

The Hacker News
What's the Right EDR for You?
EDR solutions can detect threats that traditional defenses like antivirus often miss. Find out how EDR provides a deeper level of security.


The Hacker News
EDR solutions can detect threats that traditional defenses like antivirus often miss. Find out how EDR provides a deeper level of security.


Cyber Security News
In the rapidly evolving, complex threat landscape EDR companies constantly race against new vectors.As recently Helvio Benedito Dias de

Latest Hacking News
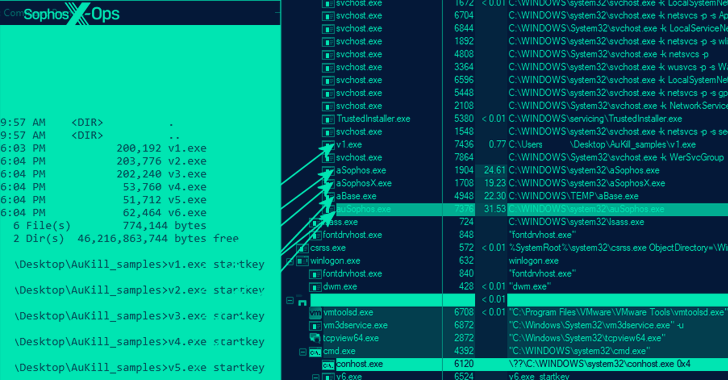
Researchers have discovered a new malware that remained under the radar for quite some time. Identified is AuKill, it is a potent EDR kill malware that leverages BYOVD to disable EDR clients. The hackers have


Infosecurity News
Acronis EDR is integrated into its Cyber Protect Cloud solution along with backup and data recovery functionalities

The Hacker News
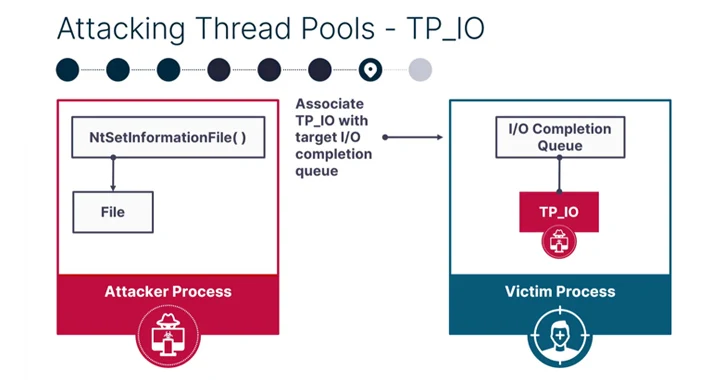
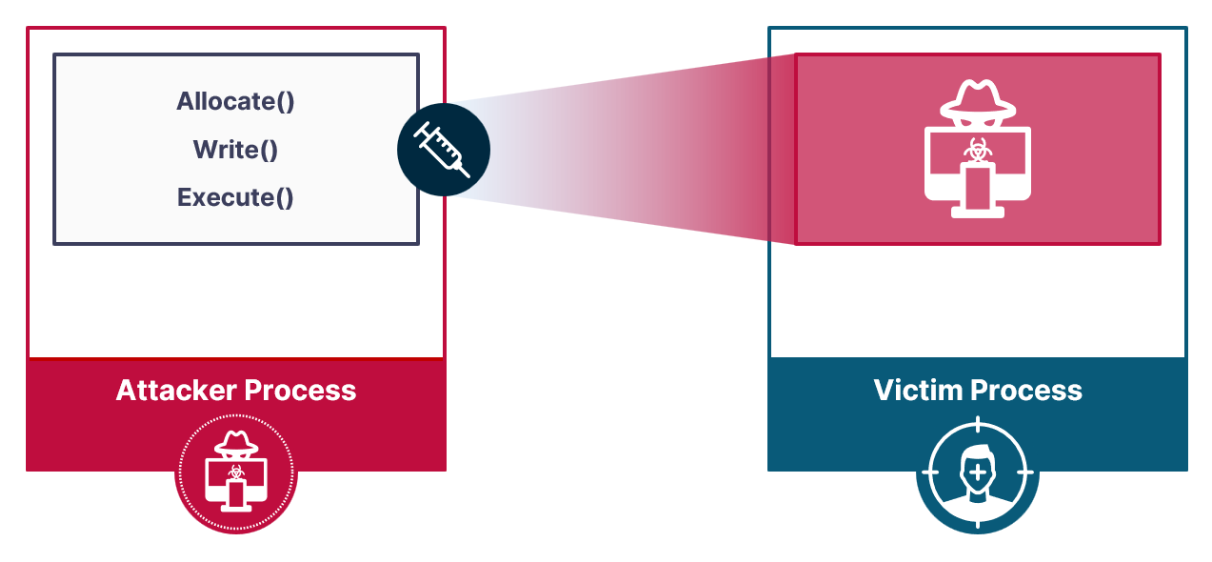
New process injection techniques called "PoolParty" allow code execution on Windows systems while evading EDR detection.


Security Affairs
Ransomware operators use the AuKill tool to disable EDR software through Bring Your Own Vulnerable Driver (BYOVD) attack. Sophos researchers reported that threat actors are using a previously undocumented defense evasion tool, dubbed AuKill, to disable endpoint detection and response (EDR) software. The tool relies on the Bring Your Own Vulnerable Driver (BYOVD) technique to disable the […]


Bleeping Computer
A new process injection technique named 'Mockingjay' could allow threat actors to bypass EDR (Endpoint Detection and Response) and other security products to stealthily execute malicious code on compromised systems.

The Hacker News
EDR provides some endpoint protection, but Network Detection and Response (NDR) solutions are a proven and reliable way of monitoring network traffic,

Latest Hacking News
The newly devised Mockingjay process injection technique can evade most existing security mechanisms, allowing EDR bypass. It’s a trivial process to carry out, requires minimal steps, and delivers maximum results merely by exploiting legit DLLs. Researcher

The Hacker News
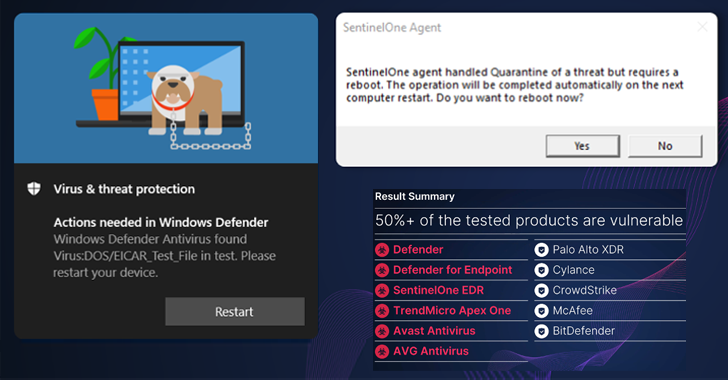
Researchers have discovered new vulnerabilities in popular endpoint detection and response (EDR) and antivirus solutions (AV) that can be weaponized a

The Hacker News
Ransomware attackers are utilizing a new "defense evasion tool" called AuKill to deactivate EDR software using a BYOVD attack.


Bleeping Computer
A security researcher has found a way to exploit the data deletion capabilities of widely used endpoint detection and response (EDR) and antivirus (AV) software from Microsoft, SentinelOne, TrendMicro, Avast, and AVG to turn them into data wipers.


Bleeping Computer
Emsisoft is having a holiday deal where you can get 20% off 1-year licenses of the Emsisoft Enterprise Security EDR solution through December 17th, 2023, with no license limits.


Bleeping Computer
The Windows 11 22H2 KB5027231 cumulative update released during this month's Patch Tuesday also breaks Google Chrome on systems protected by Cisco and WatchGuard EDR and antivirus solutions.

SecurityWeek
Several cybersecurity firms have warned Microsoft that cybercriminals have been using signed malicious drivers to kill antivirus and EDR processes.


DarkReading
Attackers are using custom malware to exploit drivers and terminate security processes so they can deploy ransomware.


DarkReading
The technique loads a non-monitored and unhooked DLL, and leverages debug techniques that could allow for running arbitrary code.


Security Affairs
Mockingjay is a new process injection technique that can be exploited to bypass security solutions to execute malware on compromised systems. A new process injection technique dubbed Mockingjay can be exploited by attackers to bypass security controls and gain unauthorized access to compromised systems. The term process injection is used to refer to a method […]


DarkReading
The previously unknown malware (aka Hidden Shovel) is a ghost in the machine: It silently attacks kernel drivers to shut down security defense systems and thus evade detection.


Bleeping Computer
A malicious crypto mining campaign codenamed 'REF4578,' has been discovered deploying a malicious payload named GhostEngine that uses vulnerable drivers to turn off security products and deploy an XMRig miner.


DarkReading
Two new code-execution techniques, Poison Fiber and Phantom Thread, take advantage of a little-known Windows OS workhorse to sneak shellcode and other malware onto victim machines.


DarkReading
Researchers warn that polymorphic malware created with ChatGPT and other LLMs will force a reinvention of security automation.


SecurityWeek
Pool Party is a new set of eight Windows process injection techniques that evade endpoint detection and response solutions.


SecurityWeek
Vulnerabilities in Palo Alto Networks Cortex XDR allowed a security researcher to turn it into a malicious offensive tool.

Cyber Security News
Researchers discovered REF4578, an intrusion set that uses vulnerable drivers to disable established security solutions (EDRs) for crypto


Bleeping Computer
An updated version of the MATA backdoor framework was spotted in attacks between August 2022 and May 2023, targeting oil and gas firms and the defense industry in Eastern Europe.

DarkReading
New Golang cyberattacks use deep space images and a new obfuscator to target systems — undetected.


DarkReading
Malicious Windows drivers signed as legit by Microsoft have been spotted as part of a toolkit used to kill off security processes in post-exploitation cyber activity.


Cyber Security News
From handling simple inquiries to instantly generating written works and even developing original software programs, including malware, ChatGPT proves to be an all-encompassing solution. However, this advancement also introduces the potential for a dangerous new cyber threat. Traditional security solutions such as EDRs harness multi-layered data intelligence systems to combat the highly sophisticated threats prevalent […]


Cyber Security News
The cybersecurity researchers at Security Joes recently discovered a new injection technique that is dubbed "Mockingjay."


Cyber Security News
Security experts have developed a method for tricking the well-known AI Chatbot ChatGPT into creating malware. So all you need to get the chatbot to perform what you want is some smart questions and an authoritative tone.


ThreatPost
Ashwin Vamshi Adware strains Shlayer and Bundlore are the most common malware in macOS – although they have slight variations, they have long invaded and bypassed Xprotect, Notarization, Gatekeeper, and File Quarantine, all security features pre-built into macOS. The Uptycs threat research team has tracked these threats, along with 90% of macOS malware in routine


DarkReading
A newly patched flaw in Windows Defender allows attackers to hijack the signature-update process to sneak in malware, delete benign files, and inflict mayhem on target systems.

Security Affairs
Researchers devised novel attack vector for process injection, dubbed Pool Party, that evades EDR solutions.


DarkReading
Campaign demonstrates the DPRK-backed cyberattackers are gaining tools to avoid EDR tools.


CyberSecurity Dive
The technique was discovered by Mandiant researchers looking into a campaign designed to avoid EDR detection.


The Hacker News
Unlock Endpoint Security with our top 10 must-know tips! From MFA to EDR, discover how to protect your digital kingdom.

SecurityWeek
A SafeBreach security researcher discovered several vulnerabilities that allowed him to turn endpoint detection and response (EDR) and antivirus (AV) tools into wipers.

SecurityWeek
Microsoft's SMB-focused Defender for Business packs antivirus capabilities, attack surface reduction, and endpoint detection and response (EDR) features.


The Hacker News
Ransom demands, data theft, operational halt... The nightmare of cyberattacks on SMBs. Can you afford to risk it? Read how Managed EDR can help

SecurityWeek
BlackByte ransomware is seen targeting a vulnerability in the legitimate RTCore64.sys driver to disable EDR solutions.


CyberSecurity Dive
More than 50 federal agencies expect to have EDR technology by the end of fiscal year.


SC Magazine
Security pros say it almost looks like the malware developers have an EDR product manager on staff.


The Hacker News
Discover the limitations of honeypots, CDN providers & EDR/XDR in cybersecurity intelligence.


CSO
In what the chipmaker claims is an industry first, the latest processor line from Intel will incorporate threat detection right into the hardware, bolstering EDR and other cybersecurity platforms.


Bleeping Computer
Threat actors use a new hacking tool dubbed AuKill to disable Endpoint Detection & Response (EDR) Software on targets' systems before deploying backdoors and ransomware in Bring Your Own Vulnerable Driver (BYOVD) attacks.


The Record
A team of Greek academics has tested endpoint detection & response (EDR) software from 11 of today's top cybersecurity firms and found that many fail to detect some of the most common attack techniques used by advanced persistent threat actors, such as state-sponsored espionage groups and ransomware gangs.


Bleeping Computer
A financially motivated threat actor tracked as Scattered Spider was observed attempting to deploy Intel Ethernet diagnostics drivers in a BYOVD (Bring Your Own Vulnerable Driver) attack to evade detection from EDR (Endpoint Detection and Response) security products.

The Cyber Wire
Comprehensive guide on mitigating Phobos ransomware threats, issued by the FBI, CISA, and MS-ISAC. This advisory unpacks the tactics, techniques, and procedures (TTPs) of the Phobos ransomware, operating under a Ransomware-as-a-Service (RaaS) model, targeting critical infrastructures since May 2019. Learn about effective strategies to secure RDP ports, remediate vulnerabilities, and implement EDR solutions to safeguard against this evolving cyber threat.

Infosecurity News
BlackByte delivers new way to circumvent endpoint detection


Trend Micro
The latest study said that OT security is less mature in several capabilities than IT security, but most organizations are improving it.


Security Affairs
SolarWinds warns customers of potential cyberattacks targeting unpatched installs of its Web Help Desk (WHD) product. SolarWinds has published a security advisory to warn customers of the risk of cyberattacks targeting unpatched Web Help Desk (WHD) installs. The WHD is described by SolarWinds as an affordable Help Desk Ticketing and Asset Management Software. SolarWinds declared […]

Ars Technica
Two of the simplest forms of evasion are surprisingly effective against EDRs.


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing


Cyber Security News
The cryptocurrency miner occurred when a suspicious Windows service was found running on the endpoint, triggering an alert shortly after the miner was installed


Security Affairs
The Uptycs threat research team has been observing an increase in utilization of regsvr32.exe heavily via various types of Microsoft Office documents. The full report that includes Indicators of Compromise (IOCs) is available here: https://www.uptycs.com/blog/attackers-increasingly-adopting-regsvr32-utility-execution-via-office-documents During our analysis of these malware samples, we have identified that some of the malware samples belonged to Qbot and […]

The Hacker News
CVSS v4.0 evaluates vulnerabilities using a revised scoring system, emphasizing environmental and threat metrics.


DarkReading
Disguised as harmless PDF documents, LNK files trigger a PowerShell script, initiating a Rust-based injector called Freeze[.]rs and a host of malware infections.


CSO
Cybersecurity vendor says enhancement allows for increased human-led threat hunting to uncover more behavior-based findings associated with specific threat actors.


Bleeping Computer
A threat actor known as Spyboy is promoting a Windows defense evasion tool called "Terminator" on the Russian-speaking forum RAMP (short for Russian Anonymous Marketplace).

SecurityWeek
SolarWinds this week issued an alert to warn customers of potential cyberattacks targeting unpatched Web Help Desk (WHD) instances.


Infosecurity News
The cybersecurity monitoring firm offers 18 recommendations on security controls to help organizations anticipate tougher cybersecurity regulations

Cyber Security News
Endpoint Security Tools let security teams to monitor and secure all connected devicesit uncover dwelling threats.


Security Affairs
Sentinel Labs found evidence that links the Black Basta ransomware gang to the financially motivated hacking group FIN7. Security researchers at Sentinel Labs shared details about Black Basta‘s TTPs and assess it is highly likely the ransomware operation has ties with FIN7. The experts analyzed tools used by the ransomware gang in attacks, some of […]


Ars Technica
A key component: Installing known vulnerable drivers from Avast and IOBit.


The Hacker News
Not all attacks start at the endpoint. Inline security controls must be prioritized over passthrough detection.


SecurityWeek
Fresh off its $69 billion acquisition of VMware, Broadcom creates an Enterprise Security Group unit that merges Symantec and Carbon Black.


Security Affairs
An initial access broker claims to have hacked Deutsche Bank and is offering access to its systems for sale on Telegram. A threat actor (0x_dump) claims to have hacked the multinational investment bank Deutsche Bank and is offering access to its network for sale online. The security researcher Dominic Alvieri was one of the first experts […]


SC Magazine
Trellix researchers say the RansomHouse group is mostly targeting corporate networks in the U.S. with multiple hypervisors.


DataBreaches
Bill Toulas reports: Security researchers at Sentinel Labs have uncovered evidence that links the Black Basta ransomware gang to the financially motivated...


DarkReading
Collaboration between the two firms will help organizations better identify and protect against complexity cyberthreats, chief executives from both companies said.


CSO
The new tools and capabilities include AI-enhanced incident investigation, no-code application development, XDR, and data protection, exposure management, and IT automation features.


Bleeping Computer
SolarWinds warned customers of attacks targeting Internet-exposed Web Help Desk (WHD) instances and advised removing them from publicly accessible infrastructure (likely to prevent the exploitation of a potential security flaw).

Bleeping Computer
Microsoft announced today that it added device isolation support via Microsoft Defender for Endpoint (MDE) on onboarded Linux devices.

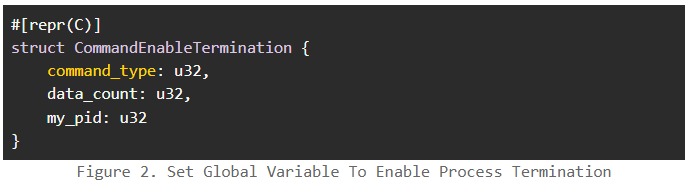
Security Affairs
Researcher demonstrated how to exploit a signed Minifilter Driver in a BYOVD attack to terminate a specific process from the kernel.

The Hacker News
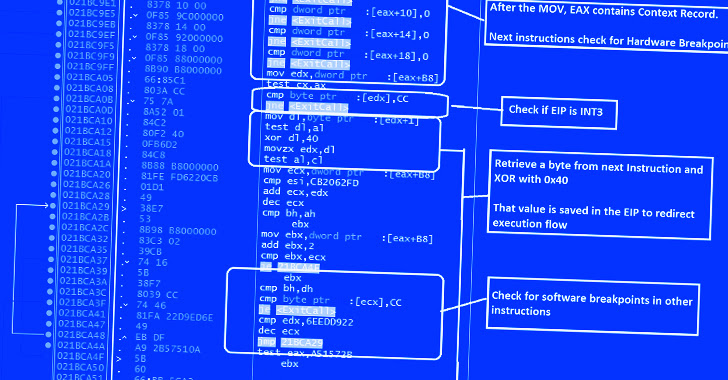
GuLoader malware using advanced tactics to bypass security software.


DataBreaches
Trend Micro Incorporated, a global cybersecurity leader, today revealed that 86% of global healthcare organizations (HCOs) that have been compromised by...


DataBreaches
Over the past week, I’ve been contacted by a number of people. Some have contacted me to say that they see what has been going on with the harassment and...


The Hacker News
Worried about your organization's security? Managed Detection and Response (MDR) is the key!


ZDNet
A new batch of cyberthreats requires shifting away from the best-of-breed, point-product approach to security.


Cyber Security News
It has been identified recently that a RAT known as ZuoRAT is hijacking SOHO routers to target remote workers. As of 2020.


DataBreaches
The Twitter account of a researcher known on Twitter as @ido_cohen2 is gone and their DarkFeed.io site has an “under maintenance” notice for the...


DataBreaches
Bethan Moorcraft reports: Cyber insurers are hyper-focused today on best-practice risk mitigation and cybersecurity protocols. Many carriers have introduced...


Security Affairs
Researchers attribute the Raspberry Robin malware to the Russian cybercrime group known as Evil Corp group. IBM Security X-Force researchers discovered similarities between a component used in the Raspberry Robin malware and a Dridex malware loader, which was part of the malicious operations of the cybercrime gang Evil Corp. Raspberry Robin is a Windows worm discovered […]


Bleeping Computer
The BlackByte ransomware gang is using a new technique that researchers are calling "Bring Your Own Driver," which enables bypassing protections by disabling more than 1,000 drivers used by various security solutions.

SecurityWeek
Security and networking platform provider Todyl has raised $28 million in Series A funding led by Anthos Capital.


Bleeping Computer
Recent attacks from Ryuk ransomware operators show that the actors have a new preference when it comes to gaining initial access to the victim network.


Security Affairs
Cybersecurity researchers exposed new evasion techniques adopted by an advanced malware downloader called GuLoader. CrowdStrike researchers d a detailed multiple evasion techniques implemented by an advanced malware downloader called GuLoader (aka CloudEyE). GuLoader uses a polymorphic shellcode loader to avoid traditional security solutions, the experts mapped all embedded DJB2 hash values for every API used by the […]


Cyber Security News
Hackers may exploit LNK files to deliver malicious payloads by disguising them as legitimate shortcuts, and execution of malicious code.

SecurityWeek
Hackers, possibly Chinese cyberspies, have been using a new technique to install persistent backdoors in VMware ESXi hypervisors, giving them significant capabilities while making detection more difficult.


Security Affairs
Cybersecurity researchers exposed new evasion techniques adopted by an advanced malware downloader called GuLoader. CrowdStrike researchers d a detailed multiple evasion techniques implemented by an advanced malware downloader called GuLoader (aka CloudEyE). GuLoader uses a polymorphic shellcode loader to avoid traditional security solutions, the experts mapped all embedded DJB2 hash values for every API used by the […]


SecurityWeek
A new technique named TunnelVision allows attackers to bypass the VPN and redirect traffic through the local network.


Infosecurity News
Picus Security sees huge uptick in malware designed to detect and disrupt security tooling


The Hacker News
Cybercriminals are targeting healthcare, exploiting vulnerabilities for huge ransoms. It’s not just data at stake; it’s patient care.


SecurityWeek
YL Ventures leads a seed funding round for Miggo Security, a Tel Aviv startup working on application detection and response technology.


Bleeping Computer
VMware patched today a VMware ESXi zero-day vulnerability exploited by a Chinese-sponsored hacking group to backdoor Windows and Linux virtual machines and steal data.


CSO
AI will be is used for behavioral fraud categorization and turning known schemes into actionable anti-fraud strategies.


ZDNet
Federal agencies have until the end of fiscal year 2024 to "achieve specific zero trust security goals."


CyberSecurity Dive
The deal follows reported negotiations between Microsoft and the incident response specialist, which sold off its FireEye products business last year.


Security Affairs
Sobeys, the second-largest supermarket chain in Canada, was he victim of a ransomware attack conducted by the Black Basta gang. Sobeys Inc. is the second largest supermarket chain in Canada, the company operates over 1,500 stores operating across Canada under a variety of banners. It is a wholly-owned subsidiary of Empire Company Limited, a Canadian business conglomerate. During […]
Loading more articles....