

Bleeping Computer
Vodafone Portugal 4G and 5G services down after cyberattack
Vodafone Portugal suffered a cyberattack causing country-wide service outages, including the disruption of 4G/5G data networks, SMS texts, and television services.


Bleeping Computer
Vodafone Portugal suffered a cyberattack causing country-wide service outages, including the disruption of 4G/5G data networks, SMS texts, and television services.

Cyber Security News
Critical issues in ConnectedIO's ER2000 edge routers have been discovered, and an attacker can leverage them to completely compromise the cloud infrastructure


The Hacker News
Multiple high-severity vulnerabilities discovered in ConnectedIO's routers and cloud platform could let hackers execute malicious code.


ZDNet
The company discovered the network disruption on Monday night.


ZDNet
While taking longer to ban Huawei and ZTE than some of the Five Eyes, Canada has also gone further by requiring telcos to rip out LTE equipment from the vendors by the start of 2028.


Bleeping Computer
The Government of Canada announced its intention to ban the use of Huawei and ZTE telecommunications equipment and services across the country's 5G and 4G networks.


Cyber Security News
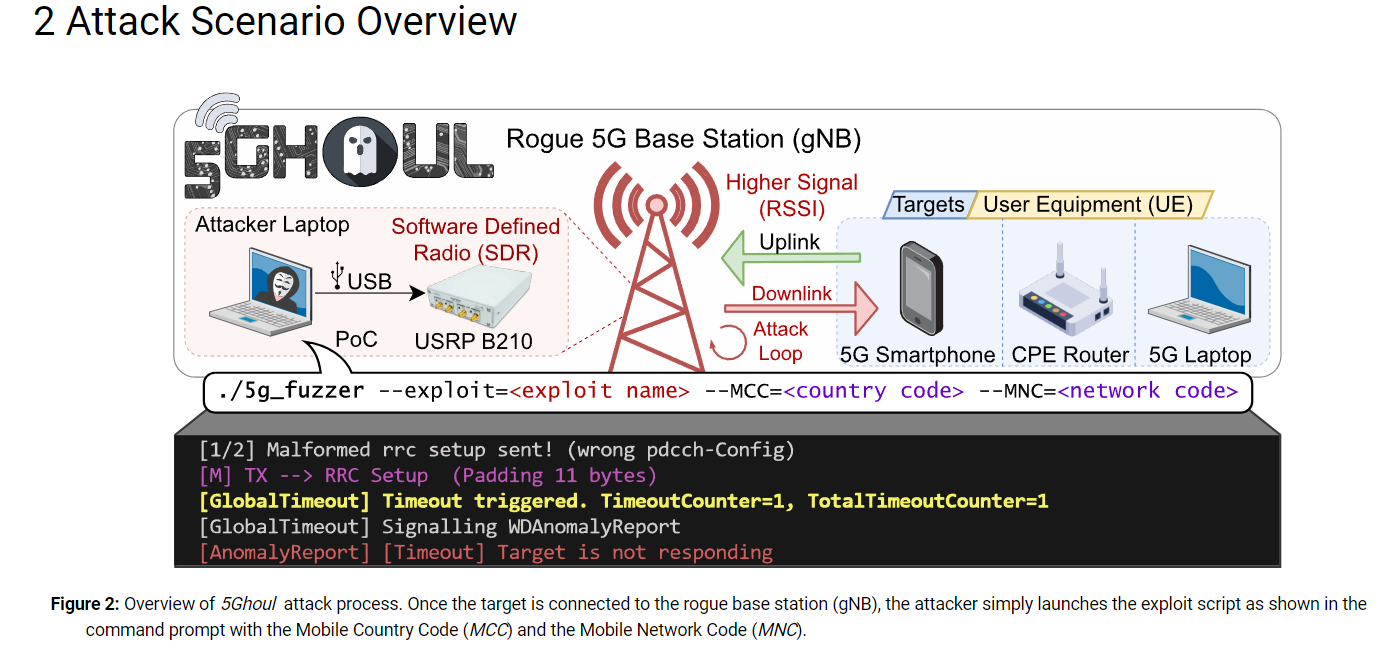
Cybersecurity researchers from the following organizations recently discovered the new 5Ghoul attack that impacts the 5G devices


DataBreaches
Catalin Cimpanu reports: Vodafone Portugal said today that a large chunk of its customer data services went offline overnight following “a deliberate and...


Bleeping Computer
A new set of vulnerabilities in 5G modems by Qualcomm and MediaTek, collectively called "5Ghoul," impact 710 5G smartphone models from Google partners (Android) and Apple, routers, and USB modems.


ZDNet
What's the best mobile VPN? Our number one pick is NordVPN! We analyzed privacy features, reliability, mobile platforms, and speed to determine the best mobile VPN, whether you are using an iOS-powered iPhone or Android smartphone.


Bleeping Computer
Google has finally rolled out an option on Android allowing users to disable 2G connections, which come with a host of privacy and security problems exploited by cell-site simulators.


The Hacker News
Discover the untold security secrets of 5G! Find out how encryption, privacy protection, and more are transforming mobile connectivity.


Security Affairs
Vodafone is investigating a recently suffered cyberattack, after a ransomware gang Lapsus$ claimed to have stolen its source code. Vodafone announced to have launched an investigation after the Lapsus$ cybercrime group claimed to have stolen its source code. The Lapsus$ gang claims to have stolen approximately 200 GB of source code files, allegedly contained in […]


The Cyber Express
Vodafone Egypt, the largest mobile operator in the country serving over 40 million customers, finds itself grappling with a partial


DarkReading
Drone-based cyberattacks to spy on corporate targets are no longer hypothetical, one incident from this summer shows.


The Record
Vodafone Portugal said today that a large chunk of its customer data services went offline overnight following "a deliberate and malicious cyberattack intended to cause damage and disruption."


Bleeping Computer
Croatian phone carrier 'A1 Hrvatska' has disclosed a data breach exposing the personal information of 10% of its customers, roughly 200,000 people.


Infosecurity News
CISA releases a five-step plan to aid agencies in the development and deployment of 5G projects


SecurityWeek
Hackers stole a database containing the list of the European Telecommunications Standards Institute’s online users.

The Hacker News
Zyxel releases critical security patches for firewall devices. Flaw could allow remote code execution on affected systems.


The Hacker News
Attention all network administrators! Zyxel firewalls under attack! Act now to prevent a potential DoS attack and remote code execution.


SecurityWeek
Palo Alto Networks has launched a new rugged firewall for industrial environments and announced several OT security improvements.


Security Affairs
Croatian phone carrier A1 Hrvatska has disclosed a data breach that has impacted roughly 200,000 customers. Croatian phone carrier A1 Hrvatska has disclosed a data breach that has impacted 10% of its customers, roughly 200,000 people. Threat actors had access to sensitive personal information of the customers, including names, personal identification numbers, physical addresses, and […]

SecurityWeek
The US government makes a $45 million investment in 16 projects to improve cybersecurity across the energy sector.


Ars Technica
Verizon simplifies its data plans: Do you want the fast one or the slow one?


Security Affairs
Ukrainian authorities revealed that Russia-linked APT Sandworm had been inside telecom giant Kyivstar at least since May 2023.


DarkReading
The Intellexa alliance has been using a range of tools for intercepting and subverting mobile and Wi-Fi technologies to deploy its surveillance tools, according to an investigation by Amnesty International and others.


The Hacker News
Google boosts Android security with Clang sanitizers! Meet IntSan and BoundSan, designed to catch vulnerabilities in the cellular baseband


The Record
The company’s AirLink cellular routers are often used in critical infrastructure sectors, such as government and emergency services.


SecurityWeek
Dozens of critical and high-severity vulnerabilities in the Milesight UR32L industrial router leading to code execution


The Hacker News
Major security flaws in 5G modems impact hundreds of smartphone models from brands like Apple, Samsung, and Google.


Bleeping Computer
Google has announced new cellular security features for its upcoming Android 14, expected later this month, that aim to protect business data and communications.


Infosecurity News
At MWC Barcelona leaders explored the opportunities available in the emerging metaverse


Latest Hacking News
SMS delivery reports not only let the sender know about the message receipt, but can also leak the recipient’s location. This is what researchers have demonstrated in their recent study, showing how receiving a silent


Security Affairs
Kyivstar, the largest Ukraine service provider, was hit by a cyber attack that paralyzed its services .......


Security Affairs
TIM Red Team Research (RTR) researchers discovered a new flaw on Ericsson Network Manager, aka Ericsson flagship network product. TIM Red Team Research (RTR) team discovered a new vulnerability affecting Ericsson Network Manager, which is known as Ericsson flagship network product. Ericsson Network Manager and network OSS As mentioned, we’re talking about an Ericsson flagship […]


Bleeping Computer
SAC Wireless, a US-based and independently-operating Nokia company subsidiary, has disclosed a data breach following a ransomware attack where Conti operators were able to successfully breach its network, steal data, and encrypt systems.

Bleeping Computer
Security researcher HaxRob discovered a previously unknown Linux backdoor named GTPDOOR, designed for covert operations within mobile carrier networks.


Security Affairs
Experts at TIM research laboratory, Red Team Research (RTR), have disclosed a couple of bugs affecting F5 Traffix SDC. Among these 45 bugs fixed by the well-known manufacturer of computer security systems, 2 were detected by TIM research laboratory, Red Team Research (RTR), as part of the bug hunting activities, on the F5® Traffix® Signaling […]


The Cyber Express
Islamabad's Safe City Authority experienced a significant disruption when its online system was breached by hackers, prompting an immediate shutdown.


ZDNet
EFF urges Apple to follow Google and give smartphone users the option to dodge 2G.


ZDNet
Redmond says no customer code or data was taken without directly addressing whether its own source was exfiltrated.

Bleeping Computer
A high severity security vulnerability found in Qualcomm's Mobile Station Modem (MSM) chips (including the latest 5G-capable versions) could enable attackers to access mobile phone users' text messages, call history, and listen in on their conversations.

Security Affairs
A set of flaws, collectively called 5Ghoul, in the firmware implementation of 5G mobile network modems impacts Android and iOS devices.


Computerworld
It's not the 100,000 Russian troops on Ukraine's borders that worries me as much as cyberattacks that can easily get out of hand.


ZDNet
Company says a 'small percentage' of customers could have had their data viewed or acted on, and simple maths turns that number into 375 customers.


Ars Technica
There are vulnerabilities in 5G platforms carriers offer to wrangle embedded device data.


Bleeping Computer
A set of 21 newly discovered vulnerabilities impact Sierra OT/IoT routers and threaten critical infrastructure with remote code execution, unauthorized access, cross-site scripting, authentication bypass, and denial of service attacks.

The Cyber Wire
Drone technology improvises and adapts, but so do air defenses. Experts warn of hybrid wars' spillover into remote sections of cyberspace.

The Cyber Wire
Drone technology improvises and adapts, but so do air defenses. Experts warn of hybrid wars' spillover into remote sections of cyberspace.


The Record
Britain’s cyber and signals intelligence agency GCHQ could monitor logs of domestic internet traffic in the United Kingdom in real-time to identify online fraud and interrupt criminals during the act, under a new law being considered by the government.

CSO
A joint proposal from federal cybersecurity and defense agencies defines a process for ensuring the security of 5G networks.


Trend Micro
Crafted packets from cellular devices such as mobile phones can exploit faulty state machines in the 5G core to attack cellular infrastructure. Smart devices that critical industries such as defense, utilities, and the medical sectors use for their daily operations depend on the speed, efficiency, and productivity brought by 5G. This entry describes CVE-2021-45462 as a potential use case to deploy a denial-of-service (DoS) attack to private 5G networks.


Trend Micro
In this three-part blog entry, our team explored SMS PVA, a service built on top of a global bot network that compromises smartphone cybersecurity as we know it.


CSO
A new report discovers edge network definitions are in flux across industries as organizations look to augment traditional security controls to address edge network risks.


Trend Micro
The ICS Security Event S4 was held for the first time in two years, bringing together more than 800 business leaders and specialists from around the world to Miami Beach on 19-21 Feb 2022. The theme was CREATE THE FUTURE.


Trend Micro
In today's business world's dynamic and ever-changing digital landscape, organizations encounter escalating security challenges that demand a more business-friendly and pertinent approach.


ZDNet
Healthcare and maritime are key sectors that can benefit from 5G connectivity with their need for low network latency, but they also have to prepare for higher security risks.


ZDNet
The NSA's 'Best Practices for Securing Your Home Network' guide provides remote workers with advice on how to protect against online threats.


Trend Micro
In the second part of this series, we will examine how attackers can trigger vulnerabilities by sending control messages masquerading as user traffic to cross over from user plane to control plane.


Trend Micro
The Open Radio Access Network (ORAN) architecture provides standardized interfaces and protocols to previously closed systems. However, our research on ORAN demonstrates the potential threat posed by malicious xApps that are capable of compromising the entire Ran Intelligent Controller (RIC) subsystem.


ZDNet
Your smartphone contains your passwords, private messages, bank details and more. Here's how to keep that vital info a little bit safer.


ZDNet
Is your slow internet connection getting you down? Here's how to fix the most common issues.


Trend Micro
In this entry we look into how Log4j vulnerabilities affect devices or properties embedded in or used for connected cars, specifically chargers, in-vehicle infotainment systems, and digital remotes for opening cars.

.webp)
Cyber Security News
Secure Network As a Service for MSP: 1. Perimeter 81 2. Cloudflare 3. Netskope 4. VMware 5. Palo Alto Networks 6. Aarna Networks.