

DarkReading
Municipalities Face a Constant Battle as Ransomware Snowballs
As record-breaking volumes of ransomware hit cities, towns, and counties this year, municipalities remain easy targets that pay, and there's no end of the attacks in sight.


DarkReading
As record-breaking volumes of ransomware hit cities, towns, and counties this year, municipalities remain easy targets that pay, and there's no end of the attacks in sight.


Infosecurity News
Mandiant’s latest M-Trends report shows that organizations only needed a median time of 16 days to detect an intrusion in 2022


The Hacker News
Conflicting business requirements is a common problem – and you find it in every corner of an organization, including in information technology.


CyberNews
Just as it has recently seemed like calm before the storm on the cyber front, the Ukrainian embassy to the UK reported being under siege, following a wave of cyberattacks.


Naked Security
Last time they arrived 28 minutes after lighting up their fake domain… this time it was just 21 minutes


Security Affairs
This is the advantage of Data Detection and Response (DDR) for organizations aiming to build a real-time data defense.


SecurityWeek
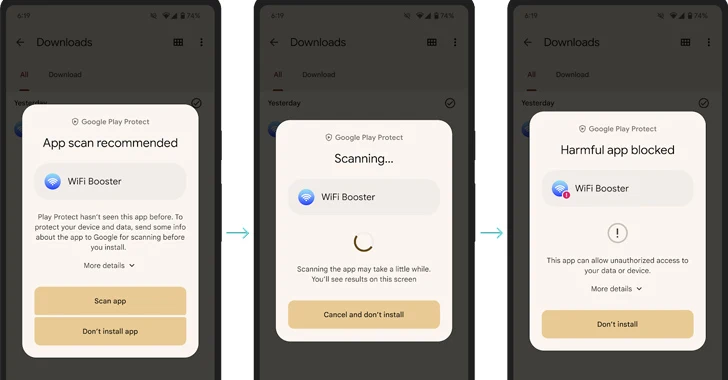
Google improves Android devices’ proactive protections against malware with real-time scanning at code level.


Bleeping Computer
Cybercriminals are abusing X advertisements to promote websites that lead to crypto drainers, fake airdrops, and other scams.


Trend Micro
Explore why Trend Micro is recognized—for the 18th time—as a Leader in the Gartner Magic Quadrant for Endpoint Protection Platforms.


DataBreaches
Christopher Brown reports: Illuminate Education Inc. defeated for the second time a proposed class action alleging it failed to protect the personal...


Bleeping Computer
Cloudflare announced today that they are raising prices for their Pro and Business plans for the first time since they launched in 2017.


Computerworld
A cyberwar could spill over to the business world at any moment, so it's time to lock things down tight.


SecurityWeek
Chrome’s standard Safe Browsing protections now provide real-time malicious site detection and Password Checkup on iOS flags weak passwords.


The Hacker News
Google announces a major upgrade to Safe Browsing! Real-time, privacy-preserving URL checks are now on Chrome for desktop & iOS.


Bleeping Computer
Ransomware threat actors are spending less time on compromised networks before security solutions sound the alarm. In the first half of the year the hackers' median dwell time dropped to five days from nine in 2022

Ars Technica
Poem/1 Kickstarter seeks $103K for fun ChatGPT-fed clock that may hallucinate the time.


Bleeping Computer
The threat actor behind the Twilio hack used their access to steal one-time passwords (OTPs) delivered over SMS to from customers of Okta identity and access management company.


Computerworld
With this month's very light Patch Tuesday release from Microsoft, security and systems administrators should take time to test their apps and desktop/server builds.

The Hacker News
Google Play Protect now scans apps in real time to detect and block novel malware before you install them.


Bleeping Computer
Google will roll out a Safe Browsing update later this month that will provide real-time malware and phishing protection to all Chrome users, without compromising their browsing privacy.


Bleeping Computer
Featuring 168 hours of content, The Premium Core CompTIA Certification Prep Bundle from ITProTV should help you pass first time. For a limited time, you can get the training for just $23.99 using code WELOVEDAD at Bleeping Computer Deals.


SecurityWeek
China implanted malware in US power and communications networks in a "ticking time bomb" that could disrupt the military in event of a conflict


Bleeping Computer
The threat actor behind the Twilio hack used their access to steal one-time passwords (OTPs) delivered over SMS to from customers of Okta identity and access management company.


Bleeping Computer
Google has announced new, real-time scanning features for Google Play Protect that make it harder for malicious apps employing polymorphism to evade detection.


SecurityWeek
Multi-cloud strategies are the norm, but that took time and lessons learned about how we need approach new technologies to gain traction.


ZDNet
Okay, my friends, time for a little tough love.


CSO
The CSO Hall of Fame is accepting nominations for the first time to honor exceptional security leaders with at least 10 years of executive experience.


CyberNews
The White House directed NASA to establish a unified standard of time for the moon and other celestial bodies as the US aims to continue its dominance in outer space.


Bleeping Computer
Google announced today that it is deprecating the standard Google Chrome Safe Browsing feature and moving everyone to its Enhanced Safe Browsing feature in the coming weeks, bringing real-time phishing protection to all users while browsing the web.


The Cyber Express
A particularly nefarious Banking Trojan, TrickBot, has reemerged, this time with an Android variant named "TrickMo" - a reference to


DataBreaches
This is not be the first time the Texas Department of Transportation (TxDOT) has apparently had a data security incident, and it certainly not the largest...


Bleeping Computer
Get The Ultimate Lifetime Bundle of StackSkills + Infosec4TC + Stone River on sale for just $119.99 (reg. $480) for a limited time only


Security Affairs
Russian national Denis Mihaqlovic Dubnikov has been sentenced to time served for committing money laundering for the Ryuk ransomware operation. Russian national Denis Dubnikov (30) has been sentenced to time served for committing money laundering for the Ryuk ransomware group. The man was also ordered to pay $2,000 in restitution. On February 7, 2023, Dubnikov pleaded […]


ZDNet
If you are relying on Russian software or services it might be time to consider the level of risk that involves, says the NCSC.


DataBreaches
A cardiology practice recently discovered that early patient records stored in a basement locker had been stolen at some unknown time. Given that these were...


Computerworld
Though this month's Patch Tuesday update from Microsoft deals with more than 86 reported vulnerabilities, the testing and deployment profile for July should be easy to handle. Use your time wisely.


Bleeping Computer
Microsoft provides some of the key tools for data analysis. With these ten training bundles, you can learn how to master the key apps. For a limited time, every deal below has an extra 40% off when you use code VIP40 at Bleeping Computer Deals.


The Record
Carmakers, and in some cases insurers, are increasingly harvesting data from drivers, often without their knowledge. It’s time for regulation, according to privacy experts — and even some industry insiders.


Infosecurity News
Extortion was most common impact from cyber-attacks in 2022


The Record
Britain’s cyber and signals intelligence agency GCHQ could monitor logs of domestic internet traffic in the United Kingdom in real-time to identify online fraud and interrupt criminals during the act, under a new law being considered by the government.


Latest Hacking News
Memcyco will showcase its solutions at Deloitte’s annual Cyber iCON event, demonstrating how organizations can build effective defenses to protect their customers against digital impersonation fraud Memcyco Inc, the real-time digital impersonation detection and prevention solution

DarkReading
Feeling creative? Submit your caption and our panel of experts will reward the winner with a $25 Amazon gift card.


The Record
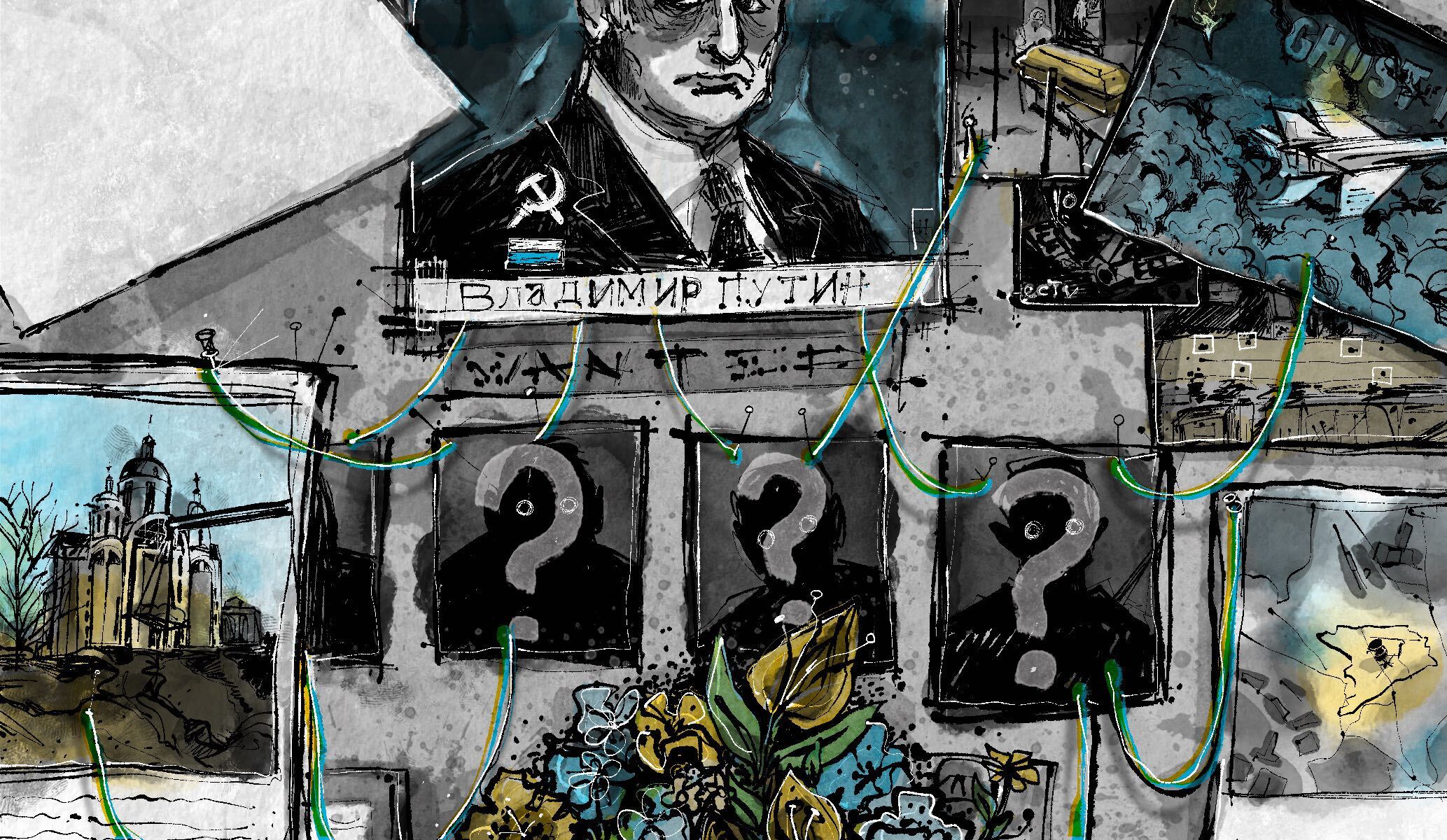
Stanislav is struggling to survive in an economy the world is trying to unplug. The U.S. and its allies have frozen Russian credit card card transactions, the value of the ruble has fallen by nearly a half. So Stanislav has to figure out how to navigate an economy in mid-collapse and his solution is crypto. Plus, the hack heard ‘round the indie music world. Was Grimes really behind it?


Infosecurity News
Most intrusions in the region also reported by third parties


SC Magazine
The infamous data leak site’s domain and Telegram account were seized Wednesday morning.


Cyber Security News
ELLIO, a provider of real-time, highly accurate intelligence for filtering of unwanted network traffic and cybernoise, and ntop, a provider of open-source and commercial high-speed traffic monitoring applications, have announced a partnership to enhance visibility into malicious traffic originating from opportunistic scans and attacks within the network traffic monitoring tool ntopng. By integrating a highly […]


CyberSecurity Dive
Supply-chain attacks and zero-day exploits, such as the widespread attacks against the MOVEit file-transfer service, are surging, according to the Identity Theft Resource Center.


Infosecurity News
It now takes threat actors on average just 62 minutes to move laterally from initial access, Crowdstrike claims

Computerworld
It’s reasonable to anticipate a wave of cyberattacks, which means technology users need to audit their existing security protection. Here are some starting points.


Bleeping Computer
Columbia University researchers have developed a novel algorithm that can block rogue audio eavesdropping via microphones in smartphones, voice assistants, and IoTs in general.


Infosecurity News
Every second counts as threat actors accelerate lateral movement


Infosecurity News
Sanctioned entities accounted for the largest volume


Infosecurity News
Kremlin coercion and sanctions could impact Western customers


CyberNews
If you know anything about the malicious hackers Target, Reshaev, Professor, Tramp, and Dandis, come forward.


Computerworld
For consumers and smaller businesses, security updates for Windows 10 21H2 will end in June. Here’s how to make sure your systems are on Windows 10 22H2 before support runs out.


CyberSecurity Dive
A constant barrage of malicious activity has organizations reeling, negatively impacting their ability to strategize or accomplish IT projects.


Computerworld
If you use your Apple Watch to authenticate access to enterprise sites and services with Microsoft Authenticator, we have bad news: this feature will stop working in January.


Computerworld
This fall, Apple will introduce a new Mail feature to protect brand identity, boost open rates, and protect against phishing attacks.


Computerworld
The browser has become central to how almost everyone uses a computer. And it needs to be as secure as possible to fend off attacks. Here's how to do just that.


The Record
At the CyCon conference in Estonia, Regine Grienberger said Germany is working on satisfying "preconditions" for diplomatic action against Russia for an alleged cyberattack on a German political party in 2023.


The Hacker News
Malicious actors are cloning legit sites to trick you into scams. Memcyco's digital watermark ensures site authenticity, so you can trust the web.


DarkReading
Just 79 minutes — that's how long it takes attackers to move from an initial compromise to extending their infiltration of a firm's network.


Cyber Security News
Keep your network up-to-date and patched round the clock with patch management tool that Powered to patch 850+ third-party applications


CSO
Shared Access Signature (SAS) tokens with excessive permissions can be managed through proper configuration and constant monitoring.


Trend Micro
Trend Micro research reveals struggle to control cyber risks against mounting digital attack surfaces.


Infosecurity News
Doing so will make human errors and workarounds less likely


Cyber Security News
The ever-changing landscape of mobile security is a constant battle between security researchers and malicious actors.


Cyber Security News
The constant deep-learning advancements, and online services are actively escalating the threat of acoustic attacks on keyboards.

.png)
Cyber Security News
Password issues are still a constant struggle for organizations. The amount of time IT teams spend managing user passwords and credentials is increasing every year. An Organization has released the findings of a new report that surveyed 750 IT and security professionals. The aim was to understand better the current state of password usage in […]


CyberSecurity Dive
Cyber-physical systems running on legacy infrastructure are ideal attack surfaces for malicious actors.


Infosecurity News
Most reports related to Google Voice scams


Infosecurity News
Chainalysis monitoring of blockchain transactions finds ransomware payments hit a record $1bn in 2023


ThreatPost
Yaron Kassner, CTO and co-founder of Silverfort, discusses why using all-seeing privileged accounts for monitoring is bad practice.


The Record
A Russian court handed down a mild one-year suspended prison sentence to a member of the FIN7 hacking group, a notorious cybercrime cartel that has hacked more than 100 US companies between 2015 and 2018.


Infosecurity News
Sophos warns against simple interpretation of the data


Ars Technica
Fictional travelogue shows man taking selfies in ancient Greece, Egypt, and more.


The Record
The U.S. doctrine of staying in constant contact with adversaries in cyberspace is "paying dividends," saidDefense Secretary Lloyd Austin.


DataBreaches
Over the Labor Day weekend, the Los Angeles Unified School District (LAUSD) experienced a ransomware attack. Although their initial disclosure did not name the...


CyberSecurity Dive
The industrial cybersecurity specialist previously thwarted a shakedown attempt in May and says the current threat has not been substantiated.


The Hacker News
Lateral movement can lead to a single endpoint becoming a full-scale compromise of an organization's environment


Bleeping Computer
Phishing campaigns continue to focus on social media, ramping up efforts to target users for the third consecutive year as the medium becomes increasingly used worldwide for communication, news, and entertainment.


DataBreaches
Katie Palmer reports: Odds are, you’ve gotten at least one of the unnerving letters in your mailbox this year: “We’re writing to inform you of a...


The Record
Dmitry Cherepanov, 45, is a self described computer geek, who goes by the nickname “Dmitry Brain.”


ZDNet
Data compromises -- especially in the form of cyberattacks -- are increasing.

SecurityWeek
SecurityWeek editors have combed the Black Hat USA 2022 agenda carefully and identified the top 10 sessions that will be making news headlines all week.


CyberSecurity Dive
A hidden epidemic that has hindered women’s ability to continue working at pre-pandemic levels is expected to impact infosec.


CyberSecurity Dive
A threat actor accessed customer support tickets and files containing sensitive data. Okta declined to say how many customers are impacted.

%20(1).webp)
Cyber Security News
A stalkerware company with poor security practices is exposing victims' data as the software, designed for unauthorized device monitoring,


Computerworld
Though Microsoft has backed off earlier plans to block unsafe macros in Excel documents, that change is still coming. Here's what to do now to stay secure.


Cyber Security News
On Wednesday, an ex-Uber CSO was found guilty of federal charges related to payments he secretly approved to hackers who broke into the ride-hailing company in 2016.

SecurityWeek
US justice officials said former Twitter worker Ahmad Abouammo, convicted of spying for Saudi officials, was sentenced to 3.5 years in prison.


SC Magazine
The USAID Colombia Facebook page was hijacked and altered to promote a scam.

CyberScoop
A sharp increase in crypto-currency related sanctions resulted in far more crypto transactions being considered illicit.


Infosecurity News
Jen Ellis urges the cyber industry to take a leading role in shaping its future, during Black Hat Europe 2022

Computerworld
With the Russia-Ukraine conflict under way, cyberattacks are likely to emerge. That's why it's important to take steps now to make sure your hardware is secure.

The Record
Will there be justice for the atrocities in Bucha, Ukraine? Stephen Rapp, a former U.S. ambassador-at-large for war crimes, talks with the Click Here podcast team about the future of that case and others.


CSO
Sysdig also announced a new cloud inventory and agentless scanning capabilities to tackle cloud security risks.


The Record
The National Cyber Security Centre said that it received 2,005 voluntary reports over the past year, a 64% increase on last year’s figures. Nearly 400 of those were so serious that the agency's incident management team had to triage the response.


DarkReading
A majority of enterprises that employ cloud-based email spam filtering services are potentially at risk, thanks to a rampant tendency to misconfigure them.


HACKRead
Under their partnership, Memcyco and Deloitte will leverage additional solutions related to integration and cooperation, such as Deloitte’s Strategic & Reputation Risk Services.
Loading more articles....