

Bleeping Computer
Datadog rotates RPM signing key exposed in CircleCI hack
Cloud security firm Datadog says that one of its RPM GPG signing keys and its passphrase have been exposed during a recent CircleCI security breach.


Bleeping Computer
Cloud security firm Datadog says that one of its RPM GPG signing keys and its passphrase have been exposed during a recent CircleCI security breach.

SecurityWeek
A cross-tenant vulnerability in AWS abused the AppSync service to provide access to resources within a target organization’s account.

SecurityWeek
CircleCI says its internal systems were breached after an engineer’s laptop was infected with information stealer.


The Hacker News
Researchers have reported a cross-tenant vulnerability in Amazon Web Services (AWS) that exploits AWS AppSync.

SecurityWeek
Fifteen cybersecurity-related M&A deals have been announced in the first half of May 2022.

SecurityWeek
Twenty-one cybersecurity-related merger and acquisition (M&A) deals were announced in the first half of November 2022.


Security Affairs
Amazon Web Services (AWS) fixed a cross-tenant vulnerability that could have allowed attackers to gain unauthorized access to resources. Amazon Web Services (AWS) has addressed a cross-tenant confused deputy problem in its platform that could have allowed threat actors to gain unauthorized access to resources. The problem was reported to the company by researchers from […]


The Hacker News
The Python Package Index (PyPI) now requires 2-factor authentication for all project maintainers to combat account takeover attacks.

SecurityWeek
Thirty-five cybersecurity-related merger and acquisition (M&A) deals were announced in November 2022.

Security Affairs
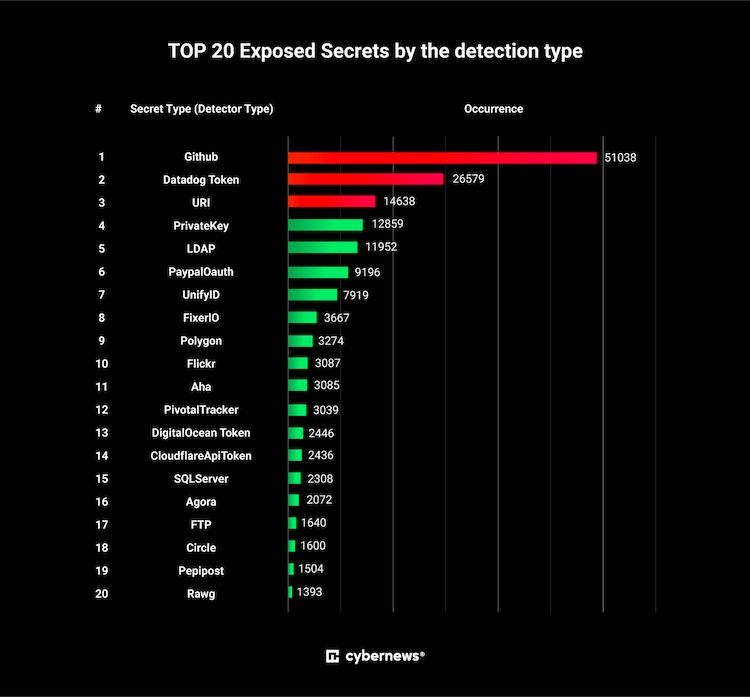
Thousands of secrets have been left exposed on Docker Hub, a platform where web developers collaborate on their code for web applications.

SecurityWeek
Twenty-three cybersecurity-related M&A deals were announced in the first half of August 2022.


Bleeping Computer
The addition of Criminal IP as a new contributor to PolySwarm's malicious URL detection represents a significant leap in specialized threat identification. Learn more from Criminal IP about this new collaboration.


CyberNews
The Docker Hub store has at least 5,493 container images that contain secrets and could be considered as exposing sensitive information.


Bleeping Computer
Criminal IP, a leading Cyber Threat Intelligence search engine, has formed a powerful alliance with Tines, a renowned provider of no-code automation solutions.


Cyber Security News
1Password detected suspicious activity on their Okta instance on September 29, but no user data or sensitive systems were compromised.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine has integrated its IP address and URL scans into VirusTotal. Learn more from Criminal IP about how this integration can help you.


Bleeping Computer
The Criminal IP threat intelligence search engine by AI SPERA has recently integrated with Cisco SecureX/XDR, empowering organizations to stay ahead of malicious actors. Learn more about this integration from Criminal IP in this article.


CSO
The suite of new capabilities includes framework customization with AI, new APIs, and evidence-collection integrations.


Bleeping Computer
Criminal IP is integrating its Threat Intelligence (CTI) search platform in SUMO Logic's cloud security platforms in a new partnership. Learn more from Criminal IP about how this integration can help SUMO Logic customers.


Bleeping Computer
Cyber Threat Intelligence (CTI) search engine Criminal IP has established a technical partnership with Tenable. Learn more from Criminal IP about how this partnership can assist in real-time vulnerability and maliciousness scans.

Ars Technica
It's tricky to exploit, and on a less-popular version, but needs patching ASAP.


Bleeping Computer
A severe security flaw in the Amazon ECR (Elastic Container Registry) Public Gallery could have allowed attackers to delete any container image or inject malicious code into the images of other AWS accounts.


The Record
The US Department of Justice has charged today five Russian nationals, including a former officer of Russia's GRU military intelligence agency, with hacking two SEC Filing Agents, stealing non-public information, and then sharing the stolen data with partners for the purpose of making beneficial trades ahead of time.


Bleeping Computer
A Russian national working for a cybersecurity company has been extradited to the U.S. where he is being charged for hacking into computer networks of two U.S.-based filing agents used by multiple companies to file quarterly and annual earnings through the Securities and Exchange Commissions (SEC) system.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.

SecurityWeek
Forty-one cybersecurity-related M&A deals were announced in August 2022.


The Hacker News
Protect your organization from security nightmares. Learn how modern API management with Gloo Gateway can fortify your defenses against data breaches

Cyber Security News
Running a system network is not so easy, and for this, you need to select the right sysadmin tools so that work can happen peacefully.


The Cyber Express
The significance of cloud security has risen dramatically in the past few years. As businesses move towards digitalization, safeguarding applications

.webp)
Cyber Security News
Best SIEM Tools, solutions and Software: 1. Splunk 2. AlienVault 3. IBM QRadar 4. SolarWinds 5. FortiSIEM 6. McAfee 7. ManageEngine Log360.