

DataBreaches
Double Extortion Ransomware Victims Soar 935%
Phil Muncaster reports: Researchers have recorded a 935% year-on-year increase in double extortion attacks, with data from over 2300 companies posted onto...


DataBreaches
Phil Muncaster reports: Researchers have recorded a 935% year-on-year increase in double extortion attacks, with data from over 2300 companies posted onto...


The Hacker News
Play ransomware, impacting 300 entities worldwide, employs a double-extortion model by exfiltrating data before encryption.


The Cyber Express
The Hunters ransomware group has claimed to have launched a cyberattack on Double Eagle Energy Holdings IV, LLC, a prominent


The Hacker News
OpenSSH releases update to fix multiple security bugs, including a pre-authentication double free vulnerability (CVE-2023-25136). Upgrade now!


Bleeping Computer
A threat actor uses an unusual attachment to bypass security software that is a double-edged sword that may work against them.


Bleeping Computer
A 8Base ransomware gang is targeting organizations worldwide in double-extortion attacks, with a steady stream of new victims since the beginning of June.


The Hacker News
U.S. agencies warn of Rhysida ransomware double extortion attacks on multiple industries, including education, manufacturing and IT.


CyberNews
India’s data center industry capacity is expected to double in the next three years from around 0.9 Gigawatts (GW) in 2023 to nearly 2GW in 2026.


Bleeping Computer
Security analysts from NCC Group report that ransomware attacks in November 2021 increased over the past month, with double-extortion continuing to be a powerful tool in threat actors' arsenal.


Naked Security
It’s a bug fix for a bug fix. A memory leak was turned into a double-free that has now been turned into correct code…


Naked Security
Double-play 0-day in Exchange – what you need to know, and what you can do


Cyber Security News
The key takeaway of these data breaches is that most of these attacks happened due to human error or inadequate knowledge about phishing and malware campaigns


The Hacker News
Dragon Breath APT group using double-clean-app technique to sideload malicious DLLs and target the online gaming and gambling industries.


Naked Security
Double 0-day exploits – one in WebKit (to break in) and the other in the kernel (to take over). Patch now!


Naked Security
Linux doesn’t BSoD. It has oopses and panics instead. (We show you how to make a kernel module to explore further.)


DataBreaches
JAKKS Pacific, Inc. describes itself as leading designer, manufacturer and marketer of toys and consumer products sold throughout the world. The firm is...


ThreatPost
Startling triple-digit growth is fueled by easy criminal access to corporate networks and RaaS tools, an analysis found.


Infosecurity News
Threat actors combine techniques to trick users


Security Affairs
The maintainers of OpenSSH address multiple security issues, including a memory safety bug in the OpenSSH server (sshd). The maintainers of OpenSSH have addressed a number of security vulnerabilities with the release of version 9.2. One of the issues addressed by the maintainers is a memory safety bug in the OpenSSH server (sshd) tracked as […]


Naked Security
That was quick! 48 hours from exploit report to published patch.

Ars Technica
Google admits that Bard isn't always accurate; ropes in Gmail through new Extensions.


DarkReading
As companies increasingly adopt MFA (even as companies like Twitter disable it), cybercriminals are developing a variety of strategies to steal credentials and gain access to high-value accounts anyway.


Infosecurity News
Business email compromise overtakes ransomware


Bleeping Computer
This week, threat actors hijacked Bitcoin.org, the authentic website of the Bitcoin project, and altered parts of the website to push a cryptocurrency giveaway scam that unfortunately some users fell for. Although the hack lasted for less than a day, hackers seem to have walked away with a little over $17,000.


Bleeping Computer
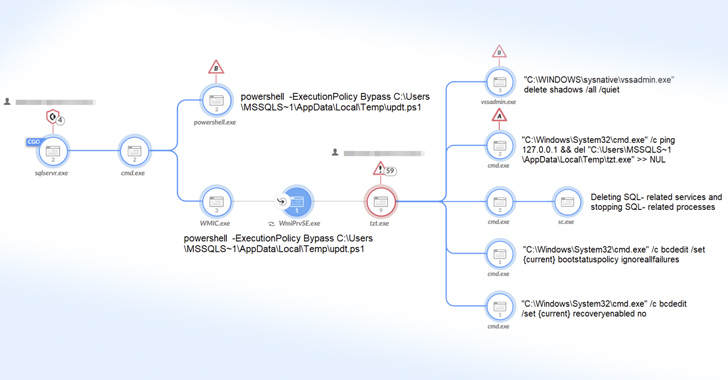
An APT hacking group known as "Dragon Breath," "Golden Eye Dog," or "APT-Q-27" is demonstrating a new trend of using several complex variations of the classic DLL sideloading technique to evade detection.


Infosecurity News
Region also experiences most DDoS events


DataBreaches
Bill Toulas reports: A BlackByte ransomware affiliate is using a new custom data stealing tool called ‘ExByte’ to steal data from compromised...


Security Affairs
An APT group tracked as Dragon Breath has been observed employing a new DLL sideloading technique. Sophos researchers observed an APT group, tracked as Dragon Breath (aka APT-Q-27 and Golden Eye), that is using a new DLL sideloading technique that adds complexity and layers to the execution of the classic DLL sideloading. The attack consists of a clean […]


Infosecurity News
Surge in threats coming from eastern Europe


Infosecurity News
Netacea warns of growing threat from malicious automation


The Record
Air Force Lt. Gen. Timothy Haugh was already subject to a long-running blockade of nominations in the Senate. Now Sen. Ron Wyden is holding it up as leverage to get more information about the NSA's potential connections with the data broker industry.


Bleeping Computer
Microsoft says BulletProofLink, a large-scale phishing-as-a-service operation it spotted while investigating recent phishing attacks, is the driving force behind many phishing campaigns that have targeted many corporate organizations lately.


DataBreaches
Joseph J. Lazzarotti of JacksonLewis writes: The healthcare sector is a prime target for data breaches. According to a summary by the HIPAA Journal, 32% of...


CyberSecurity Dive
The move is designed to boost digital security by allowing users to quickly authenticate across multiple devices and platforms.


Bleeping Computer
Password security, like threat actor methods, continues to evolve. As computing power grows, previously best-practice passwords become increasingly vulnerable. Password managers have done their best to stay up-to-date, offering increased encryption security and better password recommendations.


The Hacker News
Major cybercrime groups are under attack by police. But are these takedowns effective? Some groups vanish, others bounce back in DAYS.


DataBreaches
Michael Novinson reports: Household cleaning product giant Clorox said Wednesday that an August cyberattack had taken a big swipe out of the bleach...


DataBreaches
Brian Krebs reports: In late March 2023, 3CX disclosed that its desktop applications for both Windows and macOS were compromised with malicious code that...


The Cyber Express
Banco Promerica is currently facing a possible cybersecurity dilemma following recent revelations of a data breach and cyberattack. Initially highlighted

Bleeping Computer
A new ransomware group named 'RA Group' is targeting pharmaceutical, insurance, wealth management, and manufacturing firms in the United States and South Korea.

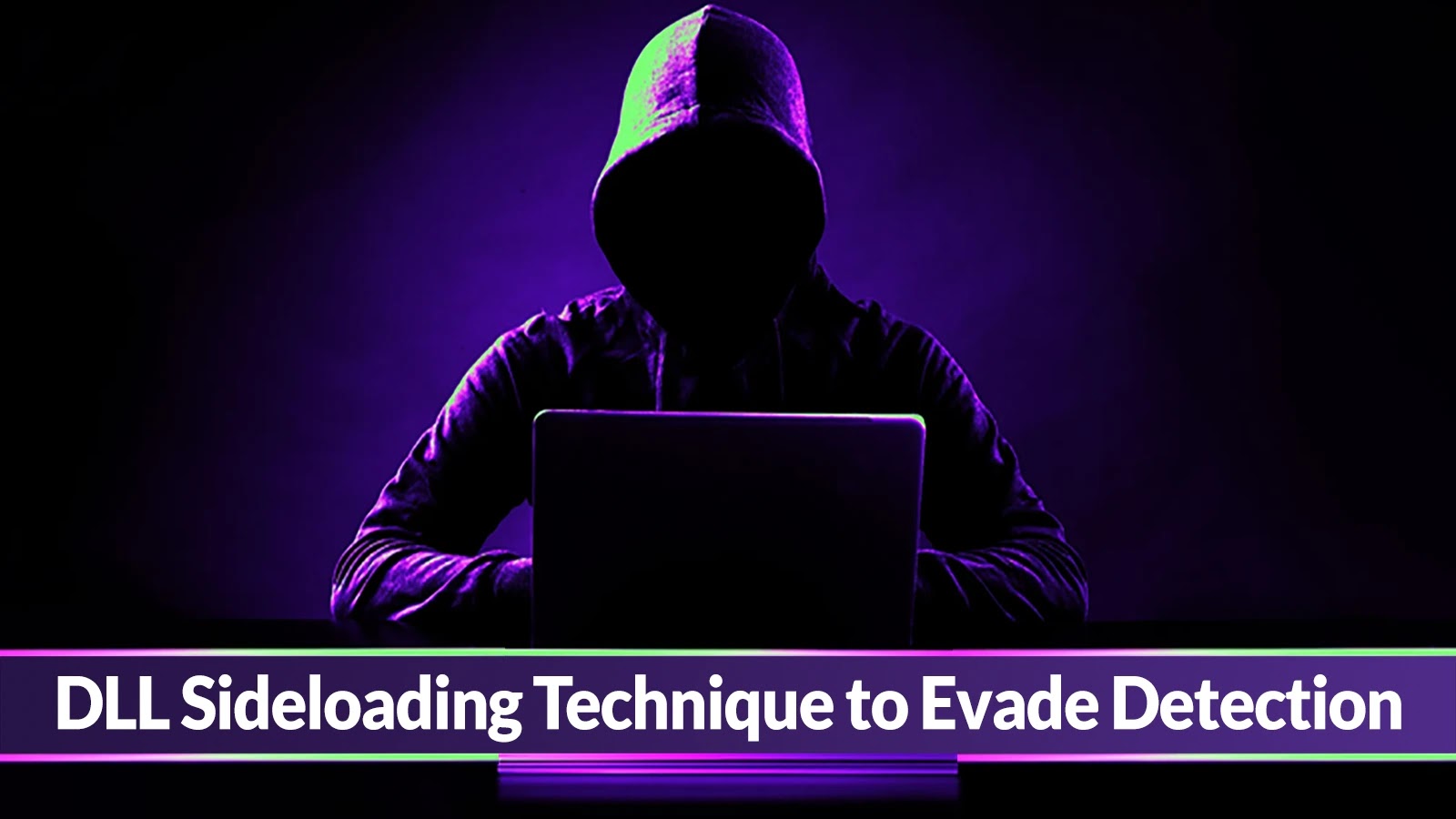
Cyber Security News
Researchers at Sophos detected the "Dragon Breath" APT group using complex DLL sideloading variations to avoid detection.


Infosecurity News
Most phishing attack vectors observed involved clicking a direct link to a phishing page


CSO
Some of the biggest challenges faced in securing industrial control systems involve integrating legacy and aging operational technology with modern IT systems.


CyberNews
With blockchain protocols taking a pounding from threat actors, state-backed currencies may be the best solution, says analyst.

SecurityWeek
The $26 million Series B brings the total raised by Pangea to $51 million and underscores a push by venture capital investors to bet on companies in the API security category.


Infosecurity News
A rising volume of calls to the Scottish Cyber and Fraud Centre highlights surging threat levels


DataBreaches
Phil Muncaster reports: Estee Lauder has become the latest big name to suffer an apparently serious ransomware breach, after two groups claimed to have...


Infosecurity News
Annual Verizon report reveals humans are still a major source of risk


The Cyber Express
The fusion of Artificial Intelligence (AI) and cybersecurity has ushered in a new era of warfare, one conducted not on


Naked Security
Wouldn’t it be handy if there were a single version number to check for in every Chromium-based browser, on every supported platform?


DarkReading
North Korean state-sponsored actors, who help economically prop up Kim Jong Un's dictatorship, continue to pummel US infrastructure.


DarkReading
Hackers are increasingly tantalized by the troves of sensitive data held by lightly protected law firms and legal services organizations.


The Cyber Express
The BlackSuit ransomware group has struck again, adding two new victims to its ever-growing list of targets. This time, the


ZDNet
The antivirus vendor's revenues, profits, and even bookings all exceeded 10% year-over-year growth as it barrels toward an early closure of its Avast merger.


CyberNews
UnitedHealth Group has confirmed that cyberattackers compromised a massive trove of sensitive data from its tech branch Change Healthcare.


Infosecurity News
Even those with policies may see coverage greatly reduced


The Cyber Express
Within a mere two-day period, two major companies have allegedly fallen victim to cyberattacks. The first incident came to light


Infosecurity News
It tried to trick victims into clicking on malicious files as part of a fake Amazon job assessment


Infosecurity News
Double extortion now the norm, says Group-IB


Cyber Security News
The email campaign impersonates the Facebook Ads Team to trick users into clicking a malicious link, as the email leverages social


The Record
Phishing attacks leveraging FIFA and targeting people living in Middle Eastern countries have grown 100% in the last month as the World Cup approaches.


SC Magazine
Hackers gained initial access to the civilian agency two months after a mandatory deadline to patch the vulnerability had expired.


Bleeping Computer
A WinRar zero-day vulnerability tracked as CVE-2023-38831 was actively exploited to install malware when clicking on harmless files in an archive, allowing the hackers to breach online cryptocurrency trading accounts.


ZDNet
Phishing campaigns use fake social media profiles, in-depth research, and more to trick unsuspecting victims into clicking malicious links.


Cyber Security News
Phishing is a common cyberattack technique that involves tricking users into clicking on malicious links, downloading malicious attachments, or entering sensitive information on fake websites.


ZDNet
Attackers now 'double dip' to clear out victim bank accounts.


SC Magazine
A flaw in Microsoft’s uAMQP C library for developers can lead to a “double free” memory error.


SecurityWeek
US and Australian government agencies warn organizations of the Play ransomware group’s double-extortion tactics.


DataBreaches
On July 15, New York State Comptroller Thomas P. DiNapoli released the following school district audits. Clicking on the links will take you to the fuller...


Infosecurity News
Kaspersky said the figures are more than double what the team observed in 2021


Bleeping Computer
Microsoft will soon add a new way to end unresponsive processes in Windows 11 in the form of a new option that will show up when right-clicking an app's taskbar icon.

The Hacker News
Mallox ransomware surges 174% in 2023, employing double extortion tactics by stealing data before encryption.


Bleeping Computer
Microsoft is now promoting some of its products in the sign-out flyout menu that shows up when clicking the user icon in the Windows 11 start menu.

Bleeping Computer
The Donut (D0nut) extortion group has been confirmed to deploy ransomware in double-extortion attacks on the enterprise.

DarkReading
Ransomware cybercrime gangs GhostSec and Stormous have teamed up in widespread double-extortion attacks.


DarkReading
The newly emerged ransomware actively targets both Windows and Linux systems with a double-extortion approach.


The Record
Researchers at Akamai examined how much internet traffic actually arises from people clicking on links in fake U.S. Postal Service texts.


SecurityWeek
Radiant Security gets $15 million in new financing as investors double down on early stage companies experimenting with AI technology.


Bleeping Computer
Microsoft found and reported a high severity flaw in the TikTok Android app in February that allowed attackers to "quickly and quietly" take over accounts with one click by tricking targets into clicking a specially crafted malicious link.


ZDNet
A new China-based double extortion ransomware has started exploiting the Log4Shell bug in VMware server products.


DarkReading
A threat you've never heard of is using double extortion attacks on mom-and-pop shops around the globe.


Bleeping Computer
The Akira ransomware operation uses a Linux encryptor to encrypt VMware ESXi virtual machines in double-extortion attacks against companies worldwide.

Bleeping Computer
In future versions of Windows 10, Microsoft has removed the venerable 'Administrative Tools' and added a new 'Windows Tools' control panel with almost double the number of tools promoted within it.


DarkReading
A new version of the double-extortion group's malware reflects a growing trend among ransomware actors to expand cybercrime opportunities beyond Windows.


Infosecurity News
Mastercard said it is using generative AI-based predictive technology to double the speed at which it can detect potentially compromised cards


DataBreaches
Ever since ransomware attacks and “double extortion” attacks became common, law enforcement has urged victims not to pay ransom demands. Paying...


Cyber Security News
The ransomware group uses the double extortion method of encrypting and exfiltrating data from a victim in order to extort money.


DarkReading
The ransomware gang has been seen exploiting a Mitel RCE flaw discovered in VoIP devices in April (and patched in July) to perform double-extortion attacks.


CyberSecurity Dive
The Hive group practices double extortion — demanding payment to free data it has encrypted while also threatening to release the unencrypted data publicly.

DarkReading
In a notable shift in strategy, the threat actors are abusing code-signing certificates to spread a double whammy of infostealers and ransomware payloads.


Bleeping Computer
Atlassian says that this month's two-week-long cloud outage has impacted almost double the number of customers it initially estimated after learning of the incident.


ZDNet
Researchers say that double-extortion ransomware attacks represent a severe risk to operational processes.


Bleeping Computer
It's a new year, and with it comes a new ransomware to keep an eye on called 'Night Sky' that targets corporate networks and steals data in double-extortion attacks.


Bleeping Computer
An international law enforcement operation has seized the servers, data, and customer logs for DoubleVPN, a double-encryption service commonly used by threat actors to evade detection while performing malicious activities.


CSO
Double-barreled API- and agent-based scanning is now available from cloud security company Uptycs.


The Cyber Express
Within the intricate landscape of cybersecurity, the year 2023 unfolds as a double-edged sword, where the interplay of innovation and


Cyber Security News
In a startling revelation, cyberattacks have surged to more than double their pre-pandemic levels, casting a long shadow over global financial stability.


The Hacker News
Over 17,000 WordPress sites hit by Balada Injector malware in Sept 2023, double the August numbers


Ars Technica
The convenience of QR codes is a double-edged sword. Follow these tips to stay safe.


Naked Security
Firefox just published a double-zero-day patch – “remote code execution” combined with “sandbox escape”. Update now!
Loading more articles....