

The Hacker News
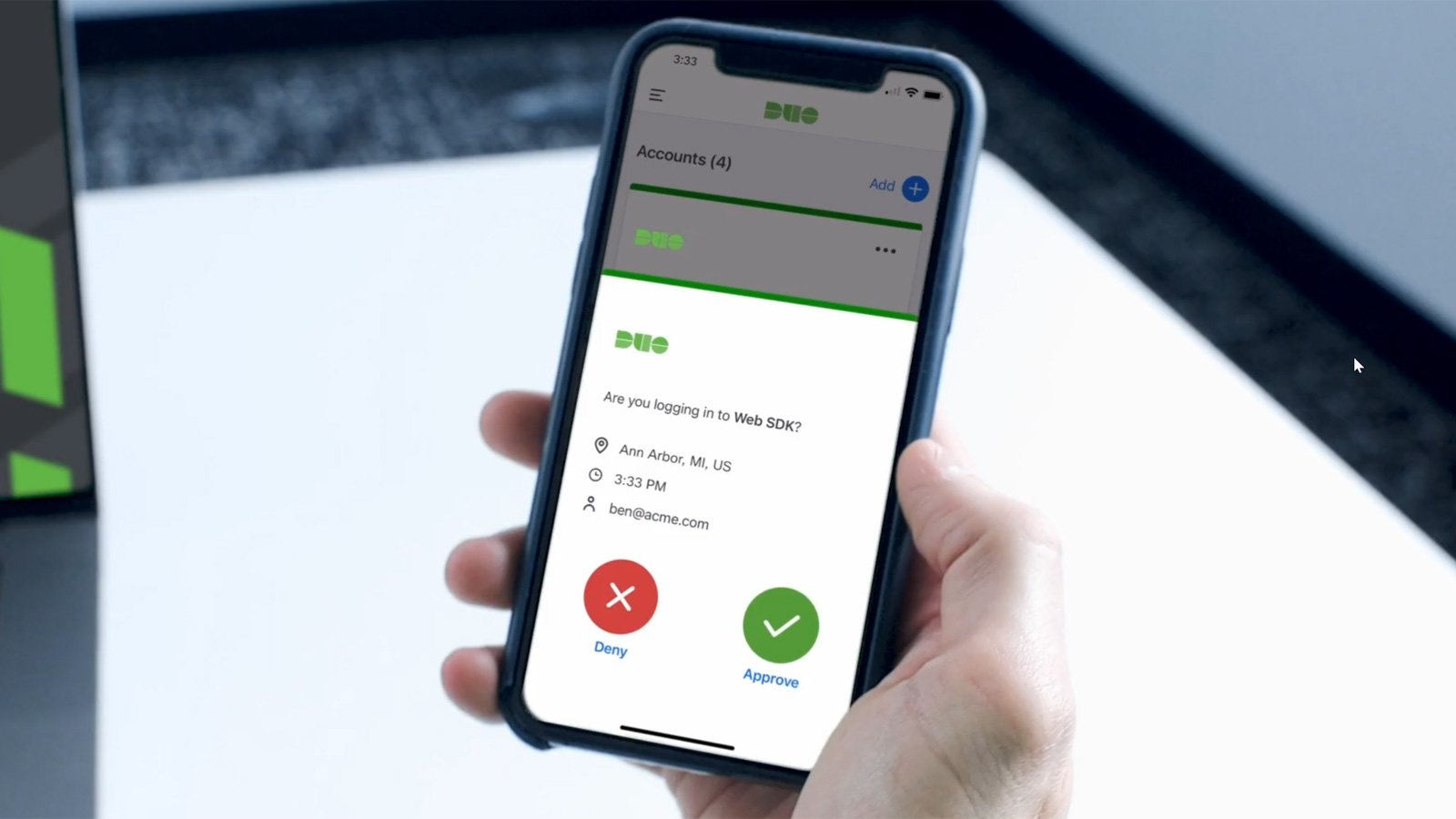
MFA Spamming and Fatigue: When Security Measures Go Wrong
MFA spamming attacks! Hackers are now targeting users with overwhelming MFA prompts, risking security.


The Hacker News
MFA spamming attacks! Hackers are now targeting users with overwhelming MFA prompts, risking security.


Infosecurity News
The package manager started enforcing MFA on owners of gems with over 180 million total downloads


The Hacker News
Understand how hackers exploit social engineering to circumvent MFA and fortify your cybersecurity defenses accordingly.


CyberSecurity Dive
The cloud giant will start requiring users with the highest level of privileges to use MFA starting in mid-2024. Google, in response, said it will mandate MFA for certain accounts this year.

SecurityWeek
Recent high-profile cyberattacks have demonstrated the effectiveness of an interesting method for getting past MFA.


DarkReading
As companies increasingly adopt MFA (even as companies like Twitter disable it), cybercriminals are developing a variety of strategies to steal credentials and gain access to high-value accounts anyway.


Bleeping Computer
Microsoft will soon fast-track multi-factor authentication (MFA) adoption for its Microsoft 365 cloud productivity platform by adding MFA capabilities to the Outlook email client.


CyberNews
Administrators using Azure, the Microsoft cloud computing platform, will have to set up multi-factor authentication (MFA) with no exceptions.

Bleeping Computer
A common threat targeting businesses is MFA fatigue attacks—a technique where a cybercriminal attempts to gain access to a corporate network by bombarding a user with MFA prompts. This article includes some measures you can implement to prevent these types of attacks.


CSO
Despite heavy adoption, MFA was found to have lighter organization-wide deployments, which can lead to credential compromises, rendering the partial adoption counterproductive.


Bleeping Computer
Microsoft has started enforcing number matching in Microsoft Authenticator push notifications to fend off multi-factor authentication (MFA) fatigue attacks.

Bleeping Computer
The FBI says Russian state-backed hackers gained access to a non-governmental organization (NGO) cloud after enrolling their own device in the organization's Duo MFA following the exploitation of misconfigured default multifactor authentication (MFA) protocols.


CyberNews
Apple users are being targeted by MFA bombing attacks, also known as push notification spam. Bad actors might be exploiting a bug in Apple’s password reset feature.


CyberNews
Cisco Duo has warned customers that a threat actor gained access to its vendor systems and obtained a set of MFA SMS logs pertaining to customer accounts.


Bleeping Computer
Microsoft is investigating an ongoing Multi-Factor Authentication (MFA) issue preventing some customers from logging into their Microsoft 365 accounts.


CyberSecurity Dive
About 1% of the MFA and single sign-on provider’s business customers are impacted. An attacker intruded the third-party vendor’s systems via phishing.


Infosecurity News
Darktrace reveals a novel phishing campaign where attackers leveraged legitimate Dropbox infrastructure to steal credentials before bypassing MFA


CyberNews
MFA breaches were behind last year’s major cyberattacks against casino giants MGM and Caesars. Yet some companies are just adding it as an extra layer of security.

Ars Technica
Not all MFA is created equal, as script kiddies and elite hackers have shown recently.

The Hacker News
Identity attacks are on the rise! Are your MFA and PAM solutions truly protecting your organization? New report reveals critical protection gaps.

SecurityWeek
CISA and the FBI have warned organizations that Russian state-sponsored threat actors have exploited MFA protocols and the PrintNightmare vulnerability in their attacks.


Latest Hacking News
Box patched the MFA bypass vulnerability following the bug report. The flaw existed in SMS-based OTP authentication mechanism.


Bleeping Computer
A devious new phishing technique allows attackers to bypass MFA by secretly having victims log in to their accounts directly on attacker-controlled servers using VNC.


The Hacker News
FBI and CISA warn that Russian state-sponsored hackers are exploiting misconfigured multi-factor authentication (MFA) protocols and vulnerabilities.


Bleeping Computer
The rising adoption of multi-factor authentication (MFA) for online accounts pushes phishing actors to use more sophisticated solutions to continue their malicious operations, most notably reverse-proxy tools.


The Hacker News
MFA is a must-have in your security environment, but it's important to understand its coverage limitations.


SecurityWeek
US government conducting airline privacy review, SEC’s overreaching SolarWinds hack probe, MFA bombing of Apple users.


SecurityWeek
Zero-Day Vulnerabilities Drive Mass Compromise Events, MFA Still Not Widely Used, Warns Rapid7's Threat Intelligence Report

Bleeping Computer
Cisco Duo's security team warns that hackers stole some customers' VoIP and SMS logs for multi-factor authentication (MFA) messages in a cyberattack on their telephony provider.


Security Affairs
Cisco Duo warns that a data breach involving one of its telephony suppliers exposed MFA messages it sent via SMS and VOIP to its customers.


Infosecurity News
A British Library report found the most likely source of the incident was the compromise of third-party account credentials and no MFA was in place to stop the attackers


Bleeping Computer
Hackers are more frequently using social engineering attacks to gain access to corporate credentials and breach large networks. One component of these attacks that is becoming more popular with the rise of multi-factor authentication is a technique called MFA Fatigue.


Bleeping Computer
Amazon will require all privileged AWS (Amazon Web Services) accounts to use multi-factor authentication (MFA) for stronger protection against account hijacks leading to data breaches, starting in mid-2024.


Bleeping Computer
Identity and access management company Okta released a warning about social engineering attacks targeting IT service desk agents at U.S.-based customers in an attempt to trick them into resetting multi-factor authentication (MFA) for high-privileged users.


CyberSecurity Dive
The “gold standard” safeguard isn’t a one-size-fits-all or all-or-nothing endeavor. For most organizations, a phased approach works best.


Security Affairs
FBI and CISA warn Russia-linked threats actors gained access to an NGO cloud after enrolling their own device in the organization’s Duo MFA. The Federal Bureau of Investigation (FBI) and Cybersecurity and Infrastructure Security Agency (CISA) warned that Russia-linked threat actors have gained access to a non-governmental organization (NGO) cloud by exploiting misconfigured default multifactor […]


Security Affairs
Resecurity researchers discovered a new Phishing-as-a-Service (PhaaS) called EvilProxy advertised on the Dark Web. Original post: https://resecurity.com/blog/article/evilproxy-phishing-as-a-service-with-mfa-bypass-emerged-in-dark-web Following the recent Twilio hack leading to the leakage of 2FA (OTP) codes, cybercriminals continue to upgrade their attack arsenal to orchestrate advanced phishing campaigns targeting users worldwide. Resecurity has recently identified a new Phishing-as-a-Service (PhaaS) called EvilProxy advertised in the Dark […]


Latest Hacking News
The Redmond giant has recently announced introducing a new privacy feature to its authenticator app. With this feature, Microsoft Authenticator app now blocks suspicious multi-factor authentication notifications to prevent potential abuse. Microsoft Authenticator App Blocks Suspicious


DarkReading
Threat actors are widely adopting the fast-growing, low-cost phishing-as-a-service (PhaaS) platform, which is sold via Telegram.


Infosecurity News
UK's security agency warns against letting protection lapse


ThreatPost
A growing class of phishing kits – transparent reverse proxy kits – are being used to get past multi-factor authentication using MiTM tactics.


CyberSecurity Dive
Security tools have evolved to include more accessible protocols that meet stringent authentication requirements. The government wants to embrace that.


CyberSecurity Dive
ESET researchers are separately warning about new data wiping malware.


DarkReading
Multifactor authentication has gained adoption among organizations as a way of improving security over passwords alone, but increasing theft of browser cookies undermines that security.


DarkReading
Several Apple device users have experienced recent incidents where they have received incessant password reset prompts and vishing calls from a number spoofing Apple's legitimate customer support line.

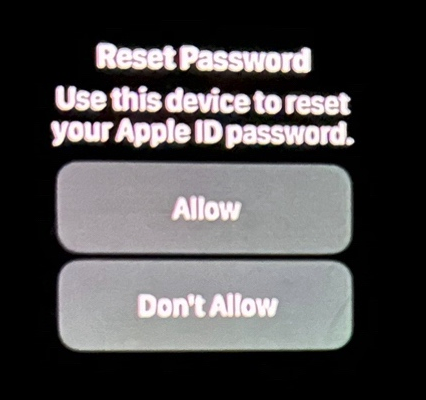
Krebs on Security
Several Apple customers recently reported being targeted in elaborate phishing attacks that involve what appears to be a bug in Apple's password reset feature. In this scenario, a target's Apple devices are forced to display dozens of system-level prompts that…


DarkReading
The ride-sharing giant says a member of the notorious Lapsus$ hacking group started the attack by compromising an external contractor's credentials, as researchers parse the incident for takeaways.


Infosecurity News
Threat actors evolve to multi-factor authentication


Bleeping Computer
Receiving an unprompted one-time passcode (OTP) sent as an email or text should be a cause for concern as it likely means your credentials have been stolen.


DarkReading
The successful combo of stolen credentials and social engineering to breach networks is increasing demand for infostealers on the Dark Web.


Bleeping Computer
Microsoft 365 Defender researchers have disrupted the cloud-based infrastructure used by scammers behind a recent large-scale business email compromise (BEC) campaign.


Bleeping Computer
Microsoft has introduced a new protective feature in the Authenticator app to block notifications that appear suspicious based on specific checks performed during the account login stage.

Bleeping Computer
A new large-scale phishing campaign targeting credentials for Microsoft email services use a custom proxy-based phishing kit to bypass multi-factor authentication.


Infosecurity News
Alert explains how misconfigured authentication allowed hackers in


Bleeping Computer
Crypto exchange Coinbase disclosed that a threat actor stole cryptocurrency from 6,000 customers after using a vulnerability to bypass the company's SMS multi-factor authentication security feature.


DataBreaches
Lawrence Abrams reports: A clever, new phishing technique uses Microsoft Edge WebView2 applications to steal victim’s authentication cookies, allowing...


CSO
Breach was detected and blocked before it granted access to attackers due to the enforcement of multifactor authentication.


Infosecurity News
Andrew Witty made the claims in a written testimony submitted before a House subcommittee hearing


Bleeping Computer
More and more attacks are occurring via browser extensions or user-profile installations of tools. Learn more about these attacks from Specops Software and what you can do to protect yourself.


Bleeping Computer
Software company Retool says the accounts of 27 cloud customers were compromised following a targeted and multi-stage social engineering attack.


Bleeping Computer
LastPass password manager users have been experiencing significant login issues starting early May after being prompted to reset their authenticator apps.


The Record
Despite years of promotional efforts to get users to enable stronger authentication mechanisms, Microsoft said this week that only 22% of all its Azure Active Directory (AD) customers used a multi-factor authentication solution to secure their accounts last year.


Bleeping Computer
Bitwarden, the creator of the popular open-source password manager, has just launched a new authenticator app called Bitwarden Authenticator, which is available for iOS and Android devices.


Bleeping Computer
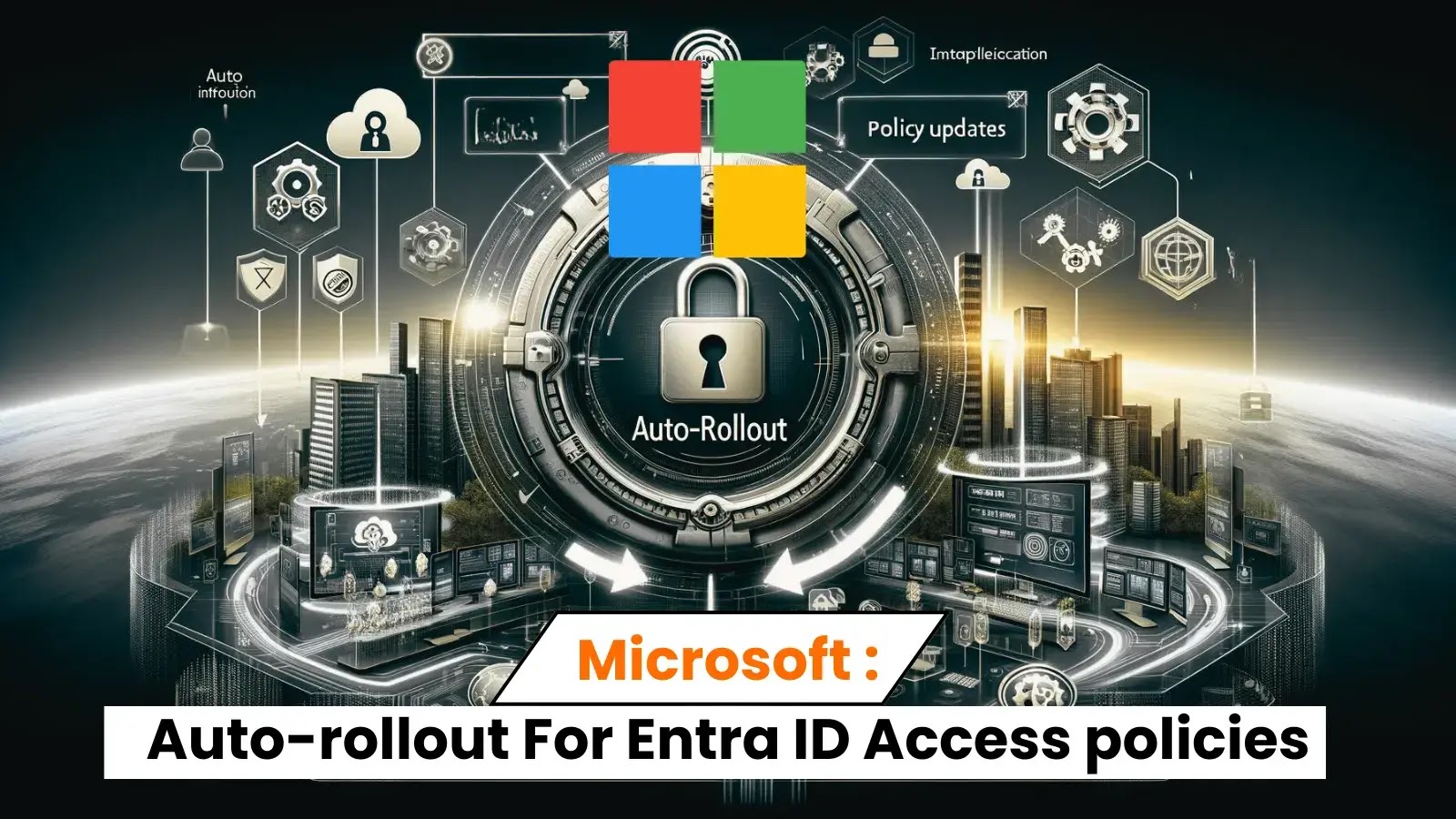
Microsoft will roll out Conditional Access policies requiring multifactor authentication from administrators when signing into Microsoft admin portals such as Microsoft Entra, Microsoft 365, Exchange, and Azure.


Infosecurity News
Proofpoint reveals surge in direct financial losses from attacks


CSO
The phishing web pages that this adversary-in-the-middle phishing campaign uses act as a proxy and pull content from the legitimate Office 365 login page.


SecurityWeek
Breach exposed phone numbers, phone carriers, metadata and other logs that could lead to downstream social engineering attacks.


The Cyber Express
Cisco Duo's security team has issued a warning regarding a cyberattack that compromised some customers' VoIP and SMS logs, potentially


Bleeping Computer
Cybercriminals have been increasingly using a new phishing-as-a-service (PhaaS) platform named 'Tycoon 2FA' to target Microsoft 365 and Gmail accounts and bypass two-factor authentication (2FA) protection.


HACKRead
This article explores Microsoft Azure Entra ID flaw, explains the vulnerability in context, and offers actionable steps to secure your organization.


Bleeping Computer
The threat actor behind the Twilio hack used their access to steal one-time passwords (OTPs) delivered over SMS to from customers of Okta identity and access management company.


Ars Technica
Rapid-fire prompts sometimes followed with spoofed calls from "Apple support."


CyberSecurity Dive
Lapsus$, one of the most prolific ransomware actors of 2022, has utilized such tactics to breach a number of high-profile organizations.


SC Magazine
A social-engineering attack against one of the company’s telephony suppliers led to the breach.


CyberSecurity Dive
A study says organizations need to implement automated hardening techniques to protect systems against future data breaches.


Ars Technica
The wide range of employee roles targeted indicates attacker's multifaceted approach.


DarkReading
Many of the technologies and services that organizations are using to isolate Internet traffic from the internal network lack session validation mechanisms, security startup says.


Ars Technica
Some forms of multi-factor authentication only go so far in preventing account takeovers.


CyberSecurity Dive
AlphV deployed ransomware nine days after it used access to a Citrix portal on Change’s network to move laterally within systems, CEO Andrew Witty said in testimony prepared for a House subcommittee hearing set for Wednesday.


Bleeping Computer
The threat actor behind the Twilio hack used their access to steal one-time passwords (OTPs) delivered over SMS to from customers of Okta identity and access management company.


DataBreaches
Seen on Resecurity’s blog: a reminder that our current defenses fall rapidly as nimble criminals find a work-around and that some developments enable...

ZDNet
Watch out for default configuration on MFA implementation.


The Cyber Express
CEO Andrew Witty testified before Congress on Wednesday, disclosing a significant cyberattack on Change Healthcare, a subsidiary of UnitedHealth Group.

ZDNet
Microsoft plans to make it easier for organizations using Azure Active Directory to enforce multi-factor authentication for users from external organizations.


CyberSecurity Dive
IT workers at four organizations using Okta were successfully hit by a consistent pattern of social engineering attacks.


CyberSecurity Dive
Additional security features could prevent phishing scams and lower exposure for companies that let workers use personal devices for work.


Bleeping Computer
A new campaign from the hacking group tracked as APT36, aka 'Transparent Tribe' or' Mythic Leopard,' has been discovered using new custom malware and entry vectors in attacks against the Indian government.


Bleeping Computer
The Aberebot banking trojan appears to have returned, as its author is actively promoting a new version of the tool on dark web markets and forums.


DataBreaches
Bill Toulas reports: A new large-scale phishing campaign targeting credentials for Microsoft email services use a custom proxy-based phishing kit to bypass...


Bleeping Computer
A threat actor known as W3LL developed a phishing kit that can bypass multi-factor authentication along with other tools that compromised more than 8,000 Microsoft 365 corporate accounts.


Cyber Security News
Dropbox disclosed a significant security breach affecting its electronic signature service, Dropbox Sign (formerly known as HelloSign).


Bleeping Computer
UnitedHealth confirms that Change Healthcare's network was breached by the BlackCat ransomware gang, who used stolen credentials to log into the company's Citrix remote access service, which did not have multi-factor authentication enabled.


ZDNet
Here's how combining single sign-on and multi-factor authentication can added up to a secure cloud-based strategy.


CyberSecurity Dive
The White House's memorandum builds on past requirements to bolster U.S. cyber standards. This time, the administration is targeting agencies that handle classified intelligence.

Ars Technica
Google's app for generating MFA codes syncs to user accounts by default. Who knew?


SC Magazine
Commission staff requested MFA be deactivated on the account several months before it was compromised.

Latest Hacking News
Microsoft noted the phishing campaign successfully registers attacker's device to victim networks that lacked MFA protection.

Cyber Security News
Microsoft has unveiled the automatic rollout of multifactor authentication (MFA)-related Conditional Access policies in Entra ID.


The Hacker News
RubyGems, the official Ruby package manager, now requires top project maintainers to use multi-factor authentication (MFA).


The Hacker News
Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop
Loading more articles....