

DataBreaches
[FLASH] #Conti Officially DisCONTInued
As seen on Twitter: #Conti Officially DisCONTInued Today the official website of Conti #Ransomware was shut down, marking the end of this notorious...


DataBreaches
As seen on Twitter: #Conti Officially DisCONTInued Today the official website of Conti #Ransomware was shut down, marking the end of this notorious...


DataBreaches
TLP: White Report: 202203101700 March 10, 2022 Conti Ransomware (Update) Executive Summary Conti is a ransomware group that has aggressively targeted...

SecurityWeek
The Ukrainian hacker who started leaking files stolen from the Conti gang has also leaked the ransomware’s source code.


DataBreaches
It almost felt like Christmas came early in a winter of despair. As noted yesterday, a Conti member who appears furious with Conti for its statement supporting...


DataBreaches
Catalin Cimpanu reports: A disgruntled member of the Conti ransomware program has leaked today the manuals and technical guides used by the Conti gang to train...


DataBreaches
Seems to be a lot of Conti-related analyses this week, as well as the $10 million reward offered by the government for information leadings to Conti’s...


DataBreaches
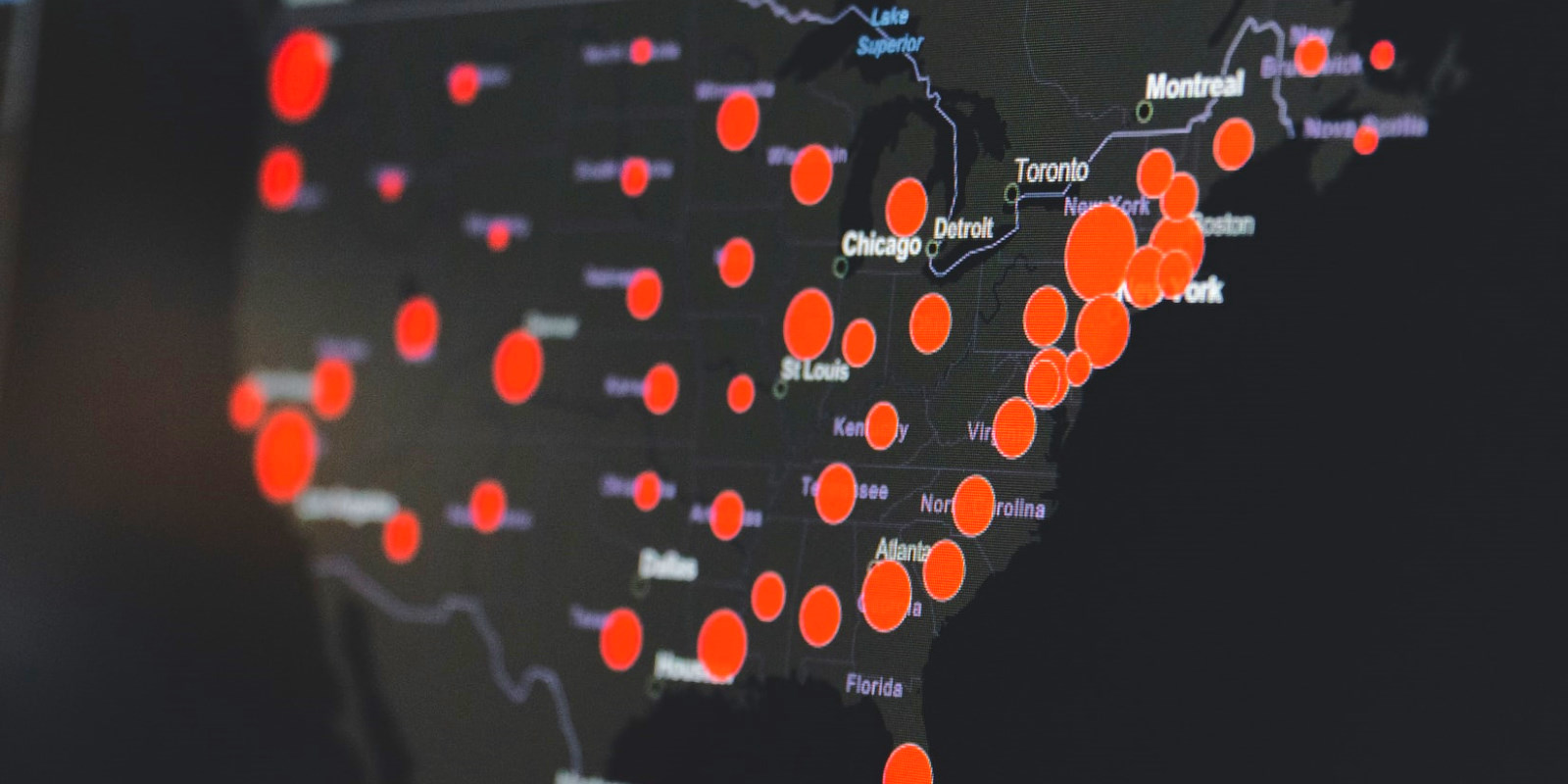
The FBI has issued a Flash Alert about Conti. Summary The FBI identified at least 16 Conti ransomware attacks targeting US healthcare and first responder...


DataBreaches
PRODAFT Threat Intelligence (PTI) Team has obtained valuable insights on the inner workings of the Conti ransomware group. The PTI team accessed Conti’s...


ZDNet
The individual responsible is targeting Conti after the group announced its loyalty to Russia during the invasion of Ukraine.


CyberNews
The official website for Conti ransomware was shut down, signaling that the notorious group is disbanding.

SecurityWeek
Conti ransomware activity has surged despite the recent exposure of the group’s operations.


Bleeping Computer
A decryption tool for a modified version of the Conti ransomware could help hundreds of victims recover their files for free.

SecurityWeek
Royal ransomware appears to be operated by seasoned threat actors who used to be part of Conti Team One.


Security Affairs
Kaspersky released a new version of the decryptor for the Conti ransomware that is based on the previously leaked source code of the malware. Kaspersky has published a new version of a decryption tool for the Conti ransomware based on previously leaked source code for the Conti ransomware. In March 2022, a Ukrainian security researcher […]


Security Affairs
A Ukrainian researcher leaked the source for the Conti ransomware and components for the control panels. Recently a Ukrainian researcher leaked 60,694 messages internal chat messages belonging to the Conti ransomware operation after the announcement of the group of its support to Russia. He was able to access the database XMPP chat server of the Conti group. Clearly, the […]


Bleeping Computer
Photography and personalized photo giant Shutterfly has suffered a Conti ransomware attack that allegedly encrypted thousands of devices and stole corporate data.


DarkReading
Conti threat actors are betting chipset firmware is updated less frequently than other software — and winning big, analysts say.


DataBreaches
Catalin Cimpanu reports: The Conti ransomware gang has been linked to an attack on Delta Electronics, a Taiwanese electronics manufacturing company and a major...


Bleeping Computer
The Costa Rican President Rodrigo Chaves has declared a national emergency following cyber attacks from Conti ransomware group. BleepingComputer also observed Conti published most of the 672 GB dump that appears to contain data belonging to the Costa Rican government agencies.


Bleeping Computer
The Australian Cyber Security Centre (ACSC) says Conti ransomware attacks have targeted multiple Australian organizations from various industry verticals since November.


DataBreaches
Lawrence Abrams reports: Photography and personalized photo giant Shutterfly has suffered a Conti ransomware attack that allegedly encrypted thousands of...


ThreatPost
Conti has become the first professional-grade, sophisticated ransomware group to weaponize Log4j2, now with a full attack chain.


Bleeping Computer
A disgruntled Conti affiliate has leaked the gang's training material when conducting attacks, including information about one of the ransomware's operators.


DataBreaches
Ionut Ilascu reports: A decryption tool for a modified version of the Conti ransomware could help hundreds of victims recover their files for free. The utility...


Infosecurity News
Ivanti observed a 7.6% rise in the number of vulnerabilities tied to ransomware, most of which were exploited by Conti


ThreatPost
The decryptor spilled by ContiLeaks won’t work with recent victims. Conti couldn't care less: It's still operating just fine. Still, the dump is a bouquet’s worth of intel.


Security Affairs
Conti ransomware gang continues to target organizations worldwide despite the massive data leak has shed light on its operations. Researchers from Secureworks state that the Conti ransomware gang, tracked as a Russia-based threat actor Gold Ulrick, continues to operate despite the recent data leak on its internal activities. The group’s activity returned to the levels […]


Security Affairs
The Conti ransomware group takes over TrickBot malware operation and plans to replace it with BazarBackdoor malware. TrickBot operation has arrived at the end of the journey, according to AdvIntel some of its top members move under the Conti ransomware gang, which is planning to replace the popular banking Trojan with the stealthier BazarBackdoor. TrickBot is […]


DataBreaches
I-SEC is one of the main providers in the field of aviation security checks according to §5 LuftSiG (German Aviation Security Law) in Frankfurt. Conti...


The Hacker News
Researchers analyze dozens of communications between Conti and Hive ransomware operators and victims.


Bleeping Computer
The Conti ransomware gang is hacking into Microsoft Exchange servers and breaching corporate networks using recently disclosed ProxyShell vulnerability exploits.

SecurityWeek
The Conti leaks show that the ransomware group has been working on firmware hacks targeting the Intel Management Engine (ME).

Bleeping Computer
Researchers analyzing the leaked chats of the notorious Conti ransomware operation have discovered that teams inside the Russian cybercrime group were actively developing firmware hacks.

The Hacker News
After siding with Russia, Conti Ransomware Gang's internal chats were published online.


Security Affairs
A Ukrainian security researcher has leaked more source code from the Conti ransomware operation to protest the gang’s position on the conflict. Hacker leaked a new version of the Conti ransomware source code on Twitter as retaliation of the gang’s support to Russia The attack against the Conti ransomware and the data leak is retaliation […]


Bleeping Computer
KP Snacks, a major producer of popular British snacks has been hit by the Conti ransomware group affecting distribution to leading supermarkets.


Bleeping Computer
Online retail and photography manufacturing platform Shutterfly has disclosed a data breach that exposed employee information after threat actors stole data during a Conti ransomware attack.


DataBreaches
Lawrence Abrams reports: The notorious Conti ransomware gang has officially shut down their operation, with infrastructure taken offline and team leaders told...

SecurityWeek
A dozen companies have been targeted by the new Black Basta ransomware and researchers say there may be some links to Conti.


DataBreaches
Alert (AA21-265A): Conti Ransomware The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) have observed the...


DarkReading
A new group, Monti, appears to have used leaked Conti code, TTPs, and infrastructure approaches to launch its own ransomware campaign.

Bleeping Computer
Training material used by Conti ransomware affiliates was leaked online this month, allowing an inside look at how attackers abuse legitimate software seek out cyber insurance policies.

SecurityWeek
The Conti ransomware operation has seen some significant organizational structure changes after the brand became toxic due to its affiliation with the Russian government.

SecurityWeek
Experts say the notorious TrickBot malware has reached its limits, but its development team appears to have been “acquired” by the Conti ransomware gang.


The Hacker News
Conti ransomware gang has shut down its infrastructure in favor of migrating its criminal activities to smaller cybercrime groups.


Bleeping Computer
The notorious Conti ransomware gang has officially shut down their operation, with infrastructure taken offline and team leaders told that the brand is no more.


Bleeping Computer
A Ukrainian researcher continues to deal devastating blows to the Conti ransomware operation, leaking further internal conversations, as well as the source for their ransomware, administrative panels, and more.

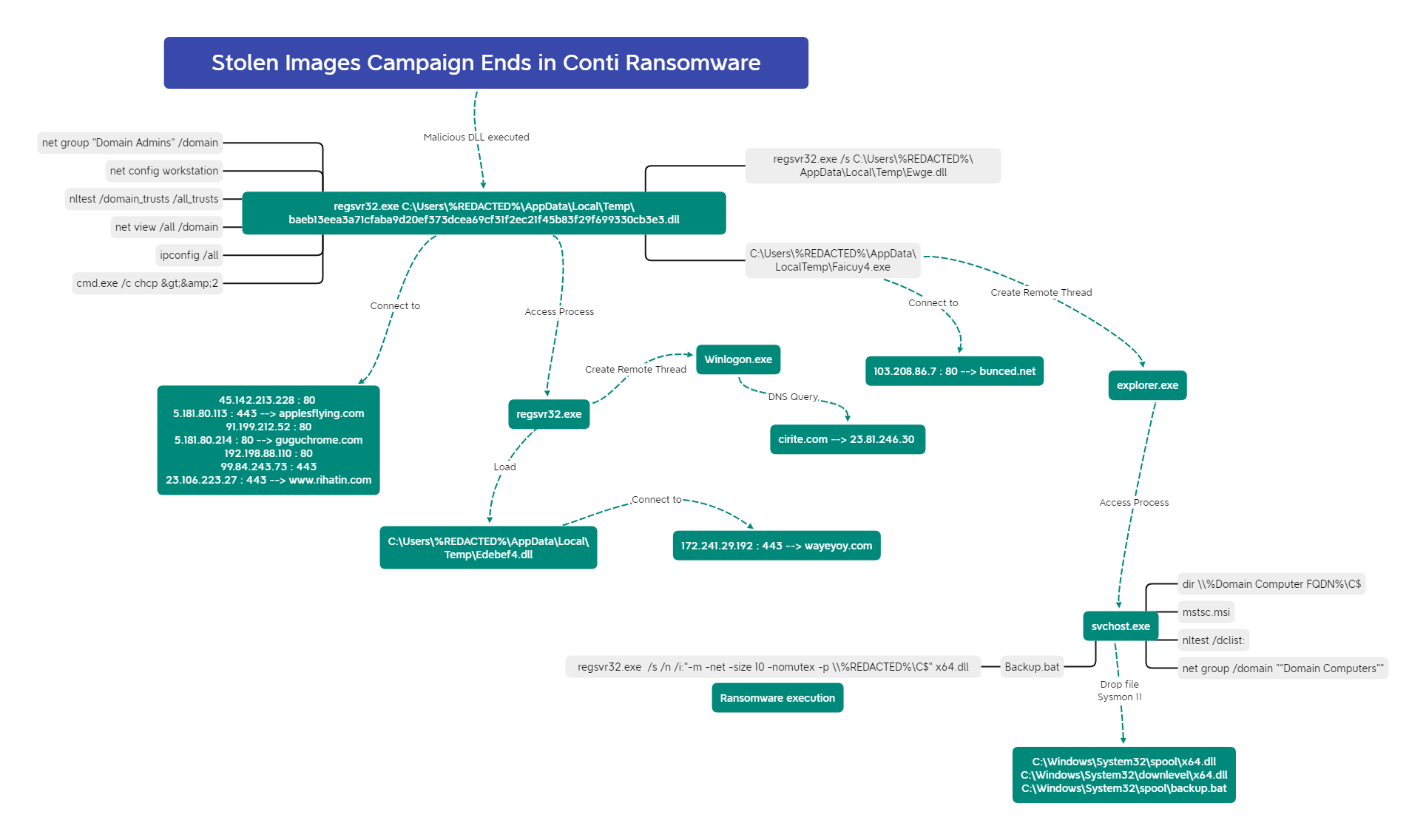
The DFIR Report
In this intrusion from December 2021, the threat actors utilized IcedID as the initial access vector to eventually deploy Conti Ransomware.

SecurityWeek
A Ukrainian security researcher has leaked the source code of a newer version of the Conti ransomware after the cybercrime gang expressed support for Russia.

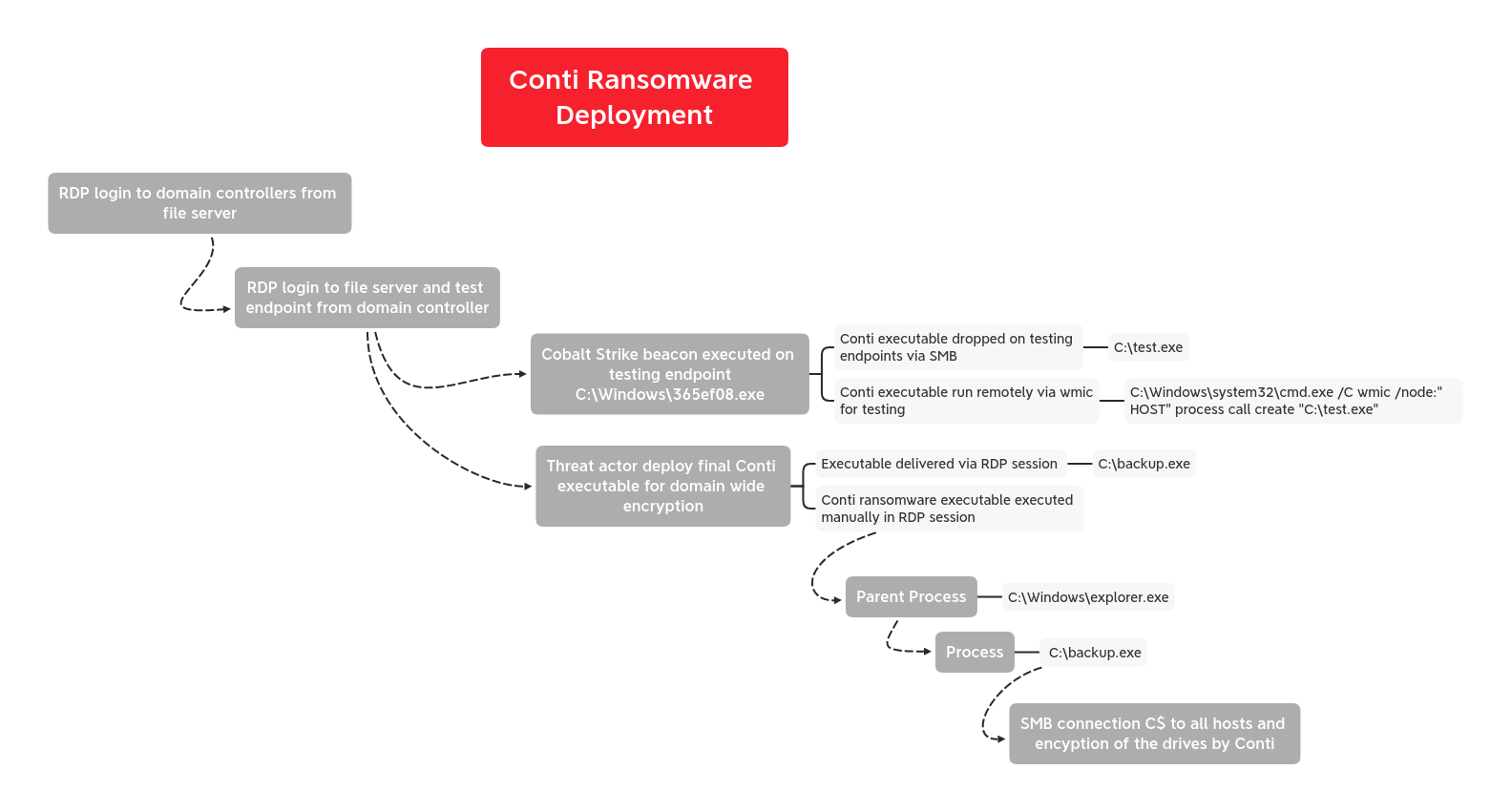
The DFIR Report
In July we witnessed a BazarLoader campaign that deployed Cobalt Strike and ended with domain wide encryption using Conti ransomware.


Bleeping Computer
An angry member of the Conti ransomware operation has leaked over 60,000 private messages after the gang sided with Russia over the invasion of Ukraine.


Bleeping Computer
The Conti ransomware gang failed to encrypt the systems of Ireland's Department of Health (DoH) despite breaching its network and dropping Cobalt Strike beacons to deploy their malware across the network.

Bleeping Computer
Almost a month after a disgruntled Conti affiliate leaked the gang's attack playbook, security researchers shared a translated variant that clarifies on any misinterpretation caused by automated translation.


Security Affairs
Some members of the Conti ransomware gang were involved in financially motivated attacks targeting Ukraine from April to August 2022. Researchers from Google’s Threat Analysis Group (TAG) reported that some former members of the Conti cybercrime group were involved in five different campaigns targeting Ukraine between April and August 2022. The activities overlap with operations […]


DataBreaches
Dina Temple-Raston and Sean Powers report: It has been a busy spring for the Russian-speaking ransomware group Conti. After an unprecedented leak of...


Cyber Security News
Cyber threat actors that were responsible for over 1000 recorded conti ransomware attacks remain active still. Tricot and Cobalt Strike are the two most significant attack vectors.


DataBreaches
Lawrence Abrams points us to some interesting findings by Advanced Intel, who pored through the Conti manuals and materials recently dumped by a disgruntled...


The Hacker News
Google uncovers the "initial access broker" that appears to be working with the Russian Conti ransomware hacking gang.


Bleeping Computer
A Ukrainian security researcher has leaked newer malware source code from the Conti ransomware operation in revenge for the cybercriminals siding with Russia on the invasion of Ukraine.


Bleeping Computer
Google says some former Conti ransomware gang members, now part of a threat group tracked as UAC-0098, are targeting Ukrainian organizations and European non-governmental organizations (NGOs).


Bleeping Computer
Google says some former Conti cybercrime gang members, now part of a threat group tracked as UAC-0098, are targeting Ukrainian organizations and European non-governmental organizations (NGOs).


Bleeping Computer
It started as a slow ransomware news week but slowly picked up pace with the Department of Justice announcing indictments on TrickBot and Conti operations members.


The Hacker News
A trio of offshoots of Conti cybercrime gang have resorted to "BazarCall" phishing attacks as an initial entry point.


Bleeping Computer
The LockBit ransomware gang has again started using encryptors based on other operations, this time switching to one based on the leaked source code for the Conti ransomware.


Security Affairs
The Conti ransomware gang shut down its operation, and some of its administrators announced a branding of the gang. Advanced Intel researcher Yelisey Boguslavskiy announced the that Conti Ransomware gang shuts its infrastructure and some of its administrators announced a rebranding of the popular RaaS operation. The news was reported by BleepingComputer that citing Boguslavskiy confirmed […]


DataBreaches
Catalin Cimpanu reports: A member of the Conti ransomware group, believed to be Ukrainian of origin, has leaked the gang’s internal chats after the group’s...


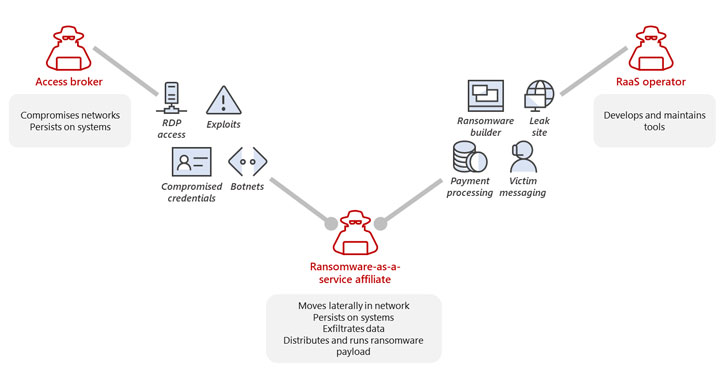
Security Affairs
Google’s Threat Analysis Group (TAG) uncovered a new initial access broker, named Exotic Lily, that is closely affiliated with the Conti ransomware gang. Google’s Threat Analysis Group (TAG) researchers linked a new initial access broker, named Exotic Lily, to the Conti ransomware operation. Initial access brokers play an essential role in the cybercrime ecosystem, they provide access to previously […]


Bleeping Computer
Conti ransomware operation is using the critical Log4Shell exploit to gain rapid access to internal VMware vCenter Server instances and encrypt virtual machines.

SecurityWeek
The US has been offering significant rewards for information on Conti ransomware leaders and affiliates, and the Department of State has now even shared a photo of a suspect.


CSO
A ransomware campaign linked to the ostensibly defunct Conti malware group has targeted mostly US businesses, in a costly series of attacks.

Bleeping Computer
The USA and the United Kingdom have sanctioned eleven Russian nationals associated with the TrickBot and Conti ransomware cybercrime operations.

Bleeping Computer
At least three groups split from the Conti ransomware operation have adopted BazarCall phishing tactics as the primary method to gain initial access to a victim's network.


Bleeping Computer
RR Donnelly has confirmed that threat actors stole data in a December cyberattack, confirmed by BleepingComputer to be a Conti ransomware attack.

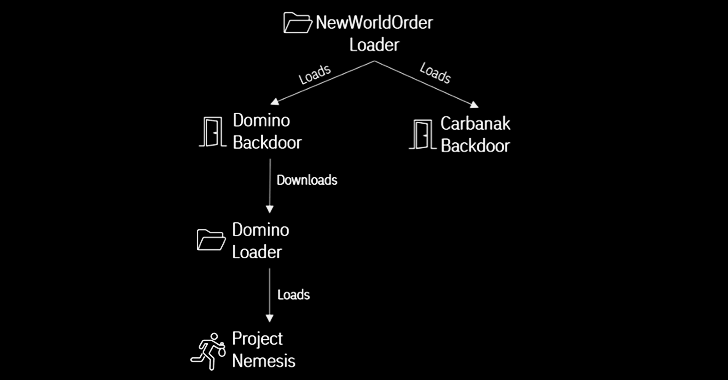
The Hacker News
Cybercriminal syndicates FIN7 and ex-Conti members have teamed up to launch Domino malware attacks.


Bleeping Computer
CISA, the Federal Bureau of Investigation (FBI), and the National Security Agency (NSA) warned today of an increased number of Conti ransomware attacks targeting US organizations.


Bleeping Computer
Security researchers analyzing the activity of the recently emerged 3AM ransomware operation uncovered close connections with infamous groups, such as the Conti syndicate and the Royal ransomware gang.


Bleeping Computer
Google's Threat Analysis Group has exposed the operations of a threat actor group dubbed "EXOTIC LILY," an initial access broker linked to the Conti and Diavol ransomware operations.


DataBreaches
Lawrence Abrams reports: The Conti ransomware operation has finally shut down its last public-facing infrastructure, consisting of two Tor servers used to leak...

The Hacker News
Russian-speaking Conti ransomware gang has threatened to overthrow the newly elected government of Costa Rica with a cyberattack.


Security Affairs
Conti ransomware gang claimed responsibility for a ransomware attack that hit the government infrastructure of Costa Rica. Last week a ransomware attack has crippled the government infrastructure of Costa Rica causing chaos. The Conti ransomware gang claimed responsibility for the attack, while the Costa Rican government refused to pay a ransom. “The Costa Rican state […]


Bleeping Computer
After four years of activity and numerous takedown attempts, the death knell of TrickBot has sounded as its top members move under new management, the Conti ransomware syndicate, who plan to replace it with the stealthier BazarBackdoor malware.


Security Affairs
The U.S. State Department announced a $10 million reward for information related to five individuals associated with the Conti ransomware gang. The U.S. State Department announced a $10 million reward for information on five prominent members of the Conti ransomware gang. The government will also reward people that will provide details about Conti and its affiliated groups TrickBot and Wizard […]

Bleeping Computer
The Federal Bureau of Investigation (FBI) says the Conti ransomware gang has attempted to breach the networks of over a dozen US healthcare and first responder organizations.


Bleeping Computer
American automotive tools manufacturer Snap-on announced a data breach exposing associate and franchisee data after the Conti ransomware gang began leaking the company's data in March.

SecurityWeek
Tens of thousands of messages exchanged between Conti ransomware operators have been leaked online after the cybercrime group expressed support for Russia as it invaded Ukraine.

SecurityWeek
The Conti ransomware gang has claimed responsibility for a cyberattack that forced wind turbine giant Nordex to shut down internal systems on March 31.


Security Affairs
The Conti ransomware gang is threatening to ‘overthrow’ the new government of Costa Rica after last month’s attack. Last month, the Conti ransomware gang claimed responsibility for the attack on Costa Rica government infrastructure after that the government refused to pay a ransom. “The Costa Rican state will not pay anything to these cybercriminals.” said […]


The Hacker News
U.S. State Department is offering a reward of up to $10 million for information leading to the identification of Conti Ransomware gang.


DataBreaches
A story by Stephen Breen inThe Irish Sun yesterday included reference to an update on the HSE attack by Conti: Earlier this month, cops seized several websites...


Bleeping Computer
JVCKenwood has suffered a Conti ransomware attack where the threat actors claim to have stolen 1.7 TB of data and are demanding a $7 million ransom.

The Hacker News
Google found that some former members of the Conti cybercrime group repurposed their hacking techniques to target Ukraine in financial attacks.


Trend Micro
We compare the targeting and business models of the Conti and LockBit ransomware groups using data analysis approaches. This will be presented in full at the 34th Annual FIRST Conference on June 27, 2022.

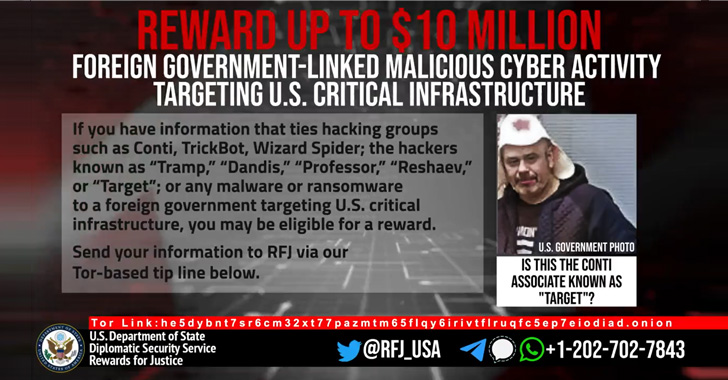
The Hacker News
U.S. State Department on Thursday announced a $10 million reward for information related to five individuals associated with the Conti ransomware.

SecurityWeek
The U.S. government has reissued an alert warning organizations about Conti ransomware attacks as the cybercrime group deals with the recent leaks.


Infosecurity News
These new sanctions follow a first wave in February 2023, where seven Russians involved with Trickbot and Conti were also sanctioned


DataBreaches
DataBreaches previously reported on the situation in Costa Rica, where the government has declared a national emergency following a ransomware attack by Conti...


Bleeping Computer
This week's biggest story is the massive data leak from the Conti ransomware operation, including over 160,000 internal messages between members and source code for the ransomware and TrickBot operation.


The Hacker News
Gold Ulrick Hackers Still in Action Despite Massive Conti Ransomware Leak | Read latest news headlines on latest news and technical coverage on cybersecurity, infosec and hacking.


Bleeping Computer
SAC Wireless, a US-based and independently-operating Nokia company subsidiary, has disclosed a data breach following a ransomware attack where Conti operators were able to successfully breach its network, steal data, and encrypt systems.


The Hacker News
An analysis of leaked chats from the notorious Conti ransomware group has now revealed that the syndicate has been working on a set of firmware attack
Loading more articles....