

DataBreaches
Japan’s “K” Line Apologizes for Second Cyberattack in Months
The Maritime Executive reports: Japanese shipping company Kawasaki Kisen Kaisha, known as “K” Line issued a brief statement today confirming that its...


DataBreaches
The Maritime Executive reports: Japanese shipping company Kawasaki Kisen Kaisha, known as “K” Line issued a brief statement today confirming that its...


DarkReading
A Japanese ministry blames a shared Active Directory between merged tech companies Line and South Korea's Naver for a massive data breach last November.


SecurityWeek
Cloud security specialists found data exposure risk associated with Azure, AWS, and Google Cloud command-line tools.


DataBreaches
Sunaina reports: LINE Pay, a smartphone payment provider, announced yesterday that between September and November of this year, approximately 133,000 users’...


DataBreaches
Jessica Lyons Hardcastle reports: False-flag cyberattacks represent a red line that even nation states like Russia and China don’t want to cross,...

Bleeping Computer
The Windows 10 package manager is getting some new and exciting features that allow you to manage any installed applications directly from the command line.


SecurityWeek
Weakening liberal democracies and weakening the NATO alliance are conjoined in the hybrid war that Russia is conducting against Ukraine.


DataBreaches
Kyodo News reported: Tech giant LY Corp. reported a massive data breach on Monday, saying as many as 440,000 items of personal data, including more than...


DarkReading
Infighting, conscription, emigration. The war in Ukraine has pitted cybercriminals against one another like no other event before it.


The Hacker News
Your emotions can be a vulnerability in the world of cybersecurity. Learn how to defend against these manipulations.


Security Affairs
CyberNews researchers discovered that at least one of the Cl0p ransomware gang masterminds is still residing in Ukraine. Original post at: https://cybernews.com/security/cl0p-hacker-hides-in-ukraine/ As the Cl0p ransomware gang continues to sow anxiety worldwide, affecting prominent companies like the BBC and Deutsche Bank, at least one of the gang masterminds, Cybernews discovered, is still residing in Ukraine. […]


Bleeping Computer
The Mastering Linux Development Bundle helps you take full control, with seven courses covering a range of skills. The training is worth $1,400 in total, but you can get it today for only $19.99


DataBreaches
There’s an update to a breach in 2019 that was first disclosed in March 2020: ATLANTA, GA – Attorney General Chris Carr today announced that the State...


DataBreaches
Katrina Manson reports: A common explanation for why the Soviet Union never used nuclear weapons during the Cold War was the expectation that any attack would...


Security Affairs
California-based Resecurity has identified a new spike of underground services enabling bad actors to generate deepfakes. According to cybersecurity experts, this may be used for political propaganda, foreign influence activity, disinformation, scams, and fraud. Introduced by Canadian researchers to the public in 2014, Generative Adversarial Networks (GANs), typically imitate people’s faces, speech, and unique facial […]


Ars Technica
Customers of the Ivanti Endpoint Protection Manager should patch or mitigate ASAP.


Ars Technica
Defendants allegedly conspired with Russians, drew as many as 1,000 daily trips.


SecurityWeek
SecurityWeek Hacker Conversations interview with HD Moore, best known as the founder and original developer of Metasploit.


Infosecurity News
The breach exposed Seiko Watch Corporation customer, employment and personnel information


DataBreaches
Amanda Seitz of AP reported: A cyberattack caused a nearly daylong outage of the nation’s new 988 mental health helpline late last year, federal officials...


CSO
New integration with Okta, containerization support and a tagging system are all present in the latest version of Remote.it’s network management platform.


CyberSecurity Dive
Critical infrastructure is on high alert, but — at least for now — the conflict in Europe could signal a lull in utility ransomware attacks.


CyberSecurity Dive
“If you look across all of these categories, security is a line item in all of them,” Spiceworks Ziff Davis’ Peter Tsai said.


The Cyber Express
A newly identified threat actor, known as "Bawless service," has surfaced on the messaging platform Telegram, showcasing a potentially dangerous


CyberNews
A line of stuck Alphabet's Waymo driverless taxis blocked traffic and frustrated residents in the Bay Area.


Bleeping Computer
Microsoft has finally made Windows Terminal the default terminal in Windows 11 Insider 'Dev' preview builds, bringing a new modern interface for all your command-line programs.


Bleeping Computer
Microsoft is moving forward with removing the Windows Management Instrumentation Command-line (WMIC) tool, wmic.exe, starting with the latest Windows 11 preview builds in the Dev channel.


SecurityWeek
Critical flaws could be exploited to bypass SSH authentication and gain access to the Aria Operations for Networks command line interface.


ZDNet
Moody's examines how incident response and defense have implications for the market.


Security Affairs
Researchers reported that the top-of-the-line Android mobile devices sold in China are shipped with surveillance software. China is currently the country with the largest number of Android mobile devices, but a recent study conducted by researchers from the University of Edinburgh and the Trinity College of Dublin revealed that top-of-the-line Android devices sold in the […]


The Record
Palo Alto Networks is urging customers to patch a line of firewall products after finding that the vulnerability was used in a DDoS attack.


ZDNet
The bottom line is that right now, an entry-level cybersecurity role has requirements much closer to an intermediate one.


Infosecurity News
Ukraine's allies may be in the firing line for destructive attacks


Cyber Security News
Curl command line tool posted a pre-announcement regarding two vulnerabilities that affected both the curl tool and the libcurl library.


Naked Security
A rogue line-continuation character can trick the code into validating just the second half of the line, but executing all of it.


DataBreaches
The email in my inbox on Friday night had the subject line, “Hey sexy,” and appeared to come from “eims@ic.fbi.gov” <eims@ic.fbi...


Cyber Security News
The line of control has been under too much pressure after what happened between Ukraine and Russia. The two countries were being attacked everyday by every means.


Bleeping Computer
Microsoft has fixed a critical security vulnerability that could let attackers steal credentials from GitHub Actions or Azure DevOps logs created using Azure CLI (short for Azure command-line interface).


Bleeping Computer
Windows Terminal is now the default console for Windows 11 22H2, marking a significant shift in how Windows users run their command line programs.


CyberNews
Line app has informed users about unauthorized access to its systems, which resulted in hundreds of thousands of user, business partner, and employee records being leaked.

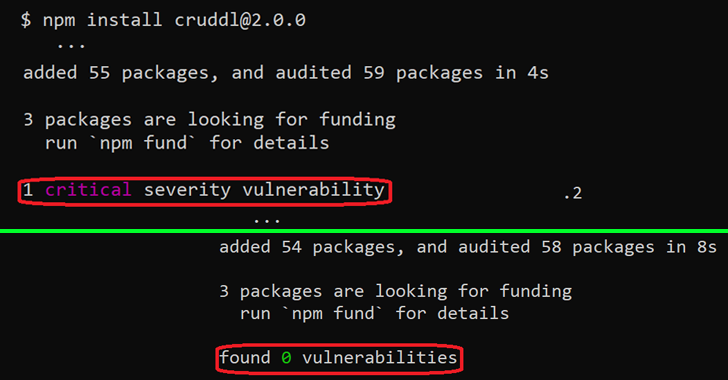
The Hacker News
An "unexpected behavior" in the npm command line interface could allow malicious NPM libraries to bypass security checks and hide vulnerabilities.

SecurityWeek
Bishop Fox has released CloudFox, an open source command line tool designed to help pentesters find exploitable attack paths in the cloud.


Infosecurity News
Regulator takes a harder line on enforcement


Ars Technica
One does not simply suggest changing a kernel line to help out a parsing tool.


ZDNet
In line with last month's communities announcement, users can now send files up to 2GB in size at a time, protected by end-to-end encryption.


DarkReading
This is the latest in a line of law-enforcement actions busting up the ransomware scene.


ThreatPost
2.5 million people were affected, in a breach that could spell more trouble down the line.


Security Affairs
Cisco Talos researchers published PoC exploits for vulnerabilities in Netgear Orbi 750 series router and extender satellites. Netgear Orbi is a line of mesh Wi-Fi systems designed to provide high-speed, reliable Wi-Fi coverage throughout a home or business. The Orbi system consists of a main router and one or more satellite units that work together […]


Infosecurity News
Global report ties poor security to bottom-line impact


DataBreaches
Admire Moyo reports: The Cyber Crimes Bill, which seeks to bring SA’s cyber security laws in line with the rest of the world, has just been signed into law...


DataBreaches
Thomas Rudkin of Farrer & Co writes: There is a developing line of cases in England & Wales where those who have been subject to a ransomware attack...

SecurityWeek
Proofpoint expands enterprise security product line with cyber deception technology acquisition.


ZDNet
For Formula 1 teams, the cybersecurity race has no finish line.


CyberScoop
The sophisticated hacking effort is the latest in a long line of financially motivated malware campaigns emanating from Brazil.


DataBreaches
Although HHS OCR generally fails to take a hard enforcement line with reporting breaches by the “no later than 60 day” rule in HIPAA, state...


CyberSecurity Dive
The 72-hour timeframe falls in line with the Critical Infrastructure Act that President Joe Biden signed in March, but is twice as long as the reporting window banks have had to comply with since May.

Ars Technica
ChatGPT-generated command line can create virtual files, execute code, play games.


Ars Technica
Cheaper GPUs are good for gamers but bad for Nvidia's bottom line.


CSO
Generative AI is coming to both line-of-business data analysis as well as security, as Cohesity deepens its ties to Microsoft.

Computerworld
Mosyle Hardening and Compliance ensures that employee devices are protected, compliant and are in line with the latest cybersecurity benchmarks.


DataBreaches
Wendy Ruderman reports: Federal and state authorities are looking into allegations that a Main Line Women’s Healthcare employee used a personal cellphone to...


DataBreaches
Catalin Cimpanu reports: Australian security researcher Troy Hunt announced today that he granted the US Federal Bureau of Investigation a direct line to...


The Cyber Express
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ


The Record
A Q&A Steven Adeoye on the line between art and its inspiration.


Cyber Security News
Endpoint Security Best Practices: Endpoint security serves as the first line of defense against cyberattacks for businesses.

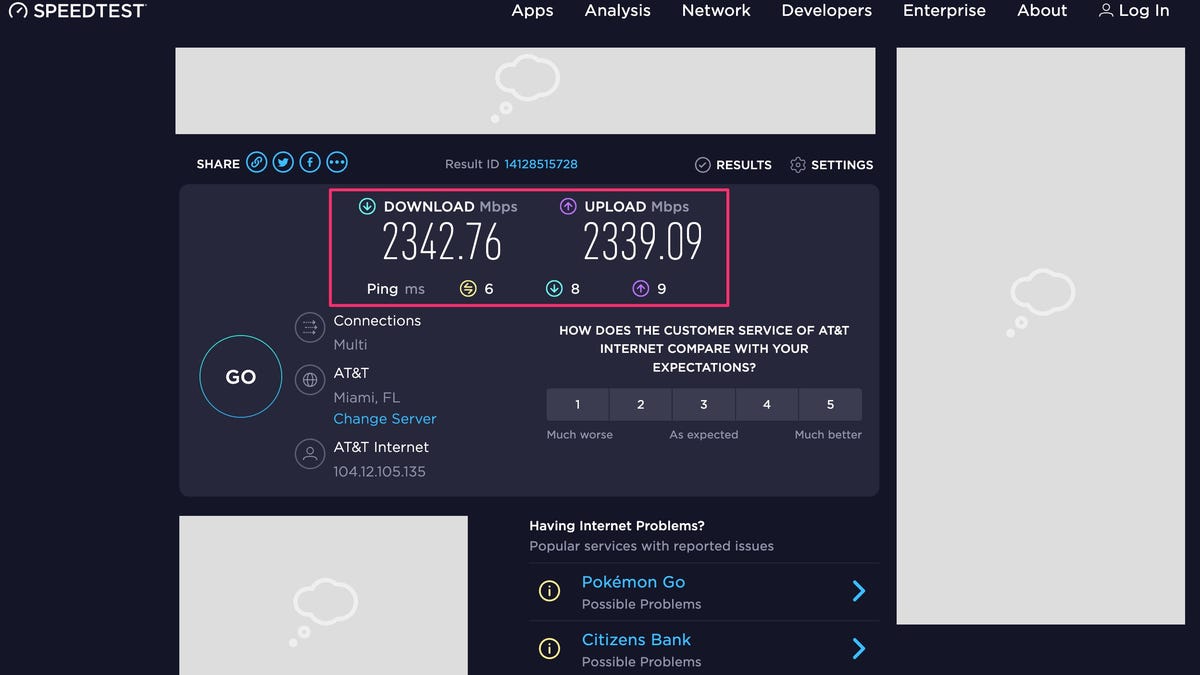
ZDNet
Wire-line speeds at over 2Gbps require fast switches and Wi-Fi APs, and very fast firewalls


DataBreaches
Intel471 writes: Ransomware attacks have crossed a red line for many countries with continued merciless attacks. The threat to national economies and critical...


Security Affairs
An affiliate of the LockBit 3.0 RaaS operation has been abusing the Windows Defender command-line tool to deploy Cobalt Strike payloads. During a recent investigation, SentinelOne researchers observed threat actors associated with the LockBit 3.0 ransomware-as-a-service (RaaS) operation abusing the Windows Defender command line tool MpCmdRun.exe to decrypt and load Cobalt Strike payloads. The attackers initially compromise the target […]

Bleeping Computer
Microsoft has released the first stable version of the native Winget Windows 10 package manager that helps you manage applications directly from the command line.


The Record
Operational technology giant Honeywell joined the Cybersecurity and Infrastructure Security Agency (CISA) Thursday in warning of several serious vulnerabilities affecting a line of industrial control tools used widely within the manufacturing industry.


DataBreaches
Marcus Hand reports that the South Korean shipping line has disclosed a breach: HMM said that an unidentified security breach was detected to its email servers...


ThreatPost
The RV line of small-business routers contains 15 flaws that could enable RCE, corporate network access or DoS – and many have exploits circulating.


Cyber Security News
In a current active malware campaign, the cybersecurity analysts at Crowdstrike have claimed that LemonDuck uses the Docker command-line tool to deploy a cross-platform mining botnet on Linux operating systems.


CSO
In what the chipmaker claims is an industry first, the latest processor line from Intel will incorporate threat detection right into the hardware, bolstering EDR and other cybersecurity platforms.


DataBreaches
Tom Hesse reports: Eastern Europe can be perilous if you have the kind of job Kurtis Minder has. It’s a line of work featuring regular correspondence with...


Bleeping Computer
Security analysts have observed an affiliate of the LockBit 3.0 ransomware operation abusing a Windows Defender command line tool to decrypt and load Cobalt Strike beacons on the target systems.


Bleeping Computer
Security analysts have observed an affiliate of the LockBit 3.0 ransomware operation abusing a Windows Defender command line tool to decrypt and load Cobalt Strike beacons on the target systems.


Bleeping Computer
This month, Amazon has announced that Mozilla will phase out support for the Firefox web browser app on Amazon's Fire TV product line.


PCMag
Two New York City residents worked with Russian hackers to hijack the taxi dispatch system at John F. Kennedy International Airport to help drivers skip the wait line.

CSO
The software supply chain security tool will host new secret detection capabilities through the command-line interface to help developers prioritize remediation efforts.


Security Affairs
SonicWall warns customers to address several high-risk security flaws impacting its Secure Mobile Access (SMA) 1000 Series line of products. SonicWall urges customers to address several high-risk security vulnerabilities affecting its Secure Mobile Access (SMA) 1000 Series line of products. An attacker can exploit the vulnerabilities to bypass authorization and, potentially, compromise vulnerable devices. The first issue, tracked as […]


The Record
The ringleader of a scheme to hack into the taxi dispatch system at New York City’s John F. Kennedy International Airport and charge drivers to skip ahead in the pickup line was sentenced to four years in U.S. prison on Monday. An accomplice, Peter Leyman, was sentenced to two years in prison.


SC Magazine
Andrew Witty stuck with the familiar corporate line of providing consumers with two years of credit monitoring.


Cyber Security News
SonicWall issued a security notice urging customers to immediately patch several vulnerabilities that are considered high-risk affecting its Secure Mobile Access (SMA) 1000 Series line of products.


DataBreaches
Earlier today, vx-underground reported that a hoax email was being sent from Equifax with the subject line “Free Pompompurin.” An unknown...


DataBreaches
Karl Bode writes: A few weeks ago, The Verge discovered that Anker, the maker of popular USB chargers and the Eufy line of “smart” cameras, had a bit of a...


Computerworld
As unified endpoint management platforms mature, vendors are expanding feature sets, embracing ‘modern management,’ and blurring the line between endpoint management and security.


Ars Technica
With deepfake audio, that familiar voice on the other end of the line might not even be human.


ThreatPost
The Vultur trojan steals bank credentials but asks for permissions to do far more damage down the line.

Bleeping Computer
AI research company OpenAI announced today the launch of a new bug bounty program to allow registered security researchers to discover vulnerabilities in its product line and get paid for reporting them via the Bugcrowd crowdsourced security platform.


ThreatPost
It's a double-extortion play that uses the command-line password ‘KissMe’ to hide its nasty acts and adorns its ransom note with cutesy ASCII bunny art.


DataBreaches
An email DataBreaches received yesterday from an unrecognized account contained just one line – a link to a new listing on the D#nut Leaks ransomware...


ZDNet
Security Keys can help to create an extra line of defense for your Apple ID to keep hackers away.


Bleeping Computer
If you ever wanted to play DOOM on a lawnmower, you will soon have your chance with a new software update coming to Husqvarna's robotic line of lawnmowers this spring.


CyberNews
Firefighters put their lives on the line as they enter a burning building. A new study shows that artificial intelligence (AI) could mitigate that risk by giving them an early warning.


Trend Micro
President Biden banned the sale of Russian oil to the United States to deprive the Putin regime of the economic resources needed to wage war. But this may put US companies in the firing line of cyber-attacks from the east.


CyberSecurity Dive
With a line of sight on security operations, managed service providers hold keys to materiality determinations and annual 10-K reports.


CyberSecurity Dive
In line with a White House push to close the cyber skills gap, technology firms, nonprofits and other organizations have launched a range of programs to develop a new generation of workers.


Bleeping Computer
SonicWall "strongly urges" customers to patch several high-risk security flaws impacting its Secure Mobile Access (SMA) 1000 Series line of products that can let attackers bypass authorization and, potentially, compromise unpatched appliances.


SC Magazine
A simple 10-line program could allow an attacker to “listen” to private machine learning processes, according to researchers from Trail of Bits.
Loading more articles....