

Infosecurity News
Infosecurity Europe Keynote: Building Strong Teams and Driving Change
Join Claire Williams at Infosecurity Europe to learn how F1 leadership strategies can inspire cybersecurity leaders


Infosecurity News
Join Claire Williams at Infosecurity Europe to learn how F1 leadership strategies can inspire cybersecurity leaders


Bleeping Computer
Hackers hijacked the official contact email for the Belgian Grand Prix event and used it to lure fans to a fake website promising a €50 gift voucher.


Ars Technica
Williams team leader may only be shocked because he hasn't worked IT.


Trend Micro
Heading to AWS re:Invent 2023? Don’t miss out on our talk with Melinda Marks, ESG Practice Director for Cybersecurity, about cloud detection and response (CDR) and what’s trending in cloud security.


Cyber Security News
Language models like CodeBERT, GraphCodeBERT, and CodeT5 can identify, explain, assess, and suggest patches for vulnerabilities.


Trend Micro
We observed and tracked the advanced persistent threat (APT) APT34 group with a new malware variant accompanying a phishing attack comparatively similar to the SideTwist backdoor malware. Following the campaign, the group abused a fake license registration form of an African government agency to target a victim in Saudi Arabia.


CSO
Generative AI benchmark evaluates the ability of large language models to identify and score cybersecurity threats within cloud logs and telemetries.


Cyber Security News
The malware generates malicious network behavior, often hiding it in HTTP traffic to avoid detection. So, cyber security detecting malicious traffic.

Cyber Security News
Rekoobe is a backdoor malware that targets vulnerable Linux servers known to be used by the Chinese APT31.


ZDNet
For Formula 1 teams, the cybersecurity race has no finish line.


DarkReading
CISOs and cybersecurity teams will play a key role in hardening artificial intelligence and machine learning systems.


DataBreaches
Not only was Ferrari dealing with grid penalty and car development problems with their F1 car this past week, but it now seems they were also dealing with a...


CSO
Intune Suite will streamline endpoint management with added features for controlled and secure access.


Trend Micro
Trend Micro researchers discovered a new ransomware that abuses the APIs of a legitimate tool called Everything, a Windows filename search engine developed by Voidtools that offers quick searching and real-time updates for minimal resource usage.

SecurityWeek
Thirty-nine cybersecurity-related M&A deals were announced in September 2022.


Naked Security
There’s many a slip ‘twixt the cup and the lip. Or at least between the TOC and the TOU…

Ars Technica
In the finale of our experiment, we look at how the low/no-code tools performed.

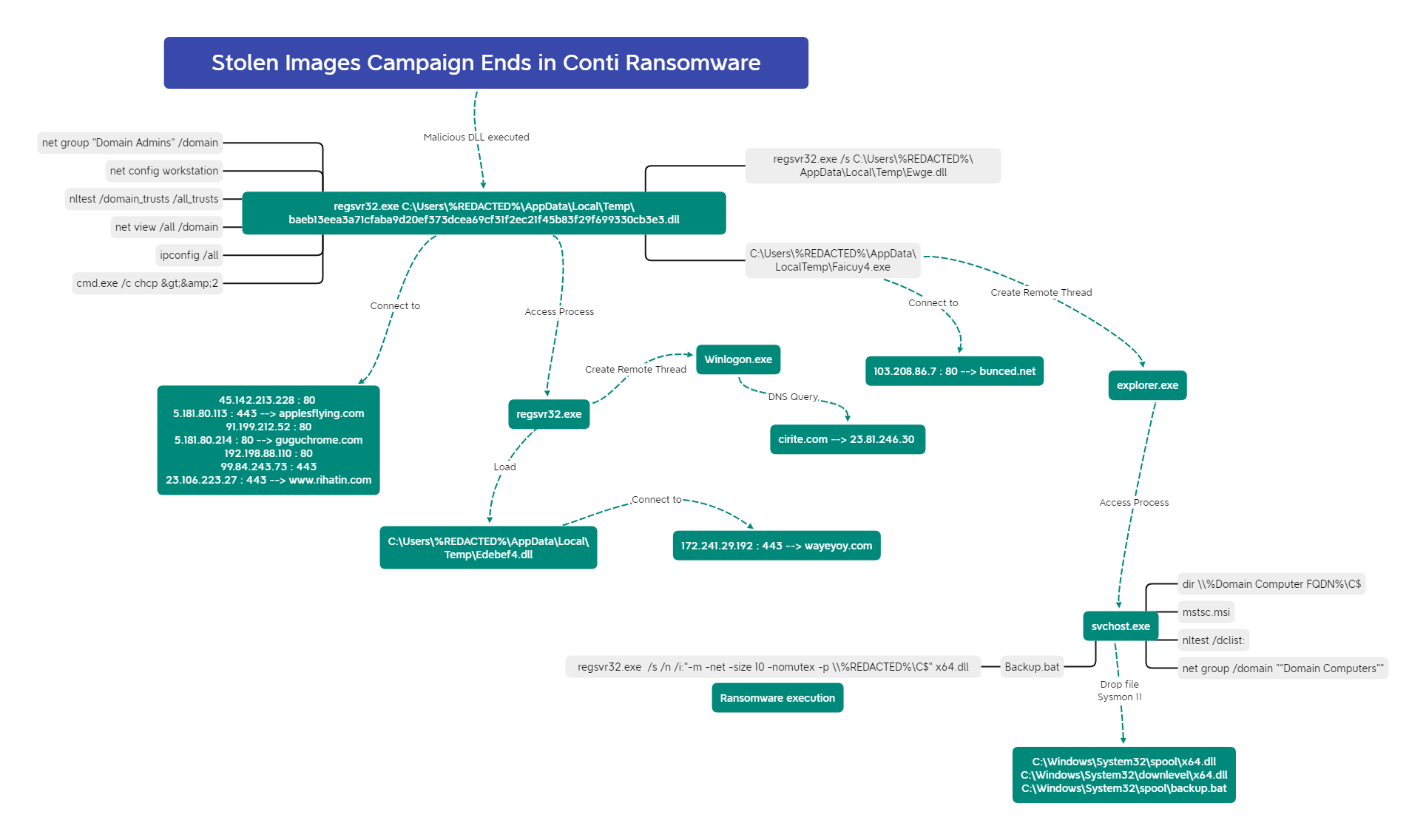
The DFIR Report
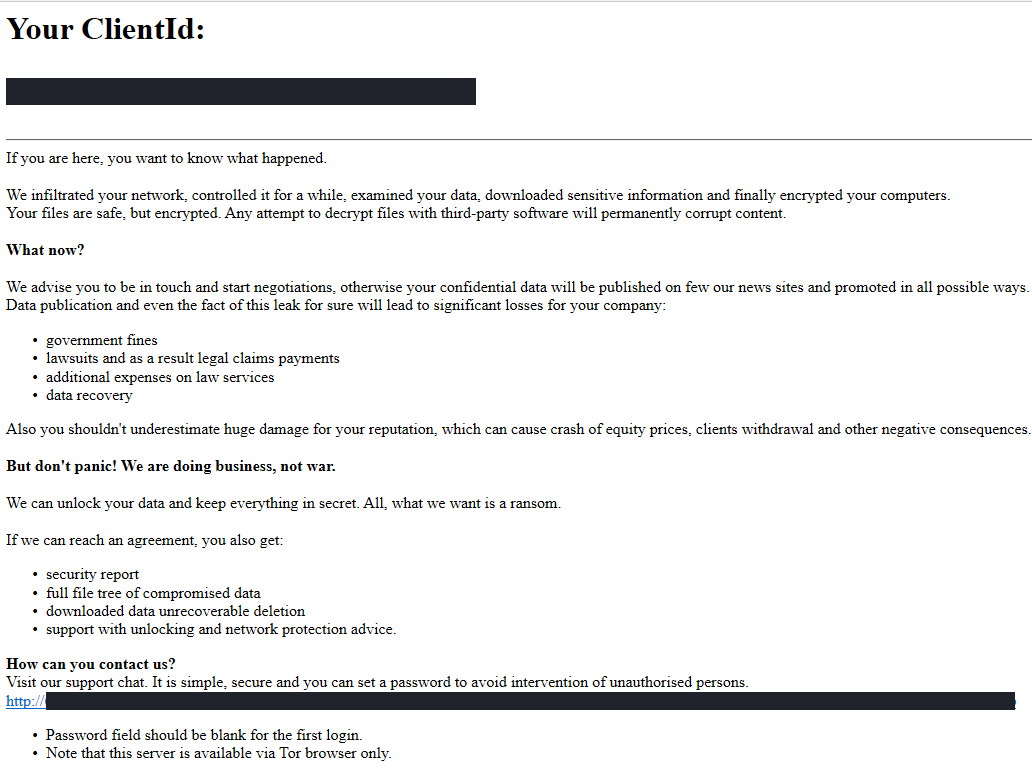
In this intrusion from December 2021, the threat actors utilized IcedID as the initial access vector to eventually deploy Conti Ransomware.


Bleeping Computer
Microsoft has released Windows 10 KB5011487 and KB5011485 cumulative updates for versions 1909, 21H2, version 21H1, and version 20H2 to fix security vulnerabilities and resolve bugs.

Bleeping Computer
Microsoft has released the optional KB5010414 cumulative update preview for Windows 11, with highly anticipated taskbar enhancements and fixes for 19 issues, including printing and driver problems.


Bleeping Computer
Microsoft has released the optional KB5010415 Preview cumulative update for Windows 10 20H2, Windows 10 21H1, and Windows 10 21H2.


Bleeping Computer
The Federal Bureau of Investigation (FBI) has released technical details and indicators of compromise associated with Lockbit ransomware attacks in a new flash alert published this Friday.

The DFIR Report
In this intrusion, we observed the threat actors use multiple DLL Beacons that would call out to different Cobalt Strike C2 channels. The threat actors used batch scripts during the intrusion for a number of purposes, primarily to disable antivirus programs and execute payloads.


Bleeping Computer
Vulnerabilities collectively referred to as BrakTooth are affecting Bluetooth stacks implemented on system-on-a-chip (SoC) circuits from over a dozen vendors.