

The Record
Breaking: LockbitSupp suspect identified as Dmitry Khoroshev
Dmitry Yuryevich Khoroshev, a 31-year-old Russian national, ran the LockBit ransomware gang under the alias LockbitSupp, said authorities from the U.S., U.K. and Australia.


The Record
Dmitry Yuryevich Khoroshev, a 31-year-old Russian national, ran the LockBit ransomware gang under the alias LockbitSupp, said authorities from the U.S., U.K. and Australia.


HACKRead
In a major blow to ransomware, international law enforcement has unmasked Dmitry Yuryevich Khoroshev, the leader of LockBit ransomware.


The Hacker News
UK's National Crime Agency has unmasked the admin behind the prolific LockBit ransomware as 31-year-old Russian national Dmitry Khoroshev.


Infosecurity News
Russian national Dmitry Yuryevich Khoroshev is behind the LockBitSupp persona, law enforcement revealed


Ars Technica
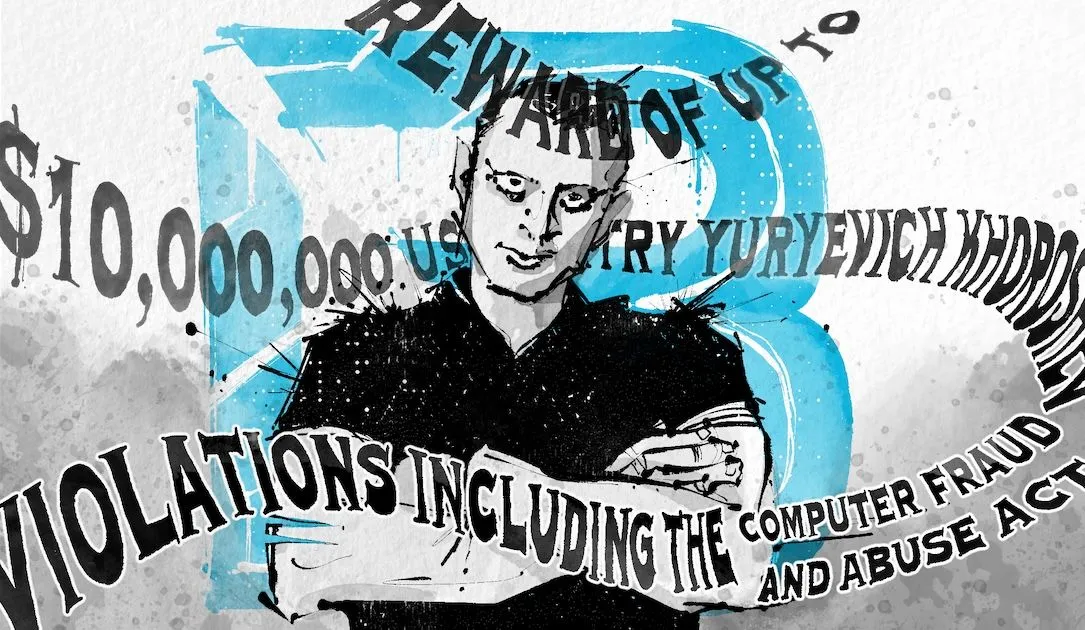
The US places a $10 million bounty for the arrest of Dmitry Yuryevich Khoroshev.


SecurityWeek
Charges and sanctions announced against Dimitry Yuryevich Khoroshev, the alleged developer and operator of LockBit ransomware.


Krebs on Security
The United States joined the United Kingdom and Australia today in sanctioning 31-year-old Russian national Dmitry Yuryevich Khoroshev as the alleged leader of the infamous ransomware group LockBit. The U.S. Department of Justice also indicted Khoroshev as the gang's leader…


DarkReading
Australian businesses and individuals now risk fines and other consequences if they pay ransoms to LockBitSupp, aka Dmitry Yuryevich Khoroshev.


The Cyber Express
In a landmark international operation, Dmitry Khoroshev, the once-anonymous leader behind the notorious LockBit Ransomware gang has been unmasked and

The Record
LockBitSupp, head of the LockBit cybercrime operation, tells the Click Here podcast team that he is not Russian national Dmitry Khoroshev, as claimed by the U.S., U.K. and Australia.


The Cyber Express
Despite the major collaborative effort by law enforcement agencies resulting in the exposure and sanctioning of Dmitry Yuryevich Khoroshev, the


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


The Cyber Express
In an unexpected turn of events, LockBitSupp, the administrator of the notorious LockBit ransomware group, responded publicly to the Federal


CyberNews
The leadership identity of the LockBit ransomware group is unveiled by the US Department of Justice (DoJ), UK’s National Crime Agency (NCA), and Europol.


Bleeping Computer
The FBI, UK National Crime Agency, and Europol have unveiled sweeping indictments and sanctions against the admin of the LockBit ransomware operation, with the identity of the Russian threat actor revealed for the first time.


Security Affairs
The FBI, UK National Crime Agency, and Europol revealed the identity of the admin of the LockBit operation and sanctioned him.


CSO
A Russian national alleged to have been the administrator of the notorious and prolific LockBit ransomware provider faces international charges. A $10-million reward for the suspect’s arrest has been offered.


SC Magazine
Security pros say the move by law enforcement puts a significant dent into LockBit.


Cyber Security News
The UK's National Crime Agency (NCA) announced a major breakthrough today in their investigation into the notorious LockBit ransomware gang.


SecurityWeek
The LockBit cybercrime group has taken credit for the recent ransomware attack that disrupted City of Wichita systems.


The Cyber Express
Boeing confirmed that the LockBit ransomware gang attack in October 2023, which impacted certain parts and distribution operations of the


DarkReading
The city is still investigating the attack, and neither the group nor city officials have offered details about the ransomware demands.


Cyber Security News
Aerospace giant Boeing has confirmed that the LockBit ransomware gang demanded a staggering $200 million extortion payment after breaching the company's network and stealing sensitive data in October 2023.


Bleeping Computer
This week was pretty quiet on the ransomware front, with most of the attention on the seizure of the BreachForums data theft forum. However, that does not mean there was nothing of interest released this week about ransomware.


SC Magazine
The Canadian drug retailer maintains it won’t pay a $25 million ransom, while LockBit allegedly said it would start releasing stolen data.


The Record
The ransomware operation gave the Kansas city until May 15 to pay up. The incident continues to unfold as law enforcement agencies announced actions against the gang's suspected leader.


Security Affairs
The LockBit ransomware group has added the City of Wichita to its Tor leak site and threatened to publish stolen data.


Bleeping Computer
The LockBit ransomware gang has claimed responsibility for a disruptive cyberattack on the City of Wichita, which has forced the City's authorities to shut down IT systems used for online bill payment, including court fines, water bills, and public transportation.


SecurityWeek
FBI is targeting Scattered Spider, Australia’s MediSecure hacked in ransomware attack, and researchers present new Wi-Fi attack.


Bleeping Computer
Today, the LockBit ransomware gang claimed they were behind the April cyberattack on Canadian pharmacy chain London Drugs and is now threatening to publish stolen data online after allegedly failed negotiations.


Bleeping Computer
After many months of taunting law enforcement and offering a million-dollar reward to anyone who could reveal his identity, the FBI and NCA have done just that, revealing the name of LockBitSupp, the operator of the LockBit ransomware operation.


The Cyber Express
This week on TCE Cyberwatch, we delve into the recent hackings of major organizations, including the International Baccalaureate, Boeing, and

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.