
SecurityWeek
Firmware Security Company Eclypsium Raises $25 Million in Series B Funding
Firmware and hardware security company Eclypsium has raised $25 million in Series B funding, which brings the total invested in the firm to $50 million.

SecurityWeek
Firmware and hardware security company Eclypsium has raised $25 million in Series B funding, which brings the total invested in the firm to $50 million.


CSO
The guide offers supply chain risk intelligence for IT infrastructure including endpoints, servers, network devices, and cloud infrastructure products.


Infosecurity News
Eclypsium is working closely with Gigabyte to rectify insecure implementation of its app center

SecurityWeek
Eclypsium discovered that QCT servers are affected by the old BMC vulnerability identified as CVE-2019-6260 and Pantsdown.


Latest Hacking News
Researchers discovered multiple vulnerabilities in MegaRAC BMC firmware that riddled the security of numerous server brands. IT admins must ensure prompt updates to their servers to avoid potential exploits. MegaRAC BMC Vulnerabilities Eclypsium Research team has found


Security Affairs
Researchers discovered a suspected backdoor-like behavior within Gigabyte systems that exposes devices to compromise. Researchers from firmware security firm Eclypsium have discovered a suspected backdoor-like behavior within Gigabyte systems. The experts discovered that the firmware in Gigabyte systems drops and executes a Windows native executable during the system startup process. The executable is utilized for insecure […]


Security Affairs
Researchers discovered a flaw in three signed third-party UEFI boot loaders that allow bypass of the UEFI Secure Boot feature. Researchers from hardware security firm Eclypsium have discovered a vulnerability in three signed third-party Unified Extensible Firmware Interface (UEFI) boot loaders that can be exploited to bypass the UEFI Secure Boot feature. Secure Boot is […]


Ars Technica
Hackers can exploit them to gain full administrative control of internal devices.


SecurityWeek
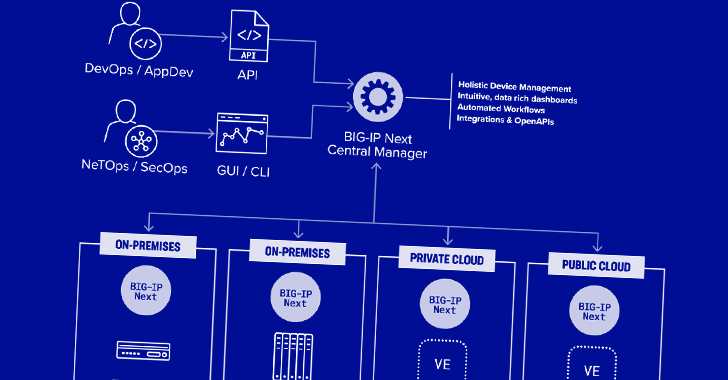
F5 has patched two potentially serious vulnerabilities in BIG-IP Next that could allow an attacker to take full control of a device.


Bleeping Computer
Security researchers have found a flaw in the Microsoft Windows Platform Binary Table (WPBT) that could be exploited in easy attacks to install rootkits on all Windows computers shipped since 2012.


CSO
Two high-risk vulnerabilities could be exploited to allow attackers to gain full administrative control on devices via leaked password hashes.


SecurityWeek
Two new vulnerabilities in AMI BMC can allow attackers to take control of systems and cause physical damage.


Ars Technica
Hidden code in many Gigabyte motherboards invisibly and insecurely downloads programs.


ThreatPost
The powerful devices leveraged by the Meris botnet have weaknesses that make them easy to exploit, yet complex for organizations to track and secure, researchers said.


Bleeping Computer
Approximately 300,000 MikroTik routers are vulnerable to critical vulnerabilities that malware botnets can exploit for cryptomining and DDoS attacks.

SecurityWeek
The Conti leaks show that the ransomware group has been working on firmware hacks targeting the Intel Management Engine (ME).


DarkReading
Five vulnerabilities in the baseboard management controller (BMC) software used by 15 major vendors could allow remote code execution if attackers gain network access.


Bleeping Computer
F5 has fixed two high-severity BIG-IP Next Central Manager vulnerabilities, which can be exploited to gain admin control and create rogue accounts on any managed assets.

Ars Technica
BMCs offer extraordinary control over cloud computers. So why hasn't Quanta patched?

SecurityWeek
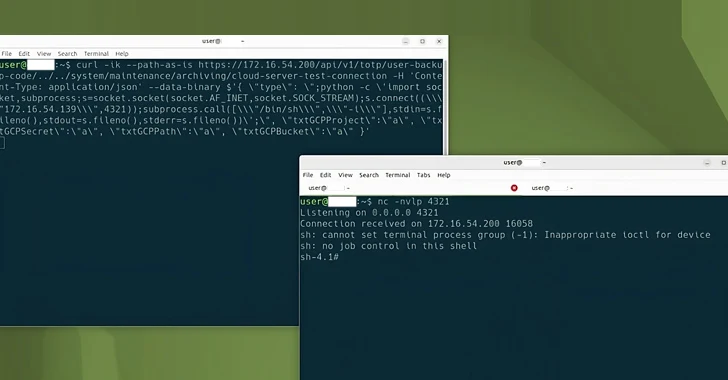
Eurosoft, New Horizon Datasys, and CryptoPro Secure Disk bootloaders, which are present on many devices made in the past 10 years, are affected by Secure Boot bypass vulnerabilities.


Bleeping Computer
Security researchers have found four major security vulnerabilities in the BIOSConnect feature of Dell SupportAssist, allowing attackers to remotely execute code within the BIOS of impacted devices.

SecurityWeek
Serious vulnerabilities in widely used AMI BMC can expose many data centers and cloud services to attacks, including remote control, malware delivery and damage.


Security Affairs
Two high-severity vulnerabilities in BIG-IP Next Central Manager can be exploited to gain admin control and create hidden accounts on any managed assets.


The Hacker News
Ivanti Pulse Secure runs on an outdated version of Linux, underscoring the challenges of keeping software supply chains secure.

Bleeping Computer
Researchers analyzing the leaked chats of the notorious Conti ransomware operation have discovered that teams inside the Russian cybercrime group were actively developing firmware hacks.


Bleeping Computer
Two new critical severity vulnerabilities have been discovered in the MegaRAC Baseboard Management Controller (BMC) software made by hardware and software company American Megatrends International.

The Hacker News
Researchers have discovered new UEFI Secure Boot bypass vulnerabilities affecting 3 Microsoft-signed boot loaders.

The Hacker News
Two more supply chain vulnerabilities disclosed in AMI MegaRAC BMC software, affecting multiple server brands.


The Record
Two new vulnerabilities have been found in a popular brand of baseboard software used in millions of devices worldwide.


SecurityWeek
A critical remote code execution vulnerability in Shim could allow attackers to take over vulnerable Linux systems.

The Hacker News
Two critical vulnerabilities have been discovered in F5 Next Central Manager that could grant attackers full admin control.

Bleeping Computer
A critical vulnerability in the Shim Linux bootloader enables attackers to execute code and take control of a target system before the kernel is loaded, bypassing existing security mechanisms.


The Hacker News
Gigabyte systems have been found with backdoor-like behavior, allowing unsecure Windows executable downloads via UEFI firmware.

CSO
Leaked Conti information show the ransomware gang likely completed a proof of concept to exploit Intel ME and rewrite its firmware.


Cyber Security News
F5 Big IP has been discovered with two critical vulnerabilities that could potentially allow a threat actor to take full administrative


Bleeping Computer
Three vulnerabilities in the American Megatrends MegaRAC Baseboard Management Controller (BMC) software impact server equipment used in many cloud service and data center providers.


Bleeping Computer
GIGABYTE has released firmware updates to fix security vulnerabilities in over 270 motherboards that could be exploited to install malware.


DarkReading
BlackLotus is the first in-the-wild malware to exploit a vulnerability in the Secure Boot process on Windows, and experts expect copycats and imminent increased activity.


Latest Hacking News
The news about Vitali Kremez’s unfortunate sudden death came in as a shock for the cybersecurity world. Reports reveal Vitali Kremez died in a scuba-diving accident. Vitali Kremez Died At 36 Recently, the U.S. Coast Guard confirmed


CSO
The newly discovered vulnerabilities could allow attackers to gain control of servers that use AMI's MegaRAC BMC firmware.


Security Affairs
The maintainers of Shim addressed six vulnerabilities, including a critical flaw that could potentially lead to remote code execution.


DarkReading
F5 customers should patch immediately, though even that won't protect them from every problem with their networked devices.


Latest Hacking News
Researchers have noticed a weird backdoor-like behavior with Gigabyte systems that risks devices’ security. The backdoor existence risks potential supply-chain attacks due to the release of pre-infected systems in the wild. The researchers suspect that


The Hacker News
Newly discovered supply chain vulnerabilities found in MegaRAC BMC software affect servers from many vendors and could allow remote code execution .


DarkReading
Conti threat actors are betting chipset firmware is updated less frequently than other software — and winning big, analysts say.


Security Affairs
The analysis of the internal chats of the Conti ransomware group revealed the gang was working on firmware attack techniques. The analysis of Conti group’s chats, which were leaked earlier this year, revealed that the ransomware gang has been working on firmware attack techniques. An attack against firmware could give threat actors significant powers, they are hard to […]

Bleeping Computer
Users may see a 0x800f0922 error when trying to install security update KB5012170 on the currently supported Windows operating system for consumers and the enterprise-class Server version.

Bleeping Computer
Some signed third-party bootloaders for the Unified Extensible Firmware Interface (UEFI) used by Windows could allow attackers to execute unauthorized code in an early stage of the boot process, before the operating system loads.


The Hacker News
A critical vulnerability (CVE-2023-40547) has been found in the shim bootloader, leaving millions of Linux systems vulnerable to attack.

Cyber Security News
Shim is maintained by Red Hat and used in almost all Linux distributions that support secure boot including Debian, Ubuntu, SUSE, and many others.


The Cyber Express
Security researchers have revealed new critical vulnerabilities in F5’s Next Central Manager, posing severe risks to organizational cybersecurity. These Next


Ars Technica
BMCs give near-total control over entire fleets of servers. What happens when they're hacked?

CSO
Tests show that deploying malware in a persistent manner on load balancer firmware is within reach of less sophisticated attackers.


SC Magazine
Security pros say teams need to patch right away because attackers can leverage the bug to gain control of the entire boot process.


Naked Security
It’s a backdoor, Jim, but not as we know it… here’s a sober look at this issue.

The Hacker News
Five Eyes intelligence alliance issued a cybersecurity advisory concerning cyber threat actors exploiting known vulnerabilities in Ivanti.

DarkReading
However, not everyone agrees with the NVD's assessment of CVE-2023-40547 being a near-maximum severity bug.


The Hacker News
Quanta Cloud Technology (QCT) servers have been identified as vulnerable to the severe "Pantsdown" Baseboard Management Controller (BMC) flaw.


The Hacker News
An analysis of leaked chats from the notorious Conti ransomware group has now revealed that the syndicate has been working on a set of firmware attack


Security Affairs
Lenovo fixed two high-severity flaws impacting various laptop models that could allow an attacker to deactivate UEFI Secure Boot. Lenovo has released security updates to address a couple of high-severity vulnerabilities impacting various ThinkBook, IdeaPad, and Yoga laptop models. An attacker can exploit the flaws to disable UEFI Secure Boot. Secure Boot is a security feature […]


Bleeping Computer
A malware campaign is using fake OnlyFans content and adult lures to install a remote access trojan known as 'DcRAT,' allowing threat actors to steal data and credentials or deploy ransomware on the infected device.

The Hacker News
New security flaws in AMI MegaRAC BMC software have been disclosed, putting vulnerable servers at risk. Attackers could remotely take control.


CSO
Two research groups demonstrate PC firmware vulnerabilities that are difficult to mitigate and likely to be exploited in the wild.


The Record
USB-over-network components have been plagued over the past two years by an ever-increasing number of vulnerabilities, and in new research published today, researchers at SentinelOne said they discovered new issues in the USB-over-network component of home and office (SOHO) routers.


Bleeping Computer
A threat actor is selling on hacking forums what they claim to be a new UEFI bootkit named BlackLotus, a malicious tool with capabilities usually linked to state-backed threat groups.


Ars Technica
Hackers can exploit vulnerabilities to install malicious firmware that survives reboots.


Bleeping Computer
Ransomware gangs continue to evolve their operations as victims refuse to pay ransoms due to sanctions or other reasons.

Ars Technica
Research is largely theoretical but exposes an overlooked security issue.

Bleeping Computer
The TrickBot trojan has just added one more trick up its sleeve, now using vulnerable IoT (internet of things) devices like modem routers as proxies for its C2 (command and control) server communication.


Security Affairs
ESET discovered a stealthy Unified Extensible Firmware Interface (UEFI) bootkit dubbed BlackLotus that is able to bypass the Secure Boot on Windows 11. Researchers from ESET discovered a new stealthy Unified Extensible Firmware Interface (UEFI) bootkit, named BlackLotus, that is able to bypass Secure Boot on Windows 11. Secure Boot is a security feature of the […]


Computerworld
To update or not to update, for Windows users that is the monthly question. And with last month's KB5012170, you better get the answer right.


Ars Technica
Buffer overflow in bootloader shim allows attackers to run code each time devices boot up.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.