

The Hacker News
XCSSET Malware Updates with Python 3 to Target macOS Monterey Users
Hackers have updated the XCSSET malware to add support for macOS Monterey by updating the source code components to Python 3.


The Hacker News
Hackers have updated the XCSSET malware to add support for macOS Monterey by updating the source code components to Python 3.


Security Affairs
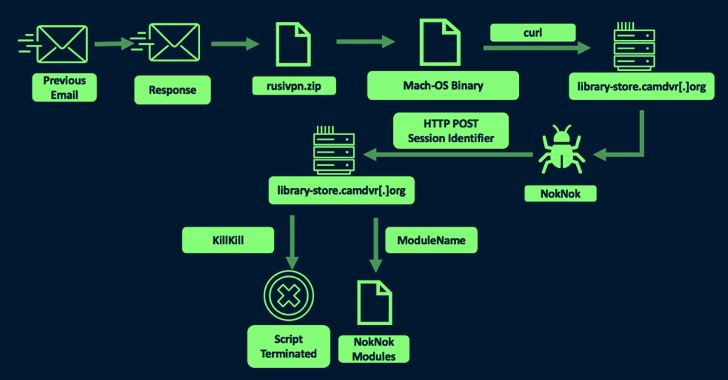
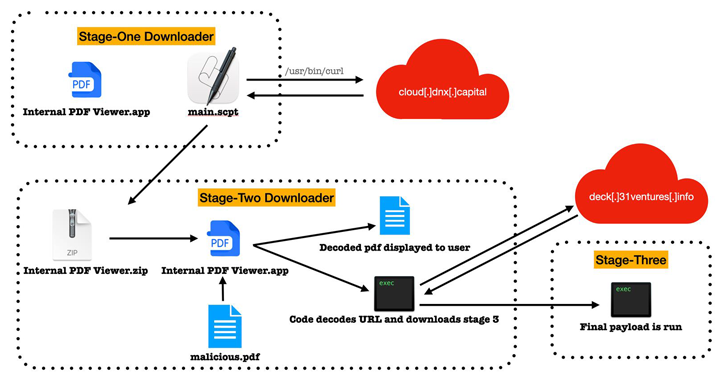
Researchers spotted a new version of the RustBucket Apple macOS malware that supports enhanced capabilities. Researchers from the Elastic Security Labs have spotted a new variant of the RustBucket Apple macOS malware. In April, the security firm Jamf observed the North Korea-linked BlueNoroff APT group using a new macOS malware, dubbed RustBucket. The group BlueNoroff is considered a group that […]


Cyber Security News
Over the past year, macOS users, particularly those in the cryptocurrency sector, have been increasingly targeted by infostealers.


The Hacker News
Malicious ads and fake websites are spreading dangerous malware that can steal your passwords, cryptocurrency, and other sensitive data.


Bleeping Computer
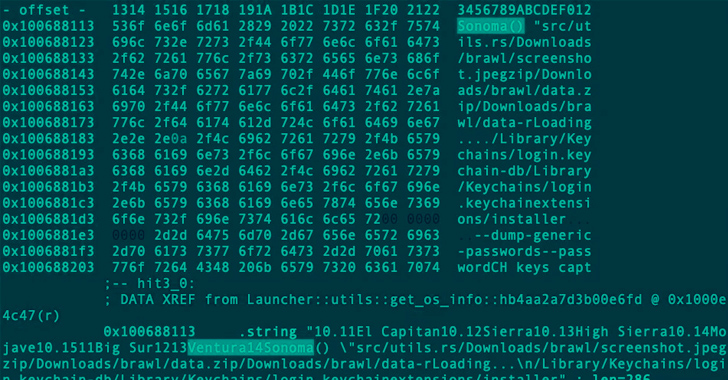
A new Mac malware named "Realst" is being used in a massive campaign targeting Apple computers, with some of its latest variants including support for macOS 14 Sonoma, which is still in development.


Bleeping Computer
A new Mac malware named "Realst" is being used in a massive campaign targeting Apple computers, with some of its latest variants including support for macOS 14 Sonoma, which is still in development.


Latest Hacking News
Heads up, gamers! If you receive access codes for seemingly lucrative blockchain games, beware! A new malware campaign targets gamers via fake blockchain games, delivering Redline stealer on Windows systems and Realst malware on Mac


The Hacker News
BlueNoroff, linked to North Korea's Lazarus Group, is behind a new macOS malware called ObjCShellz.


Infosecurity News
The average malware variant now utilizes 11 TTPs

The Hacker News
North Korea's BlueNoroff, part of Lazarus Group, has upgraded their macOS malware, Rustbucket, to avoid detection and persist longer.

The Hacker News
Iranian nation-state actor TA453 continues to evolve its tactics, deploying novel infection chains and malware to infiltrate both Windows and macOS.


Bleeping Computer
Multiple information stealers for the macOS platform have demonstrated the capability to evade detection even when security companies follow and report about new variants frequently.

The Hacker News
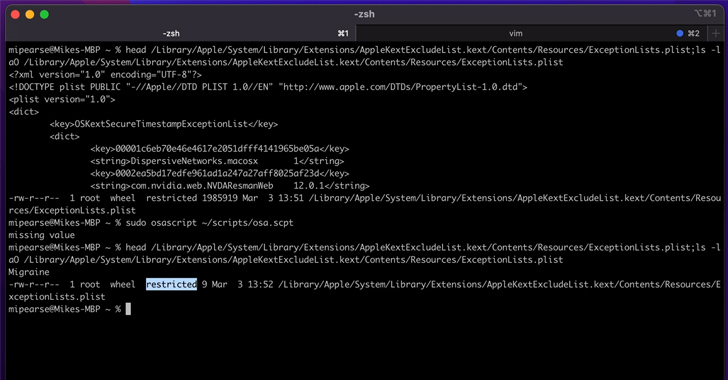
Microsoft reveals a macOS flaw, "Migraine," enabling root access bypass. Learn how threat actors could exploit this vulnerability.


Bleeping Computer
Apple has recently addressed a vulnerability that lets attackers with root privileges bypass System Integrity Protection (SIP) to install "undeletable" malware and access the victim's private data by circumventing Transparency, Consent, and Control (TCC) security checks.


The Hacker News
A Golang variant of Cobalt Strike, known as Geacon, is drawing attention in the cybersecurity world due to a rise in Geacon payloads.


Cyber Security News
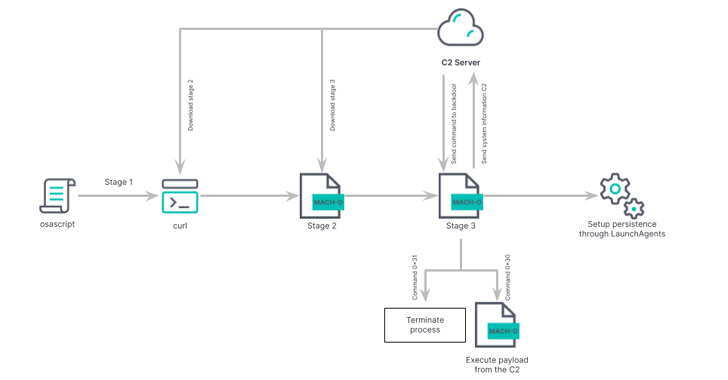
The new malware family has been tracked as "RustBucket," which downloads and executes several types of payloads.


Security Affairs
North Korea-linked APT group BlueNoroff (aka Lazarus) was spotted targeting Mac users with new RustBucket malware. Researchers from security firm Jamf observed the North Korea-linked BlueNoroff APT group using a new macOS malware, dubbed RustBucket, family in recent attacks. The group BlueNoroff is considered a group that operates under the control of the notorious North Korea-linked Lazarus APT group. The […]

The Hacker News
A new malware family called Realst is targeting Apple macOS systems, including macOS 14 Sonoma! Written in Rust programming language.


Cyber Security News
This variant of RUSTBUCKET, targets macOS systems, adds persistence capabilities not previously observed and, at the time of reporting, is undetected by VirusTotal signature engines.


The Hacker News
State-sponsored North Korean hackers are using a sneaky macOS malware called KANDYKORN to target crypto engineers via Discord.


Bleeping Computer
Geacon, a Go-based implementation of the beacon from the widely abused penetration testing suite Cobalt Strike, is being used more and more to target macOS devices.

DarkReading
A pervasive ClearFake campaign targeting Windows systems with Atomic Stealer has expanded its social engineering scams to MacOS users, analysts warn.


Security Affairs
Iran-linked APT group tracked TA453 has been linked to a new malware campaign targeting both Windows and macOS systems. The Iran-linked threat actor TA453 has been linked to a malware campaign that targets both Windows and macOS. TA453 is a nation-state actor that overlaps with activity tracked as Charming Kitten, PHOSPHORUS, and APT42. TA453 in May 2023 started […]


DarkReading
Emerging malware variants can evade various static-signature detection engines, including XProtect, as attackers rapidly evolve to challenge defense systems.


DarkReading
Threat actors seen using Go-language implementation of the red-teaming tool on Intel and Apple silicon-based macOS systems.


SecurityWeek
Threat Detection Report (2024) is based on analysis of almost 60,000 threats across 216 petabytes of telemetry from over 1,000 endpoints.


Security Affairs
Apple fixed a vulnerability discovered by Microsoft researchers that lets attackers with root privileges bypass System Integrity Protection (SIP). Researchers from Microsoft discovered a vulnerability, tracked as CVE-2023-32369 and dubbed Migraine, that can allow attackers with root privileges to bypass System Integrity Protection (SIP). System Integrity Protection (also referred to as rootless) is a macOS security feature […]

The Hacker News
BlueNoroff, a suspected subgroup of Lazarus Group, is now targeting Apple's macOS with new malware RustBucket, highlighting hackers' expanding toolset


SecurityWeek
A malware tactic dubbed ‘hunter-killer’ is growing and may become the standard approach for advanced attacks.


Naked Security
You’ll find fixes for numerous kernel-level code execution holes, including an 0-day vulnerability in many (though not all) versions.

CSO
Malware authors and cybercriminal groups are making sophisticated techniques practical for threat actors to use more widely, changing threat models.