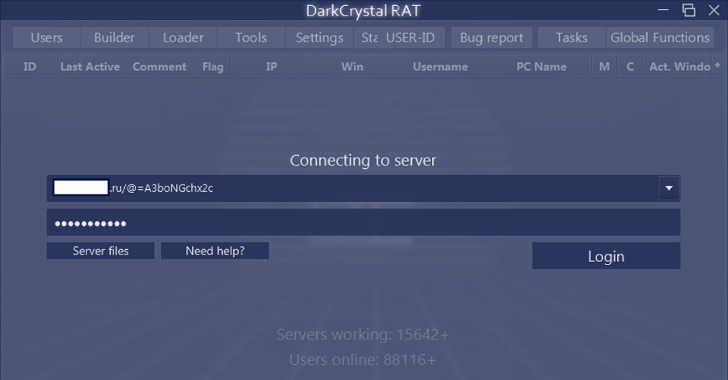
The Hacker News
Cybersecurity researchers have shed light on an actively maintained remote access trojan called DCRat ( aka DarkCrystal RAT).


The Cyber Wire
Solution Spotlight: Simone Petrella sits down with Kristie Grinnell from DXC Technology to discuss their All in on Cyber program.


Bleeping Computer
UK's National Cyber Security Center (NCSC) has published new guidance for organizations to follow when communicating with customers via SMS or phone calls.


Infosecurity News
These new sanctions follow a first wave in February 2023, where seven Russians involved with Trickbot and Conti were also sanctioned


Ars Technica
The convenience of QR codes is a double-edged sword. Follow these tips to stay safe.


CyberNews
Apple has released a new security feature called Stolen Device Protection – and you should definitely turn it on, experts say.


Infosecurity News
Ransomware gang claims responsibility for attack on Partnership HealthPlan


Computerworld
While most computer users focus on desktop and mobile device patches, it’s important to make sure browsers are kept up to date as well.

SecurityWeek
A discussion on the state of cybersecurity investments, venture capital strategies in a confusing economic climate, predictions on hot and not-so-hot product categories, and what happens with all those cybersecurity unicorns.


CyberNews
Meta has announced changes in how it shares political content by excluding it from Reels and Explore on Instagram and not recommending it on Threads.


Naked Security
Reddit is suggesting three tips as a follow-up to this breach. We agree with two of them but not with the third…


Infosecurity News
The ransomware gang made the announcement on its leak site


DataBreaches
Jonathan Greig reports: Nearly half a million people had their sensitive financial information leaked during a cyberattack on NCB Management Services – a...


Security Affairs
Threat actors compromised WordPress sites to deploy a script that was used to launch DDoS attacks, when they are visited, on Ukrainian websites. MalwareHunterTeam researchers discovered the malicious script on a compromised WordPress site, when the users were visiting the website the script launched a DDoS attack against ten Ukrainian sites. The JavaScript was designed […]

The Hacker News
As the mobile threat landscape evolves in 2022, new and existing banking trojans are increasingly targeting Android devices to perform on-device fraud


Security Affairs
The FBI warned US organizations and individuals are being increasingly targeted in BECattacks on virtual meeting platforms The Federal Bureau of Investigation (FBI) warned this week that US organizations and individuals are being increasingly targeted in BEC (business email compromise) attacks on virtual meeting platforms. Business Email Compromise/Email Account Compromise (BEC/EAC) is a sophisticated scam that […]


DataBreaches
It’s Password Day, and this is as good a time as any to mention that Britton White and I have been collaborating on some research expanding on his...


Trend Micro
Every year, experts weigh in with predictions of what the big cybersecurity trends will be—but how often are they right? That’s the question Trend Micro’s Greg Young and Bill Malik asked recently on their Real Cybersecurity podcast, looking at what forecasters got wrong on a wide range of topics, from AI to human factors.


Security Affairs
Experts discovered a malicious package on the Python Package Index (PyPI) that uses steganographic to hide malware within image files. CheckPoint researchers discovered a malicious package, named ‘apicolor,’ on the Python Package Index (PyPI) that uses steganographic to hide malware within image files. The malicious package infects PyPI users through open-source projects on Github. The […]

DarkReading
Swiss intelligence warns that Russia ramping up cyberattacks on infrastructure and cyber espionage as on-the-ground options evaporate.


CSO
Black Hat speaker proposes framework to reduce the negative consequences of risky user actions and encourage them to follow security's advice.

SecurityWeek
NATO condemned a cyberattack on Albania that Tirana and Washington blamed on Iran, and pledged to bolster the alliance member's defenses against hackers.
Loading more articles....